
Mathematical Integrity
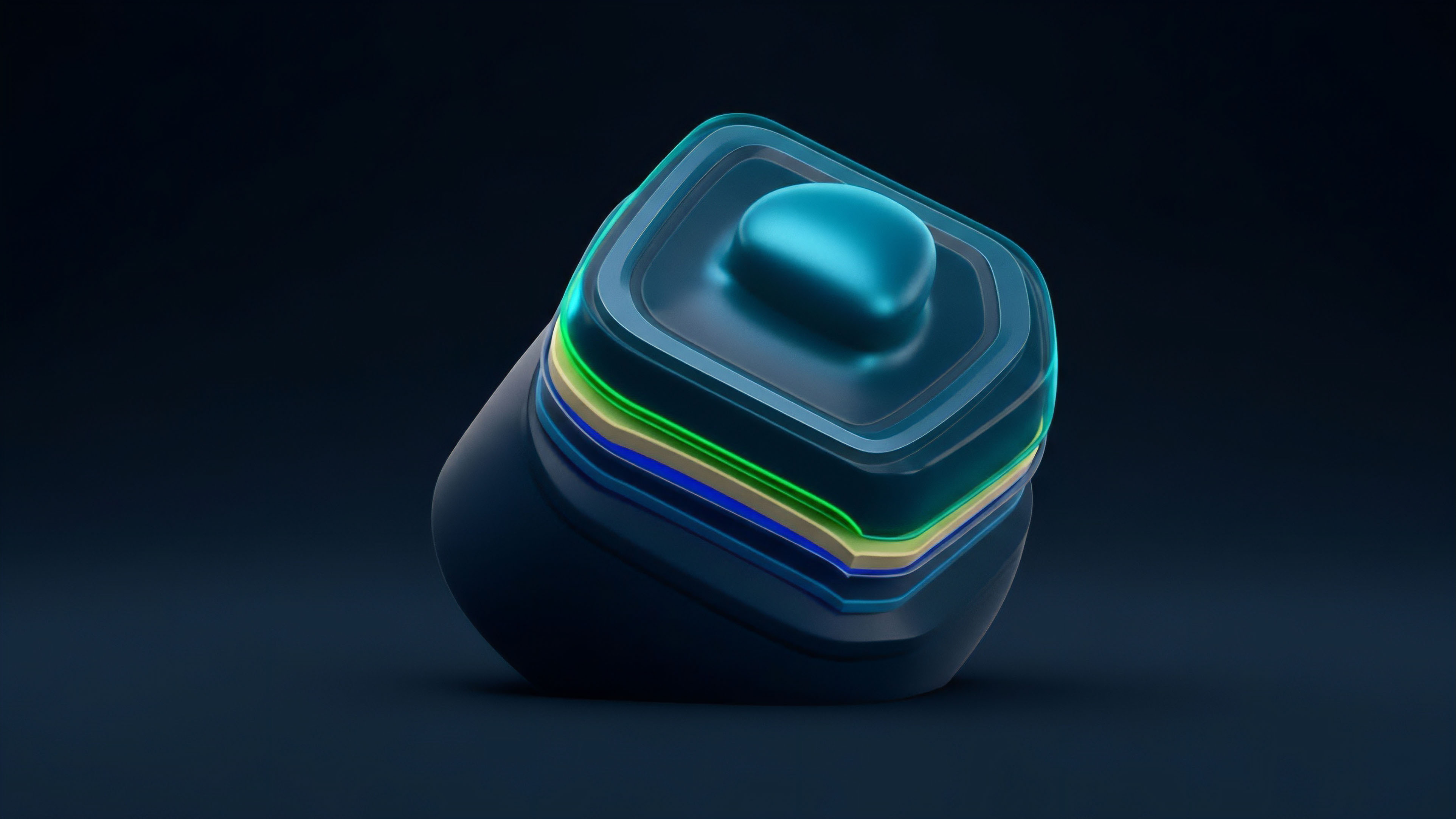
Succinct verification of high-dimensional data sets provides the structural scaffolding for decentralized margin engines. Polynomial Commitments function as a cryptographic promise, allowing a prover to attest to the validity of a mathematical function without revealing the underlying data points. This mechanism enables a verifier to confirm that a specific evaluation of a polynomial is correct relative to a previously shared commitment.
Within the architecture of decentralized finance, this capability shifts the burden of proof from centralized intermediaries to immutable algebraic constraints.
Polynomial commitments allow a prover to commit to a polynomial such that they can later provide a proof for any evaluation of that polynomial.
The application of these primitives within derivative markets addresses the bottleneck of state transition verification. By compressing large batches of trade data into a single commitment, protocols maintain high throughput while ensuring that every margin call and liquidation event adheres to the predefined rules of the smart contract. This mathematical certainty provides a level of security that traditional clearinghouses cannot match, as it eliminates the possibility of human error or malicious data manipulation during the settlement process.
Algebraic Trust and Capital Efficiency
Financial systems built upon Polynomial Commitments operate with a heightened degree of capital efficiency. Because the proofs are small and verification is fast, the latency between trade execution and final settlement decreases. This reduction in settlement time lowers the counterparty risk inherent in volatile option markets.
Traders can operate with higher leverage when the underlying system provides near-instantaneous, verifiable proof of solvency and collateralization.
- Succinctness ensures that the size of the proof remains small regardless of the complexity of the underlying dataset.
- Binding properties prevent a prover from changing the polynomial after the commitment has been made.
- Hiding characteristics protect the privacy of sensitive trading strategies by revealing only necessary evaluation points.
Cryptographic Foundations
The genesis of these schemes lies in the requirement for verifiable computation within adversarial environments. Early cryptographic structures relied on Merkle trees, which provide logarithmic proof sizes but struggle with complex algebraic relations. The transition toward Polynomial Commitments was catalyzed by the need for more expressive and efficient zero-knowledge proofs.
The KZG Commitment, introduced in 2010, established the primary standard by utilizing elliptic curve pairings to achieve constant-size proofs.
The Kate-Zaverucha-Goldberg scheme remains the foundational pairing-based commitment used in modern blockchain scaling solutions.
Derivative architects adopted these mathematical tools to solve the data availability problem. In a decentralized option exchange, the state of the order book and the margin requirements of every participant must be verifiable by all nodes. Older methods required downloading the entire state, which is unfeasible for high-frequency trading.
Polynomial Commitments allow nodes to verify specific pieces of information, such as a user’s balance or a strike price, with minimal data transfer.
| Scheme Type | Proof Size | Verification Speed | Trust Assumption |
|---|---|---|---|
| KZG | Constant | Very Fast | Trusted Setup |
| IPA | Logarithmic | Linear | Transparent |
| FRI | Polylogarithmic | Fast | Transparent |
Algebraic Mechanics
The structural logic of a Polynomial Commitment involves representing a dataset as a polynomial P(x) over a finite field. The prover computes a commitment C by evaluating the polynomial at a secret point or using a vector of group elements. When a verifier requests the value of P(z), the prover generates a proof π that demonstrates P(z) = y.
The verifier uses the commitment C, the proof π, and the evaluation point z to confirm the claim. This process relies on the hardness of the Discrete Logarithm Problem or the security of bilinear pairings.
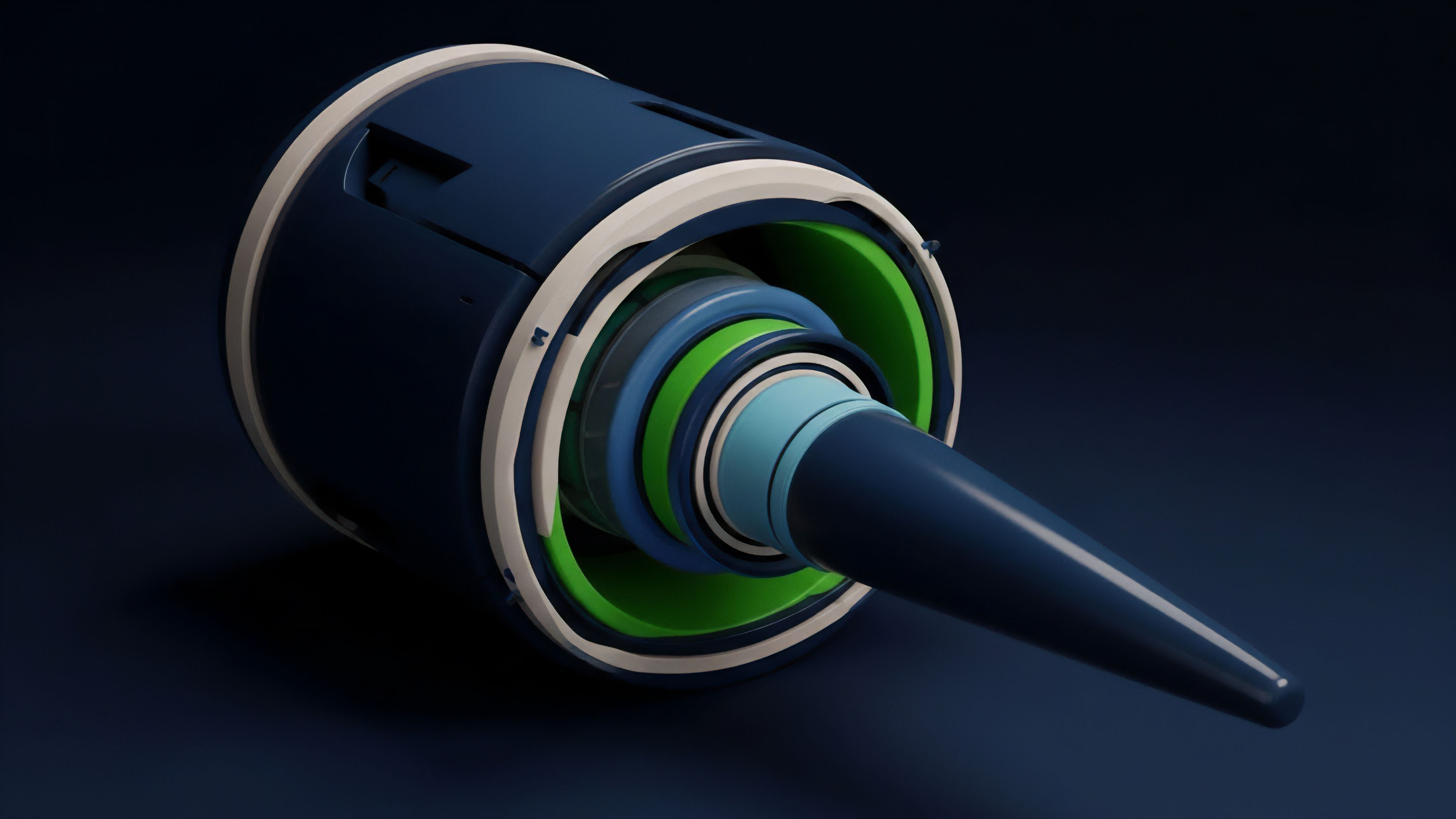
Commitment Schemes and Proof Systems
Different proof systems utilize varying commitment architectures to balance the trade-offs between security and performance. KZG Commitments are favored for their efficiency but require a one-time trusted setup ceremony to generate the initial parameters. If these parameters are compromised, the integrity of the entire system is at risk.
Conversely, FRI (Fast Reed-Solomon Interactive Oracle Proof of Proximity) utilized in STARKs avoids trusted setups by relying on hash functions, though it results in larger proof sizes that can increase gas costs on-chain.
Mathematical proofs replace the need for legal recourse by making the violation of contract terms computationally impossible.

Verification Complexity and Scaling
The computational overhead for the verifier is a primary consideration in derivative system design. In a high-volume environment, the cost of verifying proofs must remain low to prevent the congestion of the settlement layer. Polynomial Commitments achieve sub-linear verification time, meaning the effort required to check a proof grows much slower than the size of the data being proven.
This property is vital for scaling synthetic asset platforms where thousands of price feeds must be processed simultaneously.
| Property | Financial Significance | Technical Driver |
|---|---|---|
| Soundness | Prevents fraudulent withdrawals | Algebraic Binding |
| Zero-Knowledge | Protects proprietary alpha | Blinding Factors |
| Batching | Reduces transaction costs | Homomorphic Addition |
Operational Execution
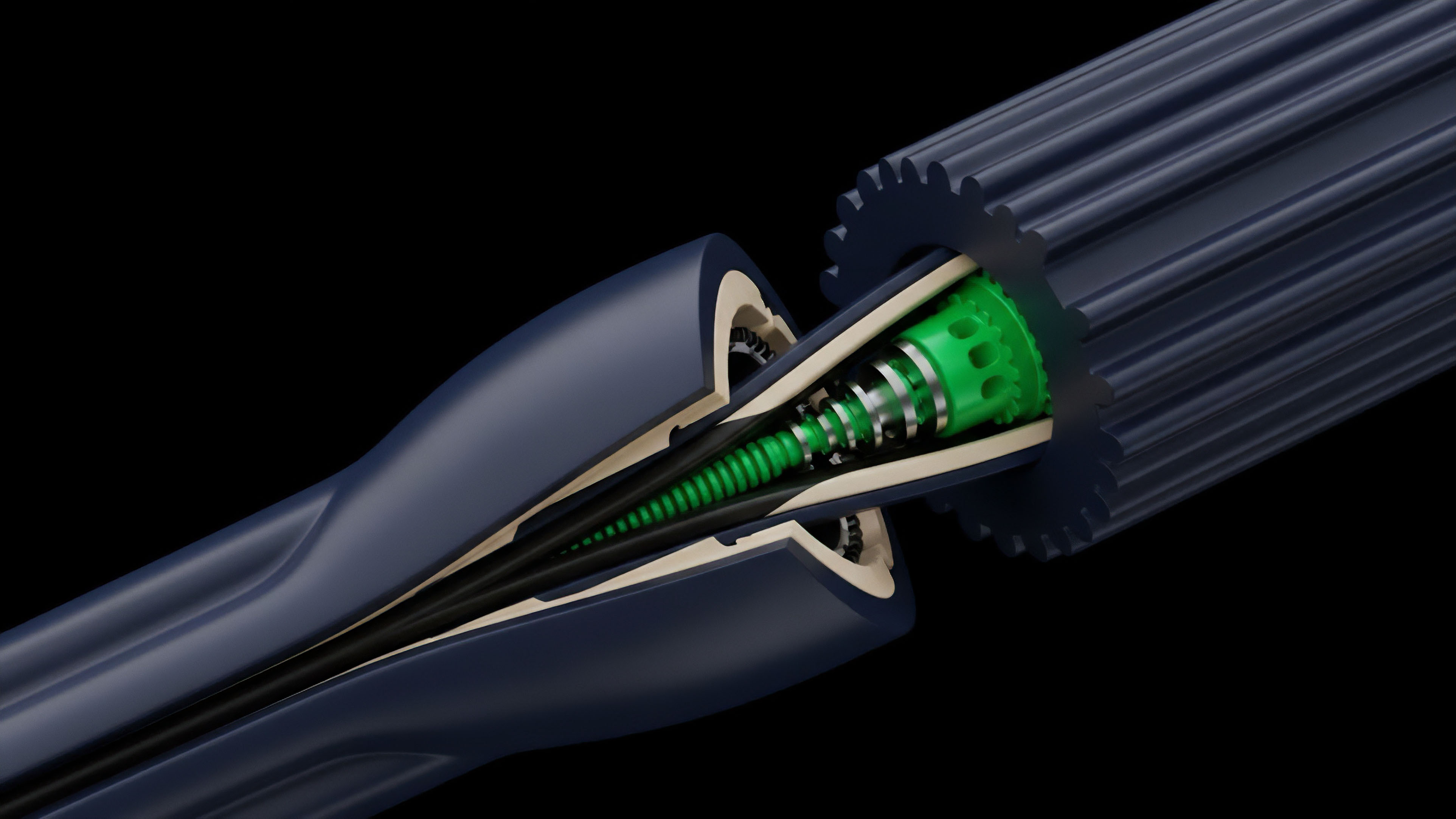
Modern decentralized derivative protocols implement Polynomial Commitments to manage complex state transitions within their margin engines. By utilizing ZK-Rollups, these platforms aggregate trades off-chain and submit a single proof to the base layer. This method ensures that every liquidation and payout is mathematically sound without requiring every node to re-execute every trade.
The efficiency of this execution model allows for the creation of sophisticated on-chain options that mirror the performance of centralized venues.

Implementation in Margin Engines
The integration of KZG Commitments in Ethereum’s EIP-4844 demonstrates the shift toward data-centric scaling. This update utilizes blobs to store transaction data, with Polynomial Commitments ensuring the data is available and correct. For a derivative trader, this translates to lower fees and higher reliability during periods of extreme market volatility.
The margin engine can verify the state of a portfolio across multiple sub-accounts using a single proof, preventing the systemic failures often seen when centralized risk engines lag during market crashes.
- Recursive Proofs allow one commitment to verify another, enabling infinite scaling of financial logic.
- Multi-point Evaluations enable the verification of multiple strike prices within a single cryptographic proof.
- Vector Commitments provide a method for proving the state of an entire order book without revealing individual orders.

Technical Progression
The advancement of commitment schemes reflects a move away from fragile trust assumptions toward robust, transparent architectures. Early implementations were limited by the necessity of trusted setups, which created a centralized point of failure during the initialization phase. The rise of Transparent Polynomial Commitments, such as those using Bulletproofs or FRI, has eliminated this risk.
This progression ensures that the security of a derivative protocol is derived solely from the laws of mathematics and the entropy of the network.
The transition to transparent commitment schemes removes the systemic risk associated with the generation of initial cryptographic parameters.
Market participants now demand higher levels of transparency and security. The failure of several centralized lending platforms highlighted the dangers of opaque risk management. Polynomial Commitments provide a path toward a “Proof of Solvency” that is updated in real-time.
By committing to the state of all liabilities and assets, a protocol can prove it is fully collateralized without revealing the specific identities or positions of its users. This balance of privacy and transparency is a significant shift from the traditional financial model.

Adaptive Security and Quantum Resistance
As computational power increases, the threat of quantum computing to traditional elliptic curve cryptography becomes a factor in long-term system design. FRI-based commitments are considered post-quantum secure because they rely on hash functions rather than the hardness of discrete logarithms. Derivative systems intended to last for decades are beginning to incorporate these more resilient schemes to ensure that the value locked in long-dated option contracts remains secure against future technological leaps.

Future Trajectories
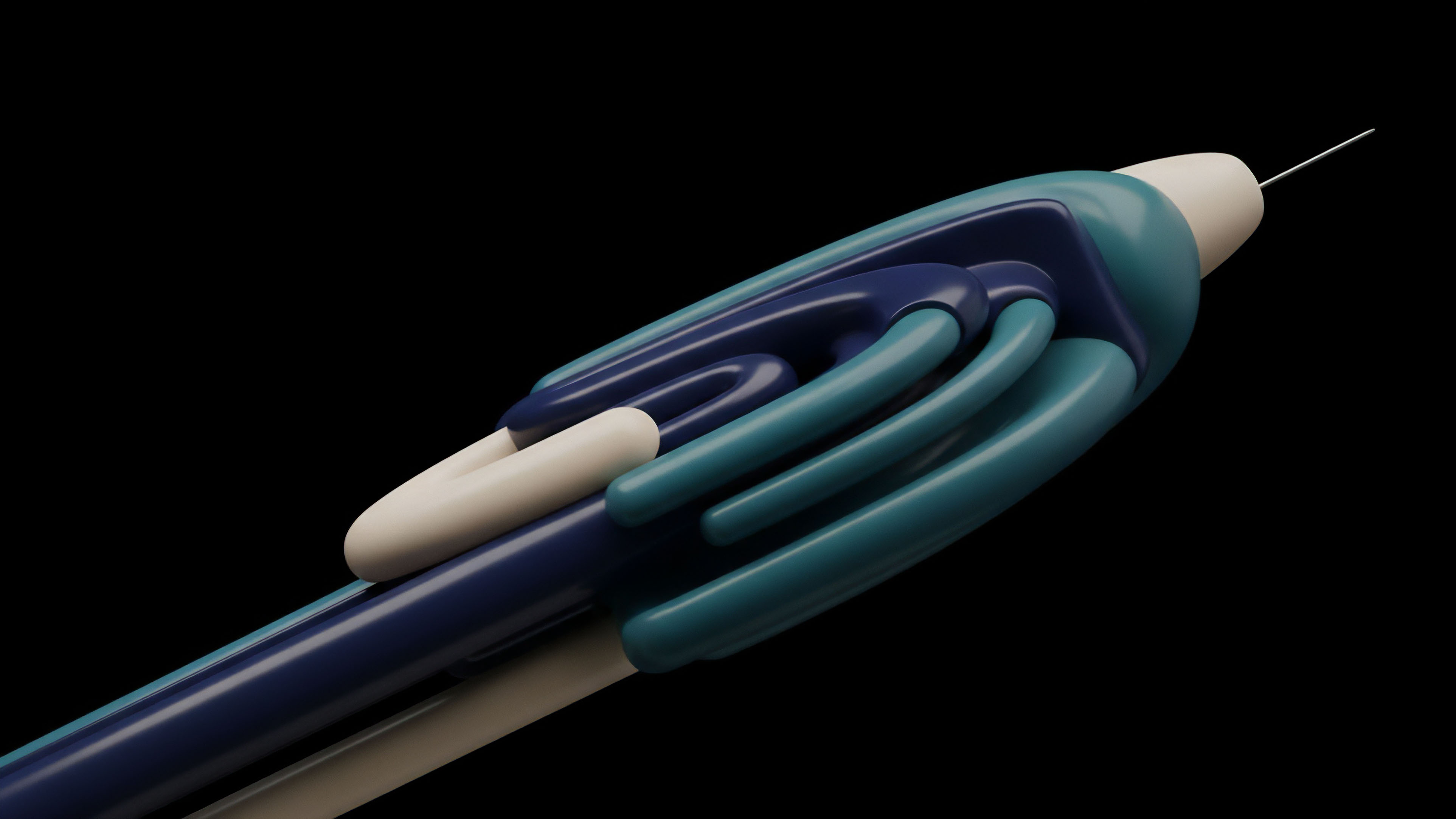
The next phase of development involves the integration of Fully Homomorphic Encryption with Polynomial Commitments.
This combination would allow for the execution of trades and the calculation of margin requirements on encrypted data. Traders could submit orders that are verified for collateral sufficiency without the exchange ever knowing the direction or size of the trade until the moment of execution. This would effectively eliminate front-running and MEV (Maximal Extractable Value) in decentralized option markets.
Future derivative architectures will likely combine zero-knowledge proofs with homomorphic encryption to achieve absolute trade privacy.
The convergence of Polynomial Commitments and artificial intelligence also presents a new frontier. AI-driven risk models can be trained on private data, with the results verified through cryptographic commitments. This allows for more dynamic and accurate pricing of exotic options and complex volatility products.
The resulting financial system is one where risk is managed by sophisticated algorithms, but the integrity of those algorithms is guaranteed by immutable mathematical proofs.
Systemic Scaling and Global Liquidity
The ultimate goal is the creation of a global, unified liquidity pool for derivatives that is accessible to anyone with an internet connection. Polynomial Commitments provide the necessary tools to bridge disparate networks and protocols without introducing new trust assumptions. By verifying the state of one blockchain on another using succinct proofs, we can create a seamless financial layer where capital flows to its most efficient use without the friction of centralized gatekeepers or the risks of manual settlement.

Glossary

Data Availability

Bulletproofs

Cryptographic Commitment Schemes
Ethereum Scaling
Hash Based Commitments
Post-Quantum Cryptography
Proof-of-Solvency
Synthetic Assets
Secure Multi-Party Computation






