
Essence
Network Security Metrics function as the diagnostic heartbeat of decentralized financial protocols, quantifying the probability of state corruption or chain reorganization. These metrics represent the raw computational and economic costs required to alter the ledger history or censor transactions. Participants in derivatives markets rely on these data points to price the underlying risk of smart contract failure and chain instability.
Network Security Metrics quantify the economic and computational barriers preventing unauthorized ledger modification.
Protocol resilience hinges on the interplay between consensus participation and decentralized verification. High values in these metrics signal robust protection against majority attacks, directly influencing the stability of automated market makers and collateralized lending engines. When these indicators degrade, systemic risk premiums adjust, reflecting the increased likelihood of network-level disruptions affecting derivative settlement.
Origin
The genesis of Network Security Metrics resides in the fundamental cryptographic challenge of securing a distributed, trustless ledger against adversarial actors.
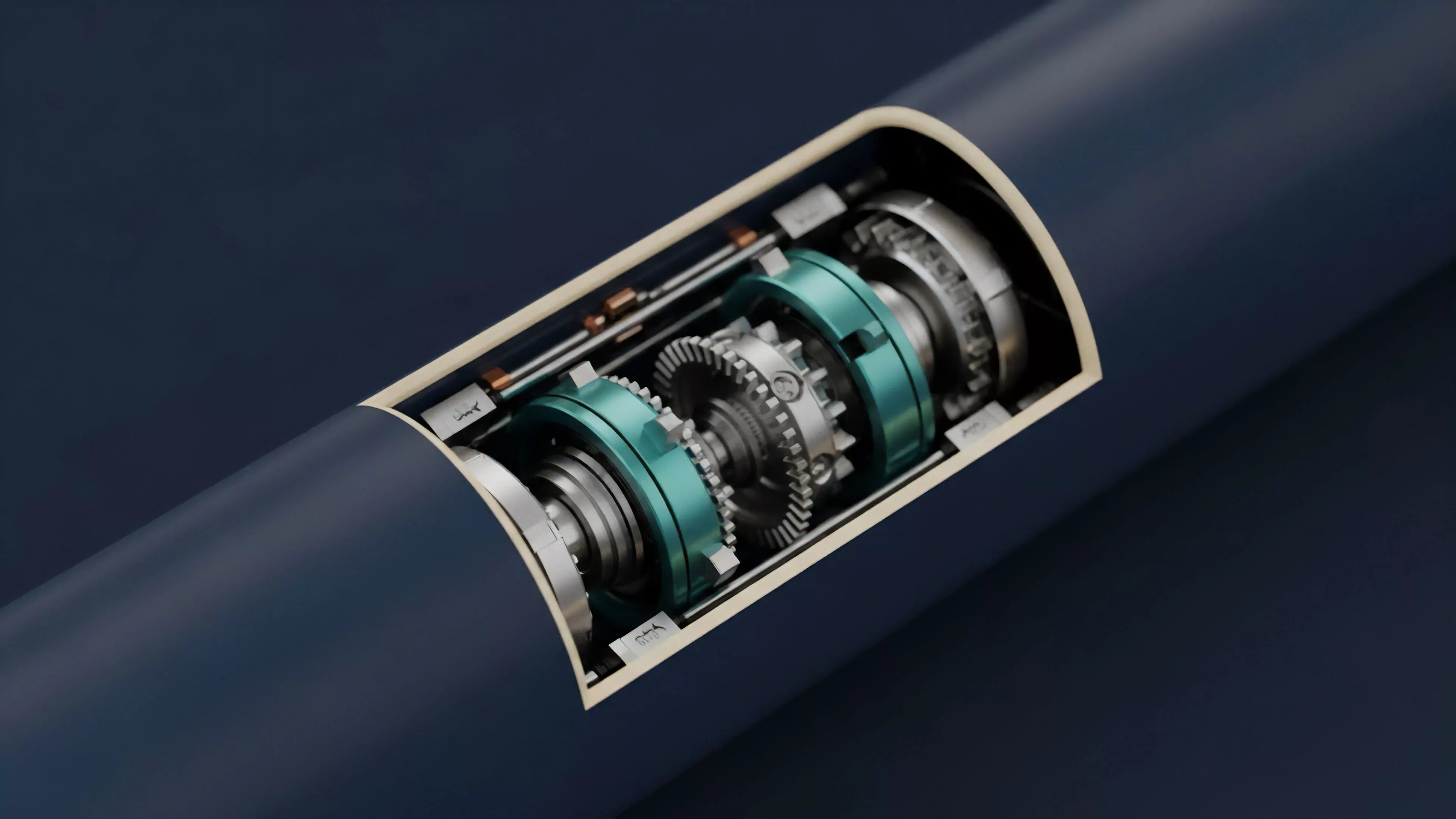
Early iterations focused on Hashrate, the total computational power dedicated to Proof of Work networks, establishing a clear link between energy expenditure and immutability. As decentralized finance expanded, the need arose to move beyond simple power consumption to more sophisticated measures of network health.
Hashrate remains the foundational metric for measuring the energy cost of ledger manipulation in proof of work systems.
Historical market cycles exposed the fragility of networks with low participation, prompting developers to create more granular tracking. These initial tools sought to map the distribution of validator nodes, the concentration of staked capital, and the speed of transaction finality. This shift transformed the perception of security from a static property of code into a dynamic, measurable output of economic and game-theoretic incentives.

Theory
The architecture of Network Security Metrics relies on modeling adversarial behavior through the lens of cost-benefit analysis.
Attackers operate within an environment where the expense of subverting consensus must exceed the potential gain from double-spending or censorship. Quantitative models analyze the Cost of Attack, a variable determined by the current market price of hardware, energy, or staked assets.
- Nakamoto Coefficient identifies the minimum number of entities required to compromise a network, providing a snapshot of decentralization.
- Finality Latency measures the duration between transaction submission and the point where reversal becomes economically unfeasible.
- Validator Distribution tracks the geographic and institutional spread of consensus participants to gauge resistance against regulatory or physical coercion.
Market participants utilize these metrics to adjust their risk models for synthetic assets and options. A sudden decline in validator participation often precedes liquidity volatility, as traders account for the heightened risk of chain halts.
Validator distribution and finality latency serve as critical inputs for assessing the structural reliability of decentralized settlement.
The mathematical structure of these metrics often involves calculating the Gini Coefficient for stake distribution, providing a rigorous assessment of power concentration. When the Gini coefficient rises, the network approaches a state of central authority, rendering standard security assumptions void. Sometimes, the most stable protocols exhibit a paradox where security increases as participation costs rise, yet this creates a barrier to entry that stifles network growth.

Approach
Current implementation of Network Security Metrics involves real-time monitoring of on-chain data to inform derivative pricing and margin requirements.
Advanced platforms integrate these metrics directly into their risk engines, automatically adjusting collateral ratios based on the real-time Security Budget of the underlying chain. This proactive stance protects protocols from cascading liquidations during periods of network stress.
| Metric | Financial Impact |
| Staking Concentration | Liquidity risk assessment |
| Unbonding Period | Collateral release latency |
| Network Throughput | Execution slippage modeling |
The industry now utilizes sophisticated Security Oracles that feed network health data into decentralized option vaults. These vaults dynamically rebalance positions, shifting capital to safer networks when security metrics drop below predefined thresholds. This approach transforms passive security monitoring into active risk management, allowing participants to hedge against infrastructure failure with the same precision applied to price volatility.

Evolution
The transition from rudimentary hashrate tracking to complex multi-factor analysis marks the maturity of decentralized infrastructure.
Early systems relied on simplistic indicators that failed to capture the nuances of economic attacks, where actors leverage financial derivatives to profit from network instability. Modern frameworks now account for MEV-Boost and other validator-level extraction techniques that directly impact network integrity.
- Staking Yields are now correlated with security, as higher rewards incentivize greater participation and resilience.
- Protocol Governance has evolved to incorporate security metrics into automated upgrade proposals.
- Cross-Chain Bridges now utilize external security data to pause transfers during detected network instability.
Modern security frameworks integrate economic incentive structures to model adversarial strategies beyond simple computational power.
The focus has shifted toward Resilience Testing, where protocols simulate various attack vectors to determine their breaking points. This shift mirrors developments in classical systems engineering, where stress testing is a requirement for operational deployment. As the industry moves toward modular blockchain architectures, these metrics are becoming increasingly specialized, targeting the unique security properties of rollups and shared security layers.

Horizon
Future developments in Network Security Metrics will likely center on predictive modeling and automated incident response.
The integration of artificial intelligence will enable the identification of subtle patterns in validator behavior that precede coordinated attacks. This move toward Autonomous Security will allow protocols to defend themselves by dynamically adjusting fee structures or validator sets in response to emerging threats.
| Future Metric | Anticipated Utility |
| Adversarial Simulation Score | Real-time vulnerability prediction |
| Validator Reputation Index | Consensus quality filtering |
| Cross-Protocol Contagion Risk | Systemic stability monitoring |
Expect to see the emergence of specialized insurance markets that underwrite risks based on these metrics. Traders will purchase protection against chain-specific security events, effectively turning network health into a tradable commodity. The ultimate goal is a self-healing financial system where security is not a constant state but an emergent property of active, incentive-aligned participation.
