Essence
The most critical point of failure in any decentralized options protocol is the price feed. A price feed vulnerability occurs when the external data source, known as an oracle, provides manipulated or incorrect price information to the smart contract. This data dictates the protocol’s core functions, including options pricing, collateral valuation, margin calls, and liquidation logic.
The integrity of the entire system collapses when this external data input is compromised.
For options, a price feed vulnerability presents a unique and severe systemic risk. Unlike spot markets where a temporary price spike might be quickly arbitraged, options protocols rely on continuous mark-to-market calculations. An options protocol must accurately determine the value of a position to assess collateral health and calculate margin requirements.
If an attacker can manipulate the underlying asset price reported by the oracle, they can force liquidations at incorrect prices or create arbitrage opportunities that drain the protocol’s liquidity pool. This is particularly dangerous for American-style options, where the ability to exercise at any time means an immediate price discrepancy can be exploited before an aggregation mechanism can correct itself.
Price feed vulnerabilities represent a single point of failure where external data manipulation can trigger catastrophic internal protocol logic, leading to systemic insolvency in options markets.

Origin
The price feed problem in decentralized finance emerged from the fundamental architectural shift away from centralized exchanges. In traditional finance, exchanges like CME or Cboe maintain internal, highly-regulated price discovery mechanisms. The price feed for derivatives on these platforms is a product of their internal order books and matching engines, creating a closed-loop system where manipulation is extremely costly and illegal.
Decentralized protocols, by design, cannot operate this way. They require external data from the real world, creating the “oracle problem.” Early iterations of DeFi protocols, particularly those in the yield farming and lending space, often relied on simple Time-Weighted Average Price (TWAP) oracles from single decentralized exchanges (DEXs) like Uniswap. The vulnerability was starkly exposed by flash loan attacks, where an attacker borrowed a large amount of capital, manipulated the price on a single low-liquidity DEX pool, and then used that manipulated price to execute a profitable trade against the vulnerable protocol before repaying the loan.
This demonstrated that a protocol’s security was only as strong as the weakest link in its data source chain.
Options protocols, requiring high-frequency updates and high-leverage positions, inherited this vulnerability. The initial solutions, which involved simply averaging prices from a small number of sources, proved insufficient against sophisticated adversaries. The design of options contracts, with their non-linear payoff structures and sensitivity to volatility, made them particularly susceptible to manipulation.
A small price change could trigger a large shift in the options’ delta, allowing an attacker to exploit the protocol’s internal risk engine.

Theory
The theoretical foundation of price feed vulnerabilities rests on the concept of economic security and data latency. An oracle’s security can be measured by the cost required to successfully manipulate its data versus the potential profit from that manipulation. For options protocols, this cost calculation is complex because the attack vector targets the options’ pricing model rather than the underlying asset itself.
The core vulnerability for options protocols lies in the non-linear relationship between the underlying asset price and the option’s value, as modeled by the Black-Scholes formula and its derivatives. A sudden, temporary price spike or dip can disproportionately affect the options’ calculated value and Greeks, particularly delta and gamma. An attacker who understands this relationship can precisely time a flash loan attack to exploit this non-linearity.
The protocol’s margin engine, operating on the manipulated price, may incorrectly calculate collateral requirements, allowing the attacker to purchase options at a discount or liquidate positions at an inflated price.

Oracle Data Aggregation Mechanisms
Different oracle designs offer varying levels of security and speed. The choice of mechanism directly impacts the protocol’s vulnerability profile:
- TWAP (Time-Weighted Average Price): This mechanism calculates the average price over a specific time interval. While effective against instantaneous flash loan attacks, it remains vulnerable to “drip feeding” attacks, where an attacker slowly manipulates the price over a longer period to skew the average. For options, this slow manipulation can still lead to mispricing over time.
- VWAP (Volume-Weighted Average Price): This mechanism weights prices based on trading volume. It is more resistant to low-volume manipulations but can be expensive to calculate on-chain and still vulnerable to large-scale, high-volume manipulation during periods of low liquidity.
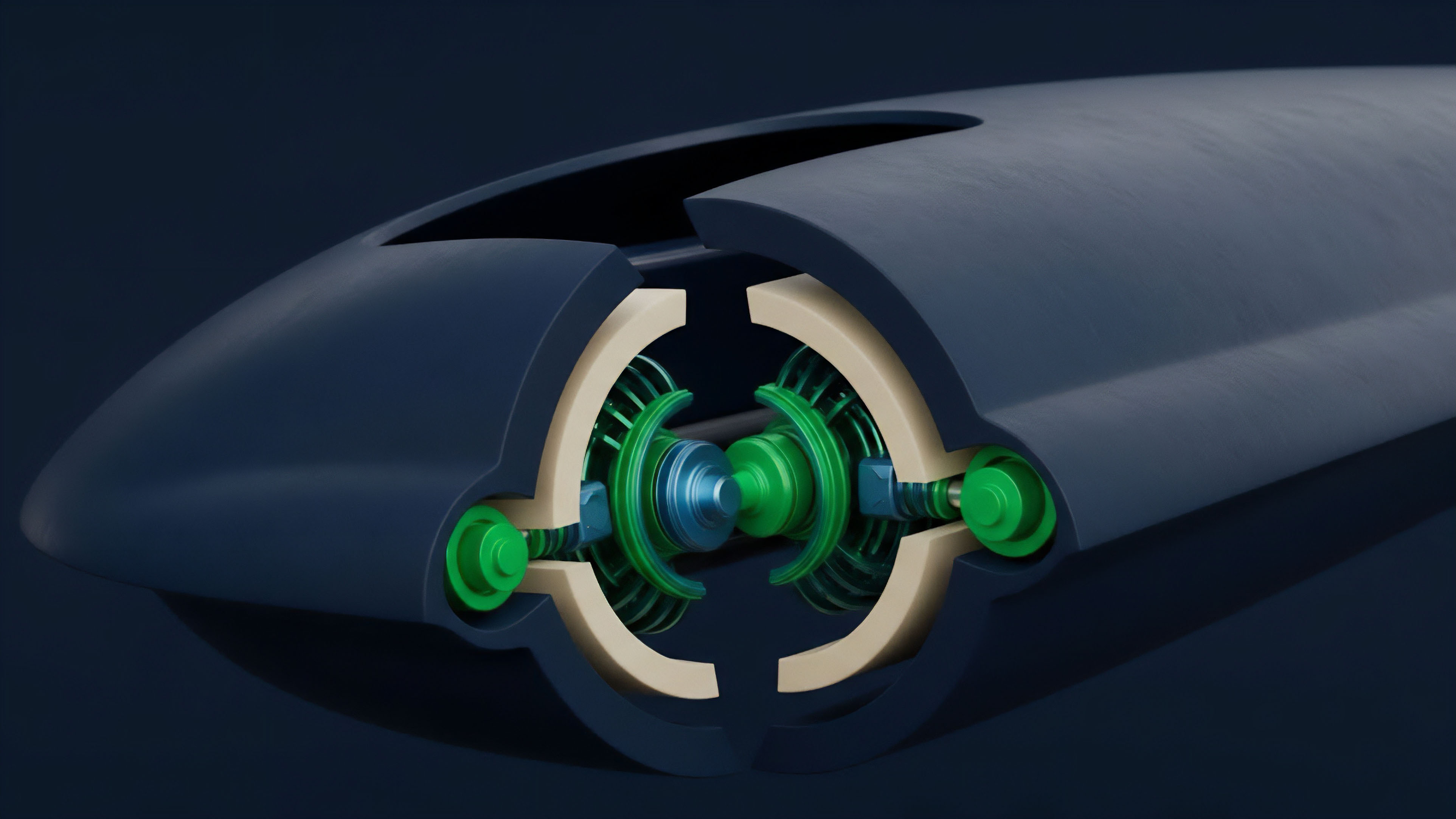
- Decentralized Oracle Networks (DONs): These networks aggregate data from multiple independent sources and nodes. The security model relies on the assumption that a majority of nodes are honest. The vulnerability here shifts to the governance of the DON itself and the cost of corrupting a sufficient number of nodes.

Flash Loan Exploits and Option Greeks
The flash loan attack vector against options protocols specifically targets the relationship between the oracle price and the calculated option Greeks. An attacker performs a sequence of actions:
- Acquire a flash loan to purchase a large amount of the underlying asset on a single exchange.
- This purchase causes a temporary, artificial spike in the asset’s price on that exchange.
- The oracle, which may be sampling from this single exchange, reports the manipulated price to the options protocol.
- The options protocol’s risk engine calculates new Greeks based on this manipulated price. The options’ delta changes, potentially altering margin requirements or allowing for profitable exercise.
- The attacker executes a profitable trade against the options protocol (e.g. buying underpriced options or liquidating positions at a favorable price).
- The attacker repays the flash loan, returning the market price to normal. The protocol is left with a loss, often resulting in bad debt or protocol insolvency.
The core issue is a data integrity failure. The protocol’s logic is sound, but its input data is corrupted. The challenge in options is that the price of the option itself is derived from a complex model, making the impact of bad data far more severe than in a simple lending protocol.

Approach
Current solutions to price feed vulnerabilities in options protocols focus on increasing the cost of attack and reducing data latency. The primary strategy involves moving away from single-source oracles to decentralized aggregation mechanisms.

Decentralized Aggregation and Economic Security
The industry standard, popularized by Chainlink, involves a network of independent nodes (DONs) that source data from multiple exchanges and data providers. These nodes submit data to an aggregation contract, which calculates a median or volume-weighted average. This approach significantly raises the cost of manipulation, requiring an attacker to compromise a majority of nodes or manipulate multiple exchanges simultaneously.
For options protocols, this approach is refined by adjusting the update frequency. High-frequency options trading requires low latency, meaning a protocol might update its price feed every few seconds. This increases the window of vulnerability, as an attacker only needs to hold the manipulated price for a short period to execute a profitable trade.
The trade-off between speed and security is constant. A protocol must choose whether to prioritize low latency for better user experience or higher security through slower updates and more robust aggregation.

Risk Management Frameworks and Circuit Breakers
A more sophisticated approach involves integrating risk management logic directly into the protocol’s architecture. Instead of blindly trusting the oracle feed, the protocol applies sanity checks and circuit breakers. These mechanisms monitor the incoming data for anomalies, such as extreme price volatility or sudden deviations from historical averages.
If an anomaly is detected, the protocol can temporarily pause liquidations, freeze new positions, or switch to a fallback mechanism. This adds a layer of defense against rapid, high-impact attacks.
| Mechanism | Pros | Cons | Risk Profile |
|---|---|---|---|
| Single Exchange TWAP | Low cost, simple implementation | High manipulation risk via flash loans; single point of failure | High vulnerability to high-leverage attacks |
| Multi-Source Aggregation (DON) | High security; resistance to single-exchange manipulation | Higher cost; increased latency; reliance on governance security | Lower vulnerability to flash loans; higher risk of data source collusion |
| On-Chain VWAP (Uniswap v3) | On-chain calculation; no external oracle dependency | High cost for frequent updates; potential for manipulation in low-liquidity pairs | Vulnerability tied to pool liquidity and trading volume |

Evolution
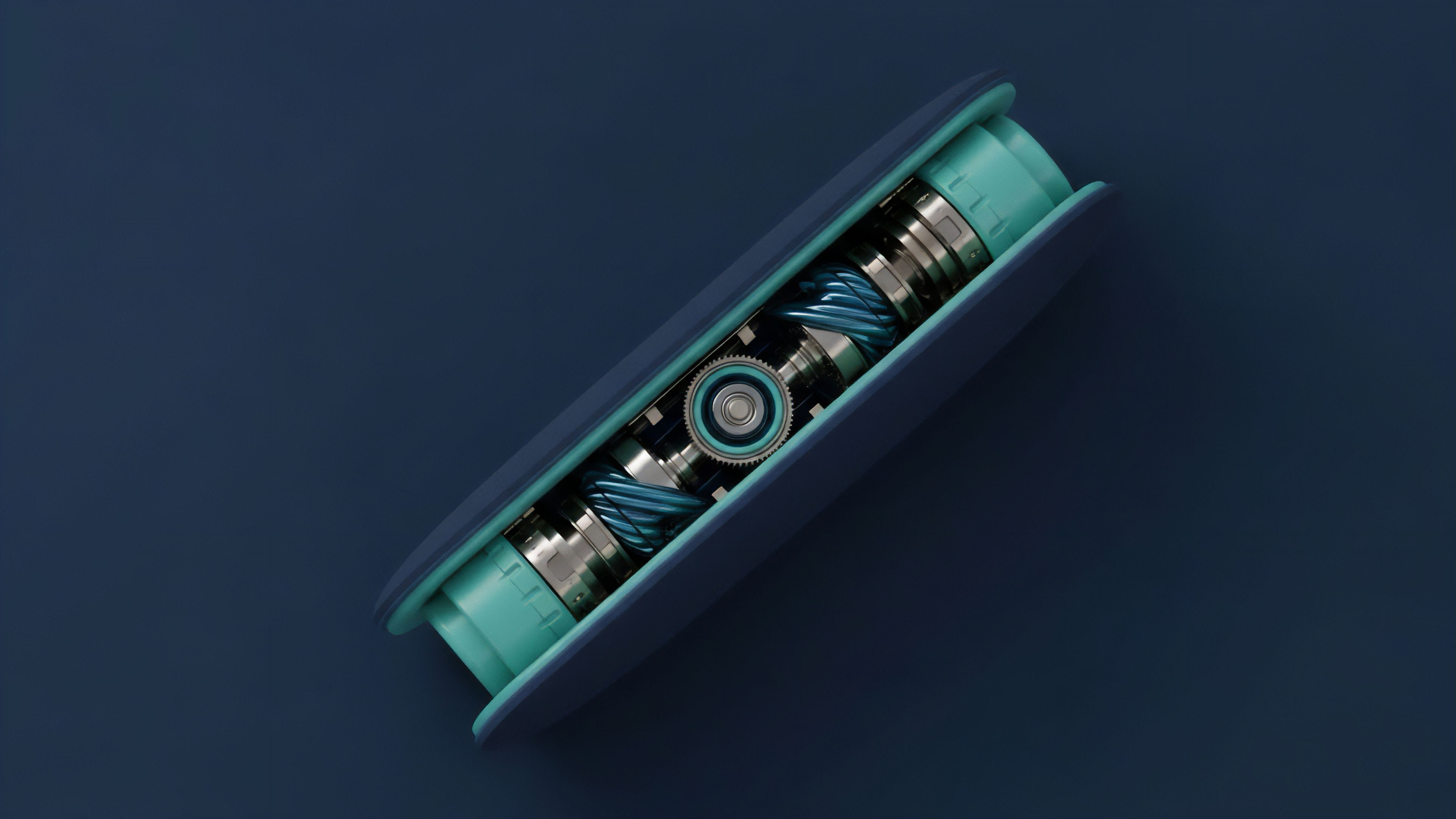
The evolution of price feed architecture for options protocols moves toward a hybrid model where external data is combined with internal protocol data and a more nuanced understanding of volatility. The industry has learned that relying solely on external feeds creates an exploitable dependency.
One significant development is the integration of volatility oracles. Options pricing is highly sensitive to implied volatility. A simple price feed for the underlying asset does not capture the full risk profile required for accurate options pricing.
Next-generation protocols are exploring methods to feed implied volatility data directly into the options pricing model, either by calculating it on-chain or sourcing it from specialized volatility oracles. This adds a layer of complexity to the attacker’s task, requiring them to manipulate both the spot price and the implied volatility simultaneously.
Another area of evolution involves the concept of “on-chain data validity.” Instead of accepting oracle data at face value, protocols are developing mechanisms to verify the data’s integrity. This includes using zero-knowledge proofs to verify data source authenticity or implementing governance mechanisms that allow users to challenge suspicious price updates. The goal is to move beyond passive data consumption to active data verification, creating a more resilient system where the cost of a successful attack increases exponentially with each layer of security added.
The future of options protocol security involves a shift from simply consuming external data to actively verifying data integrity through on-chain risk analysis and hybrid data models.

Horizon
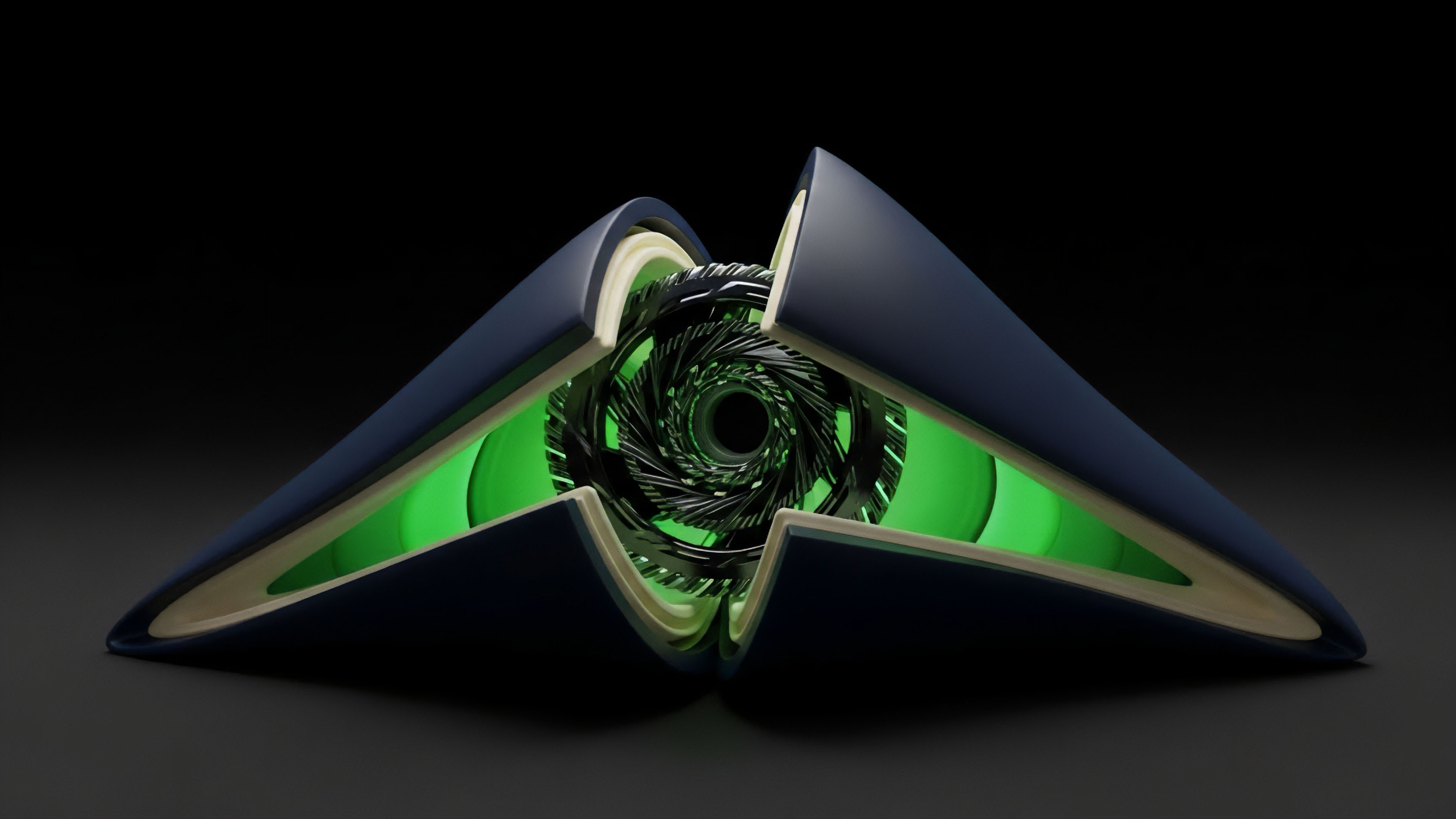
Looking ahead, the next generation of options protocol architecture will likely internalize price discovery to minimize external dependencies. The most resilient protocols may move toward a design where the price feed is derived from internal market dynamics and liquidity, rather than relying on external sources. This approach views the protocol’s own liquidity pools and order book as the primary source of truth, minimizing the impact of external market manipulation.
A further development involves “risk-adjusted data pricing.” In this model, protocols dynamically adjust the risk parameters of an options contract based on the perceived quality and cost of the oracle data. For example, if a protocol is using a low-cost, low-security oracle, it might increase margin requirements or decrease available leverage. Conversely, a high-cost, high-security feed would allow for higher leverage and tighter spreads.
This approach acknowledges that data quality is a variable cost and risk factor, rather than a fixed input. The challenge here is to create a dynamic pricing model that accurately reflects the real-time risk of the underlying oracle feed, potentially leading to a new class of financial instruments where data quality itself is a tradable asset.

The Challenge of Latency and On-Chain Settlement
The final challenge remains the conflict between speed and security. High-frequency options trading demands near-instantaneous price updates. The current state of decentralized oracle networks often introduces latency, as multiple nodes must agree on a price before it is finalized on-chain.
This latency creates arbitrage opportunities for sophisticated high-frequency traders who can execute trades on centralized exchanges before the decentralized protocol updates its price. The future requires solutions that bridge this latency gap without compromising security, perhaps through a combination of off-chain computation and on-chain verification.
The ultimate goal is to build a self-contained options market where price discovery is as robust as a centralized exchange, but with the transparency and resilience of a decentralized network. The systemic risk to DeFi remains significant as long as a single point of data input can bring down a multi-million dollar protocol.
Glossary

Data Feed Data Providers

Cryptographic Primitives Vulnerabilities

Oracle Price Feed Latency

Data Feed Architectures

Options Protocols

Margin Engine Risk

Protocol Composability Vulnerabilities

Implied Volatility
Compiler Vulnerabilities






