Essence
Decentralized Identity, or DID, represents a fundamental shift in digital trust models, moving control of personal data from centralized institutions to the individual user. In the context of decentralized finance, DID is not simply a tool for privacy; it is a critical infrastructure component for managing systemic risk and enabling capital efficiency in permissioned derivatives markets. A user’s identity becomes a set of cryptographic proofs, allowing them to selectively disclose verifiable credentials without revealing underlying personal information.
This capability is essential for bridging the gap between traditional financial institutions and decentralized protocols. The ability to verify specific attributes ⎊ such as accredited investor status, jurisdictional eligibility, or credit history ⎊ without requiring full know-your-customer (KYC) data disclosure changes the risk profile of options protocols. By enabling selective verification, DID facilitates the creation of differentiated liquidity pools, allowing protocols to segment their markets for specific user groups while remaining non-custodial and decentralized.
Decentralized Identity redefines trust in financial systems by allowing users to prove attributes without disclosing sensitive data, enabling compliance and risk management in permissioned DeFi.
This architecture allows for a new form of capital efficiency where risk is priced based on verifiable reputation rather than anonymous collateralization alone. The system design relies on a framework of issuers, holders, and verifiers, where issuers (like regulatory bodies or credit agencies) attest to a user’s attributes. The user (holder) then presents these proofs to a verifier (the options protocol) to gain access to specific financial products or lower collateral requirements.
The implications for derivatives markets are profound, as DID allows protocols to mitigate regulatory risk and onboard institutional capital without sacrificing the core tenets of decentralization.

Origin
The concept of self-sovereign identity (SSI) emerged from a long-standing dissatisfaction with centralized identity models, where users were forced to entrust sensitive data to large corporations and government databases. These centralized data silos became honeypots for hackers and single points of failure for entire systems.
The initial development of SSI focused on cryptographic key management and user-centric data storage, but lacked a truly decentralized, global trust anchor. The advent of blockchain technology provided the necessary foundation for this trust anchor. The immutability of blockchain ledgers offered a public, verifiable record of identity identifiers without storing the personal data itself.
The progression from early digital identity efforts to modern DID standards was driven by the need for interoperability and a shift from data ownership to data control. The World Wide Web Consortium (W3C) standardized the concept of Verifiable Credentials (VCs), defining a secure format for presenting cryptographic proof of claims. This standardization was critical for financial applications, allowing different protocols and jurisdictions to interpret the same set of identity data.
In the context of crypto derivatives, the need for DID became acute as DeFi protocols began to attract significant capital, prompting scrutiny from global regulators. The inability of early DeFi protocols to differentiate between retail and institutional users created a significant barrier to institutional adoption. DID emerged as a potential solution to this regulatory impasse, offering a pathway for protocols to enforce compliance without compromising the non-custodial nature of decentralized applications.

Theory
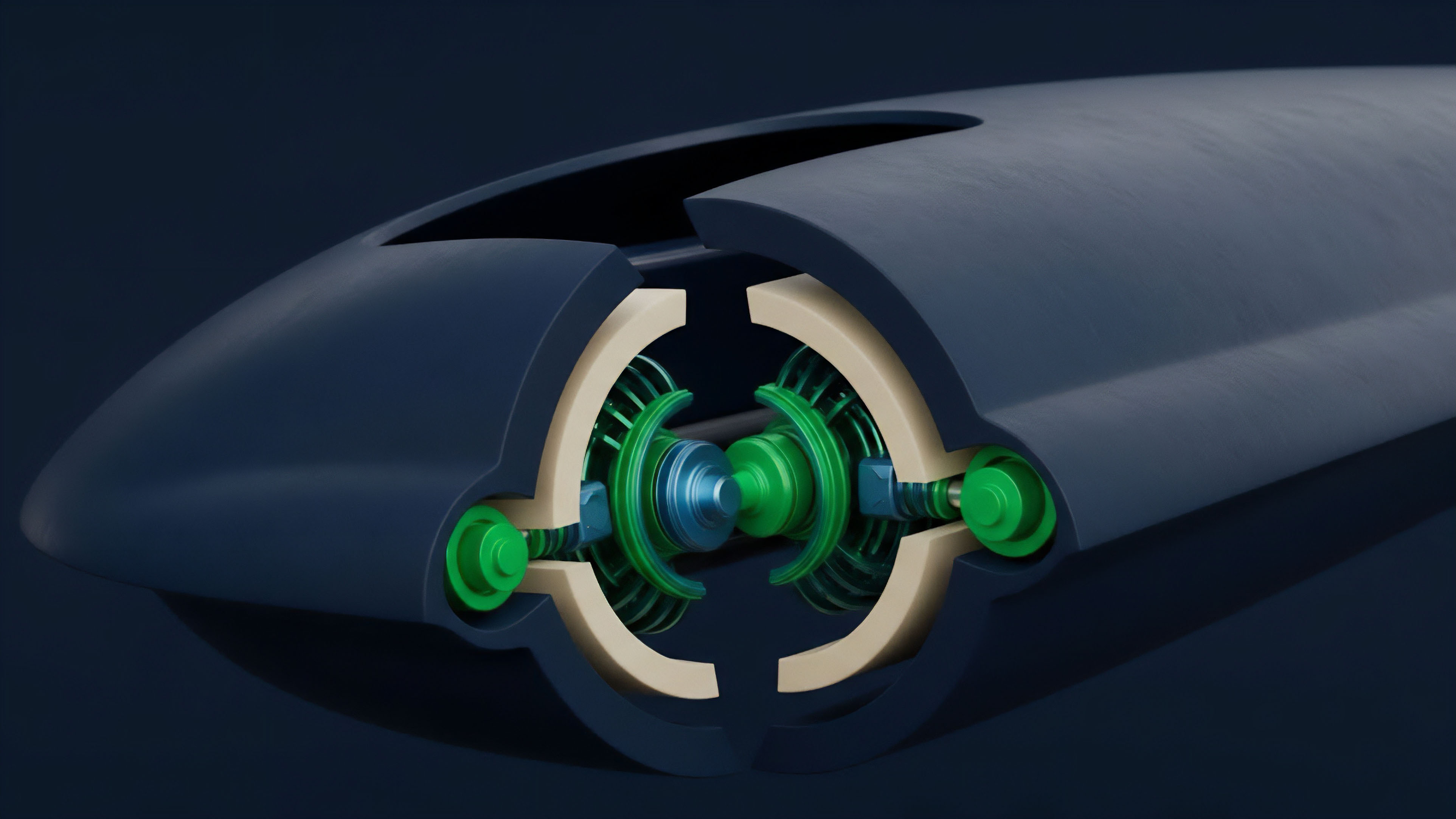
The theoretical foundation of DID in finance rests on a tripartite model of trust and information asymmetry. This model consists of three core components: the issuer, the holder, and the verifier. The issuer (e.g. a credit bureau or regulatory body) creates a verifiable credential, attesting to a specific attribute of the user.
The holder (the individual) stores this credential in a secure wallet. The verifier (the options protocol) receives the credential and validates it against the issuer’s public key on the blockchain. The core technical mechanism enabling this model is Zero-Knowledge Proofs (ZKPs).
ZKPs allow a holder to prove they possess a specific credential without revealing any information about the credential itself. For example, a user can prove they are over 18 without revealing their exact birthdate. In options markets, this capability is used to prove compliance with specific regulatory requirements, such as accredited investor status, without compromising the user’s privacy.
This approach transforms risk management by allowing protocols to enforce a “gate” on specific derivatives products. The risk profile of a protocol shifts from being a single, undifferentiated pool of capital to a segmented structure where different levels of risk tolerance and regulatory compliance can coexist.
The Impact on Protocol Physics
DID alters the physics of protocol design by introducing an external, verifiable constraint on internal state transitions. When a user interacts with a derivatives protocol, their identity credential acts as a precondition for specific actions. This impacts several key areas:
- Liquidation Engines: A user’s reputation score or collateral history, verifiable via DID, could be integrated into the liquidation mechanism. A user with a high reputation score might face different margin call thresholds or receive different collateral ratios compared to an anonymous user.
- Risk Pricing Models: The pricing of options relies heavily on implied volatility and risk assessment. If a protocol can verify that its users are sophisticated institutions, it changes the fundamental assumptions of market behavior and risk distribution, potentially altering the skew and kurtosis of volatility surfaces.
- Market Segmentation: DID allows for the creation of separate liquidity pools for different user classes. An institutional pool for accredited investors might offer lower collateral requirements for certain strategies, while a retail pool maintains stricter parameters. This fragmentation, while potentially reducing overall liquidity in any single pool, enables protocols to attract a broader range of capital.

Approach
Implementing DID in decentralized derivatives protocols requires a specific architectural approach that integrates identity verification into the smart contract logic. This process involves several layers of implementation, moving beyond simple wallet address authentication to a more robust, attribute-based access control system. The practical implementation of DID for derivatives protocols typically follows a clear process:
- Credential Issuance: A user first obtains a verifiable credential from a trusted issuer. This issuer could be a regulatory body, a credit scoring agency, or a specialized decentralized autonomous organization (DAO) focused on reputation.
- Credential Storage: The user stores this credential securely in a self-sovereign wallet. The credential is often linked to a non-transferable token, such as a Soulbound Token (SBT), which ties the identity to a specific wallet address without allowing transfer or sale.
- Verification on Protocol: When the user attempts to interact with the options protocol, they present the credential. The protocol’s smart contract logic then verifies the credential’s validity using ZKPs, checking for specific attributes required for access.
- Access Gating: Based on the verification result, the protocol grants or denies access to specific financial products or adjusts parameters like collateral requirements, leverage ratios, or fee structures.
Implementation Challenges and Market Microstructure
The primary challenge in this approach is maintaining capital efficiency. By segmenting liquidity pools, DID creates different risk environments within the same protocol. This fragmentation can lead to wider spreads and reduced depth in specific pools.
| Market Model Comparison | Permissionless DeFi | DID-Enabled Permissioned DeFi |
|---|---|---|
| User Access | Anonymous, open access for all users | Gated access based on verifiable credentials |
| Risk Profile | Uniform risk, higher collateral requirements for all users | Segmented risk, lower collateral for verified users |
| Liquidity | Consolidated in a single pool | Fragmented across different pools (e.g. retail vs. institutional) |
| Regulatory Compliance | Minimal or none; high regulatory risk | Enforced compliance through identity verification |
This architecture allows for a new form of market design where risk management is not solely reliant on over-collateralization. Instead, protocols can utilize DID to establish a user’s reputation, allowing for under-collateralized loans or options strategies based on a verifiable history of responsible financial behavior.

Evolution
The evolution of DID in crypto finance has progressed from a niche concept to a critical component for institutional adoption.
Early attempts at identity verification in DeFi were often rudimentary, relying on centralized KYC providers that violated the core tenets of decentralization. The current phase of development is characterized by the implementation of specific DID standards, focusing on a balance between privacy and compliance. The market is currently fragmented, with several different approaches to DID implementation.
Some protocols use a “whitelisting” approach, where specific addresses are pre-approved by a centralized entity. Other, more advanced protocols are experimenting with ZKP-based VCs and SBTs to create truly decentralized identity layers. This progression reflects a maturation of the space, moving from a binary choice (permissioned or permissionless) to a more nuanced spectrum where identity attributes determine access levels.
Regulatory Arbitrage and Market Dynamics
The current regulatory landscape for crypto derivatives is highly inconsistent across jurisdictions. DID offers a powerful tool for protocols to navigate this environment through regulatory arbitrage. By implementing DID, a protocol can effectively geofence its services, restricting access to users in specific jurisdictions where certain derivatives products are illegal.
The primary challenge in the current environment is achieving widespread adoption and interoperability. A single user needs to obtain credentials from multiple issuers to interact with various protocols. The lack of a unified standard for VCs and SBTs hinders network effects.
The “cold start problem” for identity systems remains significant; protocols are reluctant to adopt DID until there are enough verified users, and users are reluctant to obtain credentials until there are enough protocols requiring them.

Horizon
The future of DID in crypto options will be defined by the shift toward reputation-backed derivatives. As DID infrastructure matures, protocols will move beyond simple access gating to integrate identity data directly into their pricing models and risk engines.
This creates a new financial primitive where a user’s verifiable reputation score influences the terms of their financial interactions. The key innovation on the horizon is the development of a reputation-adjusted margin engine. In this model, a user with a strong, verifiable track record of successful trades and on-chain behavior would be able to access lower margin requirements or higher leverage for options trading.
Conversely, new or unverified users would be subject to higher collateral requirements. This system fundamentally alters the capital efficiency calculation for protocols. It allows for a move away from the current system of anonymous over-collateralization to a more efficient model where trust is quantified and priced.
Novel Conjecture and Instrument Design
A key conjecture is that DID will lead to the emergence of highly specialized, “gated” derivatives products where the options themselves are priced based on the collective reputation of the pool participants. This creates a feedback loop where verifiable credentials become a source of value accrual, incentivizing users to maintain positive on-chain behavior. The practical instrument to enable this future is a DID-Enabled Liquidation Engine (DLE). This engine would utilize ZKPs to verify a user’s reputation score without revealing their identity. The DLE would implement dynamic liquidation thresholds based on this score. For example, a user with a high reputation score might have their liquidation process triggered at a lower collateral ratio than a low-reputation user. This creates a tiered risk system where sophisticated, verified participants can operate with greater capital efficiency, while the protocol’s overall risk remains manageable through a reputation-based risk premium. The primary question for this future is whether a truly decentralized identity system can maintain its integrity against sophisticated sybil attacks and identity spoofing, particularly when significant financial incentives are at stake.

Glossary

Credential Storage
Identity Verification Solutions

Modular Identity Layer
Zero-Knowledge Identity Proofs
Soulbound Tokens
On-Chain Credit Identity
Decentralized Identity Primitives

Recursive Identity Proof
Leverage Ratios