
Essence
Data Sharing Agreements within decentralized derivatives markets function as the formal protocols governing the exchange of proprietary order flow, execution metrics, and risk parameters between market participants. These instruments define the terms under which liquidity providers, high-frequency trading firms, and decentralized exchange operators disclose or restrict access to transactional metadata.
Data Sharing Agreements standardize the technical and legal parameters for distributing sensitive order flow information across decentralized financial venues.
The primary utility of these arrangements lies in balancing the need for transparency in price discovery against the imperative to protect strategic trading alpha. By codifying how, when, and to whom execution data is transmitted, these agreements create a predictable environment for liquidity provision, mitigating the risks of predatory front-running while facilitating institutional-grade market making.
Origin
The genesis of Data Sharing Agreements traces back to the inherent limitations of public mempool transparency in early decentralized exchange architectures. As automated market makers struggled with adverse selection, sophisticated participants sought methods to internalize order flow, creating a demand for private, verifiable communication channels between venues and liquidity providers.
The shift from monolithic, public-only order books toward fragmented, multi-layered liquidity pools necessitated a framework to manage information asymmetry. Developers recognized that uncontrolled exposure of pending transactions invited toxic flow, undermining the viability of complex derivatives strategies. Consequently, the industry adopted concepts from traditional electronic communication networks, adapting them for blockchain-based settlement layers to govern how participants share intent and execution data without sacrificing decentralization.

Theory
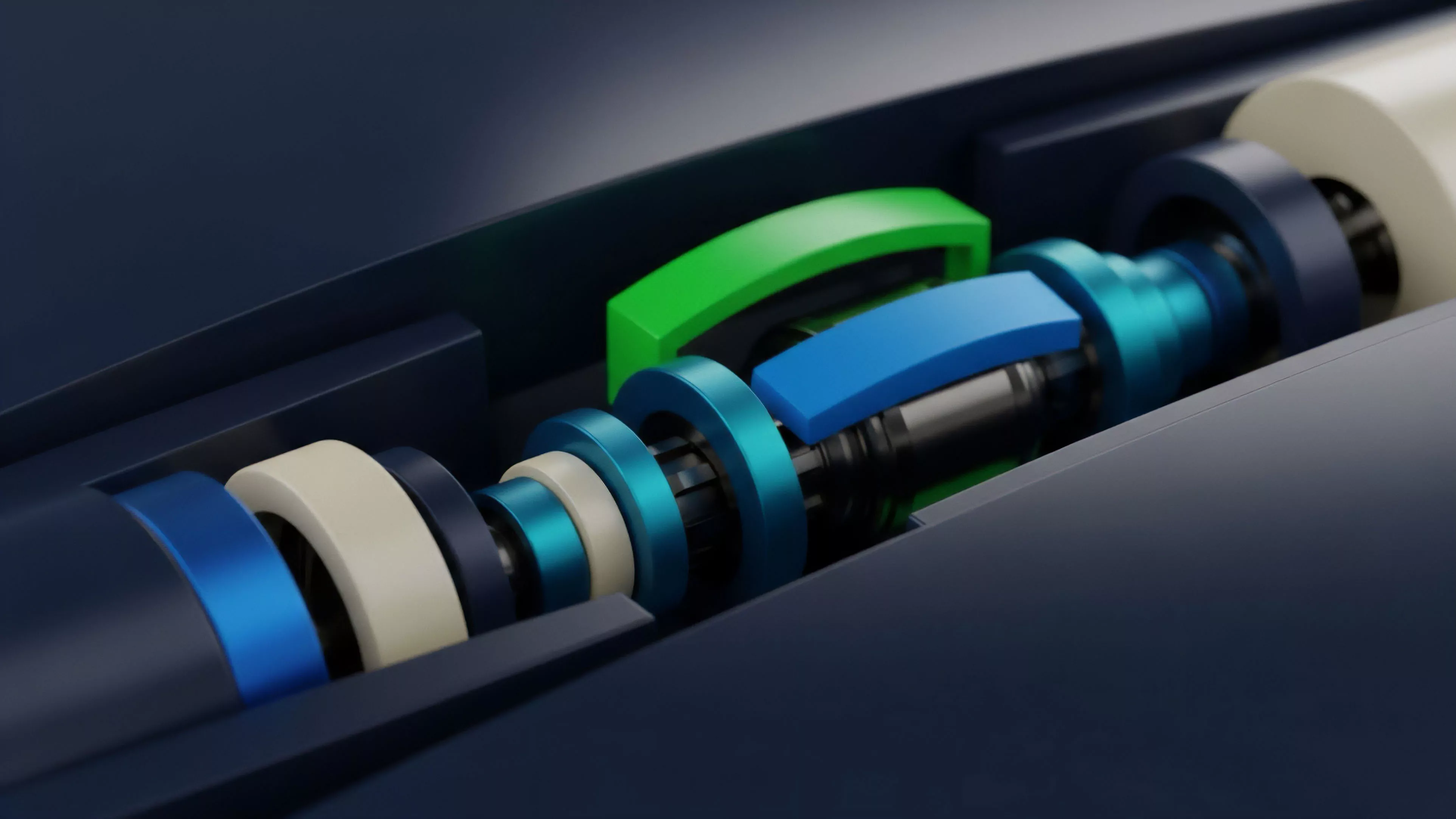
The mechanics of Data Sharing Agreements rely on cryptographic proofs and off-chain relay networks to enforce access control over sensitive order data.
These agreements function as a layer of abstraction between the raw mempool and the execution engine, ensuring that only authorized participants receive high-fidelity signals regarding order book depth, volatility skew, and potential liquidation events.
- Information Asymmetry Management: These agreements utilize zero-knowledge proofs to verify participant eligibility before granting access to granular order flow data.
- Latency Arbitration: By formalizing the delivery of data packets, these protocols minimize the advantages gained by participants exploiting network propagation delays.
- Execution Privacy: Encrypted data streams allow for the private negotiation of block space, reducing the impact of MEV-related exploitation on derivative pricing.
The structural integrity of derivative pricing depends on the controlled dissemination of order flow data through verifiable cryptographic channels.
Mathematical modeling of these agreements involves analyzing the trade-offs between information leakage and market efficiency. When data access is too restrictive, price discovery slows, leading to wider spreads. When access is too broad, the protocol becomes vulnerable to adversarial extraction.
The optimal configuration requires a dynamic balance, often modeled using game-theoretic frameworks where the cost of data access is tied to the liquidity provided by the participant.
| Mechanism | Function | Risk Factor |
|---|---|---|
| Zero-Knowledge Relays | Anonymizes order origin | Complexity overhead |
| Time-Locked Feeds | Prevents front-running | Latency jitter |
| Tiered Access Keys | Segmented data distribution | Centralization bias |

Approach
Current implementations prioritize the development of decentralized sequencers and private mempools to execute Data Sharing Agreements. Market participants now utilize off-chain computation to process high-frequency signals, submitting only the final state transitions to the mainnet. This methodology allows for the preservation of confidentiality for institutional strategies while maintaining the trustless nature of the underlying protocol.
The technical architecture frequently involves a governance-controlled registry that manages the credentials for data consumers. This registry ensures that participants contributing to market stability ⎊ such as market makers providing tight bid-ask spreads ⎊ receive priority access to order flow, creating a feedback loop that rewards liquidity provision while penalizing extractive behaviors.

Evolution
The progression of these agreements reflects the maturation of decentralized derivatives from experimental primitives to robust financial infrastructure. Early iterations relied on rudimentary allow-lists, which were susceptible to sybil attacks and lack of transparency.
Modern iterations utilize on-chain governance to dynamically adjust access rights based on real-time performance metrics and historical participation data.
Market evolution drives the transition from static access control toward algorithmic, performance-based data distribution models.
This shift has enabled the rise of institutional-grade options protocols that can handle sophisticated hedging strategies. By evolving beyond simple visibility controls, these agreements now incorporate complex incentive structures that align the interests of liquidity providers with the broader health of the protocol. The integration of reputation-based systems has replaced rigid gatekeeping, allowing for a more fluid and resilient market structure.
| Phase | Primary Focus | Outcome |
|---|---|---|
| Genesis | Public mempool access | High toxicity |
| Transition | Private relay networks | Reduced front-running |
| Maturity | Algorithmic reputation systems | Institutional participation |

Horizon
The future of Data Sharing Agreements lies in the intersection of fully homomorphic encryption and cross-chain liquidity aggregation. Future protocols will likely allow for the computation of global order book statistics without ever decrypting individual orders, fundamentally changing the economics of data availability. This advancement will enable the creation of truly global, unified derivatives markets that operate with complete privacy yet remain perfectly synchronized.
As these systems scale, the challenge will transition from managing individual protocol data to orchestrating interoperability across disparate decentralized financial ecosystems. The next generation of agreements will focus on standardized, cross-chain data primitives, allowing participants to leverage execution signals across multiple networks simultaneously. This architecture will define the next phase of decentralized finance, where information flow becomes the primary driver of capital efficiency and market stability.
