Essence
The core risk, which we define as ZK Solvency Opacity, is the systemic hazard introduced when zero-knowledge proofs (ZKPs) are applied to the critical functions of a decentralized derivatives platform, specifically margin maintenance and collateral auditing. While ZKPs successfully provide transactional privacy by allowing a prover to confirm the validity of a computation ⎊ such as a user’s margin ratio being above the liquidation threshold ⎊ without revealing the exact size of their collateral or position, this opacity simultaneously obstructs real-time, public verification of the protocol’s overall solvency.
ZK Solvency Opacity is the fundamental trade-off between user-level financial privacy and the systemic auditability of a decentralized derivatives exchange’s total collateral pool and counterparty risk exposure.
This paradox is particularly acute in crypto options and perpetual futures markets. These instruments are inherently leveraged, making the accurate and timely assessment of aggregate risk a non-negotiable requirement for system stability. When the sum of all liabilities and assets held by a market maker or a centralized exchange operating on a ZK-Rollup is only verifiable via a succinct proof, the external observer ⎊ or even a governance mechanism ⎊ lacks the necessary visibility to detect systemic under-collateralization or a “death spiral” of cascading liquidations until the final proof fails, which is too late for preemptive action.
The financial system relies on observable, auditable state, and ZKPs deliberately mask that state to protect individual actors.

Foundational Conflict
The conflict is one of data rights versus system rights. Derivatives require a shared, transparent ledger of risk to function safely at scale. ZKPs fracture this transparency into individual, non-transferable proofs of correctness.
- Prover’s Goal To prove a statement: “My collateral Ci is greater than my margin requirement Mi” without revealing Ci or Mi.
- System’s Goal To prove the aggregate statement: “Total Assets sum Ai are greater than Total Liabilities sum Li” where Ai and Li are hidden variables, making the sum only verifiable through complex, computationally expensive aggregation proofs.
The inability to audit individual, large positions without a judicial subpoena or a catastrophic event creates a moral hazard for market makers and liquidity providers, potentially leading to risk-taking that would be instantly corrected in a transparent environment.
Origin
The genesis of ZK Solvency Opacity lies at the intersection of two distinct cryptographic breakthroughs and one fundamental market structure problem. The initial cryptographic concept was established in 1985 by Goldwasser, Micali, and Rackoff, defining the properties of zero-knowledge proofs: completeness, soundness, and zero-knowledge.
This was an academic curiosity until the rise of blockchain technology.
Technological Catalyst
The practical application in finance was accelerated by the need for scalability, leading to the development of ZK-Rollups. These Layer 2 solutions bundle thousands of off-chain transactions into a single, cryptographically valid proof posted to Layer 1, dramatically reducing cost and increasing throughput. Derivatives protocols, with their high volume of trades, quotes, and liquidations, became primary candidates for ZK-Rollup deployment, such as the early implementation by dYdX.

Financial History Rhyme
The risk itself is a modern recurrence of an old financial problem: the opaqueness of highly leveraged counterparty risk. Historically, crises like the Long-Term Capital Management (LTCM) collapse or the 2008 subprime mortgage crisis were driven by hidden, interconnected liabilities that were too complex to audit. In the decentralized context, ZKPs replace human complexity with cryptographic complexity.
The system proves correctness mathematically, but it does so without providing the raw data needed for human or regulatory oversight, creating a Hidden Leverage Paradox. The protocol’s soundness relies on the correctness of the proof system, while its financial stability depends on the hidden solvency of its participants, which the proof system is designed to conceal. This tension is the true origin of the risk.
Theory
The theoretical grounding of ZK Solvency Opacity resides in the gap between the cryptographic soundness property and the financial auditability requirement. The ZK system is theoretically sound if the statement being proven is true, meaning a fraudulent prover cannot convince an honest verifier except with negligible probability. The financial problem arises because the statement being proven ⎊ ”The sum of all collateral is greater than the sum of all open risk” ⎊ is a snapshot that is only as reliable as the underlying inputs and the proof generation process itself.
Protocol Physics and Proof Generation
The complexity of generating a ZK-proof for an options protocol’s entire state is immense. It requires proving the correct execution of a large circuit that includes:
- Correct calculation of all user margin balances.
- Accurate pricing of all open options positions (which requires feeding an implied volatility surface into the circuit).
- Correct execution of any liquidations based on the margin checks.
The slightest flaw in the circuit’s logic, or a vulnerability in the compiler that abstracts this logic, can be exploited to generate a valid proof for an invalid state. The zero-knowledge property then prevents external detection of this invalid state, transforming a minor smart contract bug into a systemic, undetectable solvency hole.
The computational cost and complexity of ZK proof generation for derivatives forces a reliance on a centralized or semi-centralized prover, transforming a cryptographic guarantee into a systems risk rooted in human trust.

Quantitative Finance Implications and Greeks
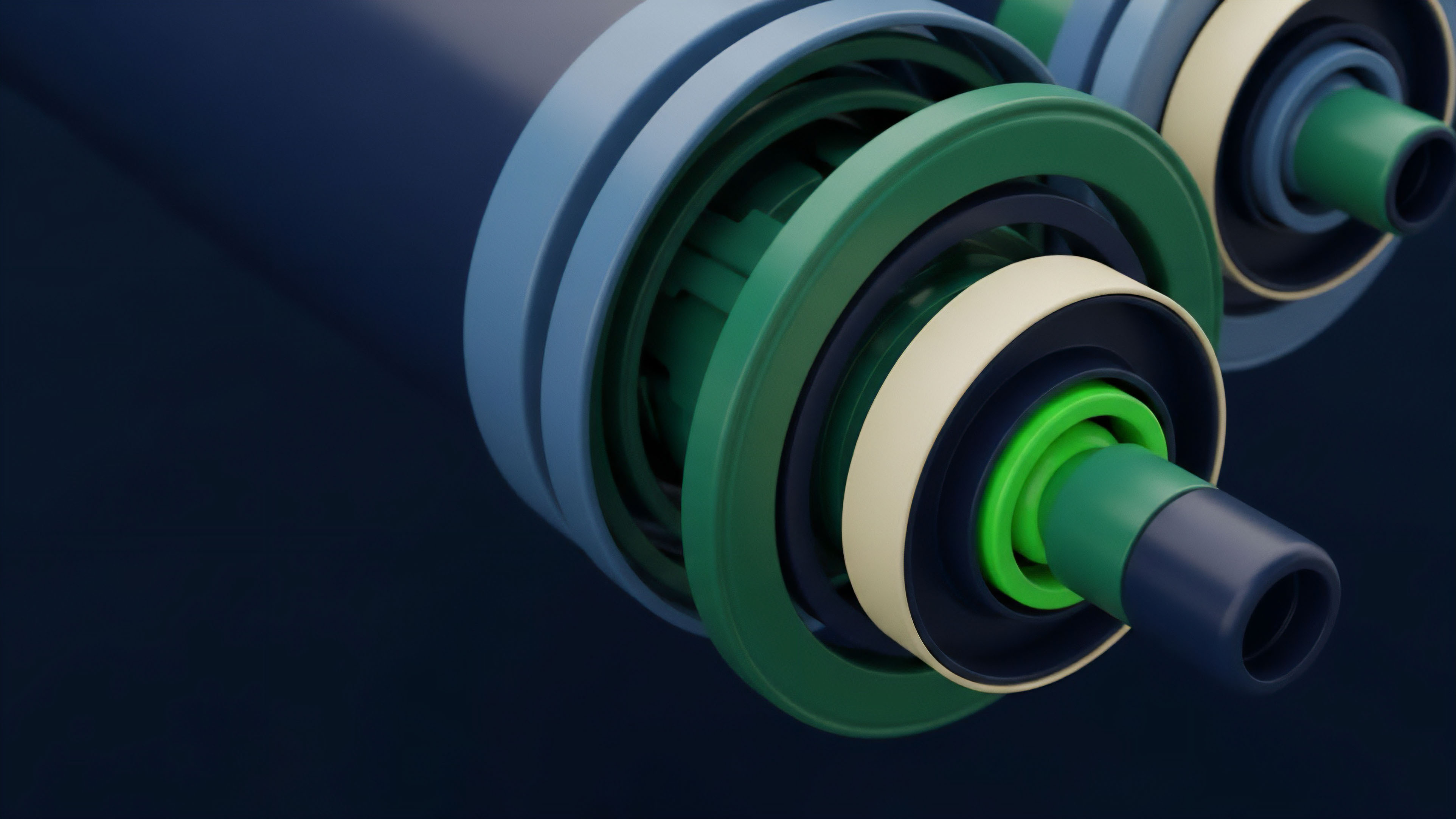
In options trading, the risk is quantified using the Greeks, specifically Delta and Vega. A market maker’s solvency is not simply a function of their cash balance; it is a function of their portfolio’s sensitivity to price changes and volatility. Proving solvency in a ZK context requires the prover to attest that their portfolio’s aggregate Delta and Vega exposure are within predefined, safe limits, without revealing the individual option strikes, expiries, or underlying quantities that constitute those Greeks.
This is mathematically challenging and computationally heavy, demanding highly specialized circuits. The critical point is that a cheating prover could exploit a flaw in the commitment scheme to create a proof that their portfolio is Delta-neutral, when in reality, they hold massive, unhedged tail risk, which would only be exposed when a large market move forces a margin call.
| Mechanism | Visibility | Liquidation Trigger | Systemic Risk Exposure |
|---|---|---|---|
| Centralized Exchange (CEX) | High (Internal Logs) | Real-time (Proprietary Risk Engine) | Counterparty Risk, Operational Failure |
| Transparent DeFi (L1/Optimistic) | High (On-chain) | Publicly verifiable (Smart Contract) | Front-running, MEV-based Liquidation |
| ZK Derivatives (ZK Solvency Opacity) | Low (Cryptographically Obscured) | Proof-based (Circuit Logic) | Hidden Insolvency, Cryptographic Trapdoor |
The philosophical digression here is that this tension is a direct parallel to the Heisenberg Uncertainty Principle in Finance. The act of measuring a system’s true, aggregate risk (auditability) fundamentally requires exposing the individual positions (privacy) that constitute that risk. You cannot have perfect, public auditability and perfect, private position-keeping simultaneously.
Approach
Current protocols attempting to address ZK Solvency Opacity typically employ a multi-layered approach, acknowledging that a single, monolithic ZK proof of solvency is too complex and brittle. The practical approach shifts the burden of proof from a single, final solvency check to a continuous, partial compliance audit.

Decentralized Compliance Auditing
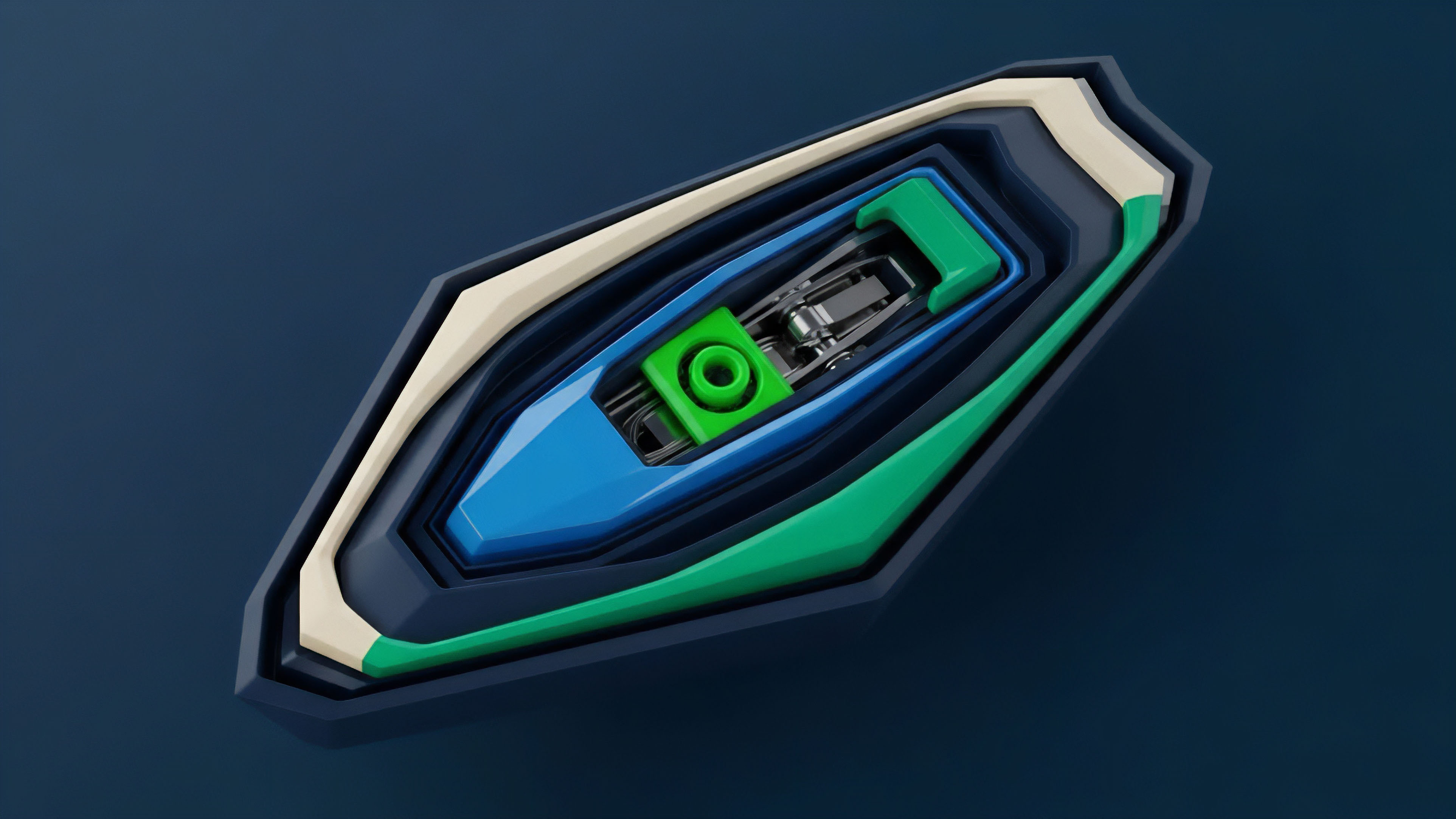
The most robust attempts rely on a Zero-Knowledge Compliance Audit (zkCA) layer. This is a set of verifiable constraints embedded into the circuit itself, which the prover must satisfy for every batch of transactions. The prover does not just prove transactions were valid; they also prove specific compliance constraints were met.
- Bounded Exposure Proofs The prover must generate a proof that no single user’s open position exceeds a system-defined maximum notional value, or that the aggregate market-wide Vega Exposure is below a predefined cap, all without revealing the underlying data.
- User-Verified Liabilities The system uses Merkle trees or similar structures, where each user receives a private commitment to their balance (liability). Users must be incentivized to check that their commitment is correctly included in the aggregate proof of liabilities, acting as decentralized, adversarial auditors. If users fail to check their commitments, the prover can simply zero out their liabilities in the circuit, artificially inflating the apparent solvency.
- Asset Proofs of Reserve The platform proves control over its collateral assets using cryptographic techniques like Schnorr signatures or other Proof of Knowledge protocols, confirming possession of private keys without revealing them. This is the simpler half of the solvency equation, as assets are public on Layer 1.
Circuit Security and Trusted Setup
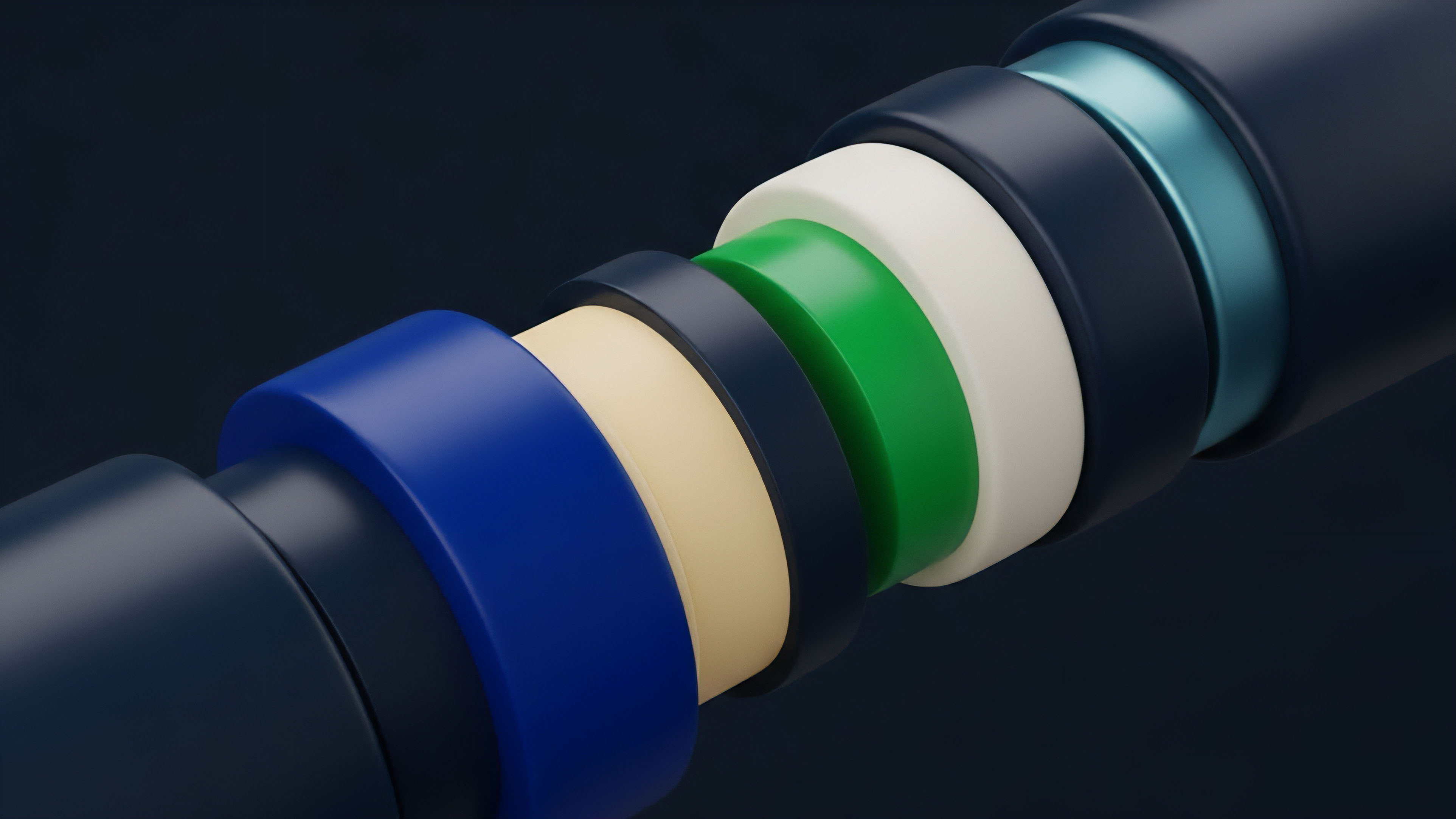
The technical approach is dominated by the choice of the ZK scheme. zk-SNARKs are succinct but often require a Trusted Setup ceremony, where initial parameters are generated and then the “toxic waste” (the secret seed) must be verifiably destroyed. A compromise of this initial setup creates a universal trapdoor, allowing a malicious prover to generate proofs for false statements forever. zk-STARKs avoid this setup, relying on stronger cryptographic assumptions and offering greater transparency, but often at the cost of larger proof sizes, complicating the Layer 1 verification cost. The architectural choice between these schemes is a direct trade-off between the risk of a single, catastrophic setup failure and the ongoing cost of verification.

Evolution
The evolution of ZK Solvency Opacity mitigation has moved from theoretical cryptographic constructs to pragmatic financial engineering solutions. The initial phase focused solely on scaling and transactional privacy. The current stage is defined by the struggle to satisfy the dual demand for “auditability + privacy”.

From Proof of Reserves to Proof of Solvency
The first generation of ZK solutions in centralized finance focused on a simple Proof of Reserves, proving control over assets. The second, more sophisticated generation, which applies directly to derivatives, moved to a full Proof of Solvency, proving Assets ≥ Liabilities. This shift requires homomorphic commitments (like Pedersen commitments) to allow the addition of hidden values (sum Ai and sum Li) and then proving the non-negativity of the difference using a ZK range proof.

The Rise of zk-EVMs and Composability
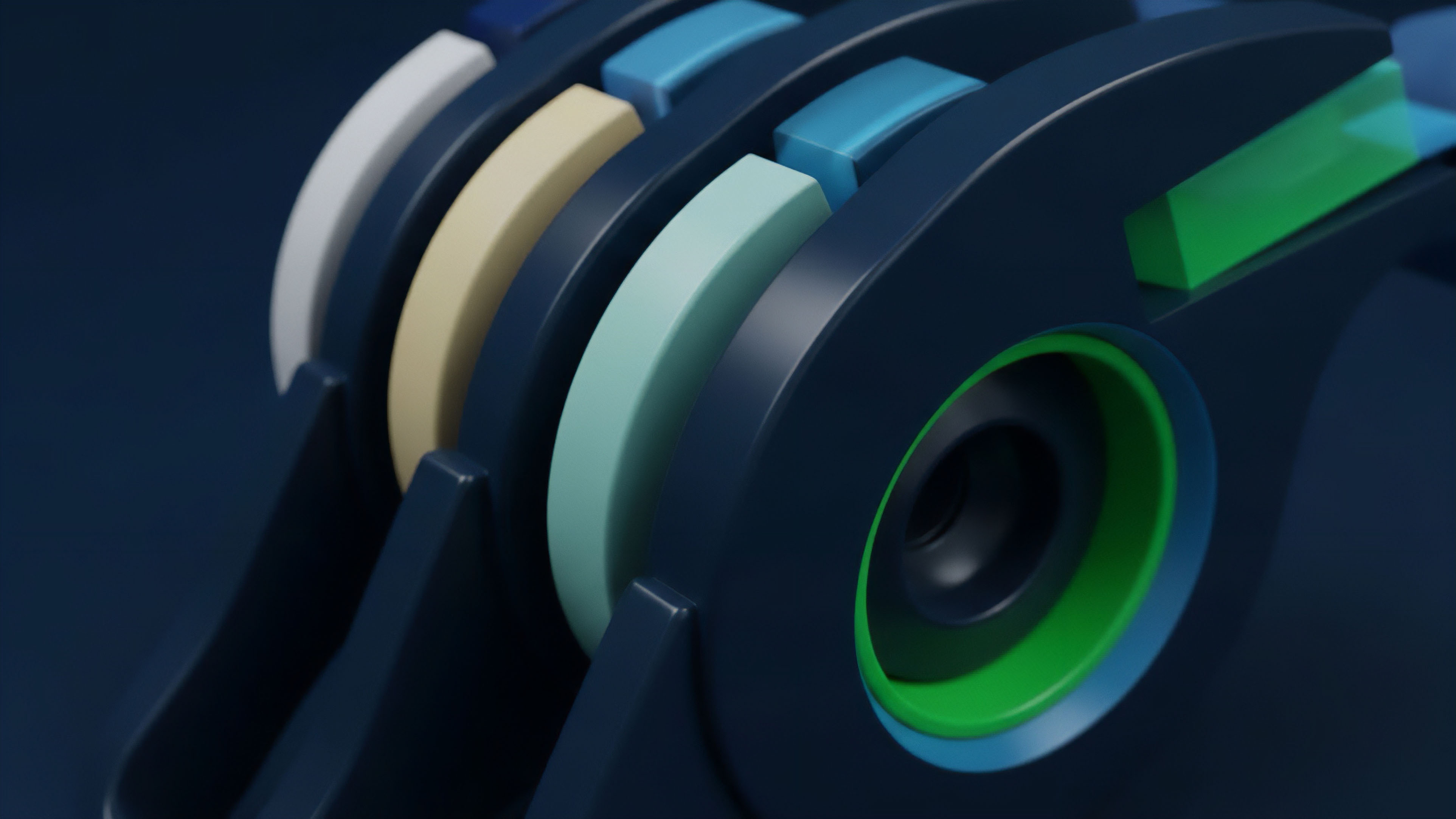
The technical challenge is transitioning from specialized ZK-Rollups, which only support simple token transfers or a limited set of financial primitives, to general-purpose zk-EVMs. zk-EVMs allow for the full complexity of an options smart contract ⎊ including sophisticated Black-Scholes or implied volatility surface logic ⎊ to be executed and proven in a ZK context. This capability introduces an order of magnitude more complexity into the circuit, which exponentially increases the surface area for logic bugs and exploits. However, it also enables Permissionless Composability, allowing a ZK options position to be used as collateral in another ZK lending protocol, potentially propagating the hidden solvency risk across the entire DeFi stack.
While zk-EVMs enable a new era of private financial composability, they also create the potential for a hidden, multi-protocol contagion event, where a solvency failure in one system propagates silently across the ecosystem.
The current trajectory is one of intense engineering focus on making the proving process itself transparent and decentralized. This involves techniques like Recursive ZKPs, where a proof can attest to the validity of another proof, allowing for a more modular and verifiable circuit design. The key strategic hurdle is the computational cost, which still results in higher gas fees for ZK-Rollups compared to their optimistic counterparts.

Horizon
The future trajectory for mitigating ZK Solvency Opacity is defined by the institutionalization of cryptographic auditing and the creation of a new risk primitive: the Auditability Oracle.

Systemic Implications and Behavioral Game Theory
The next generation of ZK derivatives protocols will not simply prove solvency; they will enforce a dynamic, verifiable risk policy. This moves the system from a passive accounting proof to an active risk management mechanism. The game theory shifts from an adversarial prover trying to cheat the verifier to a system where every actor’s behavior is constrained by the ZK circuit.
- Dynamic Margin Proving Instead of a fixed margin calculation, the ZK circuit will prove that a position’s liquidation price is not within a predefined percentage of the current mark price, effectively creating a verifiable Circuit-Based Buffer against sudden price movements.
- Collusion Resistance Protocols must implement mechanisms to detect and penalize asset pooling, where two insolvent entities temporarily combine capital to pass a solvency check. This requires embedding time-lock constraints and dependency graphs into the ZK circuit, increasing complexity but securing the integrity of the proof over time.

The Auditability Oracle Specification
The final state of ZK derivatives will likely involve a specialized oracle that feeds non-sensitive, aggregated risk data into the ZK circuit. This is not a price feed, but a Volatility Surface Commitment.
| Parameter | Data Type | ZK-Function | Risk Mitigation |
|---|---|---|---|
| Implied Volatility Surface | Cryptographic Commitment | Verifies Option Pricing Correctness | Prevents Solvency Manipulation via Mispricing |
| Aggregate Delta Exposure | Range Proof | Proves Portfolio Hedge within Bounds | Limits Hidden Market Directional Risk |
| System-Wide Liquidity Depth | Succinct Argument | Validates Liquidation Engine Capacity | Prevents Liquidity Crises and Contagion |
This Auditability Oracle transforms the problem from “How do we prove solvency without revealing data?” to “How do we reveal the minimum necessary risk parameters to secure the system, while keeping the user data private?” This is the necessary trade-off for scaling decentralized finance into a robust, institutional-grade derivatives market. The focus shifts from protecting the user from the market to protecting the market from the user’s hidden leverage.

Glossary

Zero Knowledge Range Proof
Position Integrity Proof

Exercise Logic Proof

Fraud Proof Systems

Liquidation Trigger Proof

Gamma Vega Exposure Proof
Proof of Validity

Zero Knowledge Execution Environments

Proof Verification Overhead