
Essence
The existence of Cryptographic Solvency establishes a mathematical guarantee that a financial entity maintains sufficient assets to meet all outstanding obligations. This state of verifiable liquidity relies on public-key cryptography to prove ownership of on-chain assets while simultaneously proving the total volume of user liabilities. Traditional finance relies on periodic audits by centralized third parties.
Digital asset markets require a continuous, trustless mechanism to prevent fractional reserve practices.

Mathematical Verification of Reserves
The architecture of Cryptographic Solvency functions through the public disclosure of wallet addresses and the signing of messages to prove control over the underlying capital. This process ensures that the reported assets are not fictitious or double-counted across multiple entities. By linking on-chain balances to a specific entity, the market can verify the asset side of the balance sheet with absolute certainty.
Mathematical certainty replaces institutional trust in the verification of digital asset reserves.
Liability Attestation
Proving assets is only half of the equation. Cryptographic Solvency requires a corresponding proof of liabilities. This involves aggregating all user balances into a cryptographic commitment, often using a Merkle Tree structure.
Users can independently verify that their specific balance is included in the total liability figure without compromising their privacy. This dual-sided verification prevents the concealment of debts, which is the primary cause of insolvency in centralized financial systems.
- Verifiability allows any participant to check the solvency status without specialized permissions.
- Privacy ensures that individual user data and specific trade positions remain shielded from public view.
- Immutability prevents the retroactive alteration of financial records to hide losses or deficits.
- Frequency enables near-instantaneous updates to the solvency state rather than waiting for quarterly reports.

Origin
The demand for Cryptographic Solvency emerged from the catastrophic failures of opaque financial intermediaries. Early digital asset exchanges operated with zero public accountability, leading to massive losses during market contractions. The transition toward mathematical proofs represents a survival response to systemic distrust.

Historical Failures and the Transparency Mandate
The collapse of early exchanges like Mt. Gox highlighted the danger of trusting centralized ledgers. These entities often operated as “black boxes,” where user deposits were commingled with corporate funds. When liquidity crises occurred, users discovered that the exchange held only a fraction of the assets it claimed.
This prompted the development of Proof of Reserves (PoR) as a primitive form of Cryptographic Solvency.
| Era | Verification Model | Primary Weakness |
|---|---|---|
| Early Exchange Era | Internal Ledgers | Total Opacity |
| Post-Mt. Gox | Manual Audits | Time Lag and Human Error |
| Modern Era | Merkle Tree Proofs | Static Snapshots |
| Next Generation | Zero-Knowledge Solvency | Computational Complexity |

The 2022 Liquidity Crisis
The failure of several major lending platforms and exchanges in 2022 served as the final catalyst for the widespread adoption of Cryptographic Solvency. These events proved that even large, seemingly well-capitalized firms could be insolvent due to hidden liabilities and risky re-hypothecation. The industry realized that trust is a liability, and only cryptographic proof can provide the resilience needed for global financial adoption.

Theory
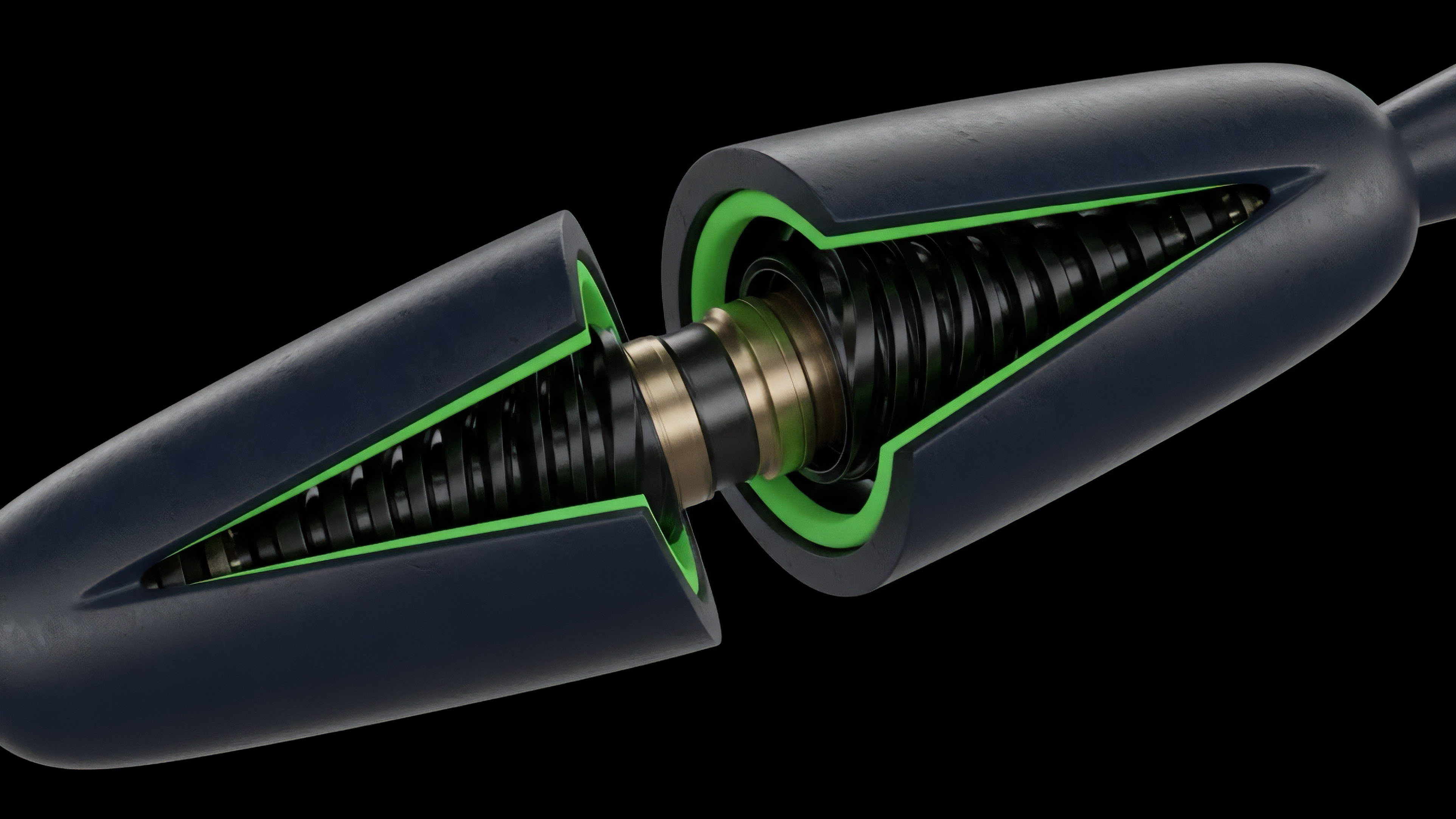
The technical architecture of Cryptographic Solvency utilizes Merkle Trees to aggregate user balances into a single root hash.
Each user can verify their inclusion in the tree without exposing the balances of others. Zero-knowledge proofs (zk-SNARKs) allow an exchange to prove that the sum of all leaf nodes equals the total liability reported, and that each leaf node is non-negative.
The summation of individual liabilities must equal the root hash of the state commitment.

Merkle Sum Trees
A Merkle Sum Tree is a specialized data structure where each node contains both a hash and a value representing the sum of the values of its children. In the context of Cryptographic Solvency, the leaf nodes are individual user balances. The root of the tree represents the total liabilities of the exchange.
This structure allows for efficient auditing. Just as the second law of thermodynamics dictates that entropy in a closed system must increase, the total liabilities in a solvent system must never exceed the verified assets.

Zero Knowledge Proofs for Privacy
The use of zk-SNARKs solves the tension between transparency and privacy. An exchange can generate a proof that it is solvent without revealing the total number of users, the size of individual accounts, or the specific addresses where funds are held. This prevents competitors from scraping sensitive business data while still providing users with the assurance that the entity is fully collateralized.
- Setup involves creating the cryptographic parameters for the proof system.
- Commitment requires the exchange to publish the root of the liability tree and the asset addresses.
- Generation produces a succinct proof that the assets are greater than or equal to the liabilities.
- Verification allows anyone to confirm the proof using the public parameters.

Approach
Entities implement Cryptographic Solvency through various technical paths. Merkle Tree proofs allow individual users to confirm their balance is part of the total. Zero-knowledge proofs enhance this by concealing individual data while proving the aggregate truth.

Implementation Procedures
The current execution of Cryptographic Solvency involves a multi-step process. First, the entity must perform an on-chain asset attestation. This is followed by a liability summation.
The final step is the publication of the proof, which can be verified by third-party tools or the users themselves.
| Feature | Merkle Tree Proof | ZK-SNARK Proof |
| Privacy Level | Partial | Full |
| User Verification | Manual/Self-Service | Automated |
| Computational Cost | Low | High |
| Audit Frequency | Periodic | Continuous |

Risk Mitigation in Execution
The effectiveness of Cryptographic Solvency depends on the integrity of the data provided. If an exchange excludes certain liabilities from the tree, the proof is invalid. To counter this, “liability sampling” can be used, where users are encouraged to check their balances frequently.
Any discrepancy between the user’s balance and the tree inclusion serves as a “canary in the coal mine” for the entire system.
Real-time solvency monitoring reduces systemic contagion risks within interconnected liquidity pools.

Evolution
The methodology has moved from simple wallet signatures to complex, privacy-preserving proofs. Initial versions were static and easily manipulated. Current iterations use continuous monitoring to prevent temporary asset borrowing.

From Static to Continuous Attestation
Early proofs were mere snapshots in time. An exchange could borrow assets for a few hours to pass an audit and then return them. This “window dressing” made early Cryptographic Solvency attempts unreliable.
The evolution toward continuous attestation involves linking the solvency proof to real-time blockchain data, making it impossible to hide deficits through temporary loans.

Institutional Integration
As the digital asset market matures, Cryptographic Solvency is moving from a voluntary feature to a structural requirement. Institutional investors now demand these proofs as part of their due diligence process. This shift is forcing centralized entities to adopt decentralized verification methods, blurring the line between traditional and on-chain finance.

Horizon
Future developments point toward a unified, cross-protocol solvency standard.
This will enable real-time risk assessment across the entire decentralized finance landscape. Regulatory integration will likely follow as these proofs become the industry standard.

Cross-Chain Solvency Standards
The next phase of Cryptographic Solvency involves tracking liabilities across multiple blockchains. As users move assets through bridges and layer-2 solutions, the ability to prove solvency becomes more complex. Unified protocols will emerge to aggregate these fragmented balances into a single, verifiable proof of health.

The Role of Smart Contract Jurisdictions
Eventually, Cryptographic Solvency will be integrated directly into the smart contracts that govern exchange operations. Instead of a human auditor, the code itself will prevent withdrawals if the solvency ratio falls below a certain threshold. This transition from “don’t be evil” to “can’t be evil” is the ultimate trajectory of the digital financial system.
- Real-time Proofs will become the default state for all reputable financial intermediaries.
- Regulatory Mandates will likely replace traditional reporting with cryptographic requirements.
- Self-Custody Integration will allow users to maintain control while participating in centralized liquidity.
- Insurance Markets will use these proofs to price risk for exchange-traded products.

Glossary

Cryptographic Security

Privacy Preserving Proofs

Asset Liability Management

Merkle Tree

Institutional Grade Transparency

Fractional Reserve Prevention

Liability Attestation

Cryptographic Commitment

Real-Time Attestation






