Essence of Zero-Knowledge Contingent Claims
The Zero-Knowledge Contingent Claim (ZKCC) represents a fundamental architectural shift in decentralized finance, defining a derivative instrument whose payoff is verifiable without revealing the data that determines the outcome. It is the cryptographic primitive that reconciles the adversarial tension between on-chain transparency and institutional-grade market privacy. A contingent claim, fundamentally, is an agreement whose execution is conditional on a future state ⎊ an option being the archetypal financial structure.
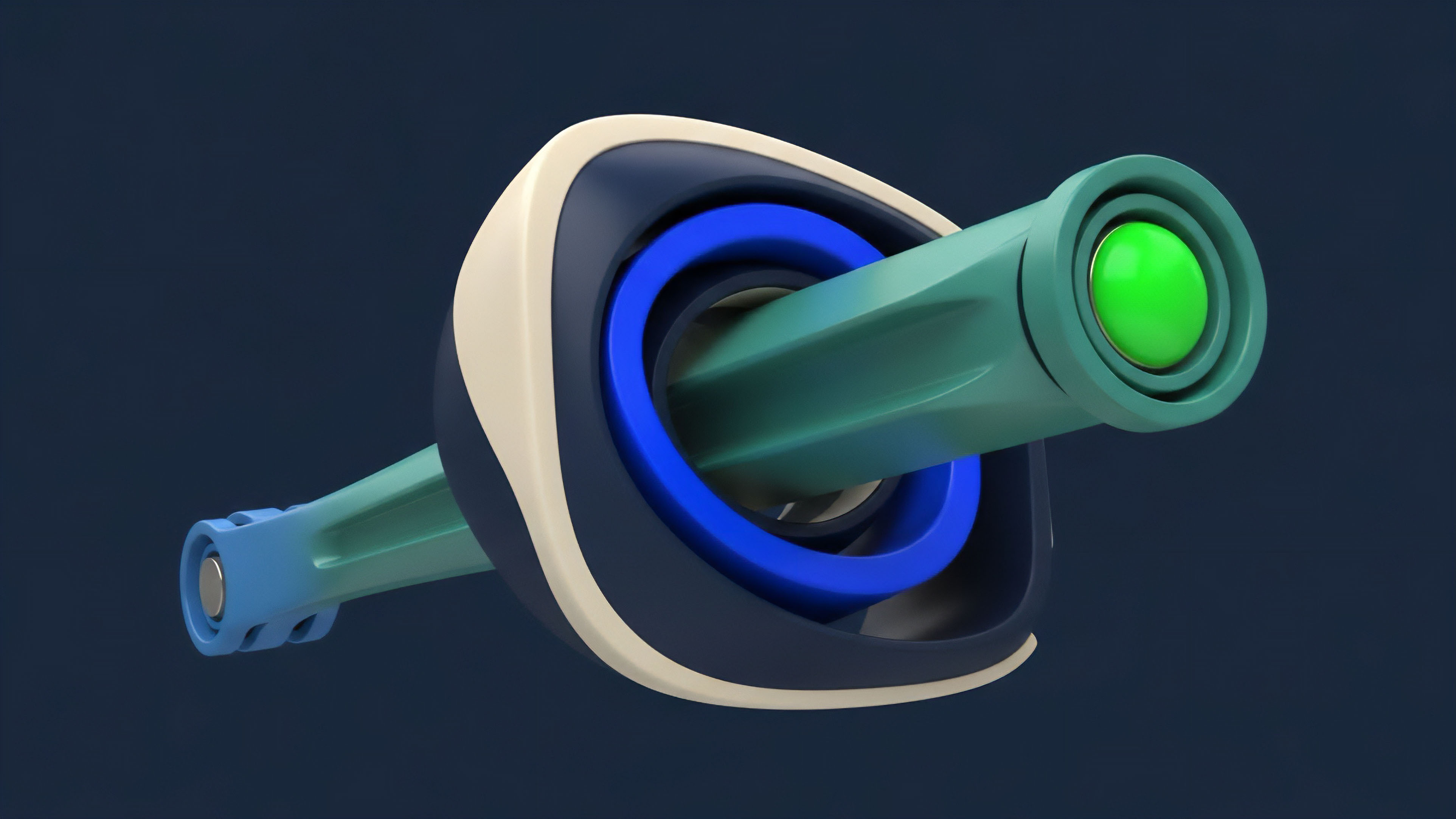
The ZKCC wraps this conditionality in a Zero-Knowledge Proof (ZKP), allowing the prover to demonstrate the satisfaction of the claim’s criteria (e.g. a specific asset price being met) to the verifier (the settlement smart contract) without disclosing the specific price or any other input data used in the calculation.
The ZKCC is the core technology that enables private, verifiable derivative settlement, transforming the public ledger into a trusted computation engine.
This construct is essential for the scaling of options and structured products within decentralized markets. Market microstructure in open ledgers is fundamentally flawed for professional participants because every order, every liquidation threshold, and every volatility hedge is public information, ripe for toxic order flow extraction and front-running. The ZKCC abstracts the sensitive data layer away from the public settlement layer.
It shifts the focus from validating the data itself to validating the correctness of the computation performed over that data, offering a pathway to high-stakes, high-volume derivatives trading where positional privacy is paramount for survival.

Origin and Foundational Roots
The conceptual genesis of ZKCCs lies not in finance, but in the theoretical computer science of the 1980s, specifically the seminal work on Zero-Knowledge Proofs by Goldwasser, Micali, and Rackoff. The application to finance, however, is a direct response to the inherent public auditability of the Ethereum Virtual Machine (EVM).
Early decentralized options protocols struggled to attract institutional liquidity because the public nature of the order book and collateral pools exposed trading strategies and created an unacceptable counterparty risk from sophisticated on-chain actors. The first practical attempts to solve this problem involved simple commitment schemes, where data was hashed, but this only proved the data existed, not that a specific computation over that data was correct. The breakthrough came with the refinement of scalable ZKP schemes ⎊ specifically zk-SNARKs and later zk-STARKs.
These cryptographic tools provided the necessary proof-of-computation primitive. The ZKCC, as a defined financial instrument, crystallized when researchers realized that a derivative’s payoff function ⎊ the mathematical relationship between the underlying asset price and the final settlement value ⎊ could be formulated as the single, verifiable statement within a ZKP. The ability to verify this complex, conditional logic without revealing the underlying spot price or the specific strike price of the option was the critical innovation.
It transformed ZKPs from a privacy tool for transactions into a core architectural component for trustless, private financial contracts.

Quantitative Theory and Protocol Physics
The theoretical foundation of the ZKCC rests on the verifiable execution of a contingent claim function P = f(ST, K, τ, σ, r) ⎊ where P is the payoff, ST is the terminal price of the underlying, K is the strike, τ is time to expiration, σ is volatility, and r is the risk-free rate ⎊ such that the smart contract only verifies the proof of P, never the inputs ST or K. This construction requires the counterparty who holds the right to exercise the option (the long side) to act as the Prover. The Prover takes the necessary inputs ⎊ the private data like the strike price, the public but concealed data like the oracle price feed, and the option pricing function itself ⎊ and generates a cryptographic proof that the payoff condition has been met and the resulting settlement amount is P. The core elegance of this system is that the on-chain Verifier contract receives only two pieces of information: the commitment to the initial state and the final, proven payoff P. The system is mathematically sound because the integrity of the proof is based on computational complexity assumptions, typically elliptic curve pairings or hash function collision resistance, depending on the specific ZKP construction used.
Our inability to respect the informational asymmetry of public ledgers is the critical flaw in current DeFi options models; ZKCCs provide the necessary computational buffer, reducing the system’s attack surface from the data layer to the cryptographic layer. The complexity of the underlying Black-Scholes or binomial model does not fundamentally change the ZKCC protocol physics; the financial model is simply compiled into an arithmetic circuit, and the Prover demonstrates the correct execution of that circuit. The challenge lies in minimizing the arithmetic circuit depth for complex, path-dependent options, as deeper circuits exponentially increase the proof generation time and cost.
This relationship between the financial model’s complexity and the cryptographic overhead is the defining trade-off of ZKCC design, forcing us to constantly optimize the expression of the derivative payoff function for cryptographic efficiency. This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored ⎊ because the gas cost of verification is a non-linear function of the option’s structural complexity, a factor which must be explicitly modeled into the final option premium.
A ZKCC transforms the option payoff function into a zero-knowledge arithmetic circuit, shifting the system’s trust assumption from counterparty honesty to cryptographic proof validity.

Technical Approach and Implementation Trade-Offs
Current ZKCC implementation relies on compiling the option’s settlement logic into a form suitable for ZKP generation, typically an R1CS (Rank 1 Constraint System) or a Plonk -style arithmetization. The choice of the underlying ZKP system dictates the latency, cost, and trust assumptions of the final instrument.

ZK-System Selection Criteria
The derivative systems architect must evaluate ZKP schemes based on two primary, adversarial metrics: Prover Latency and Verifier Cost.
- Prover Latency The time required for the option holder to generate the proof that triggers settlement. High latency makes high-frequency hedging impossible.
- Verifier Cost The gas expenditure required for the on-chain smart contract to check the proof. This is the operational cost baked into the option’s premium.
- Trusted Setup Whether the system requires a one-time, cryptographically secure setup phase.
| ZK-Scheme | Prover Latency | Verifier Cost (Gas) | Setup Type |
|---|---|---|---|
| zk-SNARKs (Groth16) | Moderate (Fastest for single proof) | Low (Constant) | Trusted Setup Required |
| zk-STARKs (FRI-based) | High (Larger proof size) | High (Logarithmic) | Trustless Setup |
| zk-Plonk (Halo2) | Low (Universal Setup) | Low (Constant) | Universal/Updateable Setup |

Impact on Market Microstructure
The ZKCC fundamentally alters order flow dynamics. In a transparent system, the existence of a large options position is a signal that market makers can exploit by front-running the inevitable hedging activity. With ZKCCs, orders are committed and matched in a private execution environment, with only the final, netted settlement instruction broadcast to the public chain.
This creates an environment of informational parity , forcing market makers to compete on genuine pricing efficiency (modeling volatility and tail risk) rather than on exploiting order book leakage. This is the only path toward robust institutional liquidity.
Private order execution via ZKCCs eliminates toxic informational leakage, forcing market makers to compete on true pricing efficiency rather than exploiting public order flow.

Systemic Evolution and Strategic Implications
The evolution of ZKCCs tracks the progress of general ZKP technology. Initially, ZKCCs were purely academic concepts, requiring proof generation times measured in minutes or even hours, making them impractical for any derivative requiring timely exercise. The advent of recursive proof composition and specialized hardware accelerators has dramatically lowered this latency barrier.

The Shift to Selective Disclosure
The current state of ZKCCs marks a strategic shift from the original DeFi axiom of “everything must be public.” The new operating model is selective cryptographic disclosure. The system proves compliance with collateral requirements and settlement logic while keeping the specific parameters of the trade private. This capability is not simply a feature; it is a critical necessity for institutional capital, which operates under strict regulatory mandates and competitive pressure to keep proprietary trading strategies secret.
- Mitigating Liquidation Cascades ZKCCs can mask individual collateral ratios, preventing malicious actors from precisely targeting a large, known liquidation point. The margin engine can prove that a collateralization ratio is above the required threshold without revealing the actual ratio or the size of the underlying position.
- Enabling Complex Products The ability to privately verify complex logic allows for the deployment of exotic options, such as multi-asset baskets or path-dependent structures, which would be too gas-intensive or informationally vulnerable to deploy on a transparent smart contract.
The Auditable Privacy Paradox
ZKCCs solve the auditable privacy paradox. Regulators require auditability and proof of systemic stability. ZKCCs provide this by allowing a designated third party (a regulator or an auditor) to verify the correctness of the entire system’s state (e.g. aggregate solvency) without having access to the specific data (individual user balances or positions).
This is achieved through the use of Merkle trees and ZK-proofs over the commitment scheme.
| Metric | Traditional DeFi Options | ZKCC-Based Options |
|---|---|---|
| Front-Running Risk | High (Public Order Book) | Near Zero (Private Execution) |
| Collateral Disclosure | Full (Publicly Viewable) | Zero-Knowledge Proof of Solvency |
| Latency Barrier | Network Congestion Dependent | Proof Generation Dependent |
| Institutional Adoption | Low (Due to Privacy Concerns) | High Potential (Data Minimization) |

Future Horizon and Synthetic Clearing
The logical conclusion of ZKCC technology is the creation of a synthetic central clearing counterparty (CCCP) entirely implemented in code. A traditional CCP manages counterparty risk by netting positions and guaranteeing settlement. A ZKCC-based protocol can perform the exact same function with superior efficiency and transparency.

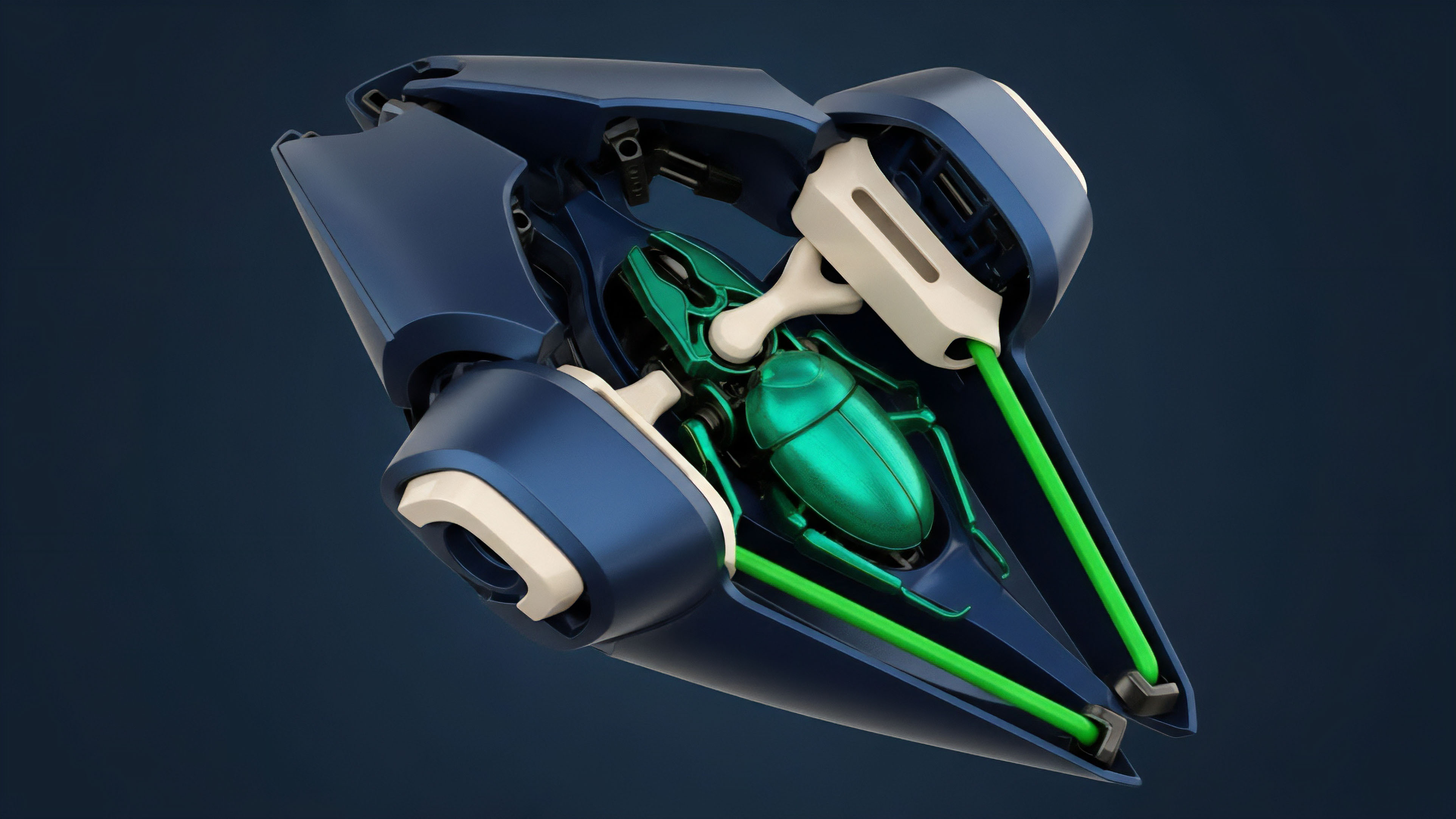
Architecture of a ZKCC Margin Engine
The next generation of options protocols will use ZKCCs to build a unified, cross-margin system that proves solvency without revealing individual leverage. This is the critical step in fostering robust financial strategies.
- Commitment Engine All collateral and position updates are committed to a Merkle tree, and only the Merkle root is publicly known.
- Proof of Solvency Module A recursive ZKP is generated over the entire Merkle tree, proving that the sum of all liabilities does not exceed the sum of all assets, and that every individual account meets its minimum margin requirement.
- Private Execution Layer Order matching and trade settlement occur off-chain, using ZKCCs to prove the validity of the trade and the resulting state change before updating the public commitment root.
- Automated Liquidation Circuit A dedicated ZK circuit that can prove a specific account is below the maintenance margin and trigger a forced deleveraging, without revealing the account’s full balance or the identity of the account.
The final state of ZKCC technology will be the synthetic central clearing counterparty, a cryptographically guaranteed risk-management system operating with perfect positional privacy.
This architecture allows for capital efficiency that rivals traditional finance, eliminating the massive capital overhead required for public over-collateralization. The ability of ZKCCs to offer highly complex, private products also provides a form of regulatory optionality , enabling protocols to satisfy regulatory requirements for data minimization while maintaining an iron-clad, cryptographically-guaranteed audit trail. The challenge remains the computational cost of recursive proofs and the inherent complexity of auditing the ZKP circuits themselves ⎊ the risk shifts from market manipulation to smart contract security within the cryptographic kernel. The market will demand, and only then will accept, ZKCC implementations that have been formally verified against all known side-channel attacks and circuit vulnerabilities. The future of decentralized derivatives is private, verifiable, and computationally intense.
Glossary

Exotic Options

Smart Contract Security

Proof Generation

Market Makers
Market Microstructure

Contingent Claims

Private Derivative Settlement

Informational Asymmetry

Path Dependent Options