Essence
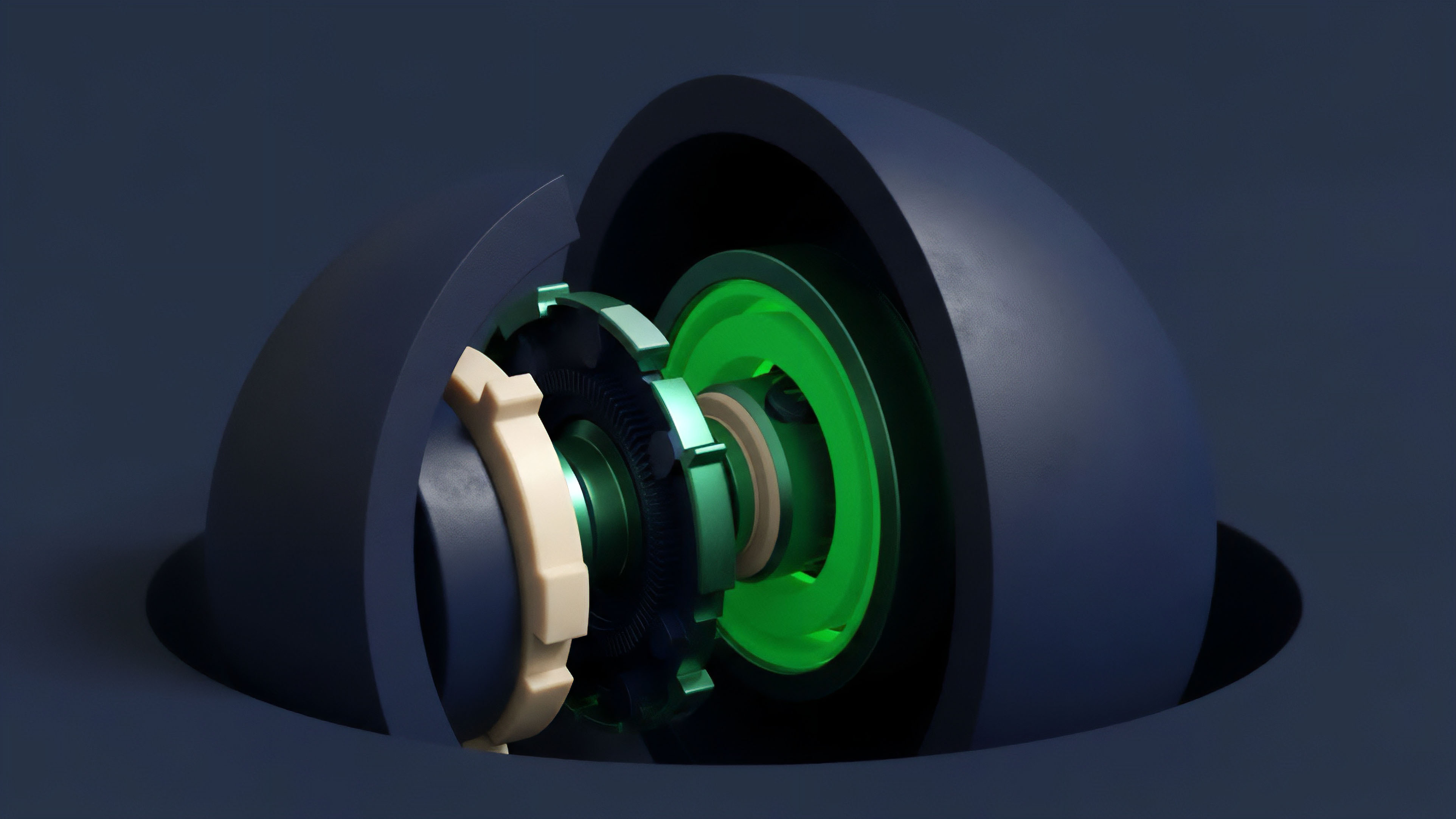
The core design challenge for decentralized derivatives protocols is the Capital Efficiency Security Trade-Off. This tension describes the inverse relationship between maximizing the utilization of collateral (capital efficiency) and ensuring the protocol’s solvency and resilience against systemic risk (security). In traditional finance, a centralized clearinghouse acts as the guarantor of security, allowing for highly efficient margin requirements and cross-margining.
Decentralized systems lack this centralized guarantor, forcing protocols to choose between high capital efficiency, which often requires complex risk models and exposes the system to liquidation cascades, and high security, which typically demands overcollateralization and results in inefficient capital allocation. The trade-off is fundamental to the architecture of options protocols, dictating everything from pricing mechanisms to liquidation thresholds and overall market structure.
A protocol’s capital efficiency directly correlates with its exposure to systemic risk; higher efficiency necessitates a more sophisticated and often fragile security mechanism.
This trade-off is a zero-sum game within a single design space. When a protocol prioritizes capital efficiency by reducing collateral requirements, it increases the risk of undercollateralization during periods of extreme volatility. This creates a vulnerability where a rapid price movement can cause a cascade of liquidations that the protocol cannot absorb, potentially leading to insolvency.
Conversely, prioritizing security by demanding high collateral ratios protects the protocol from these events but limits user participation and liquidity provision, making the market less attractive to professional traders accustomed to the high leverage of centralized venues.

Origin
The Capital Efficiency Security Trade-Off emerged from the earliest attempts to replicate traditional financial derivatives on-chain. Early DeFi protocols, particularly those offering lending and borrowing, were built on a foundation of strict overcollateralization. While this approach guaranteed solvency for simple lending markets, it proved unworkable for options and futures where high leverage is expected.
The initial options protocols often relied on static collateral pools or simple AMMs (Automated Market Makers) that required significant capital lockup to ensure liquidity. This design choice, while secure, severely limited the scale and depth of these markets.
The pressure to increase capital efficiency grew with the rise of professional market makers and institutional participants. These actors demanded systems that could compete with centralized exchanges on margin requirements. This led to a new wave of protocol design focused on dynamic collateral models and portfolio margining.
The trade-off became stark during the 2020-2021 market cycle, where protocols that attempted to increase efficiency by lowering collateral ratios often faced near-insolvency events during rapid price drops, highlighting the fragility of these new, more efficient architectures.

Theory
The theoretical foundation of this trade-off is rooted in the interplay between margin models, liquidation engines, and the Greeks. A protocol’s security depends on its ability to accurately assess and manage risk in real-time, specifically its delta and gamma exposure. A highly capital-efficient protocol must allow for cross-margining, where a user’s collateral can be netted across multiple positions to calculate overall risk.
This reduces the total collateral required but significantly increases the complexity of the liquidation process.
Margin Models and Risk Aggregation
The choice of margin model is central to this trade-off. Isolated margin, where each position is collateralized separately, is highly secure but inefficient. Portfolio margin, which aggregates risk across all positions, is highly efficient but complex to implement securely.
The challenge lies in accurately calculating the real-time risk of a user’s entire portfolio, especially during periods of high volatility when correlations between assets change rapidly. A protocol must ensure that the collateral held is sufficient to cover the worst-case scenario movement of the portfolio before a liquidation can be executed.

Liquidation Mechanisms and Latency
Security in high-efficiency systems depends heavily on the speed and reliability of the liquidation mechanism. The protocol must liquidate undercollateralized positions before the value of the collateral drops below the required threshold. This introduces a reliance on fast, reliable oracles and efficient on-chain execution.
A high-efficiency design often sacrifices security by introducing liquidation “cascades,” where a single liquidation triggers further liquidations across interdependent positions. The security aspect requires a robust insurance fund or backstop mechanism to absorb losses when liquidations fail to execute in time, further complicating the capital efficiency calculation.
The mathematical models that govern these systems must balance the probability of default with the cost of capital. A higher collateral requirement reduces the probability of default but increases the opportunity cost for the user. A protocol’s security parameters are effectively a reflection of its risk tolerance and its willingness to sacrifice capital efficiency for stability.

Approach
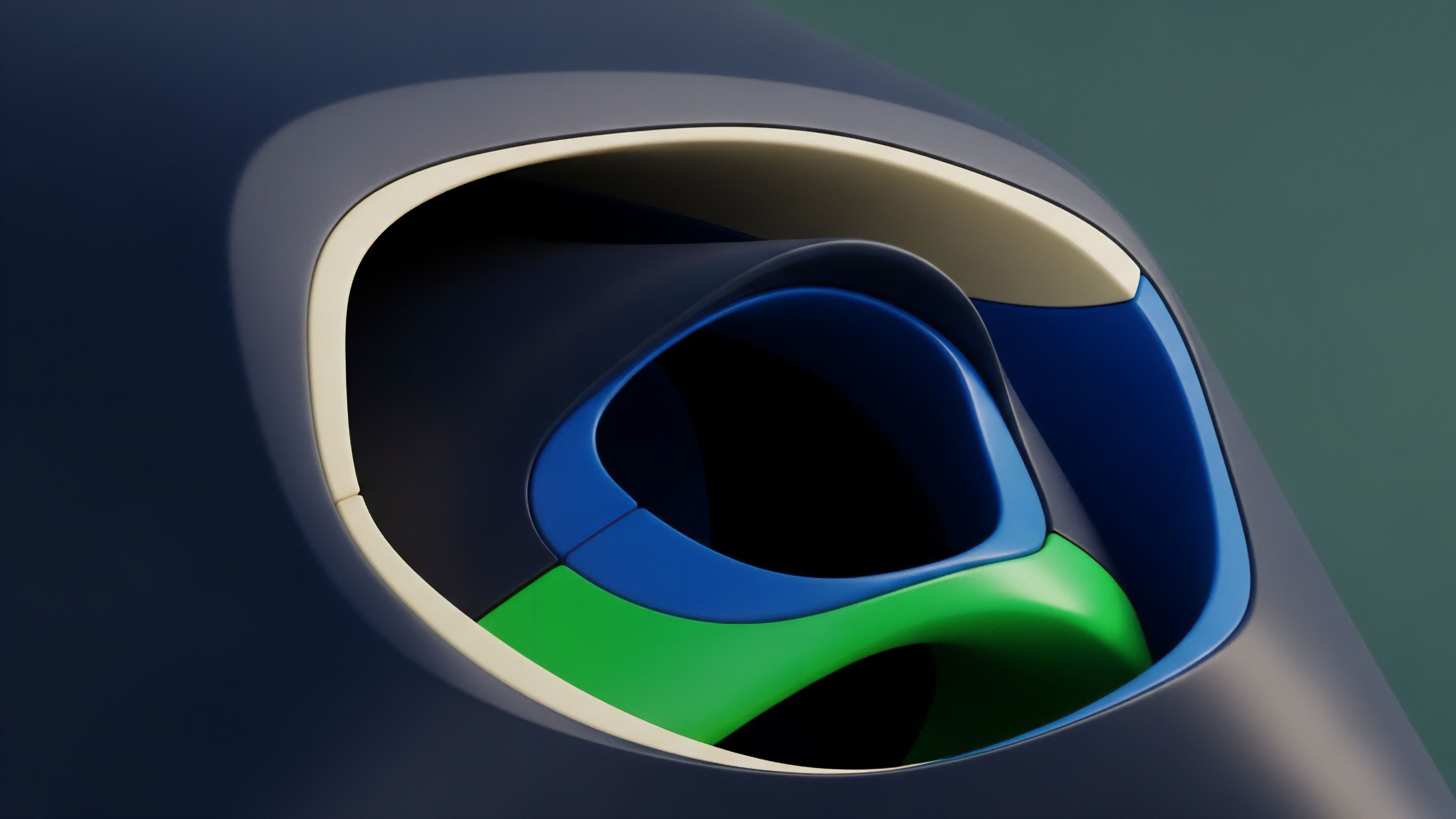
Protocols have adopted several distinct approaches to manage the Capital Efficiency Security Trade-Off, resulting in different architectures tailored for specific market segments. These approaches range from fully decentralized AMMs to hybrid models that sacrifice some decentralization for efficiency.
A common strategy for increasing capital efficiency is Concentrated Liquidity, where liquidity providers can designate a specific price range for their capital. This maximizes capital utilization within that range but exposes the provider to greater risk of impermanent loss outside that range. For options protocols, this means liquidity providers can earn higher fees but must actively manage their positions, or risk having their collateral fully allocated to a losing position.
| Design Approach | Capital Efficiency | Security Implications | Example Protocols |
|---|---|---|---|
| Overcollateralized AMM | Low | High; minimizes protocol insolvency risk. | Hegic (initial model) |
| Portfolio Margin & Cross-Margining | High | Moderate; introduces contagion risk and reliance on oracle speed. | dYdX, GMX |
| Dynamic Collateralization (Options Vaults) | Moderate to High | Moderate; risk depends on vault strategy and liquidation speed. | Ribbon Finance, Lyra |
Another approach involves separating the order matching from the settlement process. Protocols like dYdX and GMX utilize an off-chain order book for high capital efficiency and low latency, while maintaining on-chain settlement for security. This hybrid approach allows for higher leverage and lower collateral requirements, but introduces a centralization point in the off-chain sequencer or matching engine, which represents a new security vulnerability.
The trade-off here is between a fully trustless system and one that offers a more competitive user experience by compromising on a single aspect of decentralization.

Evolution
The evolution of the Capital Efficiency Security Trade-Off has been a constant progression from overcollateralized simplicity to dynamic, undercollateralized complexity. Early options protocols, such as those built on basic AMMs, treated all collateral as fungible and required high collateral ratios, making them robust but unattractive for professional trading. The industry then shifted toward dynamic risk models where collateral requirements are adjusted based on real-time volatility and the specific risk profile of the option being traded.
The current state of options protocols reflects a shift toward systems that use Risk-Adjusted Capital Allocation. Instead of static collateral, protocols now employ complex models to calculate the required margin based on the Greeks of the user’s position. This allows for higher capital efficiency by freeing up excess collateral.
However, this evolution has introduced new systemic risks related to governance and oracle manipulation. If the risk parameters are set incorrectly, or if an oracle feeds bad data, the protocol can quickly become undercollateralized. The security of these systems now relies less on simple overcollateralization and more on the integrity of the risk models and the speed of governance responses.
The transition from static overcollateralization to dynamic risk-adjusted capital allocation represents a significant leap in design, yet it exchanges a simple, robust security model for a complex, fragile one.
This evolution also includes the development of Insurance Funds. Many protocols now set aside a portion of trading fees to create a backstop against liquidation failures. While these funds increase the protocol’s security, they reduce capital efficiency by diverting potential yield from liquidity providers or token holders.
The size of the insurance fund required to ensure security is directly proportional to the capital efficiency of the protocol; a more efficient protocol requires a larger backstop to absorb potential losses from high leverage.

Horizon
The future direction of the Capital Efficiency Security Trade-Off points toward a new generation of protocols that attempt to achieve undercollateralization through decentralized credit and reputation systems. The current model, which relies exclusively on collateral, is inherently limited in its ability to compete with traditional finance. The next phase of development will involve a shift toward systems that assess counterparty risk in real-time, allowing for a user’s reputation and past performance to contribute to their margin requirements.
This requires building Decentralized Identity and Credit Scoring systems that can be integrated into options protocols. A user with a long history of successful trades and timely liquidations could be granted lower collateral requirements, increasing capital efficiency for experienced participants. However, this introduces a new set of security challenges related to Sybil attacks and data privacy.
The security of such a system relies on the integrity of the identity layer, which must be decentralized and verifiable. The ultimate goal is to move beyond the binary choice between efficiency and security and to build systems where a user’s capital efficiency is dynamically determined by their risk profile and historical data, rather than a one-size-fits-all collateral ratio.
Future protocols will attempt to solve the trade-off by incorporating reputation and credit scoring into margin calculations, allowing for dynamic, undercollateralized positions based on individual risk profiles.
We are likely to see the integration of machine learning models for dynamic risk parameter adjustment. These models will analyze real-time market data to predict volatility and adjust margin requirements automatically, allowing protocols to dynamically optimize the trade-off. This approach increases efficiency by ensuring collateral requirements are precisely calibrated to current market conditions, but it also introduces new security risks related to model manipulation and the potential for a “black box” system where the risk parameters are not fully transparent to users or governance.

Glossary

Settlement Security

Collateral Security in Defi Governance

Decentralized Capital Pools
Value at Risk Security
Order Book Security Best Practices

Trade Batch Commitment
Capital Efficiency Exposure

Consensus Mechanism Trade-Offs

Protocol Security Vulnerability Remediation Effectiveness