Essence
Automated Compliance Mechanisms (ACMs) represent the programmatic implementation of regulatory and risk controls directly within decentralized finance (DeFi) protocols, specifically for derivatives. The core function of an ACM is to translate external legal and financial mandates into executable smart contract logic. This process shifts compliance from a manual, human-mediated function to an automated, pre-trade check.
For crypto options and derivatives, this is particularly significant because of the inherent leverage and counterparty risk involved. ACMs ensure that only eligible participants can engage in specific markets, that trading activities adhere to predefined position limits, and that required regulatory reporting data is generated automatically, often in a privacy-preserving manner. The goal is to create a bridge between the permissionless nature of decentralized protocols and the stringent requirements of traditional financial institutions and global regulators.
The objective of an ACM is to create a system that can verify compliance without compromising the core tenets of decentralization. This requires moving beyond simple blacklisting of addresses. Instead, the focus is on creating a verifiable, on-chain identity layer that can be used by various protocols.
This identity layer allows for granular control over access based on factors like geographic location, accredited investor status, or institutional registration. The ACM acts as a gatekeeper, ensuring that all actions within the protocol conform to a set of rules defined by governance, external oracles, or a combination of both. This contrasts sharply with early DeFi, where protocols operated under a purely “code is law” philosophy with no consideration for external legal frameworks.
Automated Compliance Mechanisms programmatically embed regulatory and risk controls into decentralized protocols, enabling permissionless systems to interact with traditional financial requirements.

Origin
The genesis of ACMs in DeFi derivatives is rooted in the conflict between the industry’s initial ethos of complete permissionlessness and the inevitable pressure from institutional capital and regulatory bodies. Early derivatives protocols, primarily focused on perpetual futures and simple options, prioritized capital efficiency and composability above all else. The prevailing view was that the protocol itself, being non-custodial and decentralized, was outside the scope of traditional financial regulation.
However, as the market grew and attracted significant capital, particularly from traditional finance (TradFi) institutions, this perspective became unsustainable. Institutional investors are legally mandated to perform due diligence on counterparties, verify client identities, and adhere to specific jurisdictional rules regarding derivative trading. The initial attempts at compliance were rudimentary, often involving simple IP-based restrictions or off-chain verification processes that were easily circumvented.
The market quickly realized that these methods introduced centralized points of failure, contradicting the core value proposition of decentralization. The evolution of ACMs began with the development of “permissioned pools” and segregated markets. Protocols started exploring how to integrate identity verification services, such as KYC (Know Your Customer) providers, directly into their systems.
This led to the creation of Decentralized Identity (DID) solutions and verifiable credentials. The need for ACMs was further accelerated by regulatory actions, such as the targeting of specific DeFi protocols for sanctions violations or unregistered securities offerings. This forced protocols to consider how to bake compliance directly into the architecture to ensure long-term viability and avoid regulatory capture.
Theory
The theoretical foundation of ACMs for derivatives rests on solving the “compliance paradox” ⎊ how to enforce regulatory requirements without revealing the private information that decentralization protects. The most powerful tool for this is Zero-Knowledge Proofs (ZKPs). ZKPs allow a protocol to verify a statement about a user’s identity or status without ever seeing the underlying data.
A user can prove they are an accredited investor, for example, without revealing their name, address, or financial details to the protocol or other users. This preserves privacy while satisfying the compliance requirement. Another key theoretical component is the concept of on-chain risk modeling.
In traditional finance, risk models are often proprietary and run centrally by each institution. In a decentralized environment, ACMs allow for a transparent, auditable risk engine. This engine can automatically adjust margin requirements, position limits, and liquidation thresholds based on real-time market conditions and the verifiable credentials of the participants.
The protocol can theoretically enforce systemic risk controls across all users, preventing excessive leverage that could lead to contagion. The challenge lies in designing a system where the risk parameters themselves are not subject to manipulation by a single entity. This requires a robust governance mechanism that controls the rules of the ACM.
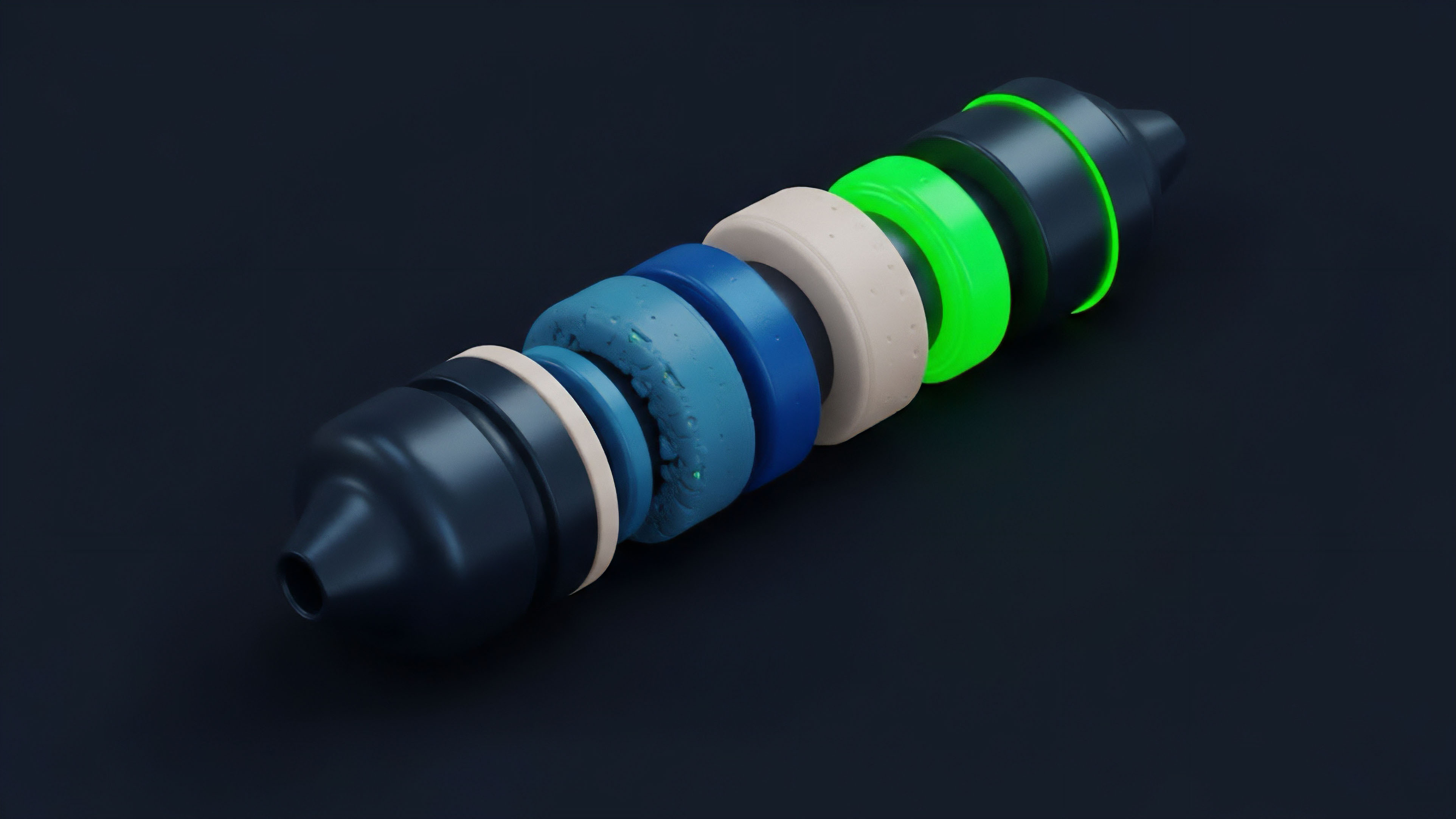
The theoretical model of a decentralized compliance system often involves several distinct layers:
- Identity Layer: A decentralized identifier (DID) standard that allows users to create and control their own verifiable credentials. This layer issues proofs of accreditation, jurisdiction, or other necessary attributes.
- Policy Engine Layer: The smart contract logic that consumes these verifiable credentials. This layer contains the specific rules for a particular market (e.g. “only users with a US-accredited investor credential can trade this option contract”).
- Monitoring Layer: Automated systems that continuously scan on-chain activity for anomalies or violations. This layer ensures ongoing compliance and provides data for regulatory reporting.
Approach
Current implementations of ACMs vary significantly in their approach, reflecting the ongoing debate between privacy and regulatory necessity. The primary methods can be categorized based on their degree of centralization and data handling.
Permissioned Pools and Walled Gardens
The most common approach for institutional entry into DeFi derivatives is the creation of permissioned pools. These pools operate similarly to traditional private markets, where access is restricted to whitelisted addresses. Users must complete an off-chain KYC process with a centralized entity, which then grants access to the protocol via an allowlist.
This method offers high compliance assurance for institutions but sacrifices a significant portion of decentralization and permissionlessness. The pool’s governance often retains a level of control over participant access, effectively creating a “walled garden” within the larger DeFi ecosystem.

Verifiable Credentials and ZKPs
A more advanced approach involves verifiable credentials (VCs) and ZKPs. This method aims to provide compliance without compromising user privacy. A user obtains a VC from a trusted issuer (e.g. a regulated financial institution or identity provider) that certifies their status.
The user then presents a ZKP to the protocol, proving they hold the necessary credential without revealing the credential itself. The protocol’s smart contract verifies the proof and grants access. This allows for compliance checks at the point of trade execution, maintaining user privacy while adhering to regulatory requirements.
This approach is gaining traction as the preferred method for long-term scalability.

Automated Monitoring and Risk Reporting
The implementation of automated monitoring tools is critical for post-trade compliance. These tools track transactions for specific patterns, such as large volume trades or interactions with sanctioned addresses. The goal is to provide automated reporting for tax purposes and to detect potential market manipulation or illicit activities.
For derivatives, this requires sophisticated analytics that can track complex positions across multiple protocols. The table below compares these different approaches.
| Compliance Approach | Centralization Level | Privacy Preservation | Market Access Model |
|---|---|---|---|
| Centralized Exchange (CEX) | High | Low (full data collection) | Permissioned, full KYC |
| Permissioned DeFi Pool | Medium | Low (off-chain KYC) | Allowlist, restricted access |
| Verifiable Credentials/ZKPs | Low | High (data minimization) | Permissionless verification |

Evolution
The evolution of ACMs in crypto derivatives has moved from simple, reactive measures to complex, proactive systems. The first generation of compliance in DeFi was primarily focused on off-chain due diligence and sanctions screening. This was often a manual process where protocols or associated entities would screen addresses against lists like the OFAC sanctions list.
This approach was inherently inefficient and created a significant bottleneck for institutional participation. The second phase introduced permissioned protocols and segregated liquidity pools. This model recognized that institutions could not participate in fully permissionless markets, so it created specific environments where compliance rules were enforced by a centralized entity.
This allowed for institutional participation but fragmented liquidity and created a two-tiered market. The challenge here was maintaining capital efficiency; a user in a permissioned pool could not easily interact with the broader DeFi ecosystem. The current evolution focuses on interoperable compliance layers and on-chain verifiable credentials.
The goal is to create a standardized compliance framework that can be used by any protocol. This involves developing a common language for identity verification and risk assessment. The key shift is from protocols enforcing compliance individually to a shared infrastructure where compliance status is portable across different platforms.
This allows for greater capital efficiency while still adhering to necessary regulatory standards. The future of ACMs will involve integrating these compliance checks directly into the core risk engines of derivative protocols.
The progression of compliance in decentralized finance moved from simple off-chain blacklists to sophisticated on-chain identity layers and risk engines.
Horizon
Looking ahead, the next generation of ACMs will shift focus from simple identity verification to automated risk reporting and capital adequacy checks. The challenge for a derivatives systems architect is to design a protocol that can prove its solvency and systemic risk profile to regulators without revealing proprietary trading strategies or individual positions. This requires a new class of ZK-compliance tools that allow for aggregated risk calculations.
The protocol will be able to prove that its total leverage exposure is below a certain threshold or that it holds sufficient collateral, all without disclosing the specific details of its users’ portfolios. The ultimate goal for ACMs is to move beyond mere compliance with existing laws to proactive system stability. The ACM of the future will not just prevent non-compliant users from entering; it will actively manage systemic risk within the protocol itself.
This includes automated adjustments to margin requirements based on real-time volatility and a mechanism for automated liquidation that minimizes market disruption. This creates a more robust and resilient system that can withstand extreme market conditions. The future architecture will likely rely on a combination of decentralized identity standards, ZK-proofs for privacy-preserving verification, and automated risk oracles that feed regulatory parameters into the smart contracts.
This creates a truly decentralized system that can still function within regulatory boundaries. The primary risk in this future architecture is not technical failure, but governance capture ⎊ the possibility that a centralized entity could gain control over the rules of the ACM, thereby undermining the system’s decentralization.

The Future of Automated Risk Reporting
A critical development will be the creation of Decentralized Regulatory Oracles (DROs). These oracles will act as a bridge between off-chain regulatory requirements and on-chain protocol logic. A DRO could feed real-time regulatory changes into a smart contract, allowing the ACM to instantly update its rules based on new laws.
This creates a dynamic, adaptable system that can respond to a constantly changing regulatory environment. The design of these DROs will be critical, as they must be decentralized and verifiable to avoid a single point of failure.

Divergence Points and Conjecture
The path forward diverges significantly based on the successful implementation of ZK-based compliance. If ZKPs fail to gain traction or prove too complex for real-world application, the industry will likely revert to permissioned pools, leading to significant liquidity fragmentation and a two-tiered market. However, if ZKPs succeed, we can build a universal compliance layer that allows for seamless, privacy-preserving institutional access.
My conjecture is that the greatest systemic risk in the future of decentralized derivatives is not a technical vulnerability in the core smart contract logic, but rather a governance failure in the associated compliance oracles. The system will be designed to prevent illicit activity, but the rules governing what constitutes illicit activity will be controlled by a centralized multisig or a small group of stakeholders, creating a new form of systemic risk. The system’s robustness will be entirely dependent on the integrity of the data feed and the governance structure that controls it.
Instrument of Agency Policy Proposal
A policy proposal for a Decentralized Regulatory Oracle Framework would address this governance risk. The framework would mandate that any protocol implementing an ACM must use a DRO governed by a diverse, multi-stakeholder DAO (Decentralized Autonomous Organization). The DAO would include representatives from different jurisdictions, legal experts, and protocol developers.
The DRO would not be controlled by a single entity, but rather by a set of checks and balances that ensure regulatory updates are applied fairly and transparently. This framework would prioritize decentralized governance of compliance rules, preventing a single point of failure and ensuring the system remains true to its decentralized principles.
Automated compliance systems for derivatives will eventually evolve into proactive risk management engines that maintain systemic stability while preserving user privacy through zero-knowledge proofs.

Glossary

Compliance Framework Maturity

Regulatory Compliance Pathway

Compliance Technology

Regulatory Compliance Innovation in Defi

Compliance Risk
Defi Regulation
Regulatory Compliance Layer

Regulatory Compliance Solutions for Institutional Defi Development
Regulatory Compliance Derivatives