Constant Time Verification


Meaning ⎊ Constant Time Verification ensures deterministic execution latency to prevent side-channel information leakage in decentralized financial protocols.
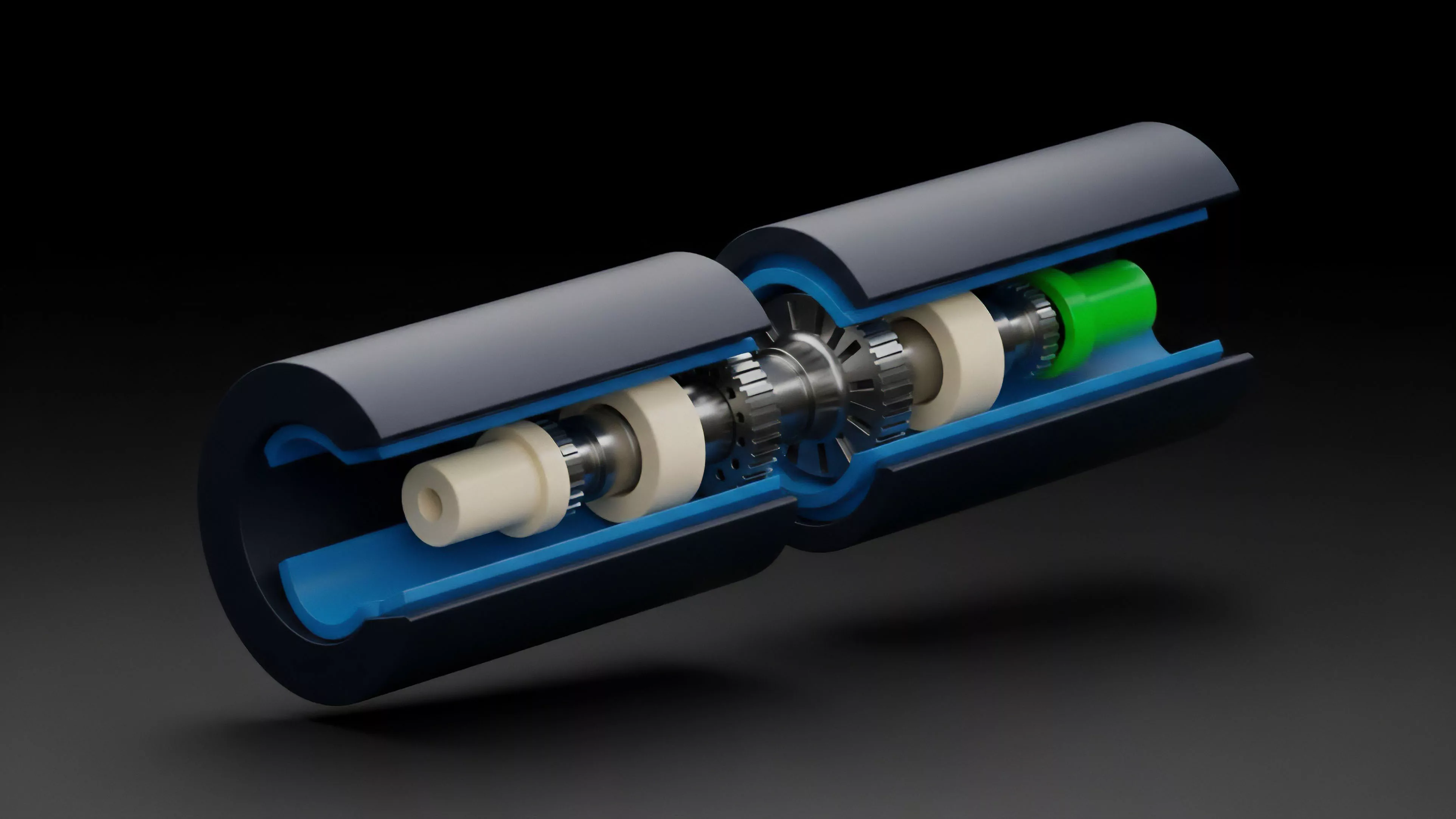
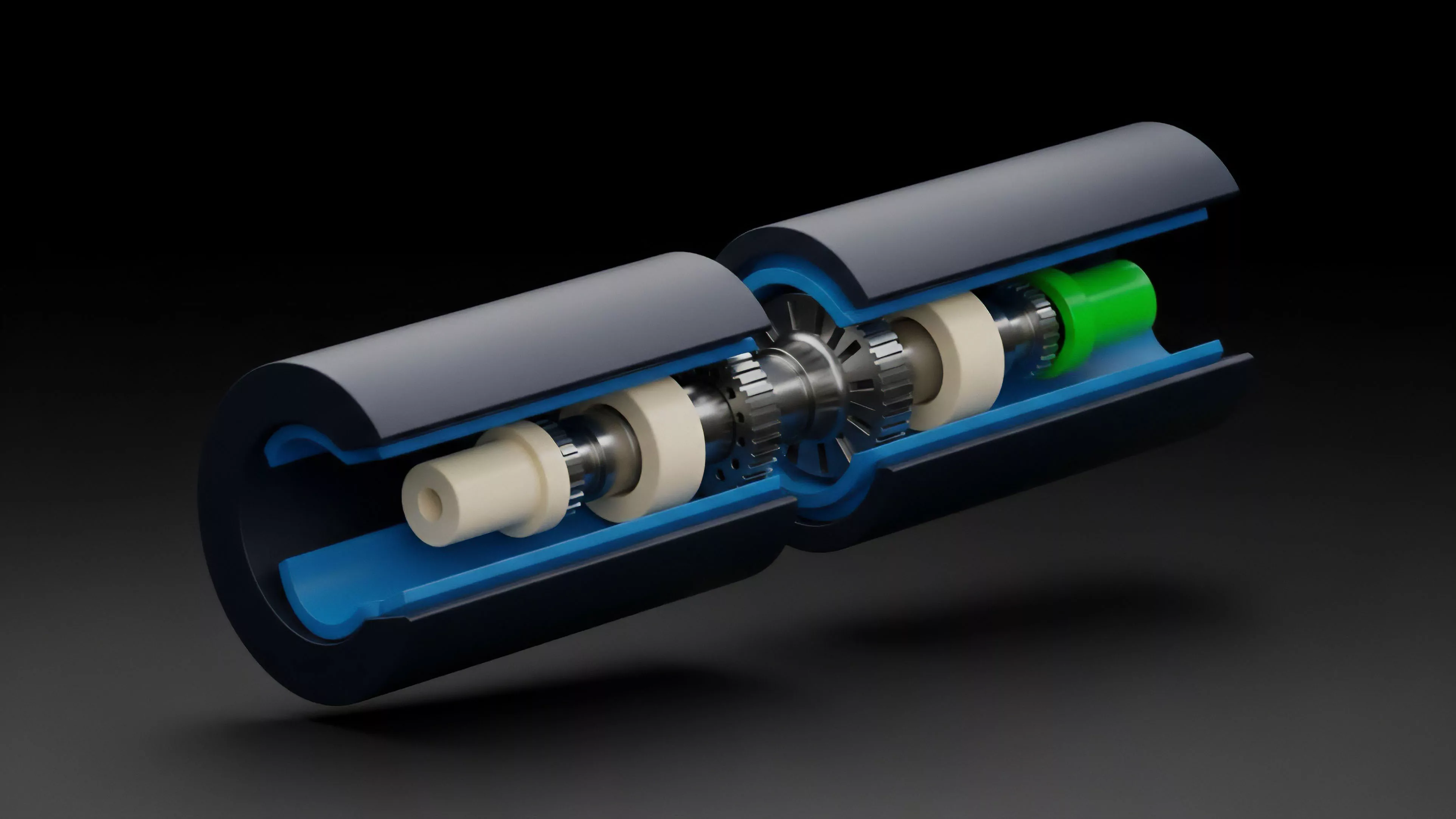
Cryptographic Hardware Security


Meaning ⎊ Hardware security modules provide the physical foundation for trust, ensuring immutable key protection within adversarial decentralized environments.
On-Chain Privacy


Meaning ⎊ On-Chain Privacy leverages zero-knowledge cryptography to ensure transaction confidentiality and protect proprietary trading strategies in DeFi.
Data Minimization Strategies


Meaning ⎊ Data minimization secures decentralized derivatives by limiting public information exposure while maintaining rigorous margin and settlement integrity.
Proxy Contract Logic Upgrades


Meaning ⎊ Architectural pattern decoupling contract data from logic to allow for secure and seamless protocol functionality updates.
Air-Gapped Storage


Meaning ⎊ A security method keeping devices physically disconnected from all networks to prevent remote digital intrusion.
Physical Vault Security


Meaning ⎊ The implementation of physical safeguards, such as fireproof safes and secure locations, to protect backup media.
M-of-N Threshold Signatures


Meaning ⎊ A cryptographic method where multiple key shares are combined to create a single valid signature for a transaction.
Confidential Smart Contracts


Meaning ⎊ Smart contracts that execute with private state and inputs, hiding sensitive data from public ledger visibility.
Zeroization Protocols


Meaning ⎊ Emergency procedures to instantly and irreversibly erase sensitive data from memory when a security breach is detected.
Tamper Responsive Memory


Meaning ⎊ Memory architecture designed to detect physical tampering and instantly erase sensitive data to prevent unauthorized extraction.
Privacy Enhancing Computation


Meaning ⎊ Privacy Enhancing Computation enables secure, private execution of financial derivatives on decentralized ledgers, preserving integrity and privacy.
Privacy by Design Principles


Meaning ⎊ Privacy by Design Principles ensure that confidentiality is structurally embedded in decentralized derivatives to protect participant financial autonomy.
Identity Wallets


Meaning ⎊ Dedicated applications for storing, organizing, and managing verifiable credentials and identity-related data.
Privacy Preserving Identity Solutions


Meaning ⎊ Cryptographic tools verifying user identity attributes without exposing sensitive underlying personal data.
Data Confidentiality


Meaning ⎊ Data Confidentiality secures order flow and proprietary strategy in decentralized derivatives, mitigating front-running and adverse selection risks.
Zero-Knowledge Trading


Meaning ⎊ Zero-Knowledge Trading provides a cryptographically secure framework for private, verifiable derivative settlement on public blockchain ledgers.
Zero-Knowledge Compliance Audit


Meaning ⎊ Zero-Knowledge Compliance Audit provides cryptographic verification of regulatory adherence in decentralized markets while preserving transaction privacy.
Data Privacy Solutions


Meaning ⎊ Data privacy solutions provide cryptographic mechanisms to protect sensitive derivative trade data while maintaining decentralized market integrity.
Air-Gapped Security


Meaning ⎊ Physical isolation of a device from all networks to prevent remote access to sensitive cryptographic data.
Zero-Knowledge Compliance Proofs


Meaning ⎊ Cryptographic verification of regulatory compliance without exposing sensitive user or transaction data.
Bulletproofs


Meaning ⎊ Efficient proofs verifying that a number is within a specific range without revealing it.
Hash-Based Commitments


Meaning ⎊ Using unique data fingerprints to lock information until a later disclosure.
Automated KYC


Meaning ⎊ The use of digital technology to automatically verify user identities and perform anti-money laundering checks.
Constructor Security


Meaning ⎊ Ensuring the safe initialization of smart contracts by avoiding vulnerable constructor patterns in upgradeable systems.
Contextual Integrity


Meaning ⎊ Ensuring contract behavior remains predictable and secure when executed within the context of another contract.
Check-Effects-Interactions Pattern


Meaning ⎊ A strict coding sequence requiring validation and state updates to occur before any external calls are made.
Vault Security
Meaning ⎊ The physical protection measures, including high-security vaults and access controls, for storing sensitive key backups.
Secure Enclave


Meaning ⎊ An isolated, hardware-protected area within a processor used to securely perform sensitive computations and store data.
