Oracle Manipulation Vulnerabilities


Meaning ⎊ Oracle manipulation vulnerabilities exploit external data dependencies in smart contracts to trigger unfair liquidations or misprice derivative settlements.
Zero-Knowledge Circuit Design


Meaning ⎊ Zero-Knowledge Circuit Design translates financial logic into verifiable cryptographic proofs, enabling private and scalable derivatives trading on public blockchains.
Code Vulnerabilities


Meaning ⎊ Code vulnerabilities in crypto options protocols create systemic financial risks by enabling economic exploits through logic flaws or external input manipulation.
Adversarial Environment Design


Meaning ⎊ Adversarial Environment Design proactively models and counters strategic attacks by rational actors to ensure the economic stability of decentralized financial protocols.
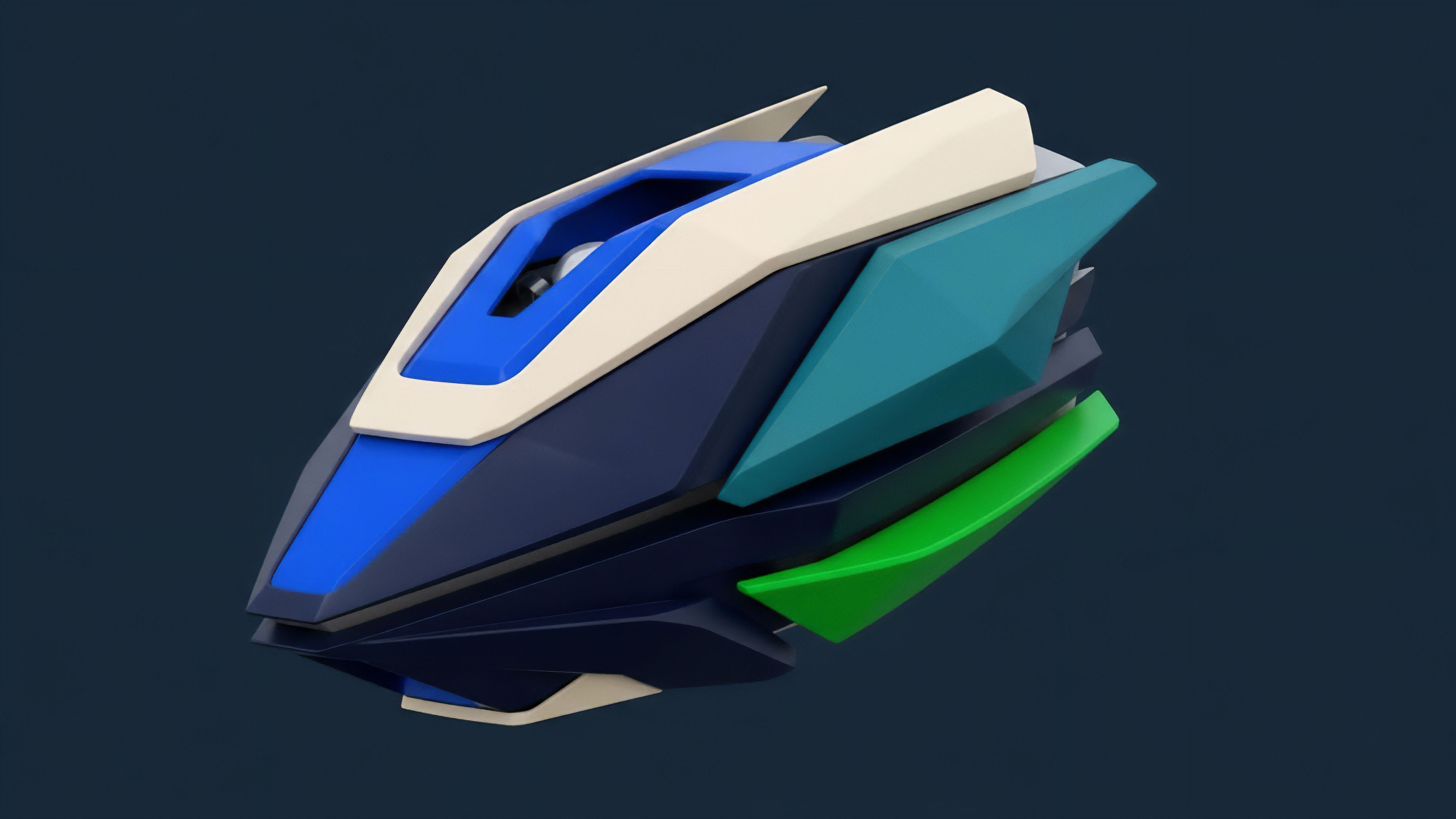
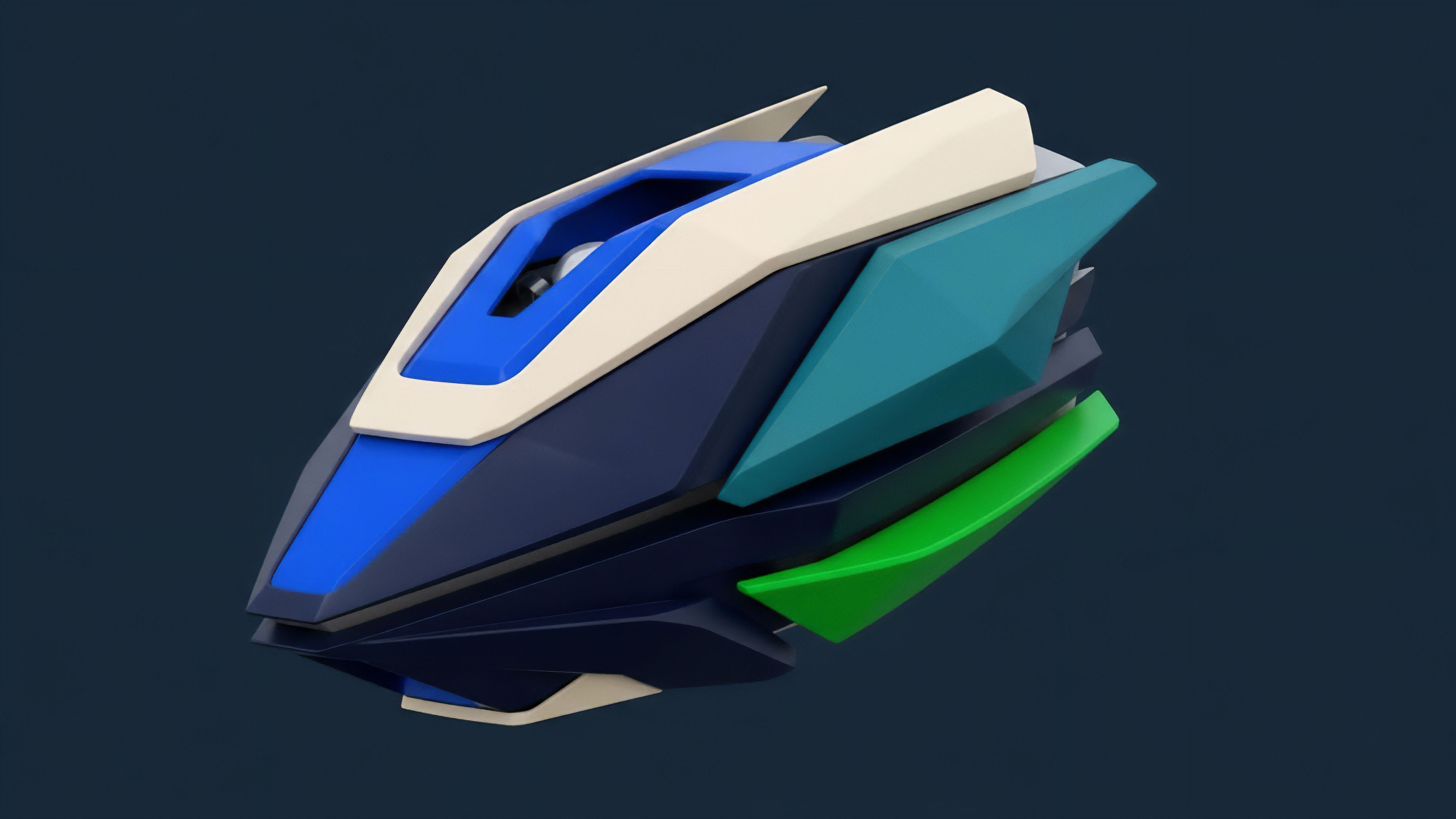
Derivative Systems Design


Meaning ⎊ Derivative Systems Design in crypto focuses on creating automated protocols for options pricing and settlement, managing volatility risk and capital efficiency within decentralized constraints.
Protocol Design Tradeoffs


Meaning ⎊ Protocol design tradeoffs in crypto options involve balancing capital efficiency against systemic risk, primarily through choices in collateralization, liquidity mechanisms, and settlement processes.
Black-Scholes Model Vulnerabilities


Meaning ⎊ The Black-Scholes model's core vulnerability in crypto stems from its failure to account for stochastic volatility and fat tails, leading to systemic mispricing in decentralized markets.
Decentralized Finance Vulnerabilities
Meaning ⎊ Decentralized Finance Vulnerabilities represent the emergent systemic risks inherent in protocol composability and automated capital flows, requiring a shift from static code audits to dynamic risk management.
Security Vulnerabilities


Meaning ⎊ Security vulnerabilities in crypto options are systemic design flaws in smart contracts or economic models that enable value extraction through oracle manipulation or logic exploits.
Fee Market Design
Meaning ⎊ Fee Market Design in crypto options protocols structures incentives for liquidity providers and liquidators to ensure capital efficiency and systemic stability.
Financial System Design Trade-Offs


Meaning ⎊ Decentralized options design balances capital efficiency, risk management, and accessibility by making fundamental trade-offs in collateralization and pricing models.
MEV Mitigation Strategies


Meaning ⎊ MEV mitigation strategies protect crypto options markets by eliminating information asymmetry in transaction ordering and redistributing extracted value to users.
Margin Engine Vulnerabilities


Meaning ⎊ Margin engine vulnerabilities represent systemic risks in derivatives protocols where failures in liquidation logic or oracle data can lead to cascading bad debt and market instability.
Consensus Mechanism Vulnerabilities


Meaning ⎊ Consensus mechanism vulnerabilities threaten derivative settlement integrity by compromising price feeds and collateral finality through state manipulation and network failures.
Delta Hedging Vulnerabilities
Meaning ⎊ Delta hedging vulnerabilities in crypto arise from high volatility and fragmented liquidity, causing significant gamma and slippage losses for market makers.
Front-Running Vulnerabilities


Meaning ⎊ Front-running vulnerabilities in crypto options exploit public mempool transparency and transaction ordering to extract value from large trades by anticipating changes in implied volatility.
Incentive Design Game Theory


Meaning ⎊ Incentive Design Game Theory provides the economic framework for aligning self-interested participants in decentralized crypto options markets to ensure systemic stability and capital efficiency.
Modular Blockchain Design
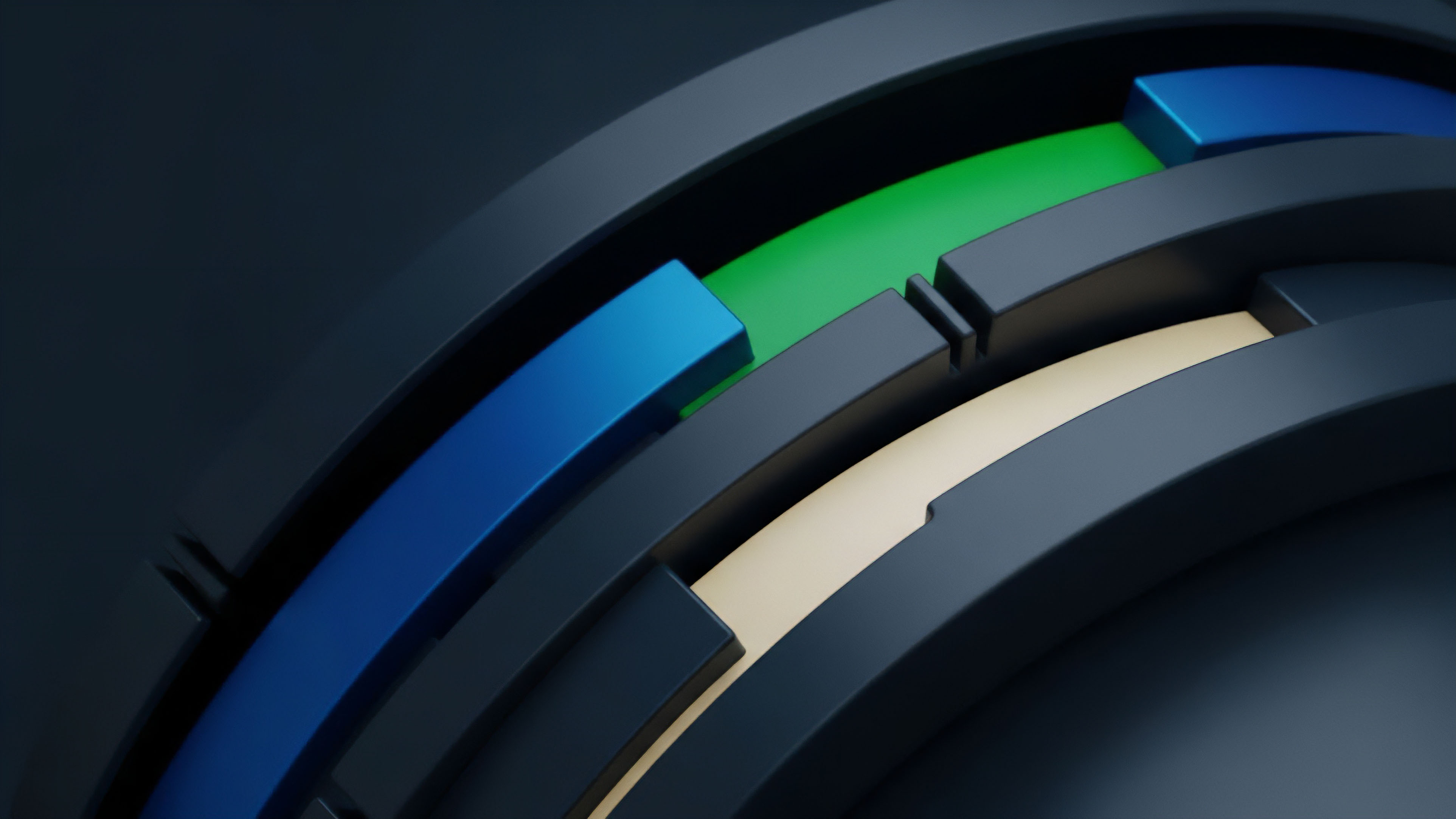
Meaning ⎊ Modular blockchain design separates core functions to create specialized execution environments, enabling high-throughput and capital-efficient crypto options protocols.
Liquidity Pool Design


Meaning ⎊ Options liquidity pool design requires dynamic risk management mechanisms to handle non-linear payoffs and volatility, moving beyond simple constant product formulas to ensure capital efficiency and LP solvency.
Smart Contract Design


Meaning ⎊ Smart contract design for crypto options automates derivative execution and risk management, translating complex financial models into code to eliminate counterparty risk and enhance capital efficiency in decentralized markets.
Automated Market Maker Design


Meaning ⎊ Automated Market Maker Design for options involves dynamic risk management to price non-linear derivatives and mitigate volatility exposure for liquidity providers.
Derivatives Market Design


Meaning ⎊ Derivatives market design provides the framework for risk transfer and capital efficiency, adapting traditional options pricing and settlement mechanisms to the unique constraints of decentralized crypto environments.
Reverse Stress Testing


Meaning ⎊ Reverse Stress Testing identifies the specific combination of market conditions and technical failures required to cause a crypto derivatives protocol to collapse.
Protocol Vulnerabilities


Meaning ⎊ Protocol vulnerabilities represent systemic design flaws where a protocol's economic logic or smart contract implementation allows for non-sanctioned value extraction by sophisticated actors.
Hybrid Oracle Design
Meaning ⎊ Hybrid Oracle Design secures decentralized options by synthesizing multiple data sources through robust aggregation logic, mitigating manipulation risk for high-stakes settlements.
Derivative Protocol Design


Meaning ⎊ Derivative protocol design creates permissionless, smart contract-based frameworks for options trading, balancing capital efficiency with complex risk management challenges.
Financial Instrument Design


Meaning ⎊ Crypto options design creates non-linear financial primitives for risk management in decentralized markets by translating traditional options logic into trustless protocols.
Financial System Design


Meaning ⎊ The Adaptive Risk-Adjusted Collateralization Framework dynamically manages collateral requirements for decentralized options by calculating real-time risk parameters to optimize capital efficiency.
Flash Loan Vulnerabilities
Meaning ⎊ Flash loan vulnerabilities exploit a protocol's reliance on single-block price data by using zero-collateral loans to manipulate on-chain oracles for economic gain.
