Decentralized Exchange Competition


Meaning ⎊ Decentralized Exchange Competition drives architectural innovation and capital efficiency through adversarial protocol design and liquidity optimization.
Decentralized Exchange Integrity


Meaning ⎊ Decentralized Exchange Integrity ensures verifiable, trustless market execution through immutable code, mitigating systemic risks in global finance.
Decentralized Exchange Liquidation


Meaning ⎊ Decentralized Exchange Liquidation automates solvency enforcement, ensuring protocol stability through algorithmic asset redistribution in volatile markets.
Decentralized Exchange Monitoring


Meaning ⎊ Decentralized Exchange Monitoring provides the essential observability required to quantify risk and verify execution in automated financial venues.
Decentralized Exchange Legal Frameworks


Meaning ⎊ The evolving legal standards defining the responsibility and regulation of non-custodial, automated trading protocols.
Decentralized Exchange Privacy


Meaning ⎊ Decentralized exchange privacy secures financial trade intent and participant data, enabling institutional-grade strategy execution on open ledgers.
Exchange Security Breaches


Meaning ⎊ Exchange security breaches represent terminal failures of custodial infrastructure that trigger systemic liquidity crises and necessitate robust protocols.
Decentralized Exchange Growth


Meaning ⎊ Decentralized Exchange Growth represents the structural migration of global trade execution to autonomous, transparent, and immutable blockchain protocols.
Decentralized Exchange Depth


Meaning ⎊ The measure of liquidity available in decentralized pools that dictates the market's ability to handle trades.
Decentralized Exchange Options


Meaning ⎊ Decentralized exchange options provide transparent, non-custodial derivative trading, utilizing smart contracts to manage risk and settlement.
Decentralized Asset Exchange


Meaning ⎊ Decentralized Asset Exchange protocols provide transparent, non-custodial infrastructure for global derivative trading and automated risk management.
Decentralized Exchange Architectures
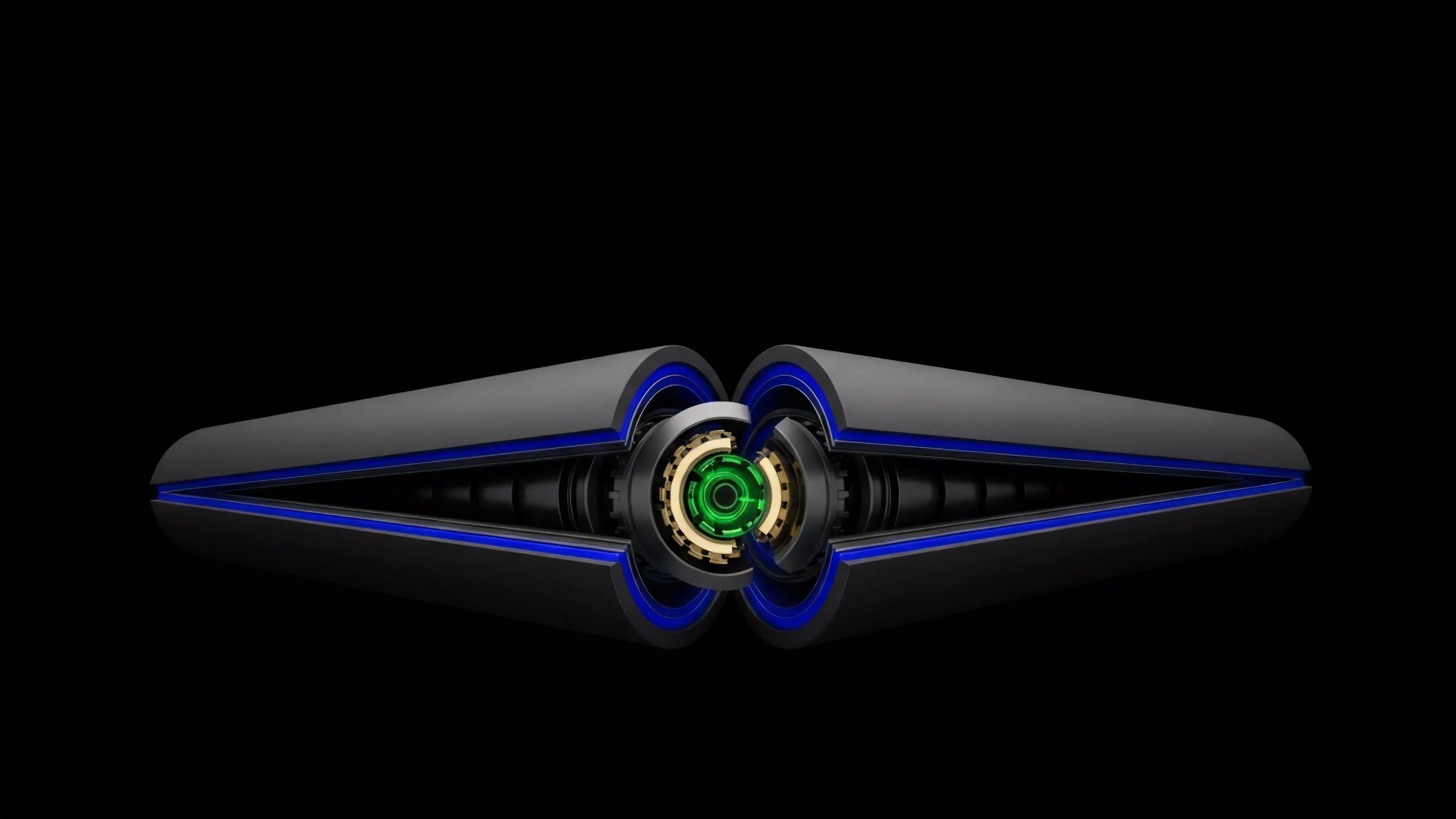
Meaning ⎊ Decentralized Exchange Architectures enable autonomous, trust-minimized asset trading and derivatives settlement through programmable smart contracts.
Decentralized Exchange Oversight


Meaning ⎊ Decentralized Exchange Oversight provides the autonomous, programmatic enforcement of risk and solvency parameters within permissionless trading venues.
Decentralized Exchange Stability


Meaning ⎊ Decentralized Exchange Stability maintains price discovery and protocol solvency through robust collateralization and automated risk management.
Decentralized Exchange Latency


Meaning ⎊ Decentralized Exchange Latency is the critical temporal friction that dictates execution quality, slippage, and systemic risk in automated markets.
Decentralized Exchange Incentives


Meaning ⎊ Decentralized exchange incentives are mechanisms that attract capital to liquidity pools, enabling efficient asset trading and price discovery.
Decentralized Exchange Optimization


Meaning ⎊ Decentralized Exchange Optimization maximizes capital efficiency and liquidity depth through algorithmic management of automated market maker parameters.
Decentralized Exchange Vulnerabilities


Meaning ⎊ Decentralized exchange vulnerabilities constitute systemic technical risks that threaten the integrity and capital efficiency of autonomous financial markets.
Decentralized Exchange Volatility


Meaning ⎊ Decentralized Exchange Volatility dictates the pricing efficiency and risk exposure of liquidity provision within automated financial protocols.
Decentralized Exchange Compliance


Meaning ⎊ Decentralized Exchange Compliance automates regulatory adherence through smart contracts to bridge permissionless innovation with global financial law.
Decentralized Exchange Limitations


Meaning ⎊ Decentralized exchange limitations define the critical boundary between trustless financial integrity and the scalability of global derivatives markets.
Decentralized Exchange Slippage


Meaning ⎊ Price impact caused by a trade in an automated market maker that can lead to losses during the liquidation of collateral.
Decentralized Exchange Strategies


Meaning ⎊ Decentralized exchange strategies enable automated, transparent derivative trading and risk management through autonomous smart contract protocols.
Decentralized Exchange Order Flow


Meaning ⎊ Decentralized Exchange Order Flow functions as the vital, transparent, and highly contested mechanism for price discovery in permissionless markets.
Decentralized Exchange Aggregation


Meaning ⎊ Decentralized exchange aggregation unifies fragmented liquidity pools to minimize slippage and optimize trade execution within decentralized markets.
Decentralized Exchange Regulation


Meaning ⎊ Decentralized Exchange Regulation establishes the necessary legal interface between permissionless protocol architecture and global financial oversight.
Decentralized Exchange Analysis


Meaning ⎊ Decentralized exchange analysis provides the essential quantitative and structural framework for evaluating risk and performance in automated markets.
Decentralized Exchange Infrastructure


Meaning ⎊ Blockchain protocols and smart contracts enabling trustless peer to peer asset trading without centralized intermediaries.
Decentralized Exchange Development


Meaning ⎊ Decentralized exchange development builds autonomous financial infrastructure for trust-minimized asset trading and derivative settlement.
