
Essence
The Zero-Knowledge Margin Engine (ZK-ME) represents the necessary cryptographic primitive for achieving true privacy-preserving solvency verification within decentralized options and perpetual futures markets. Its core function is to decouple the proof of financial compliance ⎊ specifically, that a user’s collateral exceeds their maintenance margin requirements ⎊ from the disclosure of the underlying data that determines that compliance. This resolves the fundamental trade-off that plagues transparent DeFi: the inability to support high-frequency, institutional-grade trading without leaking sensitive order book and position information to adversarial on-chain observers.
The systemic relevance of ZK-ME is immediate and profound. Current decentralized derivative protocols operate with a public ledger where all margin calls, liquidation thresholds, and collateral balances are visible. This front-runs risk for sophisticated market makers, who require information asymmetry to generate alpha, and creates an exploitable attack vector for liquidators who can preemptively calculate optimal liquidation targets.
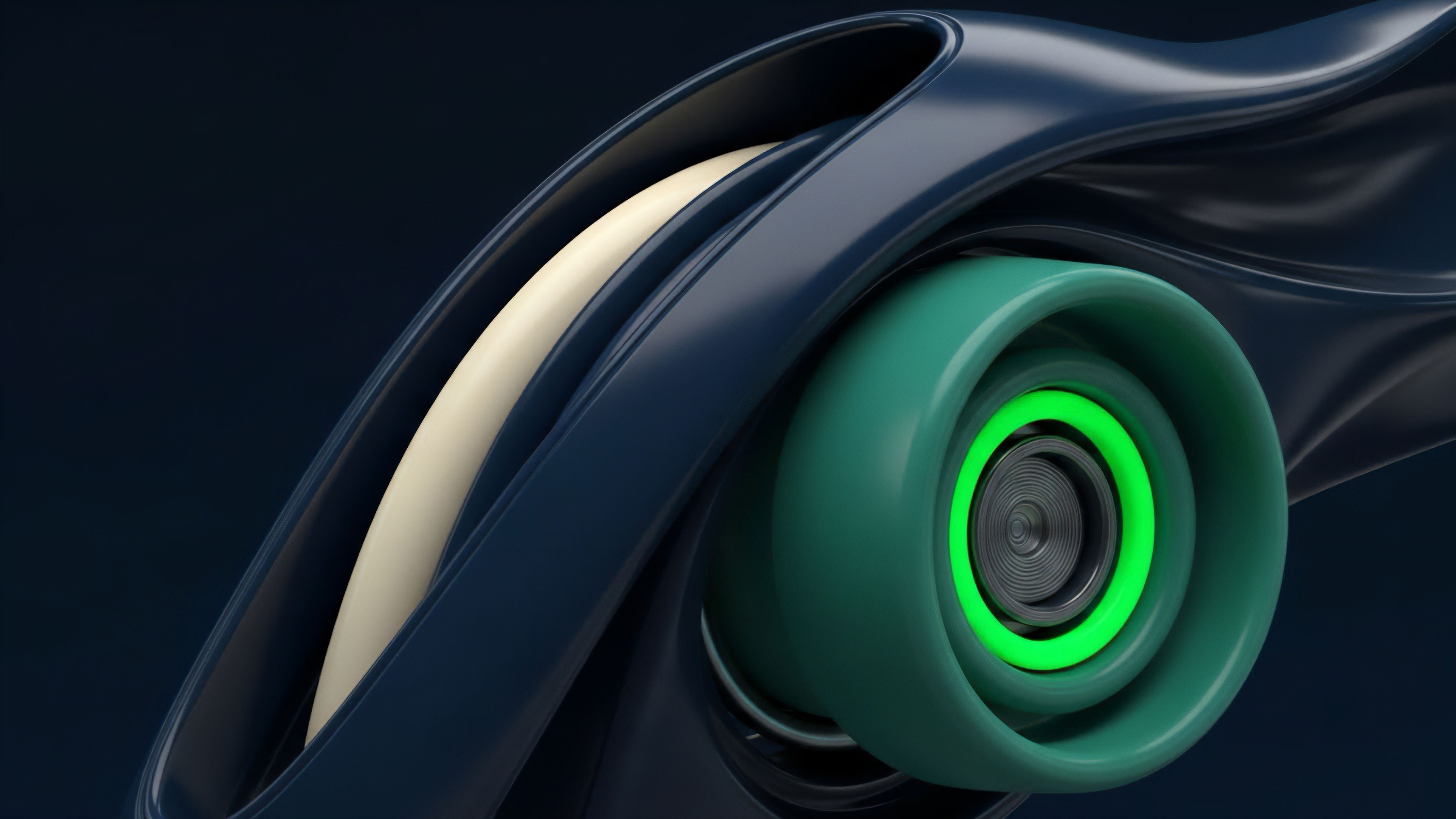
The ZK-ME transforms this adversarial transparency into verifiable, private compliance, shifting the market microstructure toward one where only the validity of the margin requirement is published, not the raw components.
The Zero-Knowledge Margin Engine is the cryptographic bridge between verifiable on-chain solvency and the private position data required for institutional-grade derivatives trading.

Core Problem of Transparent Finance
In an open-book derivatives protocol, the liquidation engine is a public oracle. The inputs to the margin calculation ⎊ position size, mark price, collateral value ⎊ are readable by anyone. This means the exact moment a position becomes underwater is public knowledge, inviting a “liquidation race” where the cost of the liquidation is borne by the protocol or the end-user.
The ZK-ME seeks to replace this public oracle with a cryptographically secured proof system.
Origin
The conceptual genesis of the Zero-Knowledge Margin Engine lies at the intersection of three distinct fields: classical financial cryptography, the invention of succinct non-interactive arguments of knowledge (SNARKs), and the architectural requirements of capital-efficient options clearinghouses. Early cryptographic protocols focused on secure multi-party computation (MPC) for financial functions, but MPC often requires high latency and multiple rounds of interaction, rendering it unsuitable for the low-latency, high-throughput environment of a derivative exchange.
The real breakthrough came with the practical deployment of ZK-SNARKs and ZK-STARKs. While initially designed for scaling transactional throughput on layer-two networks ⎊ the ‘scaling’ problem ⎊ the inherent property of zero-knowledge proofs ⎊ proving a statement without revealing the data ⎊ was quickly recognized as the solution to the ‘privacy’ problem in decentralized finance. The challenge shifted from proving a transaction was valid to proving a complex financial statement was true.

Financial Cryptography Precedents
The intellectual heritage of ZK-ME draws heavily from early work on blind signatures and electronic cash systems, which sought to separate transaction validity from identity. In the derivatives context, this translated to separating margin validity from position identity. This required the development of specialized arithmetic circuits capable of computing the Greeks ⎊ Delta, Gamma, Vega ⎊ and the resulting margin requirement in a zero-knowledge context.
This is a non-trivial computational task, demanding circuits optimized for elliptic curve operations.
- Homomorphic Commitment Schemes: These schemes allow for basic arithmetic operations (addition, multiplication) on encrypted values, a necessary precursor for aggregating collateral values without revealing them.
- Range Proofs: A fundamental building block, used to cryptographically assure that a committed collateral value is non-negative and falls within an expected range, preventing negative balances or absurdly large hidden positions.
- Succinct Non-Interactive Arguments of Knowledge (SNARKs): The primary cryptographic primitive that made ZK-ME technically feasible by reducing the size and verification time of the complex margin proof to a constant, verifiable on-chain.

Theory
The theoretical foundation of the Zero-Knowledge Margin Engine is the construction of a verifiable computational integrity proof over the margin requirement function. The objective is to prove the correctness of the output of a function f(X) without revealing the input X. In the derivatives context, the function f is the margin calculation, and the input X is the user’s portfolio data.
The core equation for any derivative protocol is the maintenance margin check: sumi Collaterali · Pricei ge MMR(Portfolio). The ZK-ME must prove this inequality holds. This is achieved by compiling the entire margin function into a large arithmetic circuit.
The user (Prover) takes their private portfolio data and generates a proof π that the calculation within the circuit yields a “True” statement for the inequality. The verifier (the smart contract) only checks the proof π against the public inputs ⎊ the latest oracle prices and the protocol’s minimum margin rate (MMR) ⎊ without ever seeing the private portfolio.

Quantitative Finance and Proof Complexity
The complexity arises because derivative margin calculations are non-linear, involving option pricing models (like Black-Scholes or variations thereof) and risk parameter functions. The conversion of these floating-point, continuous functions into finite-field arithmetic for a ZK-proof is computationally expensive. It requires fixed-point arithmetic representations and careful circuit design to minimize the number of multiplicative gates ⎊ the primary cost driver in ZK-SNARKs.
Circuit Design Trade-Offs
The choice of ZK-proof system is a trade-off between proof generation time and on-chain verification cost.
| Parameter | ZK-SNARKs (e.g. Groth16) | ZK-STARKs (e.g. FRI-based) |
|---|---|---|
| Proof Size | Constant and small (optimal for on-chain gas) | Larger, logarithmic in circuit size |
| Proof Generation Time | Slower, requires trusted setup | Faster, no trusted setup required |
| Post-Quantum Resistance | Not resistant | Resistant (based on hash functions) |
| Applicability for ZK-ME | High; favored for low on-chain cost | High; favored for transparent setup and speed |
The ZK-ME transforms a public, computationally intensive liquidation check into a private, succinct proof verification that minimizes the attack surface.
Our inability to respect the skew in the current transparent models is the critical flaw in our liquidation architecture ⎊ the ZK-ME offers a pathway to price volatility surfaces privately while proving the correctness of the resulting risk charge. This requires the prover to attest to the correct input of the volatility surface parameters into the pricing circuit, which adds a layer of necessary complexity.

Approach
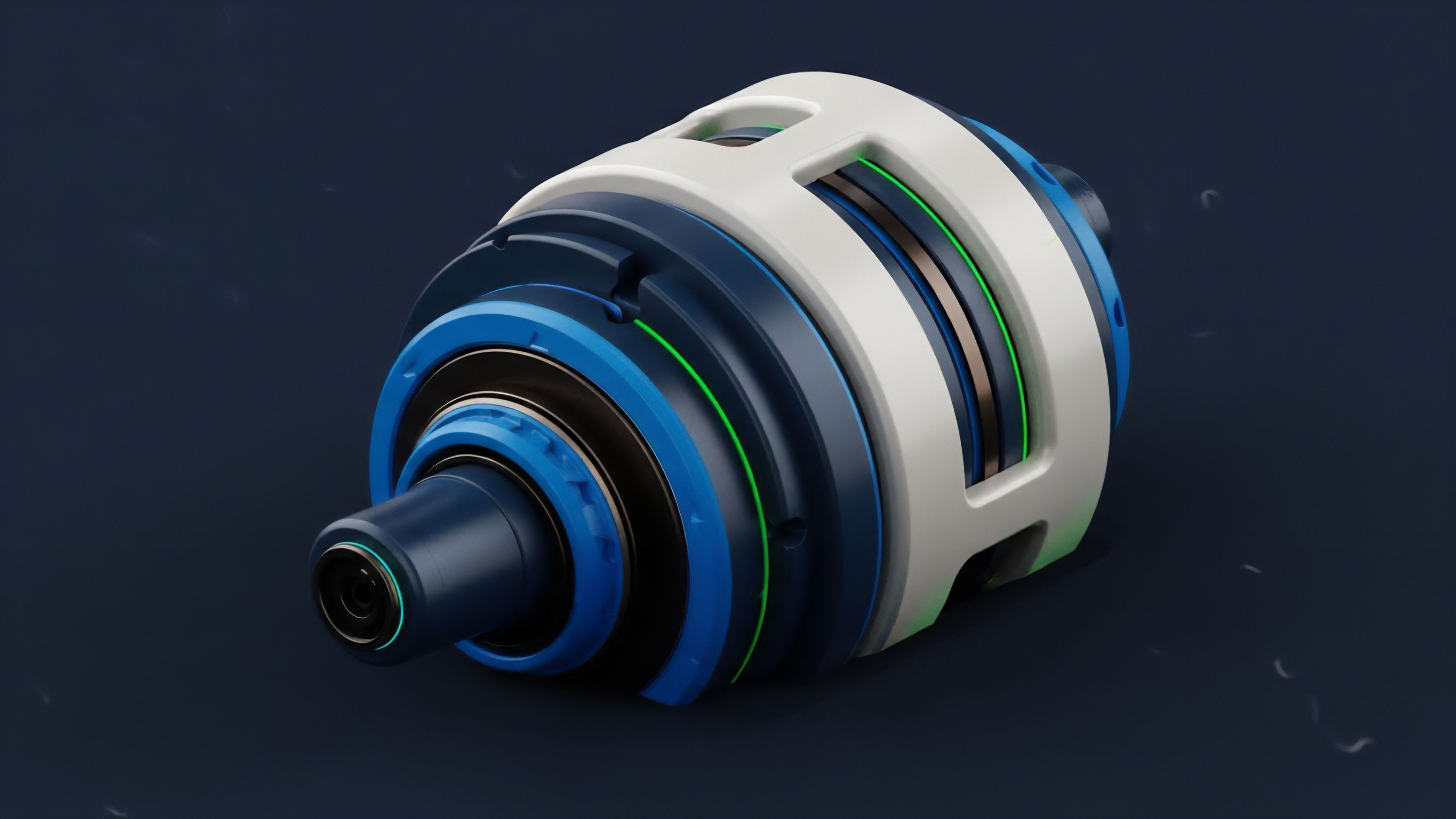
The current approach to deploying the Zero-Knowledge Margin Engine involves an off-chain Prover network and an on-chain Verifier smart contract. This architecture minimizes expensive on-chain computation while retaining the trustless guarantee of the zero-knowledge proof. The user’s client, or a centralized Prover service operated by the exchange, generates the proof of margin solvency.
The system operates on a continuous-time basis, where the user must periodically submit a fresh solvency proof to the Verifier contract to maintain their active trading status. Failure to submit a valid proof before a specified epoch time is the trigger for liquidation, a process that is far cleaner than a public calculation.

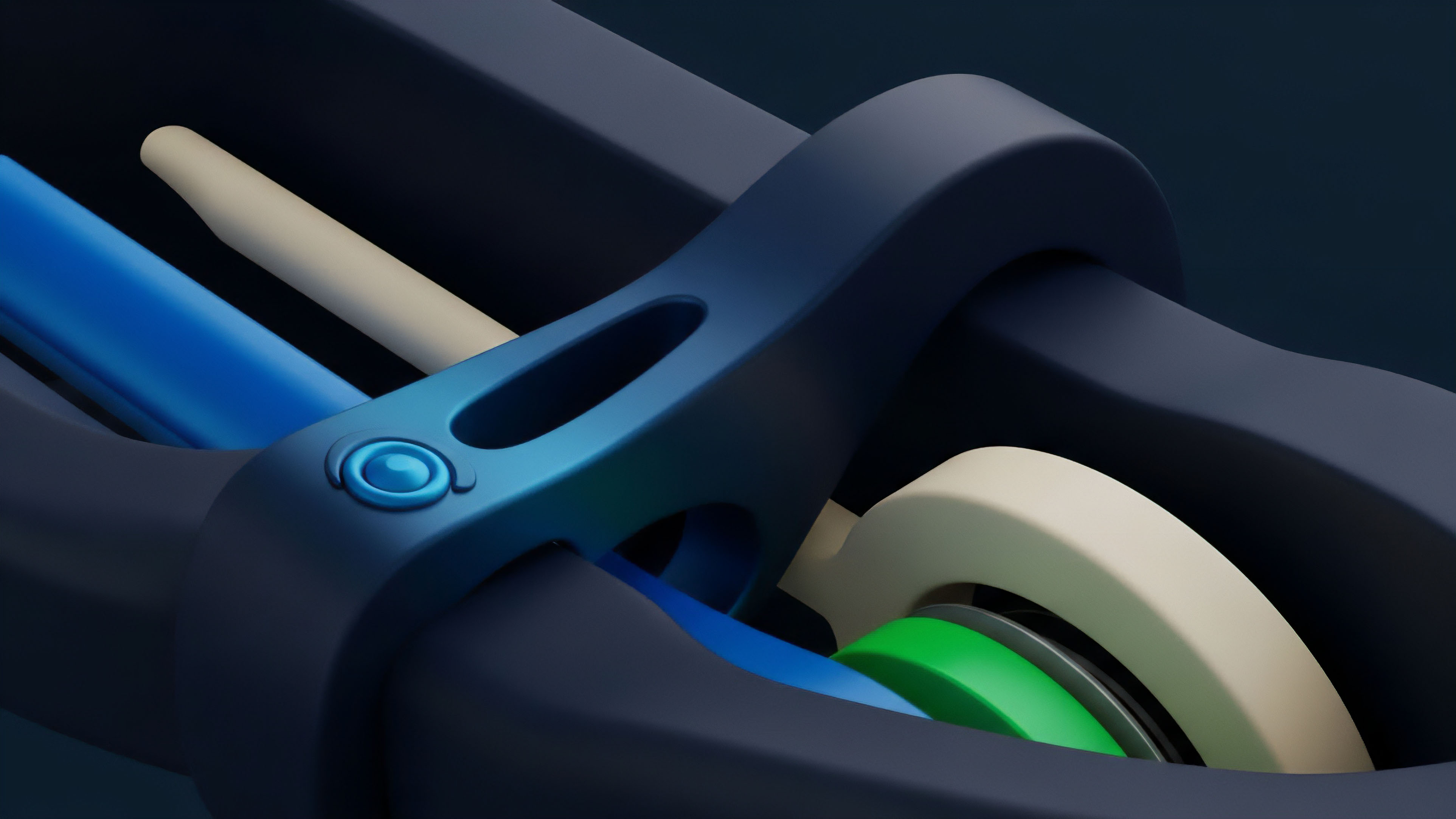
Operational Mechanics of ZK-ME
- Data Commitment: The user commits to their portfolio state (collateral, positions) using a cryptographic commitment scheme (e.g. a Merkle tree root or a Pedersen commitment). This commitment is public.
- Proof Generation: The user’s client executes the margin calculation function within the ZK-circuit, using the private portfolio data and public oracle prices as inputs. The output is a boolean (solvency: True/False).
- Proof Submission: The client submits the resulting succinct proof π to the on-chain Verifier contract. The contract checks π against the public commitment and public prices.
- State Update/Liquidation Trigger: If the proof is valid, the user’s solvency timestamp is updated. If the proof is invalid or not submitted, the system’s liquidation agent is authorized to close the position based on the public commitment, without knowing the specific margin deficit.
The implementation is constrained by the practical costs of proof generation. Generating a ZK-SNARK for a complex financial circuit can take seconds to minutes on standard hardware, creating a latency floor that must be absorbed into the protocol’s risk management parameters. This necessitates careful tuning of the margin maintenance buffer ⎊ a higher buffer reduces the required proof frequency, lowering computational overhead.
The adversarial reality of decentralized finance dictates that any new architecture will be immediately tested for exploits. The ZK-ME is no exception; the primary attack vector is not in the ZK-proof itself ⎊ which is mathematically sound ⎊ but in the oracle feed and the commitment scheme. A compromised oracle or a faulty commitment can lead to a user proving solvency on incorrect inputs, an attack that is difficult to trace because the inputs themselves remain hidden.
Evolution
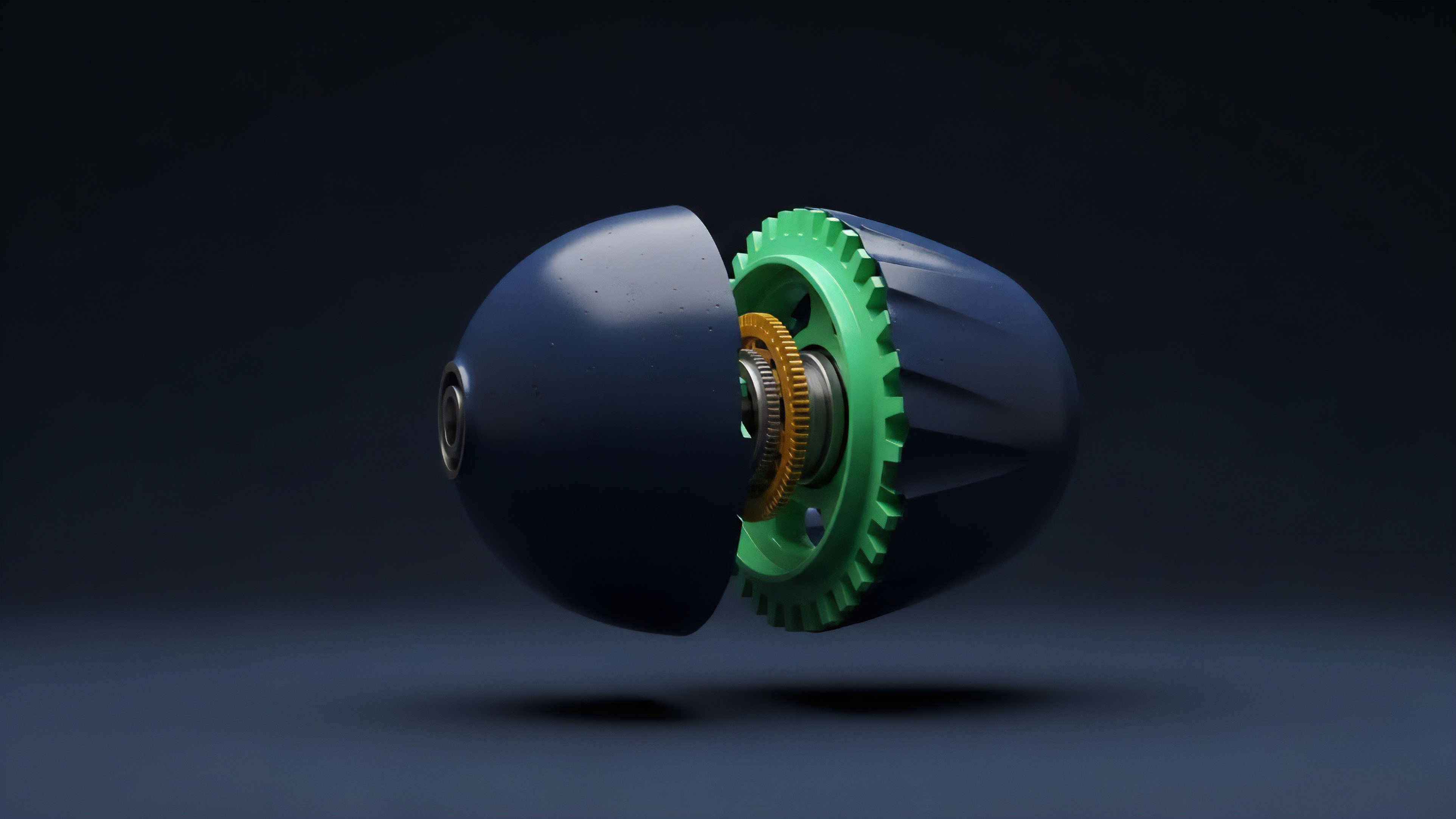
The progression of the Zero-Knowledge Margin Engine has shifted from theoretical possibility to a practical, albeit costly, tool. Initial implementations were hampered by the overhead of a trusted setup ⎊ a requirement for many early ZK-SNARK schemes that created a single point of trust in the system’s security. The move toward transparent, universal setup schemes like PLONK and ultimately ZK-STARKs has allowed for a more robust and decentralized deployment model.
The evolution is characterized by an obsessive focus on efficiency, driven by the financial necessity of minimizing gas costs. Early circuits were monolithic, proving the entire margin function at once. Modern systems employ recursive proof composition ⎊ where a small, fast proof attests to the correctness of a larger, slower proof ⎊ to reduce the final on-chain verification cost to an absolute minimum.

Efficiency and Market Microstructure
The current state-of-the-art ZK-ME systems prioritize proof generation speed off-chain, accepting a larger proof size if it translates to a lower total system latency. This pragmatic trade-off is crucial for attracting high-frequency market makers who view latency as a direct cost.
- Hardware Acceleration: The shift from general-purpose CPUs to specialized hardware (FPGAs, ASICs) for proof generation has drastically reduced latency, pushing ZK-ME toward real-time viability.
- Fixed-Point Optimization: Development of more efficient fixed-point arithmetic libraries specifically tailored for option pricing models, minimizing the number of multiplicative gates in the circuit.
- Batch Verification: Protocols now aggregate multiple user solvency proofs into a single, succinct proof for on-chain verification, amortizing the fixed gas cost across many participants.
The evolution of ZK-ME is a race to reduce the multiplicative gate count, where every optimization translates directly into lower gas fees and faster liquidation certainty.
This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored. The ZK-ME allows a protocol to enforce a complex, proprietary risk model ⎊ one that correctly accounts for volatility clustering and fat tails ⎊ without revealing the model’s intellectual property. This allows for superior risk management, moving past the simplistic linear risk models necessitated by public transparency.

Horizon
The future trajectory of the Zero-Knowledge Margin Engine points toward its total commoditization as the standard for decentralized clearing. The ultimate goal is to see ZK-ME systems capable of running an entire portfolio margin model ⎊ where risk is calculated across all assets and positions, not just per instrument ⎊ in a zero-knowledge context, achieving capital efficiency parity with traditional finance clearinghouses.
This capital efficiency is the real leverage point for profit and stability. By proving cross-collateralization and netting risk across a diverse portfolio privately, a user can maintain the same level of safety with significantly less capital locked up. This dramatically increases return on capital and makes decentralized derivatives a viable alternative for institutional funds.

Systemic Implications and Regulatory Arbitrage
The ZK-ME creates a fascinating tension in the regulatory landscape. If a protocol can cryptographically prove solvency to an auditor (Verifier) without revealing the underlying positions (Privacy), it satisfies the core requirement of systemic stability without violating user data privacy. This architecture may provide a powerful argument for regulatory acceptance, as it enforces compliance by code, verifiable by any regulator who can verify the proof, a level of auditable transparency that centralized exchanges cannot match.
| System Type | Position Privacy | Solvency Verification | Capital Efficiency |
|---|---|---|---|
| Traditional Margin | High (Centralized) | High (Audited Ledger) | High (Portfolio Netting) |
| Transparent DeFi | None (Public Ledger) | High (Public Ledger) | Medium (Isolated Margin) |
| ZK-ME Clearing | High (Cryptographic) | High (Verifiable Proof) | High (Private Portfolio Netting) |
The next generation of ZK-ME will likely be integrated directly into a decentralized autonomous organization (DAO) governance structure, where the protocol’s risk parameters ⎊ the Maintenance Margin Rate, the Liquidation Haircut ⎊ are themselves voted on and updated through a ZK-proof that demonstrates the parameter change does not introduce systemic risk. This shifts the adversarial environment from the market to the governance layer, forcing us to consider the game theory of parameter selection.
The challenge ahead is not cryptographic; it is social. We must design incentive structures that prevent Provers from colluding with users to submit proofs based on stale or manipulated oracle data, a weakness that the best mathematics cannot solve. The architecture is sound; the human element remains the greatest variable.

Glossary

Financial Cryptography
Volatility Skew

Zk-Snarks

Collateral Management
Black-Scholes Model
Liquidity Provision
Perpetual Futures

Adversarial Game Theory

Algorithmic Solvency






