Essence
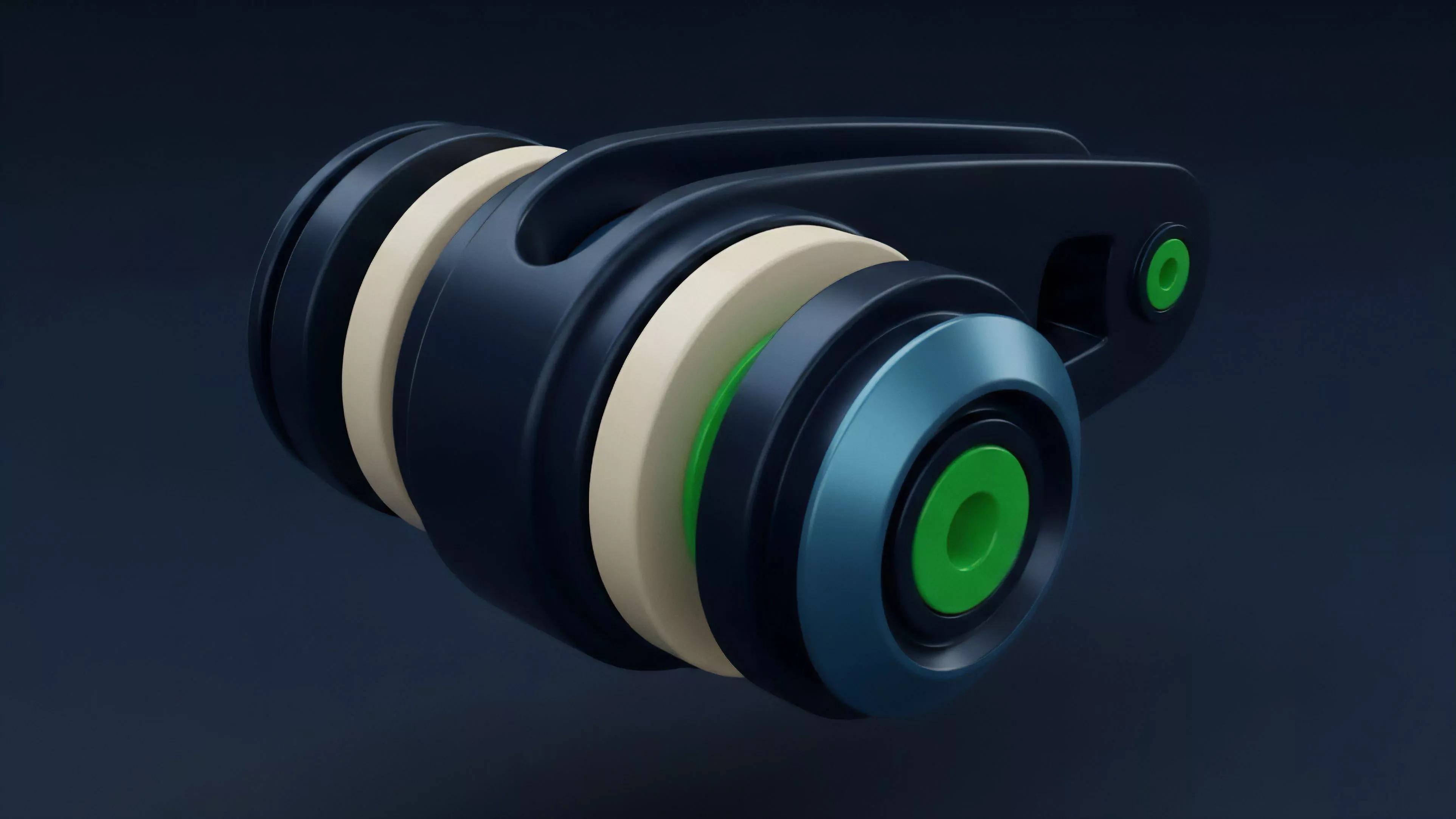
Threshold Signatures represent a cryptographic paradigm where a private key is never held in its entirety by any single entity. Instead, the key exists as a collection of secret shards distributed among a defined set of participants. A functional signature requires a minimum quorum of these participants to cooperate, mathematically combining their individual shards to produce a valid signature for a transaction.
This mechanism transforms the single point of failure inherent in traditional signing processes into a distributed, multi-party computation protocol.
Threshold Signatures replace singular private key control with a distributed quorum requirement to generate valid transaction signatures.
The systemic relevance of this architecture resides in its ability to decouple asset control from individual exposure. In the context of decentralized derivatives, this provides a mechanism for institutional-grade custody and automated execution that remains trust-minimized. The security model shifts from protecting a single secret to securing the operational integrity of the distributed nodes, fundamentally altering the risk profile of high-frequency settlement engines.

Origin
The mathematical foundations of Threshold Signatures trace back to the development of secret sharing schemes, most notably the work of Adi Shamir in 1979.
These early frameworks established the concept of dividing a secret into multiple parts, where a subset of parts could reconstruct the original information. Over decades, this concept migrated from theoretical cryptography into the practical requirements of distributed systems and secure multi-party computation. The evolution toward modern implementations, such as Threshold ECDSA, emerged as a direct response to the vulnerabilities inherent in centralized custody models.
As digital asset markets grew, the limitations of standard multisig wallets ⎊ specifically their on-chain footprint and lack of flexibility ⎊ necessitated a more efficient, off-chain cryptographic solution. Developers sought a method to achieve the same security guarantees as multisig while maintaining the performance characteristics of a single-key signature.
- Shamir Secret Sharing provides the foundational mathematical basis for splitting cryptographic keys into independent, distributed components.
- Multi-Party Computation protocols allow nodes to compute a signature without ever reconstructing the full private key in any single memory space.
- Threshold ECDSA implementations facilitate compatibility with existing blockchain networks while enabling decentralized control over asset movement.

Theory
The architectural integrity of Threshold Signatures relies on the rigorous application of distributed key generation and signing protocols. Unlike traditional signing, where a private key executes a transformation on a message, the threshold variant requires nodes to perform partial computations. These partial signatures are then aggregated into a final, valid signature that appears identical to one produced by a standard private key.
The signature generation process involves partial computation across distributed nodes, ensuring the full private key remains unexposed throughout the lifecycle of the transaction.
The mathematical complexity is governed by the specific threshold parameters, often denoted as t-of-n, where t represents the minimum number of participants required to generate a signature out of a total pool of n participants. This structure introduces significant game-theoretic considerations, as the liveness and honesty of the participants determine the availability and security of the funds.
| Parameter | Systemic Impact |
| Threshold Count | Determines the minimum collusion or failure required to compromise the system. |
| Node Distribution | Influences the geographical and institutional diversity, mitigating systemic contagion risks. |
| Computation Latency | Impacts the throughput of settlement engines in high-frequency trading environments. |
The protocol physics here are unforgiving. If the quorum is not met, the system halts; if the quorum is corrupted, the asset is lost. This is a hard constraint that forces participants into an adversarial alignment, where rational actors are incentivized to maintain the security of the threshold set to preserve the value of the underlying assets.

Approach
Modern deployment of Threshold Signatures within derivative protocols focuses on achieving capital efficiency while minimizing counterparty risk.
Current architectures leverage these schemes to manage collateral in automated clearing houses and decentralized exchanges. By offloading the signing process to a threshold network, protocols can facilitate near-instantaneous collateral movement without waiting for the overhead of standard on-chain multisig verification. This approach is particularly critical for managing margin calls and liquidation triggers.
When a market event forces a position closure, the threshold network can automatically execute the settlement signature, provided the pre-defined programmatic conditions are satisfied. This reduces the latency between market volatility and risk mitigation, directly addressing the systemic risks associated with slow liquidation processes.
- Automated Clearing systems utilize threshold nodes to execute trades based on smart contract logic without human intervention.
- Institutional Custody solutions employ these signatures to distribute risk across multiple geographic locations and hardware security modules.
- Cross-Chain Bridges rely on threshold networks to verify and authorize the transfer of assets between distinct blockchain environments.
The trade-off involves increased operational complexity. Maintaining a robust set of threshold nodes requires sophisticated coordination and monitoring to ensure consistent liveness. Any failure in the communication layer between these nodes can lead to temporary asset locking, highlighting the importance of network resilience and participant incentives in these systems.

Evolution
The trajectory of Threshold Signatures has moved from academic obscurity to the backbone of institutional digital asset infrastructure.
Early implementations were plagued by high computational overhead and fragile network requirements. The transition toward more efficient protocols has allowed for wider adoption, enabling the scaling of decentralized derivatives that require high-frequency signing capabilities. As the industry matured, the focus shifted from simple key management to the integration of these signatures within complex governance and policy frameworks.
This allows for dynamic threshold settings, where the number of required participants can change based on the value of the transaction or the current risk state of the market. The evolution reflects a broader shift toward programmable trust, where the cryptographic requirements are directly linked to the economic reality of the underlying financial instrument.
Dynamic threshold adjustment enables protocols to scale security requirements based on transaction value and prevailing market risk conditions.
This development mirrors the history of traditional finance, where settlement mechanisms evolved from manual ledgers to electronic systems, each iteration requiring higher levels of speed and security. We are currently witnessing the maturation of these cryptographic primitives into reliable, battle-tested components of global financial architecture.

Horizon
The future of Threshold Signatures involves the integration of zero-knowledge proofs to enhance the privacy and verifiability of the signing process. By combining these technologies, future protocols will allow nodes to prove they have performed the correct computation without revealing any information about the shards themselves.
This will significantly reduce the surface area for side-channel attacks and enhance the overall resilience of the network. Furthermore, the integration of these signatures with hardware-based trusted execution environments will likely become standard practice. This creates a multi-layered defense strategy where both the cryptographic protocol and the physical hardware must be compromised to gain unauthorized access.
The ultimate objective is a global, permissionless derivative market where settlement is as secure as the underlying blockchain, yet as fast as traditional high-frequency trading venues.
| Future Development | Anticipated Outcome |
| Zero Knowledge Integration | Increased privacy and reduced information leakage during the signing process. |
| Hardware Root of Trust | Enhanced physical security for node operators participating in threshold sets. |
| Automated Governance | Dynamic threshold scaling based on real-time volatility and risk metrics. |
The path forward is clear. As decentralized markets grow, the reliance on these cryptographic primitives will increase, cementing their role as a fundamental requirement for secure, scalable financial infrastructure.