Essence
Systemic Fragility
Systems Risk defines the probability that a failure in one node of the digital asset network triggers a widespread collapse. This phenomenon manifests when interconnected protocols share liquidity, collateral, or data feeds. Contagion occurs as insolvency travels through these links, turning isolated losses into systemic events.
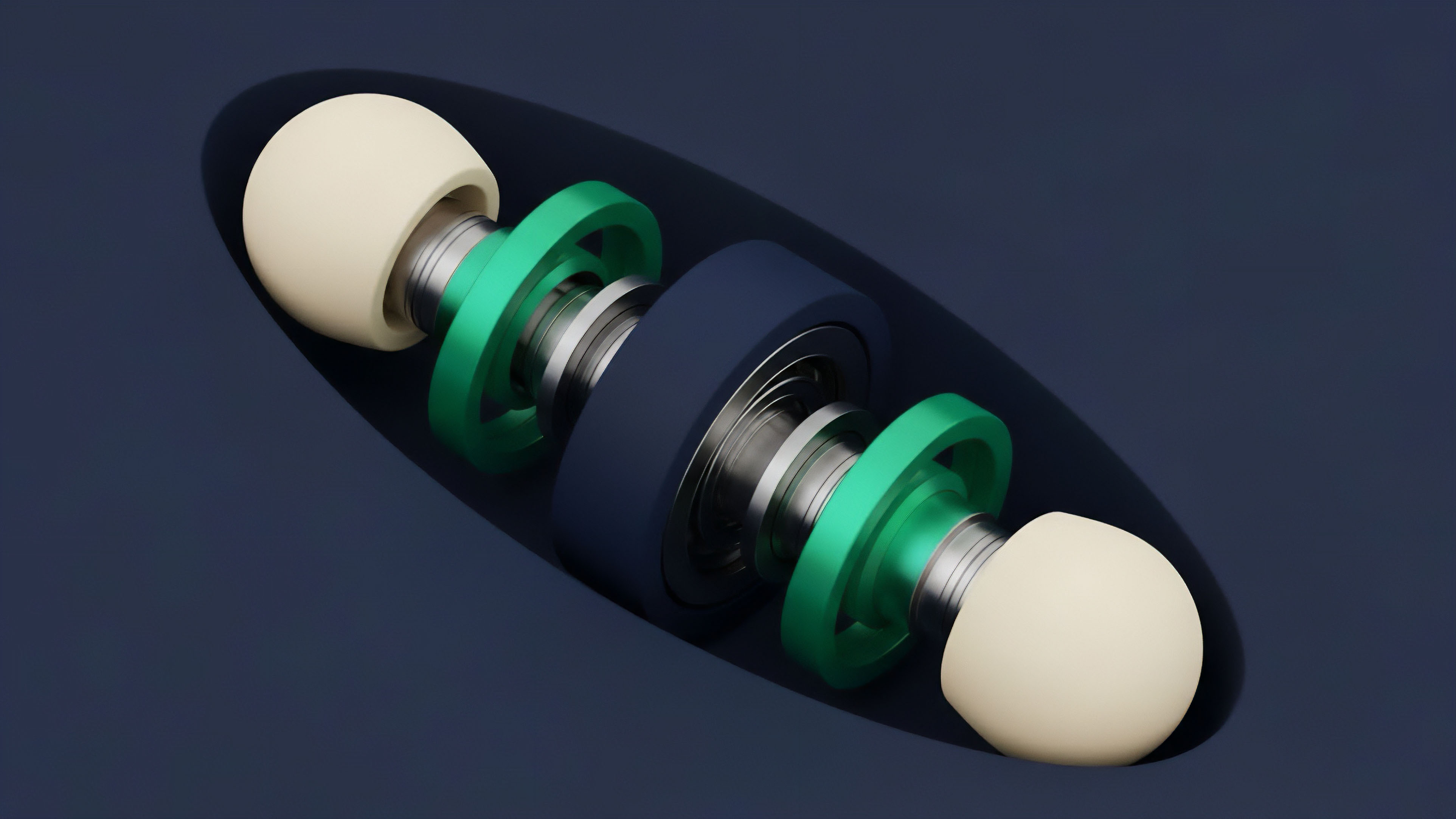
The architecture of decentralized finance relies on composability, where one application serves as the base for others. While this increases utility, it also creates hidden dependencies. A vulnerability in a widely used stablecoin or a major lending market can paralyze the entire network.
- Interconnected Liquidity creates paths for rapid value extraction across multiple venues.
- Collateral Correlation ensures that a price drop in one asset devalues the entire lending market.
- Oracle Dependency links the security of multiple protocols to a single data source.

Transmission Paths
The transmission of Systems Risk often bypasses traditional circuit breakers. In a decentralized environment, code execution is atomic and irreversible. When a liquidity pool experiences a drain, the imbalance propagates to every aggregator and derivative contract linked to that pool.
This creates a state of Systemic Fragility where the health of the most secure protocol is limited by the weakest link in its collateral chain.
Origin
The study of financial Contagion traces back to traditional market crises where bank runs and credit freezes decimated global economies. In the digital asset space, these patterns reappeared with increased velocity. Early instances involved single-point failures like exchange hacks.
As the market matured, the introduction of decentralized lending and synthetic assets introduced structural risks. The 2022 collapse of major algorithmic stablecoins and centralized lenders demonstrated how leverage and inter-entity debts create a fragile web.
| Transmission Vector | Traditional Finance | Digital Assets |
|---|---|---|
| Velocity | Days to Weeks | Seconds to Minutes |
| Transparency | Opaque Balance Sheets | On-chain Ledgers |
| Settlement | Delayed Clearing | Atomic Settlement |
Historical precedents in crypto options show that Systems Risk is often mispriced during periods of low volatility. Participants assume that the independence of protocols provides safety, yet the underlying liquidity often originates from the same concentrated sources. This concentration creates a single point of failure that remains hidden until a volatility spike occurs.

Theory

Recursive Liquidation Mechanics
The mathematical modeling of Systems Risk focuses on recursive feedback loops.
When a large participant faces liquidation, their forced selling drives prices lower, triggering further liquidations. This process is quantified through the interaction of market depth and margin requirements. Recursive Leverage acts as a multiplier, where a small percentage move in the underlying asset leads to a total wipeout of collateralized positions.
Recursive liquidation loops function as a self-reinforcing mechanism that transforms localized volatility into systemic insolvency.
Delta Hedging Feedback
Delta Hedging by option market makers adds another layer of risk. As prices move toward heavy strike concentrations, market makers must adjust their hedges, often trading in the same direction as the market move. This accelerates volatility and deepens the Contagion.
The interaction between Gamma exposure and spot liquidity creates a “feedback loop of doom” where the hedging process itself consumes the available liquidity needed to stabilize the market.
- Asset Devaluation reduces the health factor of collateralized positions.
- Automated Liquidation triggers market sell orders to recover debt.
- Slippage increases as liquidity vanishes during high-stress periods.
- Feedback Amplification occurs as lower prices trigger the next tier of liquidations.
Approach
Current risk management focuses on over-collateralization and real-time monitoring. Protocols use insurance funds to absorb losses that exceed the value of liquidated collateral. Market participants utilize stress testing to model how their portfolios perform during extreme tail events.
Advanced strategies involve cross-protocol hedging and the use of put options to protect against systemic drawdowns.
| Risk Mitigation Tool | Function | Limitation |
|---|---|---|
| Insurance Funds | Absorb bad debt | Can be depleted in seconds |
| Circuit Breakers | Pause trading | Fragmented across venues |
| Dynamic Margining | Adjust requirements | May trigger more liquidations |
The efficacy of risk management in crypto options depends on the ability to predict the correlation of assets during extreme market stress.
The use of Value at Risk (VaR) models is common, though these often fail to account for the “fat tail” distributions inherent in digital assets. Systems architects now prioritize Expected Shortfall and tail-risk hedging to ensure survival during black swan events.

Evolution
Economic Attack Vectors
The environment of risk shifted from simple code exploits to sophisticated economic attacks. Initially, security focused on preventing unauthorized access to funds.
Today, the major threat is the manipulation of market conditions to trigger protocol-level failures. Oracle Manipulation and flash loan attacks allow adversaries to create artificial price points, triggering mass liquidations that benefit the attacker’s derivative positions.
The transition from technical vulnerabilities to economic exploits represents a maturation of adversarial strategies in digital finance.

Staking Derivative Risks
The rise of liquid staking and re-staking has added new layers of involvement. The same capital is used to secure multiple layers of the network, creating a Liquidity Cascade risk. If the underlying validator set faces slashing or technical failure, the impact ripples through every derivative layer, potentially leading to a total loss of confidence in the network’s security model.
Horizon
Algorithmic Circuit Breakers
Future developments aim to create more resilient architectures through automated risk parameters and cross-chain insurance.
Proactive circuit breakers that monitor on-chain health metrics could pause protocols before Contagion spreads. These systems would function as an immune system for decentralized finance, isolating failing nodes before they infect the broader network.
Algorithmic resilience requires the inclusion of real-time risk telemetry into the protocol’s autonomous decision-making engine.

Verifiable Solvency
The inclusion of zero-knowledge proofs may allow for private yet verifiable solvency checks, reducing the risk of panic-driven bank runs. By providing proof of reserves without revealing sensitive trade data, protocols can maintain trust during periods of high Systems Risk. This transparency is the only path toward a stable and mature decentralized financial system.

Glossary
Mev Exploitation

Nash Equilibrium
Order Flow Toxicity

Sequencer Failure

Tail Risk

Auto-Deleveraging

Agent-Based Modeling
Byzantine Fault Tolerance
Censorship Resistance