
Essence
Static Analysis Techniques function as the pre-execution inspection layer for decentralized financial protocols. These methods examine the structural integrity of smart contract bytecode or source code without requiring active transaction simulation on a live network. By identifying logical inconsistencies, insecure coding patterns, and potential reentrancy vectors, these techniques serve as the first line of defense for protocol solvency.
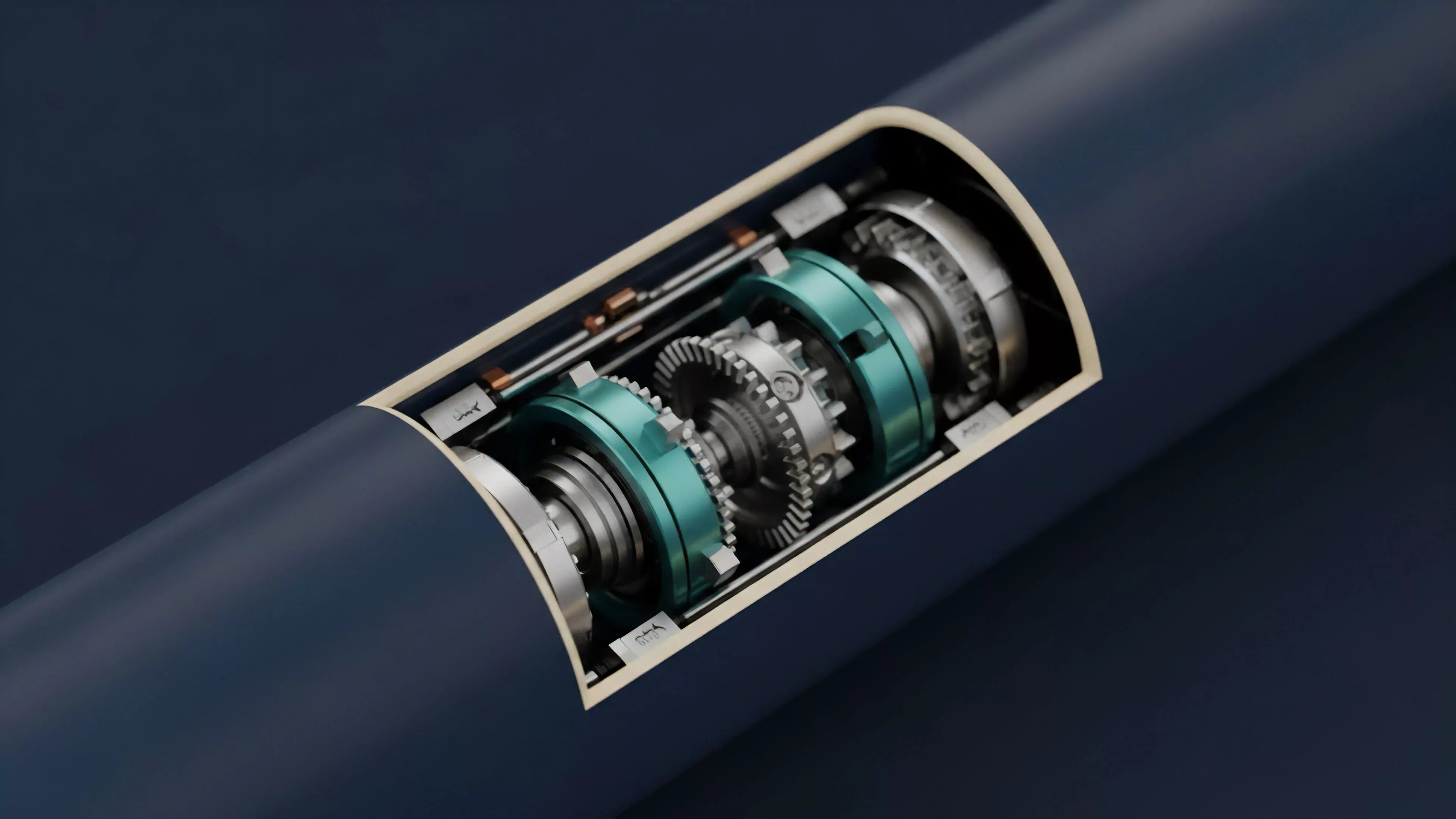
Static analysis provides a deterministic audit of contract logic by mapping code execution paths before deployment.
The primary objective involves identifying vulnerabilities that threaten the collateralization ratios and liquidation mechanisms inherent in crypto options. When evaluating derivative protocols, these techniques pinpoint weaknesses in the underlying smart contract architecture, ensuring that the programmed logic aligns with the intended financial risk parameters.

Origin
The roots of Static Analysis Techniques reside in formal verification methods developed for traditional software engineering. Researchers adapted these concepts to address the unique adversarial environment of programmable money.
Early iterations focused on basic syntax checking, but the rise of decentralized finance demanded a shift toward deeper, semantic analysis capable of parsing complex state machines.
- Formal Verification introduced the rigorous mathematical proof of code correctness.
- Abstract Interpretation allowed for the approximation of program behaviors to identify edge cases.
- Control Flow Analysis mapped the potential execution paths within a contract to detect unreachable code or logic loops.
This evolution was driven by the necessity to mitigate systemic risks within nascent liquidity pools. Developers recognized that traditional testing regimes were insufficient for immutable, high-stakes financial instruments, necessitating automated tools that could scrutinize the entire codebase for latent exploits.

Theory
The theoretical framework for Static Analysis Techniques relies on transforming contract logic into mathematical models. By constructing a Control Flow Graph, analysts visualize every possible state transition within a protocol.
This allows for the detection of non-deterministic behavior or unauthorized access points that could compromise the margin engine of an options platform.
| Technique | Mechanism | Primary Utility |
| Taint Analysis | Tracks untrusted inputs | Prevents injection attacks |
| Symbolic Execution | Explores program paths | Finds edge-case vulnerabilities |
| Pattern Matching | Scans for known flaws | Detects common coding errors |
Symbolic execution models code inputs as variables to exhaustively test state space coverage.
The precision of these models depends on the granularity of the underlying semantic representation. By analyzing the interaction between the contract state and external oracle inputs, analysts define the boundaries of acceptable behavior. If a state transition deviates from these parameters, the system flags a potential exploit before it manifests as a financial loss.
One might consider how this rigorous pursuit of code perfection mirrors the early days of structural engineering, where every rivet and beam was calculated for maximum stress, yet human error often remained the hidden variable in the equation. This realization drives the constant refinement of our analytical tools.

Approach
Current implementation strategies for Static Analysis Techniques prioritize integration within the continuous integration pipeline.
Developers utilize automated scanners that execute during the build process to provide immediate feedback on code safety. This proactive stance ensures that no contract reaches mainnet without passing a series of automated safety thresholds.
- Automated Scanning identifies common vulnerability patterns within minutes of code submission.
- Path Exploration utilizes computational solvers to determine if specific malicious states are reachable.
- Constraint Solving evaluates the feasibility of an attacker gaining control over specific protocol functions.
Automated pipelines force immediate accountability by surfacing vulnerabilities before deployment.
The focus remains on minimizing false positives while maximizing detection depth. Advanced tools now incorporate machine learning to recognize novel attack vectors that standard rule-based systems might overlook. This ongoing battle between automated defense and evolving exploit techniques dictates the efficacy of any derivative protocol’s risk management framework.

Evolution
The trajectory of Static Analysis Techniques has shifted from simple pattern recognition to holistic protocol modeling.
Initial tools were restricted to individual contract analysis, failing to capture the systemic risk inherent in interconnected liquidity pools. Current systems now account for cross-contract interactions and external dependency risks, reflecting the complexity of modern decentralized derivative structures.
| Generation | Focus Area | Risk Mitigation |
| First | Syntax errors | Basic code hygiene |
| Second | Logical flaws | Smart contract exploits |
| Third | Systemic composition | Protocol contagion risks |
The integration of Formal Methods into mainstream development has transformed the standard for code quality. Projects now view these techniques not as optional audits but as essential components of their financial infrastructure. This maturity indicates a broader recognition that protocol security is the fundamental determinant of market stability and user trust.
Horizon
Future developments in Static Analysis Techniques will likely focus on real-time monitoring and autonomous response mechanisms.
As protocols become increasingly modular, the ability to analyze dynamic, evolving systems will become paramount. Integrating static analysis with on-chain runtime monitoring will provide a continuous safety loop, allowing protocols to pause or adjust parameters if a vulnerability is detected post-deployment.
Real-time integration will bridge the gap between static code verification and live market security.
The goal is to create self-healing protocols capable of identifying and isolating threats without human intervention. This transition represents the next step in the professionalization of decentralized finance, where code safety is enforced by autonomous agents that understand both the technical architecture and the economic consequences of potential failures.
