Essence
Smart Contract Execution Security represents the operational integrity of automated financial logic within decentralized environments. It functions as the definitive mechanism ensuring that programmable code adheres strictly to intended financial outcomes without unauthorized modification or exploitation. The domain concerns itself with the reliability of state transitions in distributed ledgers where human intervention is absent and code acts as the sole arbiter of value transfer.
Smart Contract Execution Security defines the threshold where cryptographic verification meets predictable financial outcome within automated systems.
The primary objective involves minimizing the attack surface presented by immutable, autonomous protocols. Participants rely on this security to maintain confidence that derivative pricing, margin maintenance, and liquidation processes execute precisely as designed, regardless of adversarial attempts to manipulate blockchain state or oracle data feeds.

Origin
The requirement for robust Smart Contract Execution Security emerged directly from the rapid expansion of decentralized finance platforms. Early iterations of automated market makers and lending protocols suffered from rudimentary code audits and insufficient testing of edge-case scenarios.
These initial failures demonstrated that financial systems built on blockchain infrastructure remain vulnerable to logic errors, reentrancy attacks, and improper privilege management.
- Code Audit Maturity: Developers moved from simple functional testing to rigorous formal verification methods.
- Adversarial Simulation: Protocols began utilizing white-hat bounty programs to identify systemic weaknesses before exploitation.
- Infrastructure Hardening: The transition toward modular, upgradeable proxy contracts necessitated new standards for access control and emergency pause functionality.
These early challenges necessitated a shift toward defensive programming, where the architecture of the contract itself prioritizes resilience against malicious actors seeking to drain liquidity pools or trigger erroneous liquidation events.

Theory
The theoretical foundation rests upon the intersection of Formal Verification and Game Theoretic Modeling. Analysts evaluate the execution path of every transaction to ensure that state changes remain within defined economic bounds. By applying mathematical rigor to code, developers prove that specific contract states are unreachable by unauthorized actors, thereby securing the financial logic underpinning complex derivative instruments.
Mathematical proof of code correctness replaces human trust, ensuring that execution logic remains invariant under adversarial stress.
The system operates under constant observation from automated agents. These agents monitor for anomalies in transaction flow or pricing discrepancies that might indicate an impending exploit.
| Analytical Framework | Primary Focus |
| Formal Verification | Mathematical proof of code intent |
| Economic Invariant Testing | Maintaining solvency during volatility |
| Access Control Auditing | Limiting administrative privileges |
The internal logic must account for the reality that the execution environment is inherently hostile. Every line of code functions as a potential vector for economic extraction, requiring a design philosophy that anticipates failure rather than assuming perfect operation.
Approach
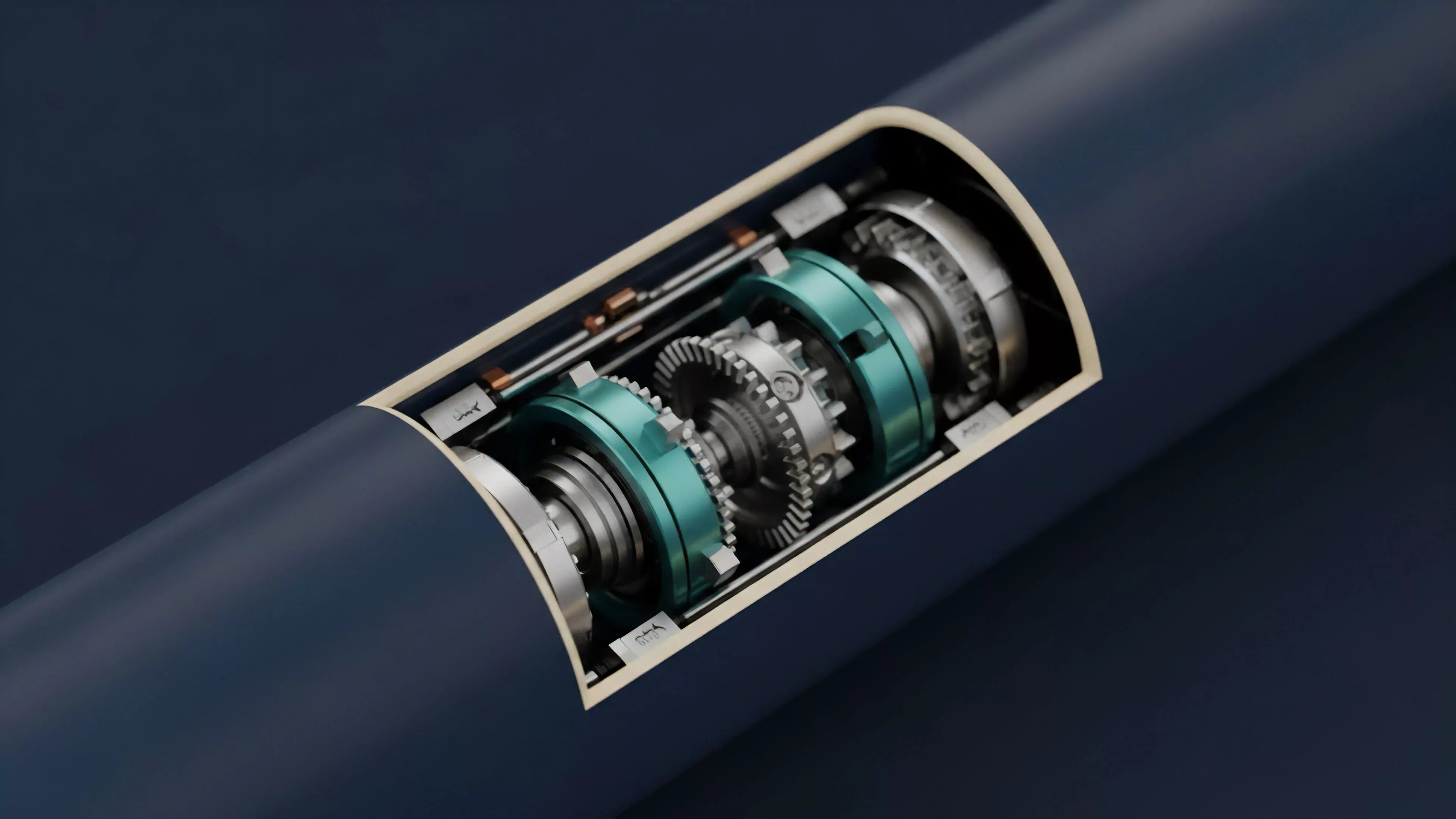
Modern practitioners utilize a multi-layered defense strategy. This involves integrating Static Analysis tools that scan code for common vulnerabilities alongside dynamic runtime monitoring systems.
These monitoring tools observe on-chain activity, providing real-time alerts or automated circuit breakers when transaction patterns deviate from established norms.
- Circuit Breakers: Automated mechanisms halt contract execution when anomalous trading volume or extreme price volatility is detected.
- Multi-Signature Governance: Critical protocol changes require consensus among geographically distributed stakeholders to prevent single-point failures.
- Oracle Redundancy: Protocols utilize multiple decentralized data sources to prevent price manipulation that could trigger faulty liquidations.
This approach acknowledges that absolute security is unattainable. The focus shifts toward containment and mitigation, ensuring that if a vulnerability is discovered, the systemic impact remains isolated and limited in scope.

Evolution
The field has moved beyond simple code review toward the implementation of Programmable Security Layers. Protocols now incorporate built-in defensive primitives that adapt to changing market conditions.
This evolution reflects the increasing complexity of crypto derivatives, which demand more sophisticated handling of leverage and margin requirements.
Adaptive security protocols adjust defensive parameters in real-time based on observed network stress and market volatility.
This shift highlights a transition from static, once-and-done security audits to continuous, proactive risk management. The architecture now treats security as a dynamic, evolving property of the system rather than a fixed state achieved at deployment.
| Stage | Focus |
| Pre-Mainnet | Formal verification and peer review |
| Active Protocol | Real-time anomaly detection |
| Incident Response | Automated circuit breakers and pausing |
The current environment demands that protocols maintain extreme vigilance. Any deviation in logic or unexpected interaction with external protocols results in immediate investigation, reflecting the high stakes involved in managing billions in collateral.

Horizon
Future developments in Smart Contract Execution Security will likely center on autonomous, AI-driven security agents. These agents will possess the capability to simulate thousands of potential transaction paths in milliseconds, identifying vulnerabilities that human auditors might miss. Furthermore, the integration of privacy-preserving technologies will allow for more robust verification of execution logic without exposing sensitive trade data to public scrutiny. The trajectory points toward protocols that possess inherent, self-healing capabilities. These systems will detect unauthorized modifications or logic exploits and automatically revert to a secure state, effectively neutralizing threats before they propagate through the broader decentralized market. The challenge remains in balancing this defensive complexity with the need for high throughput and capital efficiency in derivative trading. What happens when the defensive agents themselves become the primary vector for systemic risk within an increasingly automated financial architecture?
