Essence
The core concept of a shared security model in decentralized finance (DeFi) represents a fundamental shift in how protocols acquire and maintain trust. The prevailing model, which we will define as the Restaking Security Model, challenges the notion that every application must bootstrap its own security from scratch. This model allows new protocols, often referred to as Actively Validated Services (AVSs), to leverage the existing economic security of a larger, established network.
In practice, this means validators of a primary chain, such as Ethereum, can “restake” their already-staked collateral to provide security guarantees for secondary protocols. The financial benefit is twofold: it provides a new revenue stream for stakers, and it significantly lowers the barrier to entry for new applications, particularly those in the derivatives space that require robust, real-time security guarantees.
This architecture is particularly relevant to crypto options and derivatives protocols, where a single point of failure in a price feed or liquidation engine can lead to cascading losses. A shared security model offers a more robust solution than relying on a small, isolated set of validators. The economic incentive for validators to secure these AVSs is tied directly to the value of their underlying stake; a failure to perform correctly results in a loss of collateral through a process called slashing.
This creates a powerful alignment of incentives, ensuring that the security provided is commensurate with the value being secured. The design philosophy behind restaking is one of capital efficiency, allowing a single asset to secure multiple layers of the financial stack simultaneously.
The Restaking Security Model allows new protocols to inherit security from an established network, creating a more efficient and robust foundation for decentralized applications.

Origin
The concept of shared security originates from the challenge of building new blockchains and decentralized applications in an environment dominated by a few large, highly secure networks. The “cold start problem” for new protocols is significant: how does a new chain attract enough value to secure itself against a 51% attack when it has no intrinsic value to begin with? The first iterations of shared security focused on “renting” security from a main chain, where a new chain would pay a fee to be secured by the main chain’s validators.
This approach, however, often resulted in high costs and limited flexibility for the new protocols.
The evolution to the current Restaking Security Model, specifically in the context of Ethereum, was driven by the recognition that staked ETH represented a vast, underutilized pool of economic security. The genesis of restaking was the idea that a staker’s capital, which is already securing the base layer, could be repurposed to provide additional security guarantees for other services without requiring a separate, additional stake. This innovation moves beyond simple security sharing to create a marketplace for trust.
Stakers can dynamically choose which AVSs to secure, based on the risk-reward profile of each AVS. This represents a significant advancement in protocol design, shifting from a rigid, top-down security model to a more flexible, market-driven approach.

Game Theory and Slashing Conditions
The theoretical foundation of restaking relies heavily on behavioral game theory, specifically in designing the appropriate slashing conditions. The goal is to make the cost of misbehavior significantly higher than the potential gain from exploiting the system. For a shared security model to function, the slashing mechanism must be precise and non-ambiguous.
A staker must be able to verify that their actions will not lead to slashing for reasons outside their control. This creates a delicate balance: the slashing conditions must be strong enough to deter malicious actors but not so broad as to introduce unacceptable levels of operational risk for honest validators.

Theory
The quantitative analysis of shared security models centers on the concept of economic security aggregation. The model functions by stacking risk premiums. A staker earns a base yield from securing the primary chain.
By restaking, they take on additional risk from the AVS in exchange for an additional premium. The total yield for the staker is the sum of these premiums, minus any potential losses from slashing. The core risk for the entire system is the potential for contagion risk , where a security failure in one AVS triggers a massive slashing event that destabilizes the entire restaking pool.
The value of the shared security provided is determined by the total value locked (TVL) in the restaking contract, representing the maximum potential loss for malicious actors.
From a quantitative finance perspective, restaking introduces a new dimension to risk management. Stakers are essentially selling put options on the security of the AVS. The premium they receive (the restaking yield) is the price of this option.
The strike price is effectively the value of their stake, and the risk they bear is the probability of a slashing event. The complexity arises from the correlation between different AVSs. If multiple AVSs are securing similar services or have similar codebases, a single vulnerability could trigger simultaneous slashing events across multiple protocols, leading to a correlated risk that is difficult to hedge.

Risk Profile and Contagion Vectors
The primary risk vector in a shared security model is the potential for systemic failure. When multiple AVSs rely on the same security pool, a vulnerability in one AVS can propagate through the entire system. This creates a scenario where a failure in an options protocol could impact the security of a completely separate data availability layer.
This interconnectedness changes the risk landscape for stakers, requiring them to perform sophisticated due diligence on every AVS they choose to secure. The risk is no longer isolated to a single protocol; it is shared across the entire ecosystem.
- Systemic Contagion: A single security vulnerability in a widely used AVS can lead to a mass slashing event, causing significant losses for stakers across multiple protocols.
- Correlation Risk: The value of the restaked assets and the risk of the AVSs may become correlated, especially during market downturns, exacerbating losses.
- Slashing Condition Ambiguity: Poorly defined slashing conditions can create uncertainty for stakers, leading to lower participation and reduced security for AVSs.

Approach
For crypto options protocols, the shared security model provides a critical infrastructure layer for oracle security. Options pricing and liquidation require highly reliable, real-time data feeds. If an oracle feed is manipulated, a malicious actor could execute a profitable trade by artificially inflating or deflating the underlying asset price, leading to improper liquidations or gains.
The restaking model allows an options protocol to purchase security for its oracle from a large pool of stakers. This makes the cost of a successful attack prohibitively expensive, as it requires overcoming the combined economic security of the restaking pool.
The practical implementation involves designing specific slashing conditions for the AVS. For an options protocol, the slashing condition would likely be triggered if the oracle provides incorrect data that deviates significantly from a verifiable consensus source. The stakers, by opting in to secure this specific AVS, are agreeing to these conditions.
This creates a robust mechanism for ensuring data integrity, which is essential for maintaining the solvency of options pools and protecting against front-running and manipulation. The protocol benefits from increased capital efficiency by avoiding the need to issue its own token to incentivize validators for this specific task.

Options Protocol Application
The shared security model can be applied to various components of an options protocol, creating a layered defense against different attack vectors. The primary use case is securing price feeds for options settlement and liquidation. However, it can also be used to secure specific aspects of the protocol’s governance or even its order matching engine, creating a more robust and decentralized system.
The choice of which AVS to use for security depends on the specific risk profile of the options protocol. A protocol focused on long-tail assets might require a different security setup than one focused on high-volume assets like ETH or BTC.
A shared security model allows options protocols to secure critical components like oracle feeds and liquidation engines by leveraging the economic guarantees of a larger network.
Evolution
The evolution of shared security models began with simple, isolated protocols and has progressed toward complex, interconnected systems. The initial phase involved protocols building their own security, which led to a highly fragmented and inefficient ecosystem. The second phase involved the development of sidechains and layer-2 solutions that relied on a bridge to secure assets, but still required a separate set of validators or a centralized sequencer.
The current iteration, exemplified by restaking, represents a shift toward a more dynamic and permissionless model of security provision. This allows new protocols to innovate without being burdened by the need to bootstrap their own security from day one.
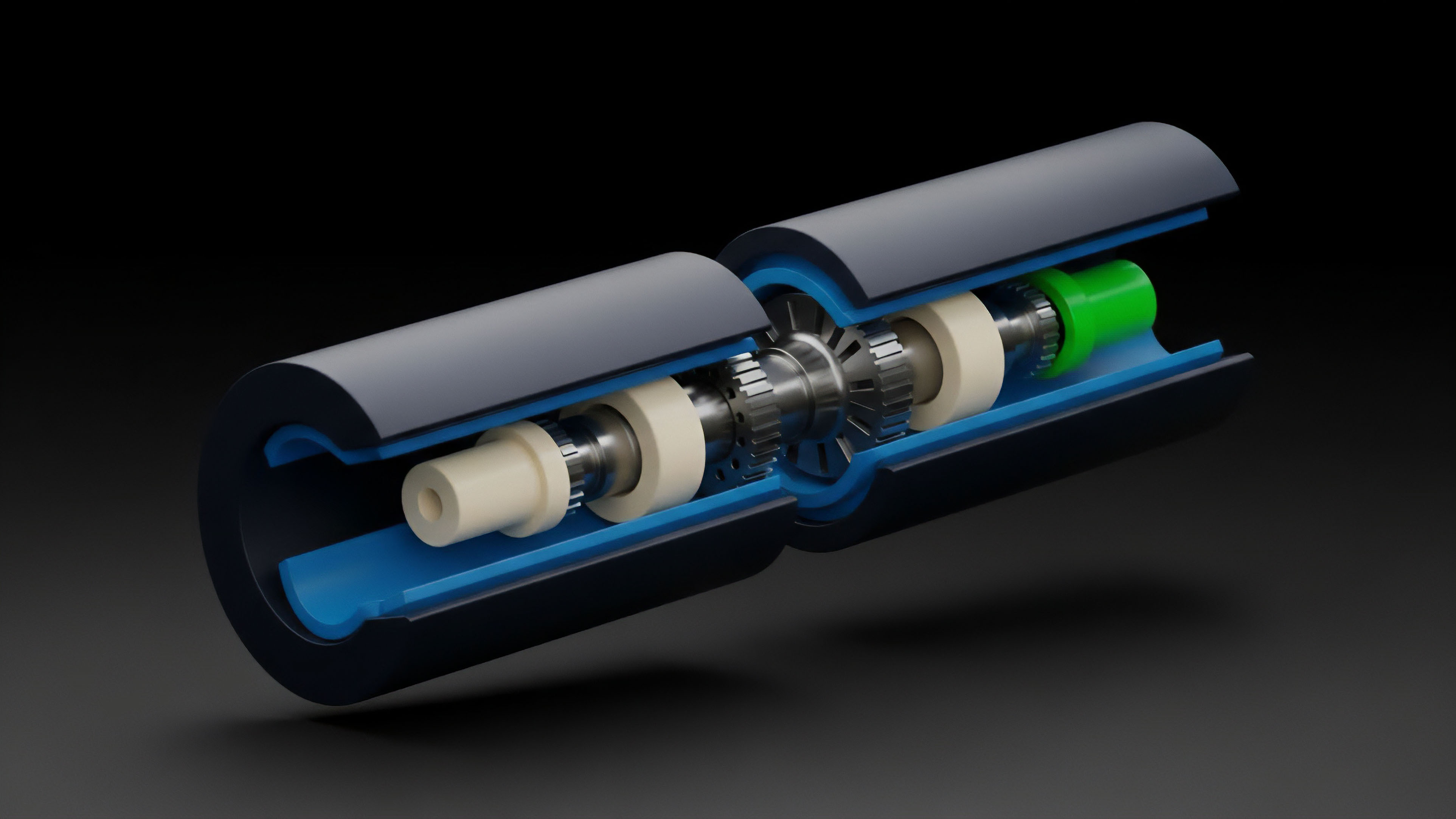
This evolution has led to a separation of concerns in blockchain architecture. The base layer focuses on consensus and data availability, while the restaking layer focuses on providing security services for a wide array of applications. This modularity allows for faster development cycles and greater flexibility in designing new financial instruments.
The challenge, however, lies in managing the complexity of these interconnected systems. The governance model for restaking protocols must evolve to ensure that stakers can make informed decisions about which AVSs to secure and that the slashing conditions are fair and transparent.
Modular Architecture and Capital Efficiency
The current state of shared security models emphasizes modularity. This approach breaks down the traditional monolithic blockchain structure into distinct layers for execution, consensus, and data availability. Restaking enables a new form of capital efficiency by allowing the same capital to secure multiple layers simultaneously.
This creates a more robust and scalable financial infrastructure. The next generation of options protocols will likely be built on top of these modular layers, leveraging restaking to secure their specific components. This approach reduces the cost of security and allows protocols to focus on developing new financial products.
The evolution also highlights the importance of governance risk. As stakers gain the ability to choose which AVSs to secure, they must evaluate the risk-reward profile of each AVS. This introduces a new layer of complexity to the staking process, requiring stakers to become active participants in the ecosystem’s risk management.
The future success of restaking depends on the development of robust governance frameworks that allow stakers to make informed decisions and manage the potential for systemic risk.
Horizon
Looking ahead, the shared security model will continue to reshape the crypto options landscape by enabling new forms of derivatives. The ability to create a secure, decentralized oracle feed through restaking allows for the creation of more complex options products, such as exotic options or options on real-world assets. The increased capital efficiency provided by restaking will also lower the cost of liquidity provision for options protocols, leading to tighter spreads and increased market depth.
However, this evolution introduces significant new risks that must be addressed.
The most pressing challenge on the horizon is the potential for cascading liquidations. If a shared security model becomes widely adopted and a significant portion of the ecosystem relies on restaking, a single security breach in a high-leverage AVS could trigger a large-scale slashing event. This event could cause a panic sell-off of the underlying asset (e.g.
ETH), leading to a cascading effect across multiple protocols. The financial system becomes highly interconnected, and a failure in one area can quickly propagate throughout the entire ecosystem. This creates a new form of systemic risk that requires careful consideration in protocol design and risk management strategies.

Systemic Risk and Regulatory Implications
The future regulatory landscape for shared security models is uncertain. The complex nature of restaking, where a single asset provides security for multiple services, blurs the line between staking and derivatives. Regulators may view restaking as a form of rehypothecation, which could subject protocols to stricter oversight.
The challenge for protocol designers is to create systems that are both robust and compliant, balancing the need for capital efficiency with the potential for regulatory scrutiny. The success of shared security models will ultimately depend on their ability to manage these systemic risks and provide clear, transparent mechanisms for risk assessment.
The future of shared security models hinges on effectively managing systemic contagion risk, ensuring that a single protocol failure does not destabilize the entire ecosystem.
The development of shared security models presents a critical inflection point for decentralized finance. It offers a pathway to a more scalable and capital-efficient ecosystem, but it also introduces complex new forms of interconnected risk. The future success of this model will depend on the ability of protocols to design robust slashing conditions and manage the potential for systemic contagion.
The ultimate goal is to create a financial system that is both highly efficient and resilient to failure.

Glossary
Data Availability and Security in Advanced Decentralized Solutions
Protocol Security Standards Development
Decentralized Finance Security Strategy

Multisig Security

Proof of Work Security
Protocol Security Community
Pooled Security Fungibility

Data Availability and Security in Advanced Solutions

Automated Security