Security Risk Foundations
Security Risk Premium represents the specific yield or price delta demanded by market participants to compensate for the structural fragility of the underlying protocol. This premium accounts for the probability of terminal failure within the code, consensus mechanism, or execution environment. In the digital asset derivatives market, participants price this risk as a spread over the risk-free rate or the standard volatility risk premium.
The valuation reflects the tension between the theoretical perfection of autonomous code and the physical reality of adversarial network conditions.
Security Risk Premium quantifies the market expectation of protocol-level insolvency or technical exploitation within a derivative contract.
Capital allocators treat Security Risk Premium as a distinct asset class of risk. While traditional finance looks at credit risk or sovereign risk, decentralized finance necessitates a focus on the integrity of the state machine. This premium expands during periods of network congestion or when new, unvetted smart contract logic enters the ecosystem.
It serves as a vital signal for the health of the decentralized financial architecture, indicating where trust remains fragmented and where the cost of security remains prohibitive for mass adoption.
Protocol Integrity Valuation
The valuation of protocol integrity requires a shift from balance sheet analysis to formal verification metrics. Traders calculate the Security Risk Premium by observing the divergence between synthetic asset prices and their spot counterparts across different chains. This delta reveals the market’s collective assessment of bridge security, validator honesty, and the liveness of the settlement layer.
When the premium spikes, it often precedes a liquidity flight, as the cost of hedging against protocol failure outweighs the potential yield.
Adversarial Environment Pricing
The adversarial nature of blockchain networks ensures that any vulnerability remains a target for automated exploitation. Security Risk Premium acts as the insurance layer for this constant state of war. Market makers adjust their spreads based on the historical uptime and exploit-free duration of a protocol, a concept known as the Lindy Effect.
A higher premium suggests a lower confidence in the protocol’s ability to withstand sophisticated economic or technical attacks, such as flash loan manipulation or reentrancy exploits.

Historical Risk Genesis
The conceptual birth of Security Risk Premium coincides with the first major systemic failures in the early Ethereum ecosystem. The 2016 DAO exploit served as the primary catalyst, demonstrating that even widely supported protocols possess terminal vulnerabilities.
This event forced a re-evaluation of the “Code is Law” ethos, introducing a permanent risk variable into the pricing of all subsequent on-chain financial instruments. Before this realization, participants often ignored the substrate risk, focusing entirely on price volatility. The subsequent emergence of decentralized exchanges and lending protocols in 2020 further refined this premium.
The “DeFi Summer” period introduced complex interdependencies between protocols, where the failure of one oracle or stablecoin could trigger a cascade of liquidations. This systemic interconnectedness necessitated a more sophisticated approach to pricing security risk, as the premium became a function of the entire tech stack rather than a single isolated contract.

Systemic Failure Milestones
- The DAO Incident: Established the precedent for hard forks as a response to technical failure, creating a premium for chain-split risk.
- Parity Multi-Sig Freeze: Highlighted the risk of permanent capital loss due to logic errors in library contracts.
- Black Thursday Liquidations: Demonstrated the danger of network congestion causing a total collapse of the margin engine.
- Cross-Chain Bridge Exploits: Introduced the concept of “wrapped asset” risk, where the security of the derivative depends on a remote validator set.
Quantitative Risk Framework
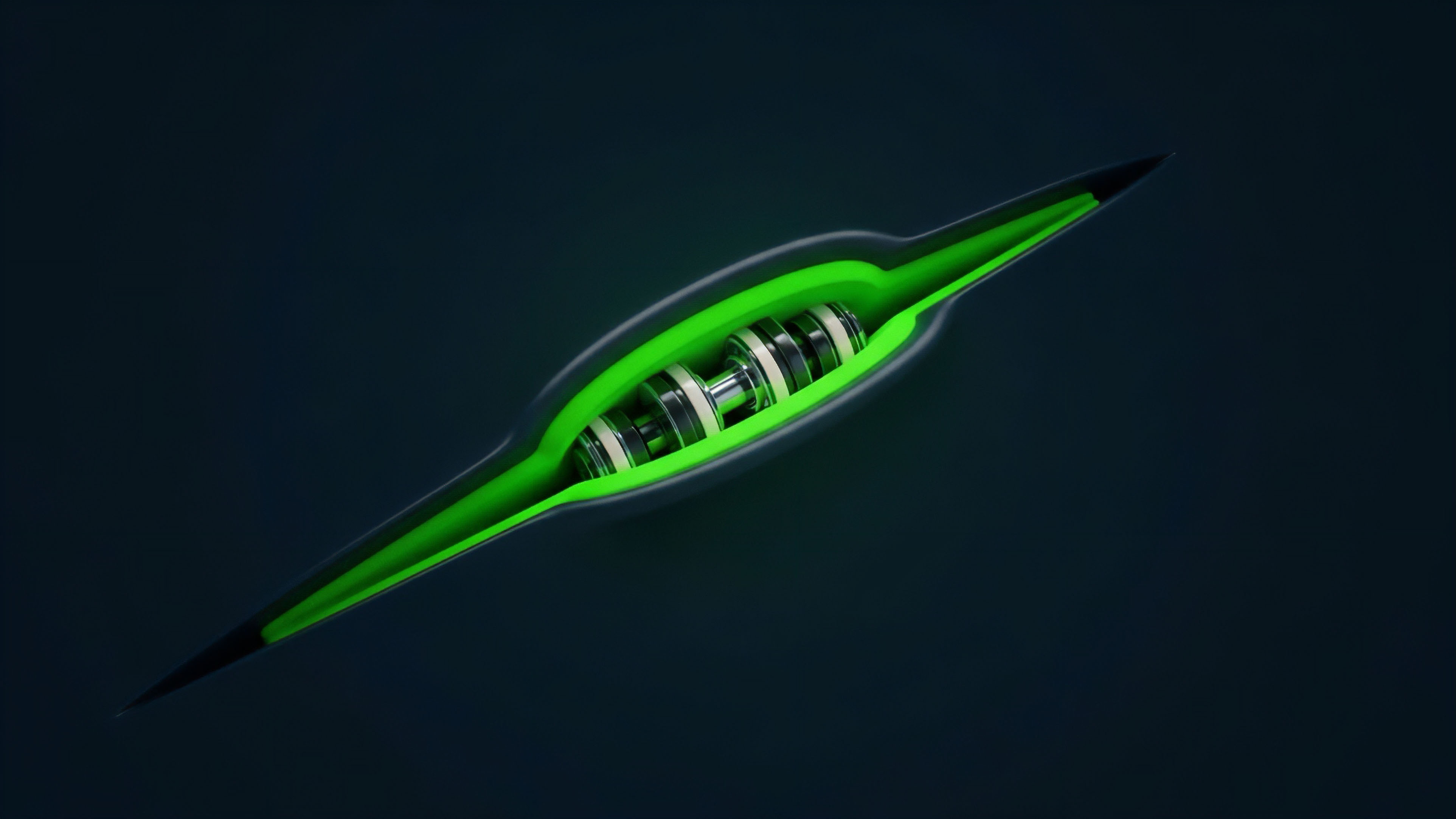
The mathematical modeling of Security Risk Premium utilizes jump-diffusion processes to account for the binary nature of protocol failure. Unlike standard market volatility, which follows a continuous path, security risk is characterized by sudden, catastrophic events that drive the asset value to zero. Analysts incorporate a “jump-to-default” parameter into the stochastic discount factor to reflect this reality.
This parameter functions similarly to a credit default swap spread, representing the annualized cost of protecting against a total loss of principal.
| Risk Component | Traditional Finance Analogy | Crypto-Specific Variable |
|---|---|---|
| Protocol Failure | Corporate Bankruptcy | Smart Contract Exploit |
| Consensus Halt | Exchange Trading Halt | Validator Liveness Failure |
| Governance Attack | Hostile Takeover | 51 Percent Voting Capture |
| Oracle Malfunction | Data Feed Error | Price Manipulation Lag |
Mathematical models for security risk incorporate jump-to-default probabilities to account for the binary nature of smart contract failure.

Sensitivity Analysis and Greeks
The introduction of security risk alters the traditional Black-Scholes Greeks. Delta becomes sensitive not just to price, but to the perceived probability of the protocol remaining functional. A new “Security Gamma” can be theorized, representing the rate of change in the Security Risk Premium relative to the discovery of new vulnerabilities or the successful completion of a code audit.
This framework allows sophisticated traders to hedge against technical debt as if it were a market-moving economic indicator.

Stochastic Default Modeling
The probability of a security event is rarely static. It fluctuates based on the Total Value Locked (TVL) within a protocol, as higher TVL increases the incentive for attackers. This creates a reflexive relationship where the success of a protocol increases its Security Risk Premium.
Quantitative analysts use power-law distributions to model these “fat-tail” events, acknowledging that the most significant risks reside in the extremes of the distribution curve.
Current Market Implementation
Modern derivative strategies integrate Security Risk Premium through the use of protocol-specific insurance vaults and decentralized cover providers. Traders seeking to capture high yields on emerging chains often purchase “cover” to offset the inherent security risk.
The cost of this cover represents the live market pricing of the Security Risk Premium. Professional firms use this data to calculate the “Security-Adjusted Yield,” providing a more accurate picture of the risk-to-reward ratio for any given on-chain position.
Quantitative Assessment Metrics
- Audit Recency Score: The time elapsed since the last comprehensive security review by a reputable firm.
- Bug Bounty Density: The ratio of total bounty payouts to the total value locked, indicating the historical frequency of discovered flaws.
- Validator Gini Coefficient: A measure of decentralization within the consensus layer, where higher concentration increases the security premium.
- Code Complexity Index: A metric based on the number of external dependencies and lines of code, correlating with the attack surface area.
Derivative Hedging Strategies
Traders utilize out-of-the-money put options on protocol governance tokens as a proxy for hedging security risk. If a protocol suffers a major exploit, the governance token typically collapses, providing a payout that offsets the loss of the deposited principal. Simultaneously, some specialized platforms offer “binary options” on specific security events, such as a bridge failure or a stablecoin de-pegging, allowing for direct speculation on the Security Risk Premium itself.

Risk Pricing Transitions
The pricing of Security Risk Premium has transitioned from a blunt, binary assessment to a granular, multi-tiered analysis. Early market participants viewed all smart contracts as equally risky, leading to a uniform premium across the ecosystem. Today, the market distinguishes between different execution environments, such as Layer 1 mainnets, optimistic rollups, and zero-knowledge circuits.
Each environment carries a unique risk profile based on its finality guarantees and the maturity of its proof system.
| Epoch | Dominant Risk View | Primary Pricing Mechanism |
|---|---|---|
| Genesis (2015-2017) | Experimental Curiosity | Zero or Infinite Premium |
| DeFi Expansion (2018-2021) | Interdependency Risk | Yield-Spread Arbitrage |
| Modular Era (2022-Present) | Execution Layer Risk | Tranche-Based Insurance |
Modern risk management shifts from broad protocol insurance toward granular, tranche-based security pricing for specific execution environments.

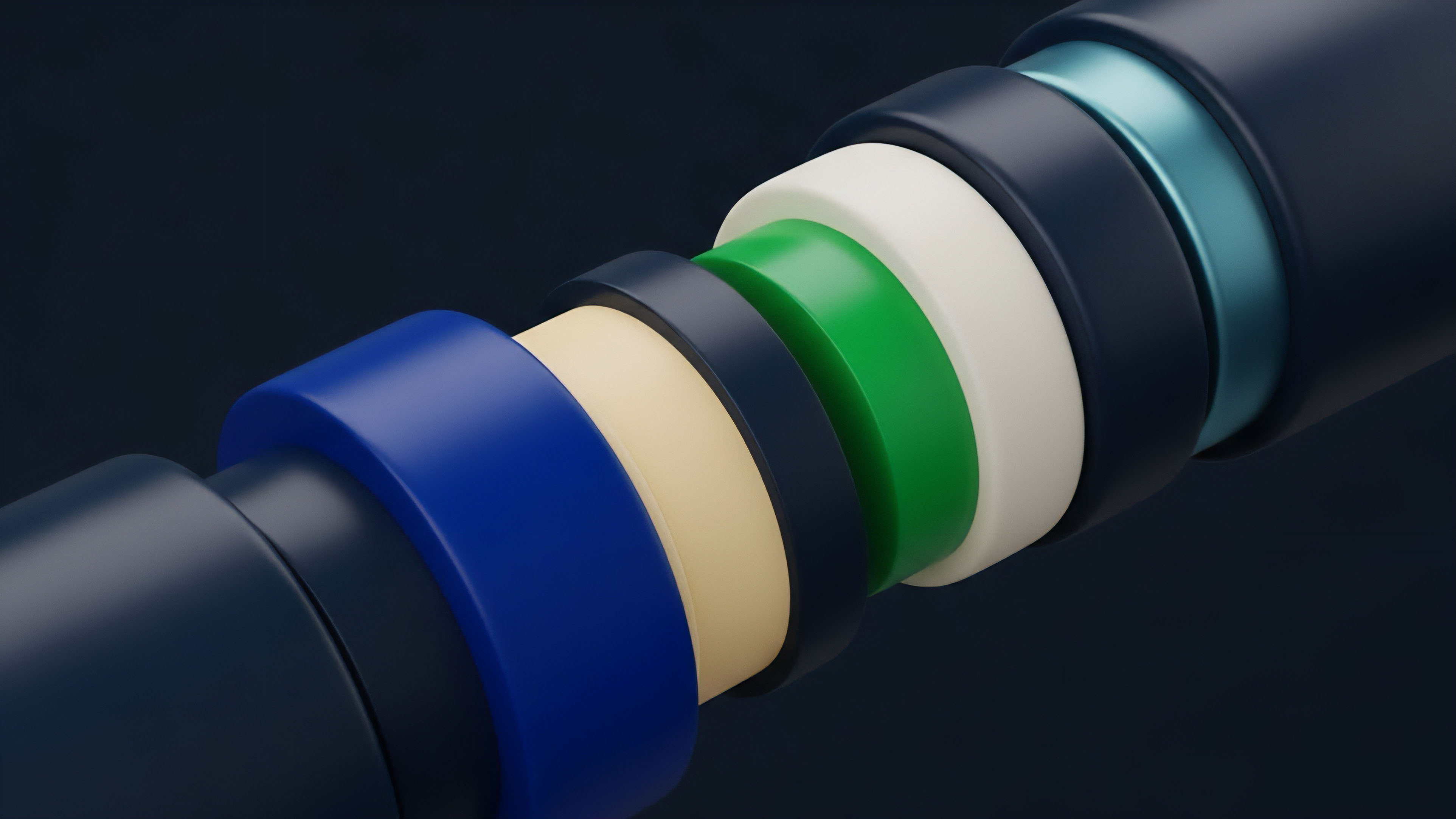
Modular Security Decomposition
The shift toward modular blockchain architectures has fragmented the Security Risk Premium. A single transaction now involves multiple layers: data availability, execution, and settlement. Consequently, the premium is no longer a monolithic value but a composite of the risks associated with each module.
This allows for more efficient capital allocation, as users can choose to pay a higher premium for the security of a decentralized data availability layer while using a more centralized, high-performance execution layer.
Institutional Risk Standards
The entry of institutional capital has forced the standardization of security risk metrics. Traditional risk management frameworks, such as Value at Risk (VaR), are being adapted to include smart contract risk. This institutionalization leads to a more stable Security Risk Premium, as large-scale liquidity providers demand rigorous documentation and formal verification before committing capital.
The result is a bifurcated market: “Blue Chip” protocols with low, stable premiums and “Experimental” protocols with high, volatile premiums.

Future Risk Trajectory
The future of Security Risk Premium lies in the automation of risk assessment through artificial intelligence and real-time formal verification. We are moving toward a state where the premium is adjusted block-by-block based on the current state of the mempool and the detection of suspicious transaction patterns.
This “Dynamic Security Pricing” will allow protocols to automatically increase fees or pause certain functions when the perceived risk of an exploit crosses a specific threshold.

Emerging Risk Vectors
- AI-Generated Exploits: The use of large language models to identify subtle logic flaws that human auditors might overlook.
- Quantum Computing Threats: The eventual necessity of a premium for protocols that have not yet transitioned to post-quantum cryptographic standards.
- MEV-Driven Consensus Instability: The risk that Maximal Extractable Value becomes so high that it incentivizes validators to reorganize the chain.
- Regulatory State Capture: The premium associated with the risk of a protocol being forced to implement censorship at the consensus level.
The integration of real-world assets (RWA) onto the blockchain will introduce a new dimension to the Security Risk Premium. The premium will need to account for the “Oracle Gap” ⎊ the risk that the digital representation of an asset diverges from its physical reality due to legal or physical interference. This will require a hybrid risk model that combines on-chain technical analysis with off-chain legal and jurisdictional assessment. As these systems mature, the Security Risk Premium will become the primary benchmark for the reliability of the global financial operating system.
Glossary
Jump-to-Default Modeling
Data Availability Risk

Risk Premium
Dynamic Premium Adjustment
Hybrid Risk Modeling
Mev Impact on Security
Formal Verification

Cross-Chain Bridge Risk

Protocol Failure