Essence
Security Policy Development within decentralized derivatives functions as the primary architectural defense mechanism against systemic insolvency and protocol-level exploitation. It constitutes the codified set of risk parameters, liquidation logic, and collateral requirements that govern the lifecycle of an options contract. By establishing deterministic boundaries for participant behavior, this framework preserves the integrity of the margin engine when faced with extreme volatility or adversarial market conditions.
Security Policy Development provides the deterministic risk boundaries required to maintain solvency within decentralized margin engines.
This domain transcends simple administrative oversight, representing the intersection of cryptographic enforcement and quantitative finance. Protocols utilize these policies to manage the inherent trade-offs between capital efficiency and system robustness. Without these structured constraints, the interconnected nature of decentralized markets would leave liquidity pools vulnerable to rapid contagion during periods of market stress.

Origin
The genesis of Security Policy Development lies in the transition from traditional centralized clearinghouses to autonomous smart contract execution.
Early decentralized finance experiments demonstrated that without rigid, programmable constraints, market participants would inevitably engage in over-leverage, leading to cascading liquidations. The industry adopted frameworks from classical finance, such as Value at Risk modeling and initial margin requirements, but adapted them for the unique constraints of blockchain settlement.
| Concept | Legacy Implementation | Decentralized Adaptation |
| Collateralization | Discretionary margin calls | Automated liquidation triggers |
| Risk Mitigation | Human-led circuit breakers | Smart contract invariant checks |
| Policy Updates | Governance committee votes | On-chain parameter adjustments |
Early protocols lacked the sophistication to handle non-linear payoffs associated with options, necessitating the development of more granular security layers. Developers realized that fixed parameters failed to account for the rapid shifts in realized volatility observed on-chain. This prompted the evolution toward dynamic, data-driven security frameworks capable of adjusting collateral requirements in real time based on oracle inputs and network congestion.
Theory
The theoretical foundation of Security Policy Development rests upon the application of game theory to adversarial environments.
Each parameter within the security framework ⎊ from the liquidation penalty to the maintenance margin ⎊ acts as a strategic incentive to discourage malicious activity or excessive risk-taking. Quantitative modeling of Greeks, specifically Delta and Gamma exposure, informs the threshold levels that trigger system-wide risk mitigation protocols.
Quantitative Greeks and game-theoretic incentives form the structural bedrock for managing systemic risk in decentralized option protocols.
Smart contract security necessitates that policies remain immutable to logic errors while being flexible enough to respond to market shifts. Engineers often utilize invariant testing to ensure that the total value locked remains protected against edge cases. This requires a rigorous mathematical approach to define the boundaries of the state space, ensuring that no combination of user actions can move the protocol into an unrecoverable deficit.
- Liquidation Thresholds define the precise point at which a position is seized to prevent negative equity.
- Volatility Buffers adjust collateral requirements based on current implied volatility surfaces to maintain systemic coverage.
- Oracle Integrity Checks validate incoming price data to prevent manipulation-based exploits of the margin system.

Approach
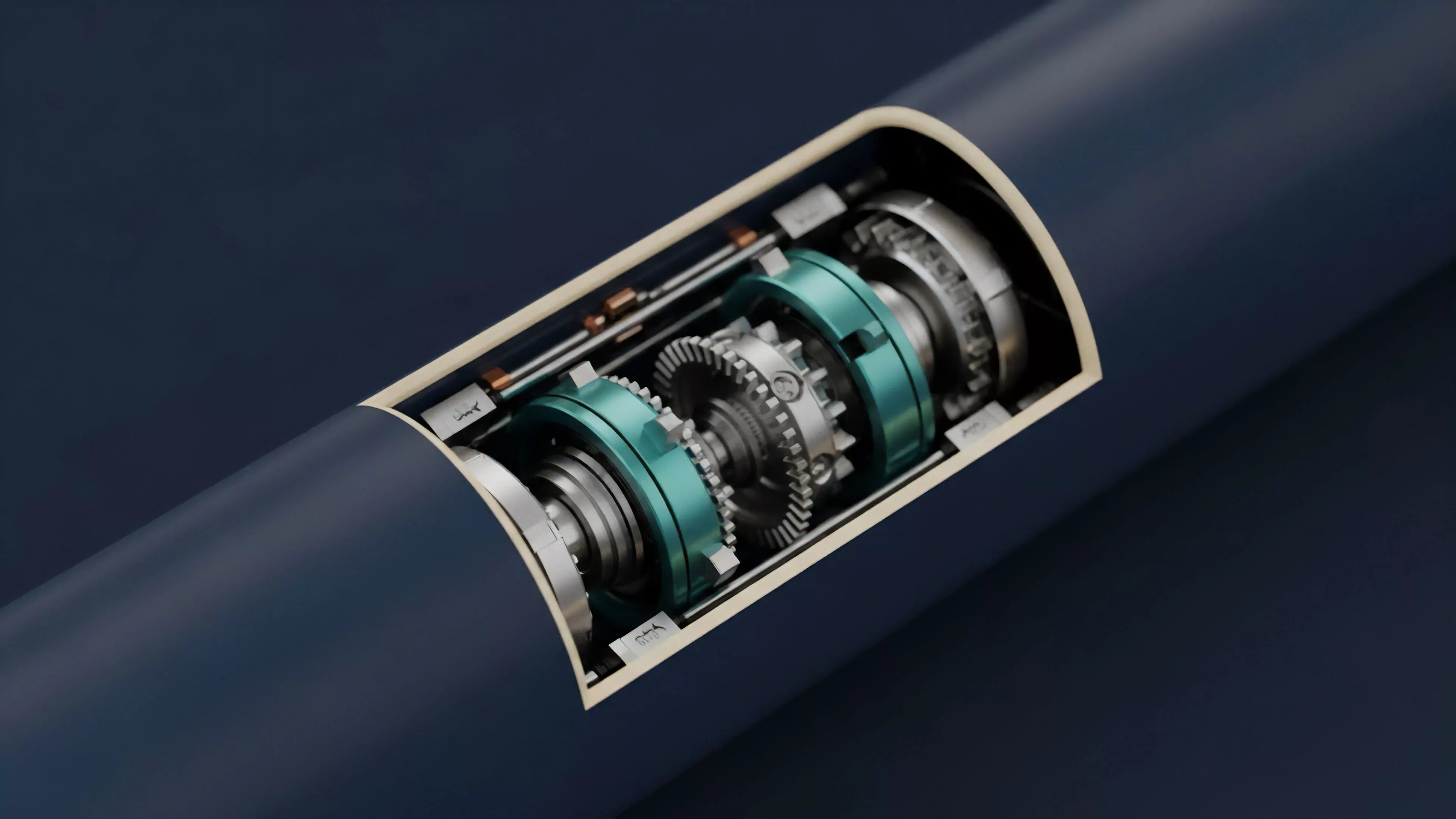
Current implementations of Security Policy Development prioritize transparency and algorithmic adaptability. Architects now deploy multi-layered defense systems that separate core logic from risk parameters, allowing for rapid updates via governance without compromising the underlying smart contract integrity. This approach recognizes that security is a process rather than a static state, requiring continuous monitoring of market microstructure and order flow.
| Layer | Focus | Mechanism |
| Protocol Level | Invariant enforcement | Hard-coded constraints |
| Parameter Level | Dynamic risk adjustment | Governance-voted thresholds |
| Monitoring Level | Adversarial detection | On-chain activity analysis |
The industry has moved toward modular risk frameworks where individual pools can operate under distinct policies tailored to the volatility profile of the underlying assets. This granularity prevents a single high-volatility event from threatening the entire protocol. By isolating risks, the system becomes more resilient to contagion, as the failure of one pool does not automatically translate into the collapse of the broader liquidity network.

Evolution
The trajectory of Security Policy Development has shifted from rudimentary collateral requirements to complex, cross-protocol risk modeling.
Early systems relied on static ratios that proved inadequate during periods of low liquidity. As protocols matured, they incorporated external data feeds and automated market maker interactions to refine their risk models. The integration of cross-chain assets and synthetic derivatives has necessitated a more holistic view of systemic exposure.
Systemic resilience now depends on the ability to synchronize risk parameters across fragmented liquidity pools and disparate chains.
Technical debt remains a primary hurdle, as older, less flexible architectures struggle to adapt to the speed of modern decentralized markets. Many protocols are undergoing architectural shifts to prioritize modularity, allowing for the integration of specialized risk-management plugins. The transition from human-governed updates to automated, machine-learning-driven parameter tuning marks the current frontier of this field.
This evolution reflects a deeper understanding of the adversarial nature of programmable finance.

Horizon
The future of Security Policy Development points toward autonomous, self-optimizing risk engines that require minimal human intervention. We anticipate the widespread adoption of real-time stress testing simulations that run concurrently with protocol operation. These systems will likely utilize zero-knowledge proofs to verify risk parameters without exposing sensitive user data, balancing privacy with the necessity of systemic transparency.
- Automated Risk Oracles will provide sub-second adjustments to collateral requirements based on global liquidity conditions.
- Cross-Protocol Liquidation mechanisms will enable shared risk pools to mitigate contagion across the broader financial stack.
- Predictive Invariant Analysis will proactively identify potential failure modes before they are exploited by adversarial actors.
The ultimate goal involves creating a self-healing financial infrastructure where security policies are inherently linked to the economic health of the underlying assets. This will redefine how we manage leverage and risk, moving away from reactive measures toward a proactive, system-wide equilibrium. The convergence of cryptographic security and quantitative finance will establish a new standard for stability in decentralized markets.