Essence
The operational reality of any decentralized derivative system depends on the mathematical boundaries established by Security Parameter Thresholds. These numeric constraints function as the physical laws of a trustless environment, defining the edge where economic activity remains secure and where it descends into systemic failure. Within a permissionless architecture, these values act as the primary defense against adversarial actors who seek to exploit latency or collateral imbalances.
Security Parameter Thresholds represent the mathematical boundaries where a protocol maintains solvency against market volatility and adversarial behavior.
These limits represent the actual solvency limits of the protocol. They dictate the maximum permissible leverage and the minimum collateralization ratios required to maintain a healthy order book. By codifying these rules into smart contracts, the system eliminates the need for human oversight, replacing it with deterministic execution.
The stability of the entire market relies on the precision of these settings, as even a minor miscalculation can lead to cascading liquidations or protocol insolvency. The nature of these parameters is inherently adversarial. In a global, 24/7 market, every threshold is under constant stress from automated agents and high-frequency traders.
The system must remain robust under extreme tail-risk events, ensuring that the Maintenance Margin is sufficient to cover the costs of closing a position even during periods of zero liquidity. This requires a rigorous application of quantitative modeling to determine the exact point where a position becomes a liability to the collective pool.

Origin
Historical risk management relied on human discretion and institutional trust. The shift toward decentralized finance replaced these subjective audits with objective, cryptographic proofs.
This transition required a new method for defining safety ⎊ one that does not depend on the reputation of a counterparty but on the immutable logic of the code itself. The early designs of blockchain protocols introduced basic security constants to prevent spam and double-spending. As these systems evolved to support complex financial instruments like options and perpetual swaps, the parameters became more sophisticated.
The need for Security Parameter Thresholds arose from the realization that trustless settlement requires a pre-defined, mathematical consensus on what constitutes a “safe” state.
The transition from human-governed risk to code-governed risk necessitates the use of deterministic Security Parameter Thresholds to ensure protocol survival.
Unlike traditional finance, where a clearinghouse might waive a margin call for a favored client, a decentralized protocol executes according to its Liquidation Threshold without exception. This impartiality is the foundation of the new financial operating system. It ensures that all participants are subject to the same physical limits, creating a level playing field where the only advantage is a better understanding of the underlying mathematics.
Theory
Quantitative modeling of Security Parameter Thresholds involves the calculation of risk sensitivity across multiple variables.
In options markets, this primarily concerns the relationship between Maintenance Margin and the underlying asset volatility. The system must ensure that the Liquidation Threshold is reached before the collateral value drops below the debt obligation.

Quantitative Risk Variables
The following table illustrates the primary variables used to construct a robust security model within a derivative protocol.
| Variable | Definition | Impact on Solvency |
|---|---|---|
| Initial Margin | Upfront collateral required to open a position. | Determines the maximum leverage available to the trader. |
| Maintenance Margin | Minimum collateral required to keep a position open. | Prevents the protocol from absorbing losses during price drops. |
| Liquidation Penalty | Fee charged to the trader during a forced closure. | Incentivizes traders to manage their own risk proactively. |
| Oracle Delay Buffer | Safety margin for price feed latency. | Protects the protocol from arbitrage during rapid price shifts. |
The mathematical proof for these thresholds often relies on Value at Risk (VaR) or Expected Shortfall (ES) models. These models estimate the potential loss over a specific time period with a given confidence level. In a decentralized context, these calculations must also account for Smart Contract Risk and the possibility of oracle manipulation.
The goal is to set the Security Parameter Thresholds at a level that maximizes capital efficiency while minimizing the probability of a systemic default.

Adversarial Game Theory
The design of these thresholds must also consider Behavioral Game Theory. Adversaries will always look for the “weakest link” in the parameter set. If the Liquidation Threshold is too conservative, the protocol loses users to more efficient competitors.
If it is too aggressive, a single volatility spike can wipe out the Insurance Fund. This creates a constant tension between growth and safety.

Approach
Current methodologies in decentralized options protocols utilize various structures to manage risk. Centralized venues employ a real-time risk engine that adjusts requirements based on portfolio Delta and Gamma.
Decentralized alternatives often rely on Automated Market Makers (AMMs) with pre-defined liquidity pools and collateralization rules.

Threshold Implementation Methods
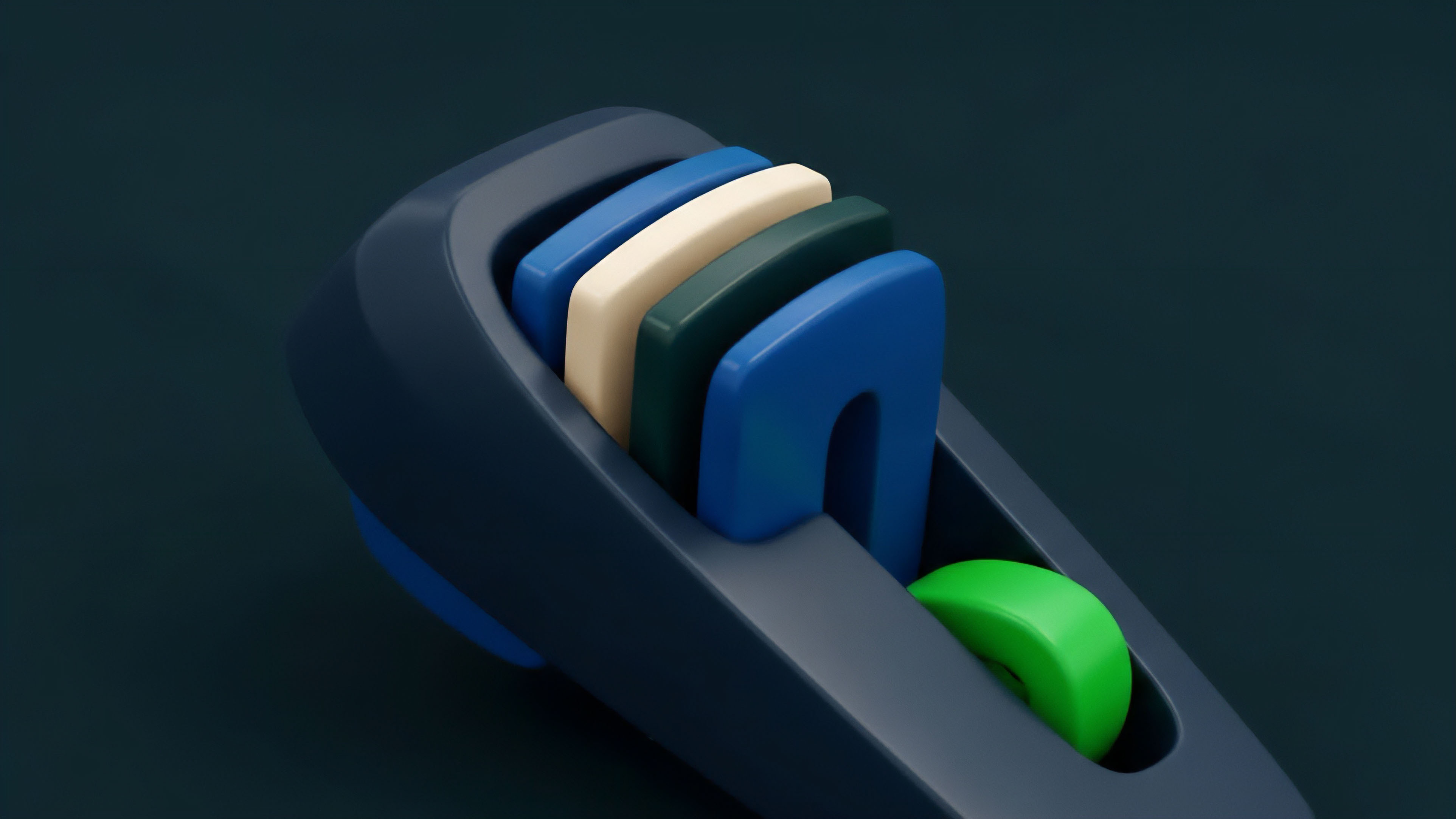
- Fixed Ratio Models: These protocols enforce a static percentage for collateralization, providing a simple but often capital-inefficient safety net.
- Dynamic Risk Engines: These systems adjust Security Parameter Thresholds based on real-time volatility and liquidity depth, allowing for higher leverage during stable periods.
- Portfolio Margin Systems: These models calculate risk across an entire account, recognizing the offsetting nature of hedged positions to reduce total collateral requirements.
- Tiered Liquidation Protocols: These systems close positions in stages to minimize market impact and preserve as much of the trader’s equity as possible.
Modern protocols utilize adaptive Security Parameter Thresholds to balance the competing needs of capital efficiency and systemic resilience.
The effectiveness of these methods depends on the quality of the underlying data. Oracle Latency remains a significant obstacle, as a delay of even a few seconds can allow a trader to profit at the expense of the protocol’s liquidity providers. To mitigate this, many protocols incorporate a Safety Buffer into their Security Parameter Thresholds, effectively requiring more collateral than the raw price data would suggest.

Comparative Protocol Architecture
| Model Type | Primary Advantage | Primary Risk |
|---|---|---|
| Over-Collateralized | High solvency assurance. | Extremely low capital efficiency. |
| Algorithmic Margin | High efficiency and leverage. | Vulnerability to flash crashes. |
| Insurance Fund Backed | Socialized risk protection. | Potential for fund depletion. |

Evolution
The progression of risk parameters moved from static, conservative ratios to more efficient, algorithmic models. Early protocols suffered from capital inefficiency because they required excessive over-collateralization. As the market matured, developers introduced Cross-Margin and Portfolio Margin systems that recognize the offsetting nature of different positions.
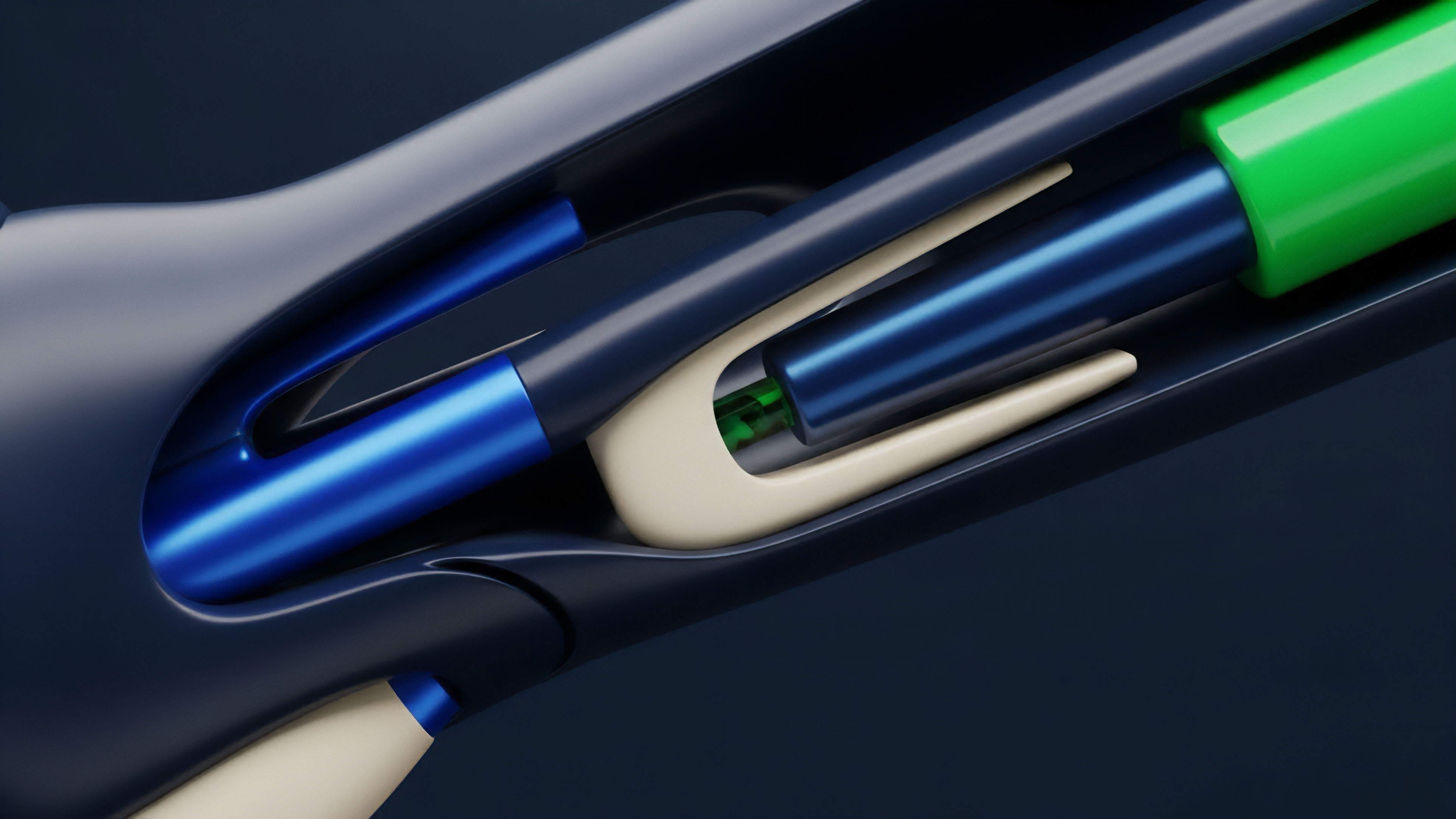
This transition mirrors the evolution of biological homeostasis, where a system maintains stability through constant, minute adjustments rather than rigid, unchanging states. By moving toward Adaptive Security Parameter Thresholds, decentralized finance is becoming more resilient and more capable of handling the complexities of global capital flows.

Drivers of Parameter Evolution
- Increased Liquidity Depth: As markets become deeper, the risk of a single trade causing a liquidation cascade decreases, allowing for tighter thresholds.
- Improved Oracle Technology: Faster and more reliable price feeds reduce the need for large safety buffers, increasing capital efficiency.
- Advanced Risk Modeling: The adoption of sophisticated financial engineering tools allows protocols to set parameters with greater precision.
- Regulatory Pressure: The need to comply with evolving legal standards is forcing protocols to adopt more robust and transparent risk management systems.
The shift from manual governance to Algorithmic Governance represents a major leap forward. In the past, changes to Security Parameter Thresholds required a slow and often contentious voting process. Today, many protocols use PID Controllers or other automated feedback loops to adjust parameters in real-time based on market conditions. This reduces the risk of human error and ensures that the protocol can respond instantly to emerging threats.

Horizon
Future developments will involve the integration of machine learning to predict tail risk events before they occur. These self-optimizing Security Parameter Thresholds will adjust in milliseconds, responding to order flow imbalances and cross-chain liquidity shifts. This will create a truly autonomous financial system that is capable of repairing itself during times of stress. The rise of Cross-Chain Interoperability will also require a new type of security model. When collateral is held on one chain and the derivative is traded on another, the Security Parameter Thresholds must account for the bridge risk and the finality time of both networks. This adds a new layer of complexity to the mathematical proofs required for solvency. Ultimately, the goal is to reach a state of Invisible Security. In this future, the Security Parameter Thresholds are so well-tuned and so responsive that the user never has to worry about protocol failure. The system becomes as reliable as the laws of physics, providing a stable foundation for the next generation of global finance. This is not a distant dream but the logical conclusion of the path we are currently on. As we continue to refine our models and our code, we are building a financial system that is not only more efficient but also more just and more resilient than anything that came before it.

Glossary

Backtesting

Color

Theta

Atomic Swaps

Stablecoin Depegging

Flash Loan

Dispersion Trading

Gamma
Basis Trading