
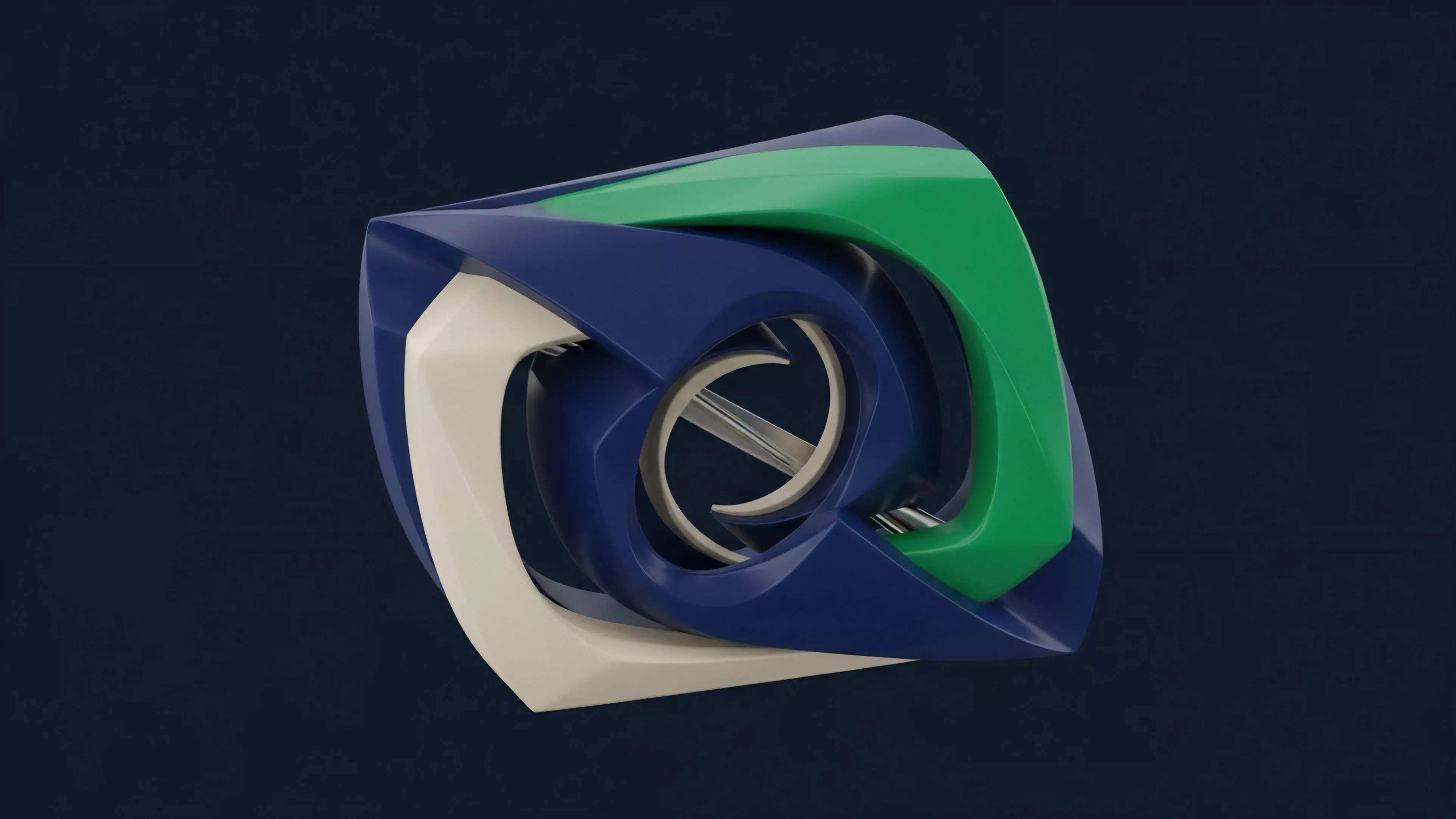
Essence
Secure Code Execution functions as the foundational architecture for verifying the integrity of logic within decentralized financial protocols. It ensures that programmatic instructions governing asset movement and risk management remain immutable and resistant to external manipulation. By establishing a verifiable environment for contract operations, it provides the technical certainty required for complex derivative structures to operate without reliance on centralized intermediaries.
Secure Code Execution provides the cryptographic guarantee that financial logic remains uncompromised during the lifecycle of a derivative instrument.
This mechanism addresses the primary vulnerability of programmable money, specifically the risk of unauthorized state changes or malicious logic injection. When protocols rely on opaque or insecure environments, the potential for systemic failure increases, as market participants cannot independently audit the execution flow. Secure Code Execution replaces trust in human developers with the objective verification of computational proofs.

Origin
The requirement for Secure Code Execution emerged from the limitations inherent in early blockchain architectures, which prioritized transparency over privacy-preserving computation.
Initial smart contract platforms lacked isolated environments, exposing sensitive financial parameters to the public ledger. This lack of isolation hindered the development of advanced derivative products, as the underlying pricing models and margin calculations required confidentiality and tamper-proof processing.
- Trusted Execution Environments provide hardware-level isolation for sensitive computations.
- Zero Knowledge Proofs allow for the validation of code execution without revealing underlying data inputs.
- Formal Verification offers mathematical certainty regarding the correctness of contract logic.
These developments shifted the focus from merely recording transactions to ensuring the validity of the underlying computational processes. By adopting these methods, decentralized protocols began to mimic the security standards of traditional financial institutions while maintaining the open nature of distributed ledgers. The transition from simple token transfers to complex derivative instruments necessitated this evolution toward robust execution standards.

Theory
The theoretical framework for Secure Code Execution relies on the intersection of cryptography, game theory, and hardware-based security.
It operates on the premise that financial logic must be both transparent in its rules and opaque in its specific data inputs to maintain competitive advantage and security. This duality is managed through advanced cryptographic primitives that enable verification without exposure.
| Methodology | Security Focus | Computational Cost |
| Formal Verification | Logical Correctness | High |
| Hardware Enclaves | Runtime Integrity | Low |
| Zero Knowledge | Data Privacy | Variable |
The integrity of decentralized derivatives depends on the ability to mathematically prove that execution logic adheres to predefined parameters.
Within this environment, the protocol acts as an adversarial machine, constantly validating inputs against established consensus rules. If a code path deviates from the expected outcome, the system triggers automated circuit breakers to prevent capital leakage. This approach minimizes the attack surface by reducing the reliance on human oversight and emphasizing the mathematical inevitability of the code itself.
Approach
Current implementations of Secure Code Execution utilize modular architectures that separate consensus from computation.
By offloading complex margin engine calculations to specialized execution layers, protocols maintain high performance while ensuring that every state transition remains anchored to the primary blockchain. This layered approach enables the scaling of sophisticated options markets without compromising the security of the underlying collateral.
- Modular Execution Layers process complex derivatives while inheriting security from the base layer.
- Automated Auditing Tools monitor real-time execution for anomalies and potential exploit vectors.
- Multi-Party Computation facilitates the secure handling of private keys and sensitive pricing data.
Market participants now demand higher standards of technical assurance, leading to the adoption of continuous verification pipelines. These pipelines integrate security testing directly into the deployment process, ensuring that any update to the derivative protocol undergoes rigorous stress testing. The result is a more resilient financial infrastructure capable of supporting institutional-grade trading volumes and risk management strategies.

Evolution
The trajectory of Secure Code Execution moves toward fully autonomous, self-verifying systems.
Early iterations relied on manual audits and centralized multisig arrangements, which introduced significant human-centric risks. As the market matured, the focus shifted to decentralized, code-based governance and cryptographic enforcement, significantly reducing the dependence on external entities for system integrity.
Evolution in execution standards transforms decentralized protocols from experimental prototypes into durable financial instruments.
The integration of Secure Code Execution with broader liquidity pools has enabled the creation of cross-chain derivatives that operate with unprecedented efficiency. By leveraging shared security models, these protocols achieve a level of systemic stability that was previously unattainable. This progression reflects a broader shift toward treating code as a verifiable financial asset, where the quality of the execution environment directly dictates the market value and liquidity of the derivative.

Horizon
Future developments in Secure Code Execution will likely center on the seamless integration of privacy-preserving computation with high-frequency trading capabilities.
As hardware accelerators become more accessible, the overhead associated with cryptographic proofs will decrease, enabling complex, low-latency derivative markets on decentralized platforms. This evolution will further erode the boundaries between traditional financial systems and the decentralized landscape.
| Future Development | Systemic Impact |
| Hardware Acceleration | Increased Trading Latency |
| Autonomous Governance | Reduced Regulatory Friction |
| Cross-Protocol Interoperability | Liquidity Aggregation |
The ultimate goal remains the creation of a global, permissionless financial network where Secure Code Execution is the default standard for all transactions. This will require not only technical innovation but also a deeper understanding of the adversarial dynamics that govern these systems. By refining the mathematical and structural foundations of execution, the industry will achieve the stability required for widespread adoption across global financial markets. The persistent tension between computational performance and absolute security remains the central paradox; how can we maximize throughput without compromising the mathematical integrity of the execution environment?
