Essence
Real-Time Threat Monitoring functions as the primary defensive architecture for decentralized derivative protocols, operating as a continuous surveillance layer that identifies systemic instabilities before they manifest as terminal failures. In the adversarial environment of permissionless finance, where code execution is final and irreversible, this monitoring infrastructure serves as the functional equivalent of a biological immune system. It maintains the integrity of the margin engine and the solvency of the liquidity pool by scrutinizing every state change on the blockchain.
Real-Time Threat Monitoring constitutes the automated verification of protocol health through continuous data validation and anomaly detection.
This infrastructure prioritizes the detection of asymmetric information risks and latency arbitrage attempts that target option pricing models. By maintaining a high-fidelity stream of on-chain and off-chain data, the system ensures that the mark price remains aligned with the broader market, preventing malicious actors from exploiting stale or manipulated oracles. The objective remains the preservation of delta-neutrality across the protocol, shielding liquidity providers from catastrophic gamma exposure during periods of extreme volatility.

Systemic Integrity and Solvency
The operational focus centers on the prevention of liquidation cascades. When market prices move violently, Real-Time Threat Monitoring tracks the health of every outstanding position, calculating the maintenance margin requirements in sub-second intervals. This proactive stance allows the protocol to trigger liquidations or deleveraging events before a position becomes undercollateralized, thereby protecting the insurance fund and preventing socialized losses.

Adversarial Game Theory
In a landscape defined by Maximal Extractable Value (MEV) and sophisticated sandwich attacks, monitoring must extend beyond simple price feeds. It involves the analysis of the mempool to anticipate large directional trades or governance attacks. By identifying these patterns, Real-Time Threat Monitoring enables the protocol to adjust spreads or temporarily increase slippage parameters, neutralizing the profit motives of predatory agents.
Origin
The transition from reactive to proactive risk management followed the catastrophic deleveraging events seen in early decentralized finance iterations.
Initial derivative platforms relied on periodic, off-chain calculations that proved insufficient during the Black Thursday liquidity crunch of 2020. This failure demonstrated that static risk parameters could not withstand the velocity of crypto-native volatility. Real-Time Threat Monitoring emerged as a technological response to the inability of traditional value-at-risk (VaR) models to account for the unique tail risks of digital assets.
The shift toward continuous surveillance was driven by the catastrophic failure of periodic risk assessment during high-volatility events.
Early implementations were rudimentary, often consisting of simple bot scripts that monitored oracle updates. As the complexity of structured products and exotic options increased, the demand for more sophisticated surveillance grew. The development of subgraph indexing and real-time event emitters provided the necessary data granularity to build robust monitoring frameworks.
This allowed developers to move away from centralized monitoring solutions toward decentralized, trustless verification systems.

Historical Liquidity Failures
The 2022 collapse of major algorithmic stablecoins and lending platforms served as a definitive catalyst for the current generation of Real-Time Threat Monitoring. These events highlighted the contagion risk inherent in interconnected protocols. Monitoring systems were redesigned to track cross-chain asset flows and collateral correlations, recognizing that a threat to one protocol often signals a broader systemic shock.
Technological Convergence
The integration of low-latency data streams and high-performance computing enabled the transition to the current state. Real-Time Threat Monitoring now leverages WebSockets and gRPC connections to ingest data directly from validators and sequencers. This technological leap ensures that the time between a threat emerging and the protocol responding is minimized, effectively closing the window for arbitrage and exploits.

Theory
The mathematical foundation of Real-Time Threat Monitoring rests on stochastic calculus and non-parametric statistics.
Rather than assuming a normal distribution of market returns, these systems employ heavy-tailed distributions to model the probability of extreme events. The monitoring engine continuously performs Kolmogorov-Smirnov tests to detect shifts in the underlying volatility surface, alerting the protocol when market conditions deviate from the assumptions of the Black-Scholes or Heston models.
Mathematical surveillance focuses on identifying deviations from expected probabilistic distributions to signal emerging systemic risks.
| Threat Vector | Mathematical Metric | Systemic Consequence |
|---|---|---|
| Oracle Manipulation | Deviation from TWAP/VWAP | Incorrect Option Pricing |
| Liquidity Exhaustion | Slippage Gradient Analysis | Inability to Liquidate |
| Smart Contract Exploit | Anomalous State Changes | Total Fund Depletion |
| Governance Attack | Voting Power Concentration | Protocol Hijacking |

Quantitative Risk Metrics
The system calculates Greeks in real-time to assess the aggregate risk of the liquidity pool. A sudden spike in Gamma or Vega across multiple positions triggers defensive measures. This involves monitoring the concentration risk of specific strike prices or expiration dates.
If the protocol’s net delta exceeds a predefined threshold, Real-Time Threat Monitoring signals the hedging engine to execute offsetting trades in the underlying spot or futures markets.

Adversarial Modeling
Theory dictates that the system must assume all participants are rational, profit-maximizing agents with access to flash loans. Monitoring logic incorporates game-theoretic simulations to predict how users might respond to liquidation thresholds or incentive changes. By modeling these interactions, Real-Time Threat Monitoring identifies recursive borrowing loops or leverage traps that could lead to protocol insolvency.
Approach
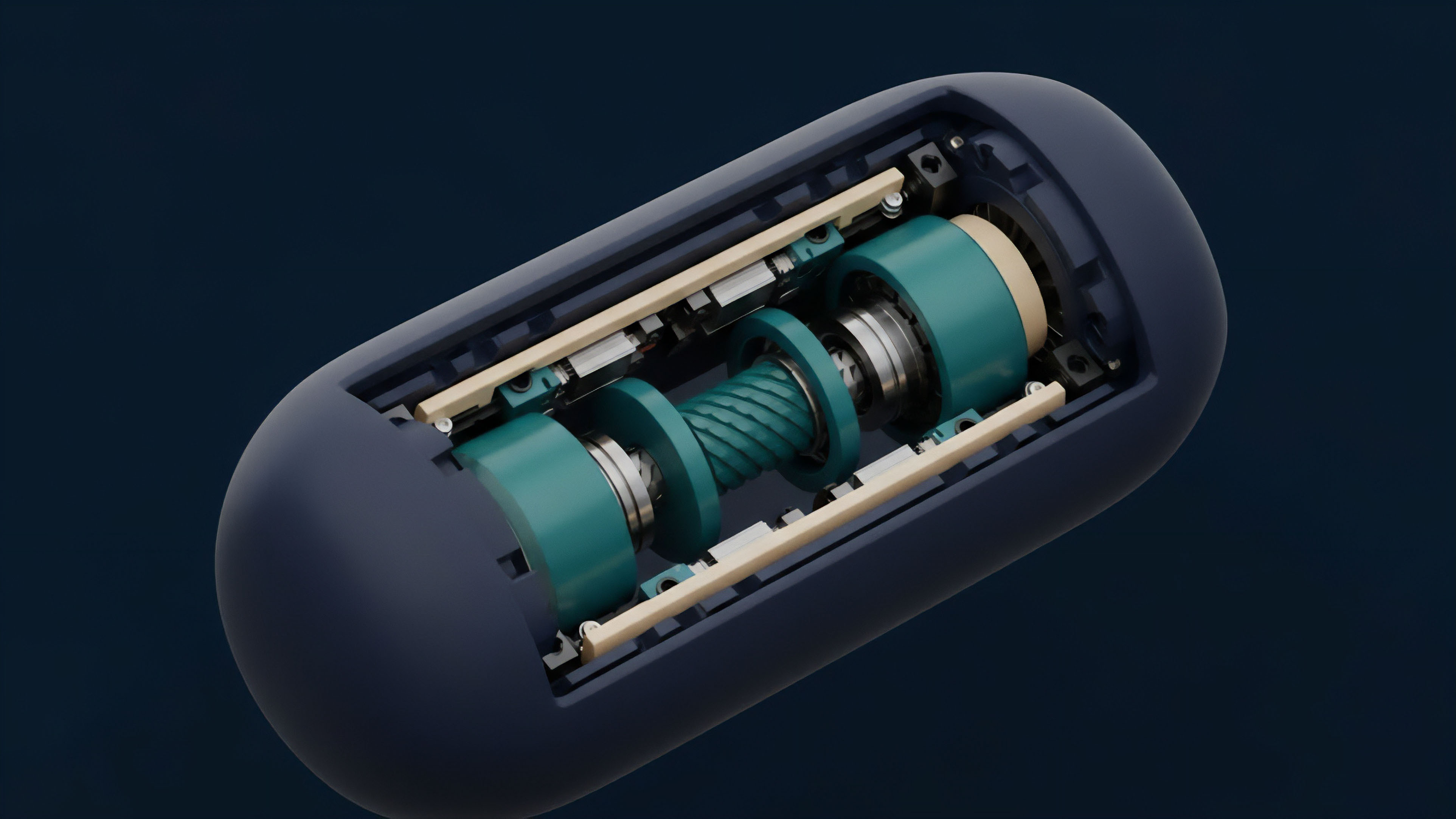
Current implementations of Real-Time Threat Monitoring utilize a multi-layered architecture that combines on-chain sensors with off-chain analytics.
The primary layer consists of smart contract events that emit data every time a trade, deposit, or withdrawal occurs. These events are ingested by indexing nodes that transform raw blockchain data into a queryable format, allowing for the rapid identification of anomalous behavior.
- Data Ingestion Layer: Utilizes JSON-RPC and streaming APIs to capture block headers and transaction receipts as they are broadcast.
- Analysis Engine: Applies machine learning algorithms to identify patterns associated with front-running, wash trading, or oracle attacks.
- Actionable Alerting: Triggers circuit breakers or emergency pauses when specific risk parameters are breached, preventing further loss.
- Post-Trade Surveillance: Monitors the settlement process to ensure that all option exercises are backed by sufficient collateral.
Heuristic Vs Machine Learning
Protocols balance deterministic heuristics with probabilistic machine learning models. Heuristics provide immediate, hard-coded responses to known threats, such as a 10% price deviation between oracles. Machine learning models, conversely, identify latent risks by analyzing multidimensional data points that human analysts might overlook.
This hybrid strategy ensures both speed and depth in Real-Time Threat Monitoring.
| Monitoring Method | Latency | Complexity | Detection Capability |
|---|---|---|---|
| Heuristic Rules | Ultra-Low | Low | Known Exploit Patterns |
| Statistical Analysis | Medium | Medium | Market Anomalies |
| ML Inference | High | High | Novel Attack Vectors |

Mempool Surveillance
Advanced Real-Time Threat Monitoring involves deep inspection of the mempool. By analyzing transactions before they are included in a block, the system can anticipate liquidation attempts or governance votes. This “pre-consensus” monitoring allows the protocol to proactively adjust its risk parameters, effectively neutralizing the advantage of high-frequency traders and MEV searchers.

Evolution
The transition from centralized surveillance to decentralized telemetry defines the recent history of this field.
Initially, monitoring was a proprietary function of centralized exchanges (CEXs), hidden behind closed doors. The rise of DeFi forced these processes into the open, leading to the creation of open-source monitoring frameworks and decentralized oracle networks. This transparency has fostered a more resilient derivative ecosystem where risks are visible to all participants.
Decentralized telemetry has transformed risk management from a proprietary secret into a public utility.
The focus has shifted from simple price monitoring to state-space analysis. Modern systems track the entire internal state of the smart contract, including variable balances, owner permissions, and reentrancy guards. This evolution was necessitated by the increasing sophistication of smart contract exploits, which often bypass simple price-based alerts.
Real-Time Threat Monitoring now incorporates formal verification principles to ensure that the protocol remains within its intended operational bounds.
Integration of AI
The adoption of Artificial Intelligence has enabled the detection of coordinated attacks across multiple protocols. Previously, monitoring was siloed within a single chain or platform. Current systems use cross-chain analytics to identify capital flight or collateral de-pegging that begins on one network and threatens another.
This holistic view is vital for managing the systemic risk inherent in the multichain future.

Circuit Breaker Innovation
The response mechanisms have also matured. Early versions of Real-Time Threat Monitoring could only send alerts to human operators. Modern systems are integrated with autonomous circuit breakers that can instantly halt specific trading pairs, increase collateralization ratios, or switch oracle providers without manual intervention.
This automation reduces the time-to-remediation, which is the most critical metric during a market crash.
Horizon
The future of Real-Time Threat Monitoring lies in the implementation of Zero-Knowledge Proofs (ZKPs) and fully homomorphic encryption. These technologies will allow protocols to perform private risk assessments, protecting sensitive user data while still providing verifiable proof of solvency. This will enable a new class of privacy-preserving derivatives that do not sacrifice security for anonymity.
Autonomous Risk Agents
We are moving toward an era of autonomous risk agents ⎊ AI-driven entities that live on-chain and manage Real-Time Threat Monitoring independently. These agents will possess their own capital reserves to act as backstop liquidators or market makers during periods of extreme stress. By operating at the protocol level, these agents will provide a level of liquidity provision that is currently only possible for the largest institutional market makers.
- Predictive Liquidity Modeling: Using deep learning to forecast liquidity droughts before they occur.
- Cross-Chain Telemetry: Unified monitoring of interoperability protocols to prevent bridge exploits.
- Self-Healing Code: Integration of Real-Time Threat Monitoring with automated patch generation to fix vulnerabilities in real-time.
- Quantum-Resistant Monitoring: Developing surveillance tools capable of detecting quantum computing threats to cryptographic signatures.

Systemic Resilience
The ultimate goal is the creation of a self-stabilizing financial system. In this vision, Real-Time Threat Monitoring is not just a defensive tool but the core engine of financial stability. By continuously rebalancing risk and incentives across the entire global market, these systems will minimize the frequency and severity of financial crises, ushering in a more robust and efficient era of value transfer.
Glossary
Front-Running Detection

Interoperability Protocol Security

Margin Engine Integrity

Oracle Latency Arbitrage
Zero-Knowledge Risk Assessment

Insurance Fund Protection

Predictive Liquidity Modeling

Quantum-Resistant Cryptography

Risk Parameters