
Essence
The Proxy Pattern Implementation functions as a foundational architectural abstraction within decentralized finance, decoupling the user-facing contract interface from the underlying logic and state management. By maintaining a stable entry point, this pattern facilitates seamless protocol upgrades and modular contract evolution without forcing migration of liquidity or disruption of historical state data.
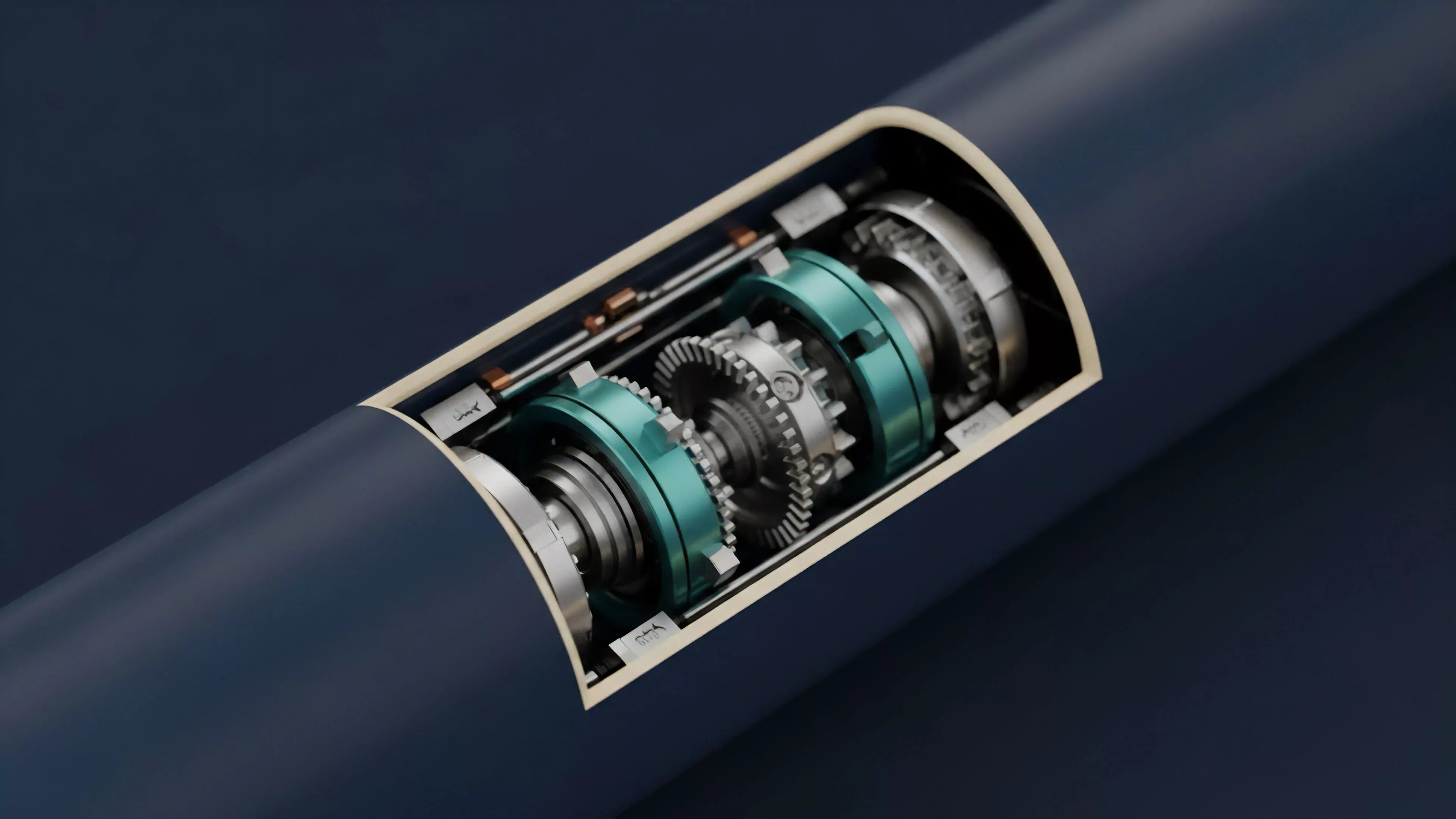
The proxy architecture establishes a separation between interface persistence and logic mutability to ensure continuous protocol operation.
At the technical level, this pattern relies on the delegatecall opcode, which enables a contract to execute code from another address while maintaining the context of the calling contract. This mechanism ensures that the proxy retains its storage and address while delegating operational authority to a dynamic implementation contract. The systemic significance resides in the capacity for protocol developers to patch vulnerabilities or deploy new financial instruments without fracturing the liquidity pool or forcing users to re-approve assets.

Origin
The requirement for the Proxy Pattern Implementation emerged from the inherent immutability of blockchain environments, which presents a significant barrier to traditional software maintenance cycles.
In early iterations of decentralized protocols, developers faced a stark trade-off: deploy static code that remains vulnerable to future exploits or implement complex migration paths that jeopardize user funds and fragment market liquidity.
- EIP-1967 established the standard storage slot convention for proxy contracts, preventing storage collisions between proxy and implementation.
- Transparent Proxy Pattern utilizes access control logic to ensure users only interact with the proxy, while administrators retain exclusive access to upgrade functions.
- UUPS Proxy Pattern moves the upgrade logic into the implementation contract itself, optimizing gas costs by reducing the complexity of the proxy contract.
This evolution represents a shift from static, rigid smart contracts toward adaptable financial infrastructure. The pattern draws heavily from object-oriented programming paradigms, repurposed for the adversarial, high-stakes domain of programmable money.

Theory
Mathematical and logical robustness in Proxy Pattern Implementation depends on the strict management of the delegatecall execution context. Because the proxy executes code within its own storage state, any error in the memory layout or storage variable ordering between the proxy and the implementation leads to immediate, catastrophic corruption of the contract state.
| Architecture | Upgrade Mechanism | Gas Efficiency |
| Transparent | External Admin | Lower |
| UUPS | Internal Logic | Higher |
| Diamond | Multi-Facet | Variable |
The risk model of this architecture is dominated by smart contract security concerns. If an attacker gains control over the implementation pointer, they can execute arbitrary code within the proxy’s storage context, effectively draining all assets. The structural integrity depends on robust governance models that control the upgrade process, ensuring that any logic change is subject to rigorous verification and community consensus.
The interplay between proxy logic and the underlying blockchain state resembles the distinction between a software layer and the hardware that executes it ⎊ a separation that remains fragile when the code managing the separation is itself subject to bugs.

Approach
Current implementation strategies focus on maximizing capital efficiency and minimizing the attack surface. Developers now prioritize standardized patterns like UUPS to lower gas consumption during interaction, while employing multi-signature wallets or DAO governance to restrict upgrade privileges.
Protocol security hinges on the immutability of the upgrade logic and the transparency of the state transition process.
Modern approaches also integrate automated formal verification tools to audit the memory layout across proxy upgrades. This practice is essential to prevent state-clobbering, where a new implementation inadvertently overwrites existing data. The strategy involves maintaining a clear separation between:
- Storage slots that remain constant across all iterations of the protocol logic.
- Functional logic that is updated to introduce new financial instruments or performance improvements.
- Access control lists that determine which entities are authorized to trigger an implementation update.

Evolution
The progression of Proxy Pattern Implementation has moved from simple, monolithic upgradeable contracts to complex, modular systems like the Diamond Pattern. This shift addresses the limitations of contract size constraints, allowing protocols to expand their feature set without reaching the maximum bytecode limit of the Ethereum Virtual Machine. The transition reflects a maturing understanding of systems risk and the need for modularity in large-scale decentralized applications.
Protocols no longer rely on a single, massive implementation contract; instead, they decompose functionality into discrete facets, each managed through a central proxy. This granular control allows for surgical updates to specific protocol features, minimizing the impact of potential bugs. The industry has effectively moved from brute-force migration strategies to a nuanced, state-preserving architectural framework.
Horizon
The future of Proxy Pattern Implementation lies in the development of automated, trust-minimized upgrade paths that remove human intervention from the loop.
We expect the rise of governance-gated, time-locked upgrades where the protocol logic updates only after a pre-defined period of community verification and automated security testing.
Future upgrades will likely transition from manual administrative control to algorithmic, time-locked state transitions.
Further innovation will focus on cross-chain proxy synchronization, where state updates are propagated across multiple L2 environments simultaneously. This will require sophisticated consensus mechanisms to ensure that the implementation state remains consistent across the entire fragmented liquidity landscape. As decentralized derivatives become more complex, the ability to iterate on logic without sacrificing market microstructure integrity will determine which protocols survive the next decade of financial competition.
