
Essence
Proxy Contract Architecture functions as the foundational decoupling mechanism between user-facing interface logic and the underlying immutable financial execution state. It enables seamless protocol upgrades, feature deployment, and critical security patching without necessitating complex asset migrations or disrupting liquidity pools. By maintaining a stable, static address for external interactions while delegating operational logic to modular, updatable implementation contracts, these structures preserve the continuity of decentralized financial services.
Proxy Contract Architecture decouples immutable interface endpoints from modular execution logic to enable secure, non-disruptive protocol evolution.
The primary utility lies in achieving a state of perpetual maintenance. In the volatile landscape of decentralized finance, the ability to address vulnerabilities or incorporate new risk parameters instantly is a structural imperative. This design pattern ensures that users retain their interaction history and liquidity positions, while developers manage the evolving backend code through controlled administrative processes.
Origin
The genesis of Proxy Contract Architecture stems from the inherent tension between the desire for trustless, immutable code and the reality of human error in complex software development.
Early decentralized applications encountered insurmountable hurdles when critical bugs were discovered post-deployment, often forcing developers to abandon existing contracts and manually migrate users to new versions. This fragmented liquidity and shattered user trust. Developers observed the limitations of static deployment models during the rapid iteration cycles of early decentralized exchanges.
The requirement for a mechanism that could reconcile the rigidity of blockchain storage with the flexibility of evolving logic led to the adoption of the delegatecall opcode within the Ethereum Virtual Machine. This technical capability allows a contract to execute code stored in another contract while maintaining its own storage context, forming the technical bedrock for modern proxy patterns.
- Delegatecall provides the low-level mechanism for executing external logic within the context of the caller.
- Storage Collision represents the primary technical risk where implementation logic overwrites existing state variables.
- Administrative Control defines the governance mechanism required to authorize upgrades to the implementation contract.

Theory
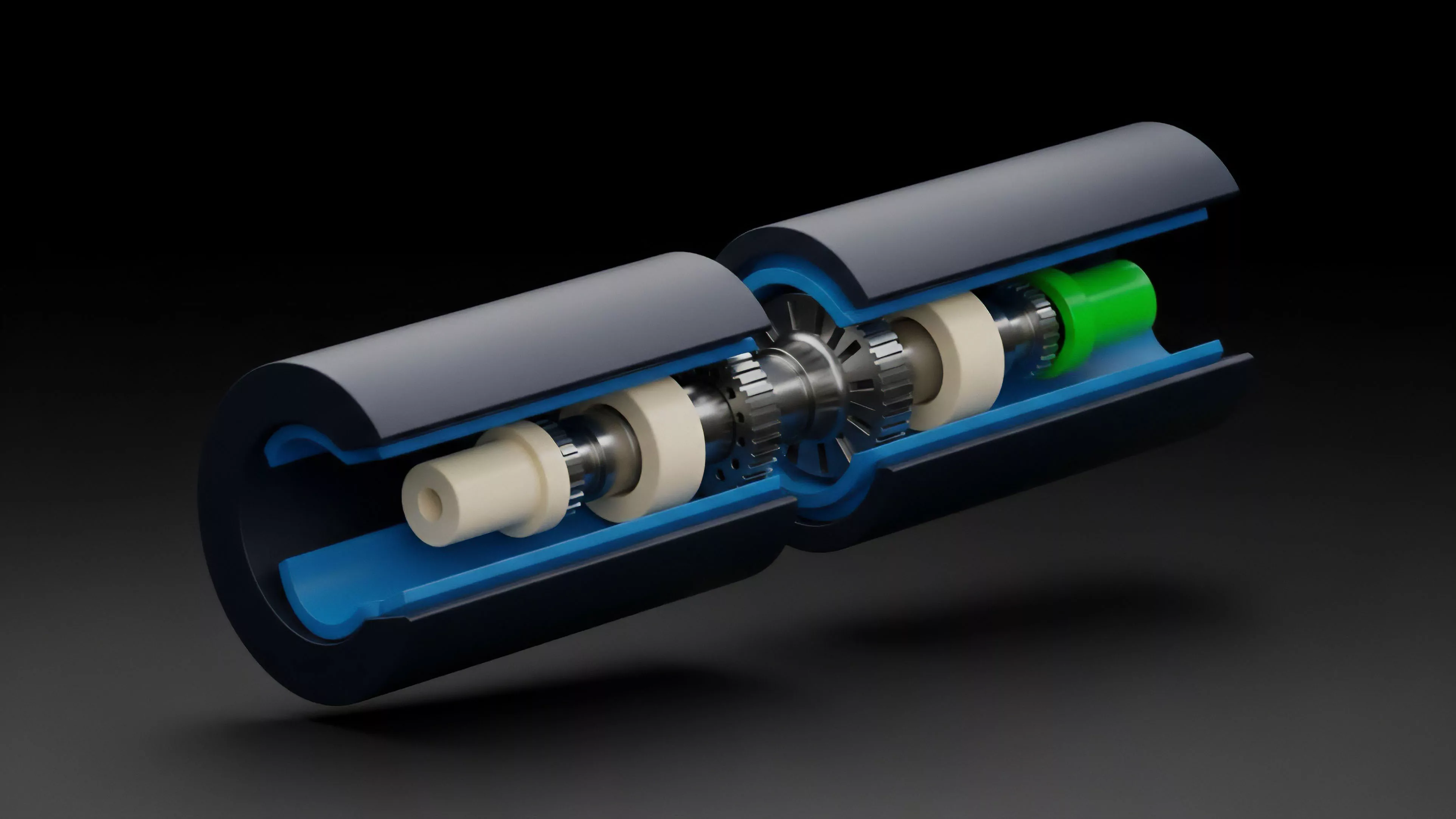
The theoretical framework of Proxy Contract Architecture relies on the strict separation of concerns between storage, logic, and interface. A central Proxy Contract holds the user assets, state, and identity, while an Implementation Contract contains the operational logic. When a user sends a transaction to the proxy, the proxy uses the delegatecall instruction to forward the execution request to the implementation.
| Component | Functional Responsibility |
| Proxy Contract | State storage and persistent address |
| Implementation Contract | Business logic and execution functions |
| Governance Module | Authorized upgrade triggers |
The mathematical and logical challenge involves ensuring that storage layouts remain consistent across versions. If the new implementation contract expects a variable at a different storage slot than the previous version, data corruption occurs. This necessitates strict adherence to storage slot ordering or the use of unstructured storage patterns, such as EIP-1967, which designates specific, randomized slots for storing the implementation address to avoid conflicts.
Consistent storage layouts and controlled delegation pathways prevent state corruption during the lifecycle of an upgradeable contract.
Consider the implications for risk management in derivatives. A protocol might need to adjust margin requirements or liquidation thresholds dynamically. Through this architecture, the logic governing these parameters can be replaced or refined, while the Proxy Contract maintains the integrity of the margin vaults and user collateral balances throughout the transition.

Approach
Current implementations prioritize the minimization of trust assumptions through multi-signature wallets or decentralized governance voting to control the upgrade path.
The industry has converged on standardized patterns like the Transparent Proxy or the UUPS (Universal Upgradeable Proxy Standard) to mitigate common pitfalls. These patterns strictly delineate the upgrade authority, preventing unauthorized logic changes that could drain assets.
- Transparent Proxy isolates administrative functions from user functions to eliminate potential function selector clashes.
- UUPS Pattern places the upgrade logic within the implementation contract, reducing the gas overhead of the proxy itself.
- Diamond Standard enables modular, multi-contract architectures where specific facets of functionality are managed independently.
The tactical execution of an upgrade involves deploying the new logic contract, testing it within a simulation environment against current state snapshots, and then updating the implementation pointer within the Proxy Contract. This process requires rigorous auditing of the new logic, as the proxy effectively delegates its entire authority to the implementation.
| Standard | Upgrade Location | Gas Efficiency |
| Transparent | Proxy Contract | Moderate |
| UUPS | Implementation Contract | High |
| Diamond | Facet Management | Variable |

Evolution
The trajectory of Proxy Contract Architecture has moved from simple, centralized upgradeability toward increasingly decentralized and modular frameworks. Initially, protocols utilized simple owner-based systems, which created a significant central point of failure. The shift toward time-locked, community-governed upgrades reflects the broader maturation of decentralized finance, where security is no longer an afterthought but the core product.
The evolution also encompasses the development of specialized tools for verifying storage layouts. Automated analysis tools now scan for potential storage collisions before deployment, significantly reducing the surface area for technical exploits. Furthermore, the industry is experimenting with immutable proxies ⎊ contracts that are upgradeable for a set period and then renounce control to become permanently immutable, balancing early-stage agility with long-term stability.
Decentralized upgrade governance and automated storage verification have transformed proxy systems into robust pillars of protocol security.
The integration of formal verification into the upgrade lifecycle allows architects to mathematically prove that the new implementation preserves the state invariants of the system. This transition from manual auditing to rigorous, code-based verification is the necessary step for institutional-grade financial infrastructure, as it provides verifiable guarantees about the behavior of the upgraded system.

Horizon
The future of Proxy Contract Architecture lies in the development of self-optimizing, autonomous systems that can adjust their own parameters based on market conditions without requiring human-in-the-loop intervention. These systems will likely incorporate on-chain oracle data to trigger logic shifts, such as adjusting interest rates or collateral factors in response to realized volatility. Furthermore, we anticipate the emergence of standardized, composable implementation modules. Protocols will not build monolithic logic contracts but will instead plug in audited, pre-existing modules for specific functions like risk assessment or liquidation. This modularity will accelerate innovation while confining security risks to individual components, creating a more resilient and agile ecosystem for crypto derivatives. The systemic implication is a move toward financial protocols that are both permanent in their existence and infinitely adaptable in their utility. This capability will eventually allow decentralized systems to outpace traditional financial institutions in speed, efficiency, and resilience, as the overhead of structural change is reduced to a simple transaction execution.
