Essence
The survival of a decentralized ledger depends on the mathematical certainty that subverting the truth costs more than the potential profit from the lie. Proof of Stake Security represents the economic wall protecting this truth, where the integrity of the network is collateralized by the market value of the native asset. This mechanism replaces the physical energy consumption of earlier systems with a capital-at-risk model, creating a direct link between the valuation of the protocol and its resistance to censorship or manipulation.
Financial participants viewing this through a derivatives lens recognize that Proof of Stake Security functions as a massive, protocol-level insurance bond. Validators lock up assets as a guarantee of honest behavior, knowing that any attempt to double-sign or reorganize the chain results in the immediate forfeiture of that capital. This creates a deterministic cost of corruption ⎊ a figure that can be calculated by looking at the total value staked and the slashing parameters defined in the code.
Proof of Stake Security functions as a financial bond where the integrity of the ledger is collateralized by the market value of the native asset.
The systemic relevance of this security model extends to the pricing of every option and derivative built on the network. If the security budget drops, the tail risk of a consensus failure increases, which should theoretically expand the volatility skew of out-of-the-money puts. Market participants are effectively trading the stability of the underlying consensus mechanism every time they engage with long-dated instruments.

Origin
The transition from resource-heavy validation to capital-based validation emerged from the need to scale decentralized systems without the environmental and industrial overhead of hardware-based competition.
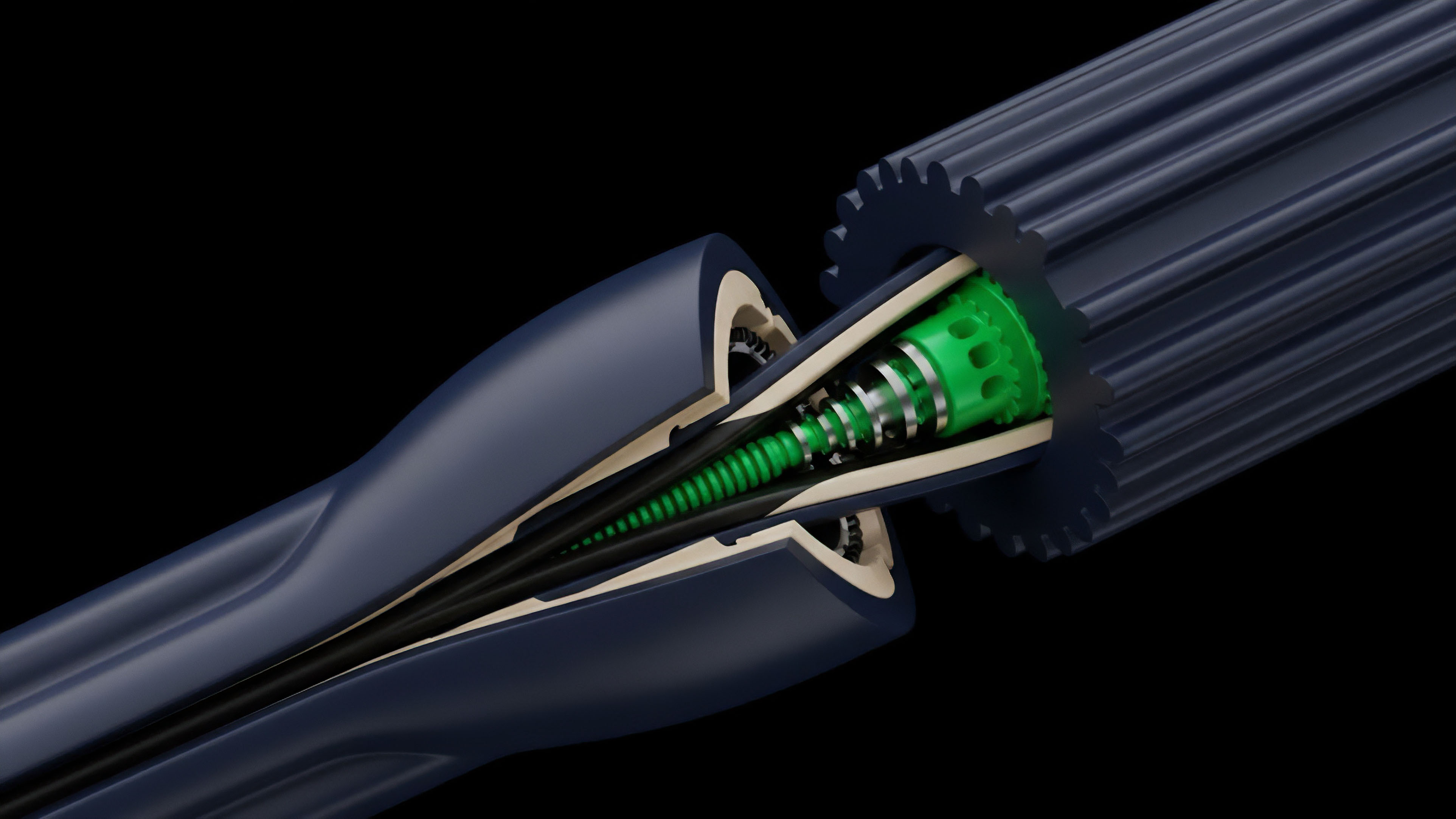
Early experiments like Peercoin introduced the concept of coin age, but the modern implementation of Proof of Stake Security matured with the realization that slashing ⎊ the explicit destruction of collateral ⎊ was the only way to solve the nothing-at-stake problem. This shift transformed the validator from a miner into a financial staker. The security of the network moved from the physical world of ASICs and electricity to the balance sheets of institutional and retail participants.
This change allowed for the creation of Liquid Staking Derivatives, which turned the security collateral itself into a tradable, yield-bearing asset, fundamentally altering the liquidity dynamics of the crypto-economy.
The cost of attacking a network scales directly with the liquidity and market capitalization of the staked instrument.
By decoupling security from energy, protocols gained the ability to fine-tune their economic defenses through governance. The security budget became a variable that could be adjusted based on market conditions, inflation targets, and the required level of economic finality. This flexibility introduced a new era of protocol-level risk management, where the defense of the network is a function of game-theoretic design and capital efficiency.
Theory
The mathematical foundation of Proof of Stake Security rests on the Byzantine Fault Tolerance threshold, typically requiring an adversary to control more than one-third of the total staked weight to halt the network or two-thirds to finalize a fraudulent state.
This creates a binary risk profile for the protocol. Below these thresholds, the system maintains safety and liveness; above them, the economic guarantees of the ledger dissolve.
Economic Finality and Slashing
The concept of economic finality is the most significant contribution of this model to quantitative finance. Unlike probabilistic finality, where the risk of a reversal decreases over time, economic finality provides a point at which a reversal becomes a known, massive financial loss for the attacker. This loss is executed through slashing, an automated protocol-level event that burns the attacker’s stake.
| Metric | Proof of Work Comparison | Proof of Stake Implementation |
|---|---|---|
| Capital Requirement | Hardware and Energy | Financial Asset Staking |
| Attack Penalty | Sunk Operational Cost | Explicit Asset Forfeiture |
| Security Scaling | Linear Energy Growth | Exponential Capital Compounding |
The Security Volatility Smile
A fascinating correlation exists between the security budget and the implied volatility of the native asset. In physical systems, entropy increases as energy decreases ⎊ a principle that mirrors the economic decay of a protocol with dwindling stake. When the percentage of the circulating supply that is staked falls, the network becomes more susceptible to governance attacks or short-range reorganizations.
This increased systemic risk manifests as a widening of the volatility smile, as the probability of a black swan event related to network failure rises.
Derivatives built on top of staked assets introduce a layer of systemic risk where slashing events can trigger cascading liquidations.

Approach
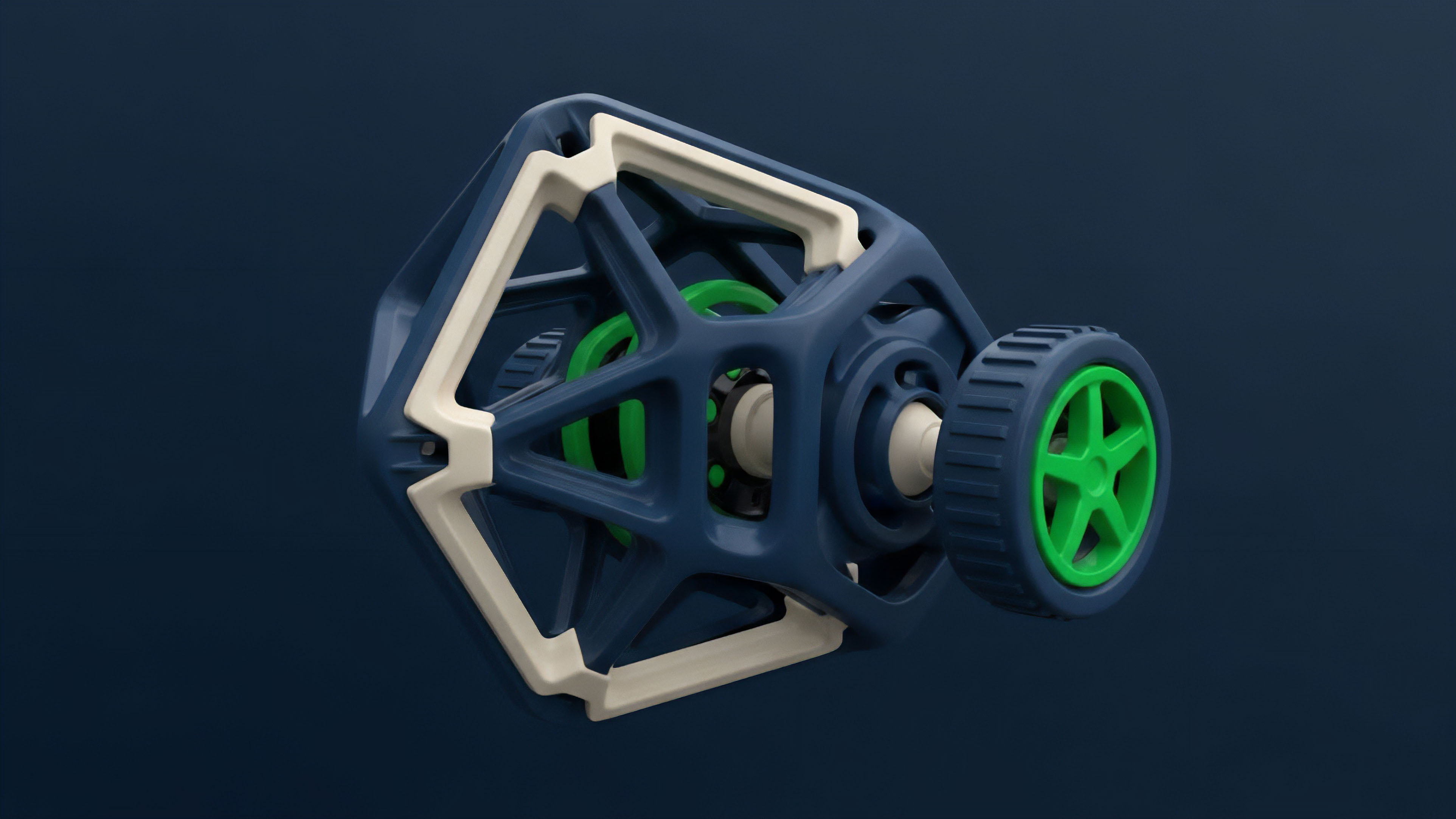
Current implementations of Proof of Stake Security utilize a multi-layered system of rewards and penalties to maintain equilibrium. Validators are selected based on their stake weight, and their performance is monitored in real-time. Failure to maintain liveness results in minor penalties, while malicious actions trigger the more severe slashing mechanisms.
Validator Risk Management
Professional staking operations now employ sophisticated risk management strategies to protect their collateral. These include multi-signature setups, distributed validator technology, and insurance against slashing events. The goal is to maximize uptime and yield while minimizing the probability of a catastrophic capital loss.
- Slashing creates a hard floor for the cost of adversarial action.
- Finality ensures that transactions become irreversible after a specific number of attestations.
- Economic Bonds align the incentives of validators with the long-term value of the network.
Liquid Staking and Re-Staking
The rise of re-staking protocols has introduced a new dimension to Proof of Stake Security. By allowing the same capital to secure multiple services simultaneously, these protocols increase the capital efficiency of the staked asset. This creates a complex web of interconnected security where a failure in one middleware service could potentially impact the security of the base layer.
| Risk Factor | Probability | Impact on Options Delta |
|---|---|---|
| Double Signing | Low | High Negative Skew |
| Downtime | Moderate | Minor Vega Decay |
| Collusion | Low | Extreme Tail Risk |

Evolution
The transition from isolated security pools to shared security models represents the most significant shift in the history of decentralized consensus. In the early stages, every new chain had to bootstrap its own validator set and economic value ⎊ a process that was both difficult and risky. This fragmentation led to many smaller networks having weak Proof of Stake Security, making them easy targets for 51% attacks.
The emergence of modularity and re-staking changed this dynamic entirely. Now, a new protocol can lease security from an established network like Ethereum, effectively inheriting its economic wall. This commoditization of security allows developers to focus on application logic while relying on a massive, decentralized pool of capital for protection.
This evolution has also led to the professionalization of the validator industry, where a few large entities control significant portions of the stake. While this centralization introduces new risks, it also brings a level of operational stability and institutional-grade security that was previously unavailable. The market for security is becoming more efficient, with clear pricing for the cost of leased capital and the risk of slashing.
This maturation is a prerequisite for the next phase of global financial integration, where decentralized ledgers must support trillions of dollars in value with absolute certainty. The interplay between the yield offered by staking and the risk of the underlying security budget is now a primary driver of the crypto-macro environment, influencing everything from interest rate parity to the pricing of complex synthetic derivatives.
Horizon
The future of Proof of Stake Security lies in the creation of sophisticated hedging instruments for slashing risk. We are moving toward a world where security is not just a binary state but a tradable commodity with its own volatility surface.
The development of Slashing Risk Adjusted Volatility Indices will allow market participants to price the specific risk of consensus failure separately from the price volatility of the underlying asset.

Security as a Service
As shared security models become the standard, we will see the rise of security marketplaces. In these venues, protocols will bid for the collateral of validators, and the price of Proof of Stake Security will be determined by the supply and demand for economic finality. This will create a transparent cost of trust, allowing for more accurate valuation of decentralized applications.
- The architecture of a robust security budget requires Capital Density to withstand large-scale coordinated attacks.
- The architecture of a robust security budget requires Validator Decentralization to prevent single points of failure.
- The architecture of a robust security budget requires Transparent Incentives to encourage honest participation.
The Socratic Conjecture
The divergence between the yield required by stakers and the security budget needed by the protocol creates a critical pivot point. If the yield falls too low, capital exits, and security collapses. If the yield is too high, the asset suffers from inflationary decay. A testable hypothesis emerges: the long-term stability of a Proof of Stake Security model is inversely proportional to the velocity of its liquid staking derivatives. As these derivatives become more liquid, the “sticky” capital that provides true security is replaced by mercenary capital, increasing the system’s fragility during market drawdowns. To mitigate this, we must architect a Slashing-Risk Adjusted Volatility Index that provides real-time feedback to the protocol’s issuance engine, creating a self-correcting security budget that responds to market stress before a failure occurs.

Glossary

Long-Range Attack
Contagion Vector

Signature Aggregation

Validator Set
Mev Redistribution

Yield Compression

Data Availability

Slashing Risk

Volatility Floor