Essence
The Price Manipulation Cost in crypto options represents the financial and operational expenditure required to force a specific outcome in a derivative contract by artificially influencing the price of the underlying asset. This concept is distinct from general market manipulation because its profitability is directly tied to the leveraged nature of the options contract itself, rather than simply profiting from a spot market position. An attacker calculates the cost to move the underlying price against the potential payout of the derivative, seeking scenarios where the required capital injection is significantly less than the potential profit from triggering a liquidation or forcing an option to expire in-the-money.
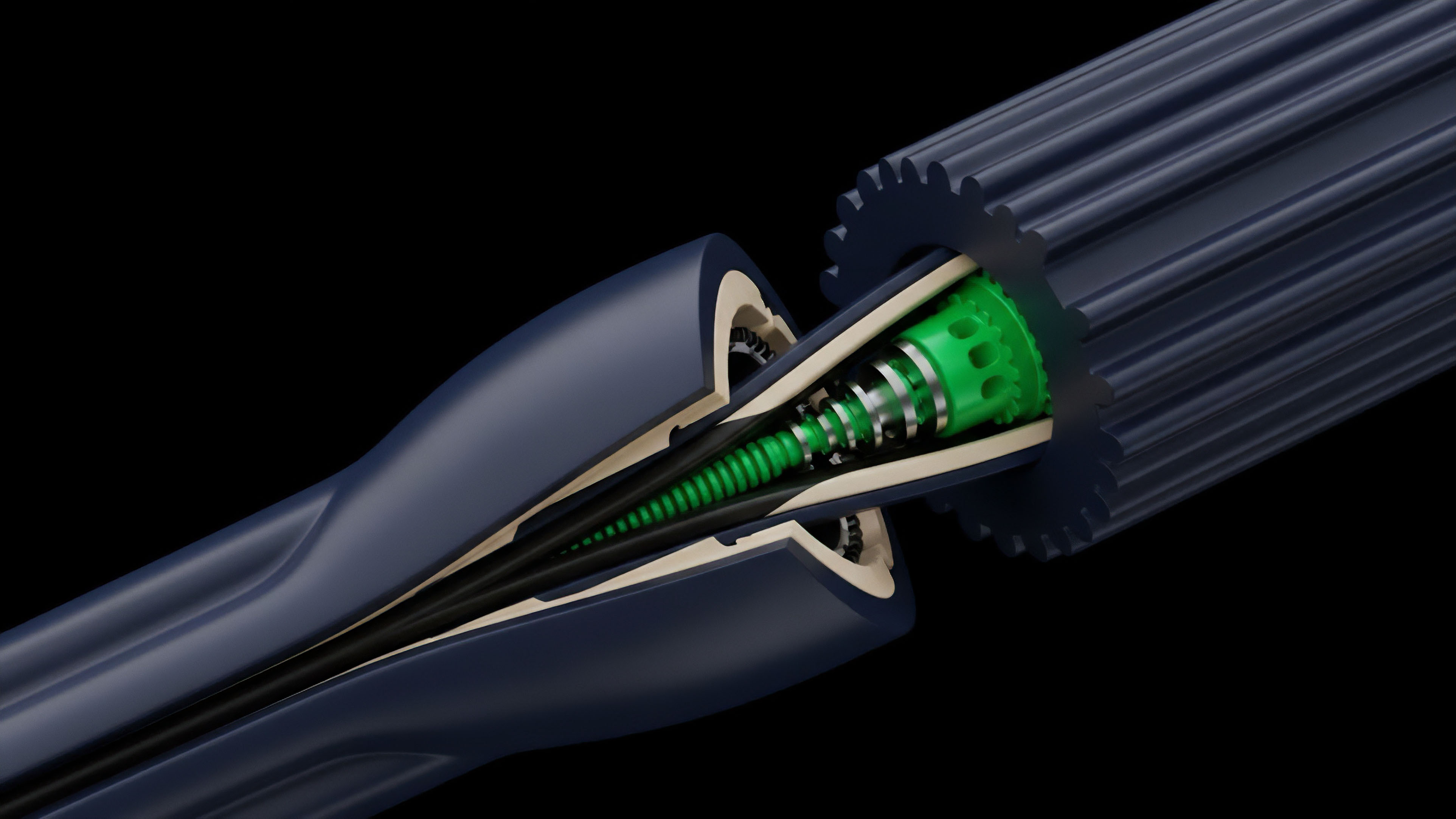
The systemic risk associated with this cost calculation stems from the reliance on on-chain price feeds, oracles, and the architecture of decentralized exchanges. When a protocol’s oracle mechanism can be influenced by a single large trade, the cost of manipulation drops dramatically. The core vulnerability is the mismatch between the capital required to move a spot market (the manipulation cost) and the potential gain from a leveraged derivative position (the payout).
In a highly liquid market, this cost is prohibitive, but in low-liquidity crypto markets, particularly those with flash loan capabilities, the manipulation cost can be reduced to near zero for a sophisticated attacker.
Price manipulation cost quantifies the capital required to exploit a derivative protocol by artificially influencing its underlying asset price, often targeting oracle mechanisms.
This vulnerability is particularly acute in American-style options protocols, where early exercise or liquidation can be triggered at any point before expiration, creating a continuous attack surface. The cost is a function of several variables, including the depth of liquidity pools, the specific design of the oracle, and the time required for a manipulation attempt. A well-designed protocol aims to maximize this cost to ensure economic security, making manipulation unprofitable for all but the most well-capitalized attackers.

Origin
The roots of price manipulation cost in crypto options lie in the intersection of traditional financial vulnerabilities and the novel technical architecture of decentralized finance. In traditional markets, manipulation has existed for centuries, with methods like “cornering the market” or “spoofing” requiring immense capital and facing high regulatory risk. However, the cost calculation changed fundamentally with the advent of automated market makers (AMMs) and flash loans in DeFi.
The origin story of this specific cost model begins when protocols started using single-source oracles or low-liquidity AMM pools for price discovery.
The early failures of DeFi protocols in 2020 and 2021 demonstrated that the manipulation cost was far lower than anticipated. Attackers realized they did not need to own large amounts of capital long-term; they simply needed to borrow it momentarily via flash loans, execute a manipulation, and repay the loan within a single transaction block. This discovery effectively reduced the capital component of the manipulation cost to zero for the attacker, shifting the cost burden entirely onto the protocol’s security architecture and the potential losses of other participants.
The resulting losses forced a reevaluation of how price feeds were sourced and how derivative contracts calculated settlement prices.
The concept gained prominence as protocols realized that a simple spot price feed was insufficient for robust derivative markets. The cost of manipulation was directly proportional to the “freshness” and “decentralization” of the oracle data. A centralized or stale oracle presented a low manipulation cost, as an attacker could easily manipulate the single source or wait for a price update delay.
The evolution from these initial, simplistic price feeds to sophisticated, decentralized oracle networks marks the origin of modern risk management for manipulation cost.

Theory
The theoretical calculation of price manipulation cost relies on an adversarial game theory framework, specifically analyzing the cost-benefit analysis for an attacker. The core principle dictates that a protocol is secure only if the cost to attack exceeds the maximum possible profit from the attack. This cost calculation involves several key components, including the capital required to move the price (slippage cost), transaction fees, and the risk of front-running by other market participants.
The most critical factor is the oracle mechanism, which serves as the interface between the real-world price and the derivative contract.
When modeling manipulation cost, we must differentiate between two primary attack vectors. The first vector involves manipulating a low-liquidity AMM pool that serves as the price feed for the derivative. The cost here is calculated based on the slippage curve of the AMM pool.
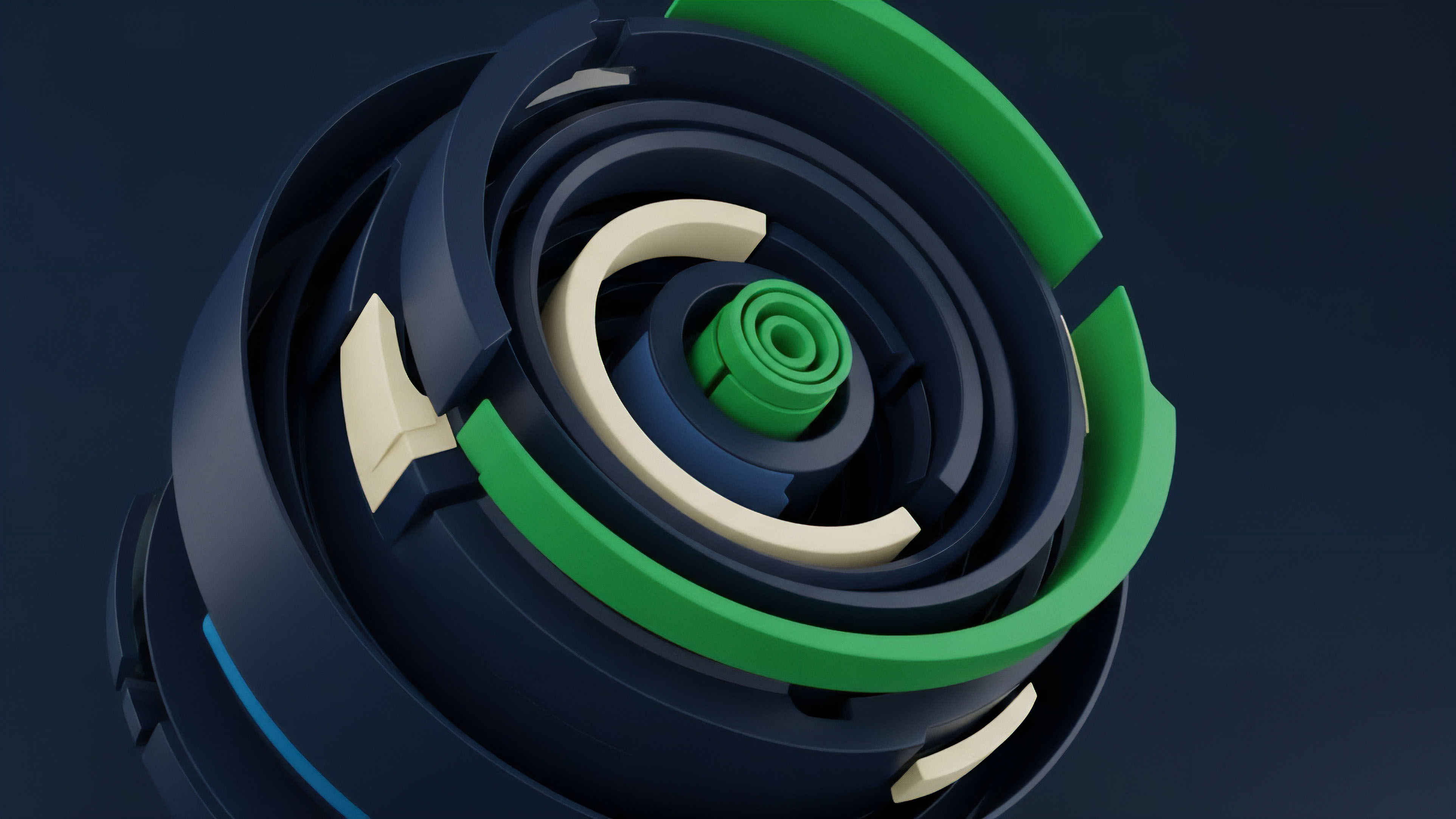
The second, more complex vector involves manipulating a decentralized oracle network. The cost calculation in this scenario becomes probabilistic, depending on the number of nodes an attacker needs to compromise and the economic incentives required to sway those nodes.
A successful manipulation attack requires an attacker to calculate the slippage cost in a low-liquidity pool and ensure the profit from the options payout exceeds this cost.
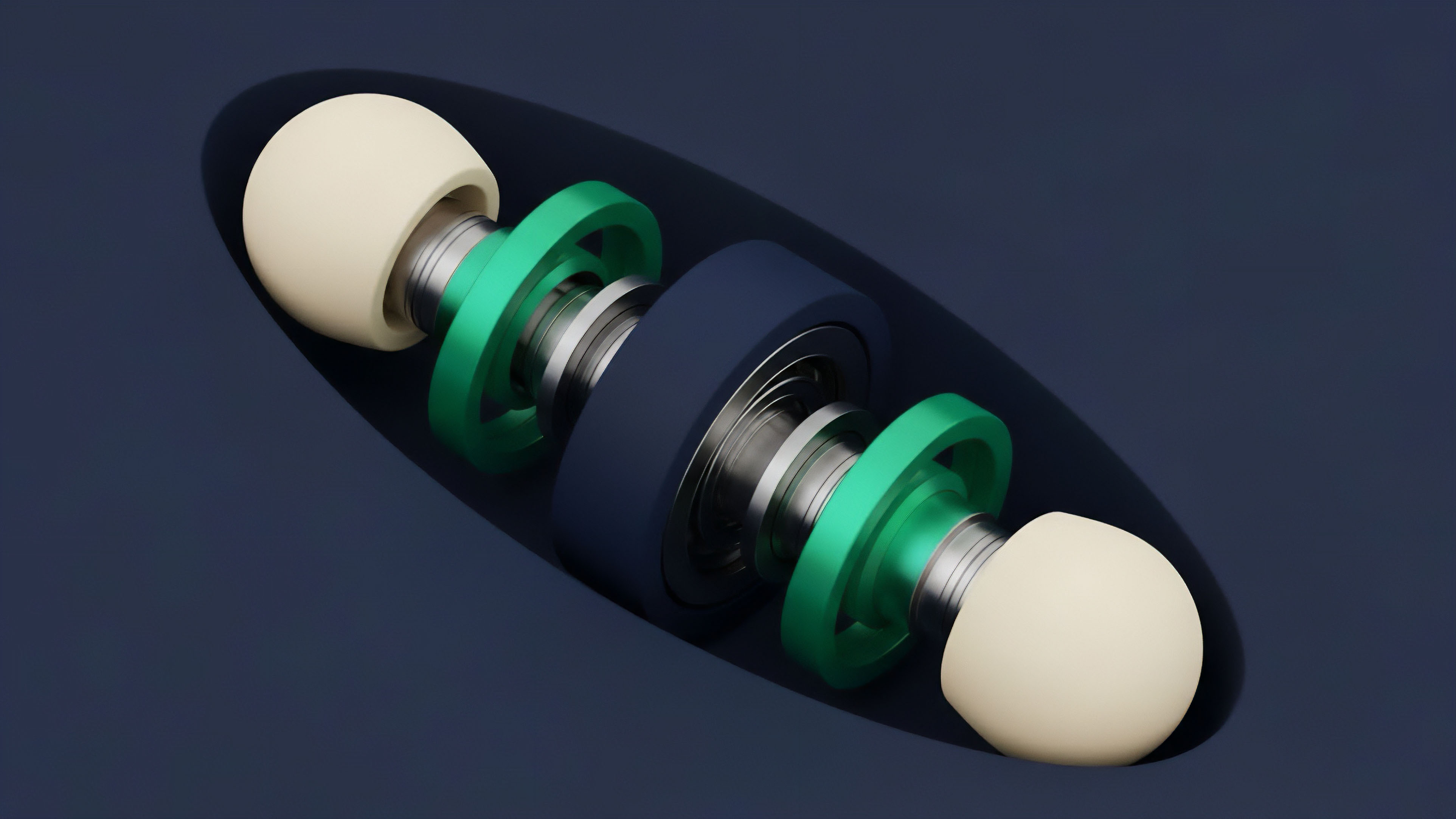
A central theoretical consideration is the “manipulation delta,” which measures the sensitivity of a derivative’s value to changes in the underlying price. For options, this delta approaches 1 near expiration for in-the-money options, making a small price movement highly profitable for the attacker. This creates a specific vulnerability window where manipulation cost must be highest.
The protocol’s design must account for this by either increasing liquidity, implementing time-weighted average prices (TWAPs), or utilizing circuit breakers to halt trading during extreme volatility.
Consider a simplified model where an attacker seeks to manipulate a price feed to liquidate a large options position. The attacker calculates the capital required to move the price by X percent, where X is the liquidation threshold. If the profit from the liquidation exceeds this capital cost, the protocol is vulnerable.
The theoretical solution involves ensuring that the liquidity required to move the price by X percent is always greater than the value of the positions being liquidated.
| Attack Vector | Cost Components | Vulnerability Window |
|---|---|---|
| AMM Pool Manipulation | Slippage cost, transaction fees, flash loan fees | Low liquidity, high leverage positions near expiration |
| Decentralized Oracle Compromise | Bribe cost for oracle nodes, collateral requirements | Node centralization, low economic incentives for honest reporting |

Approach
The practical approach to managing price manipulation cost centers on hardening the oracle and improving liquidity. The first-line defense for options protocols is to increase the capital required for manipulation by utilizing robust price feeds. This moves beyond single-source oracles, which are inherently fragile, toward decentralized oracle networks (DONs) that aggregate data from multiple exchanges and sources.
The cost to manipulate a DON is significantly higher, as an attacker must influence prices across several venues simultaneously.
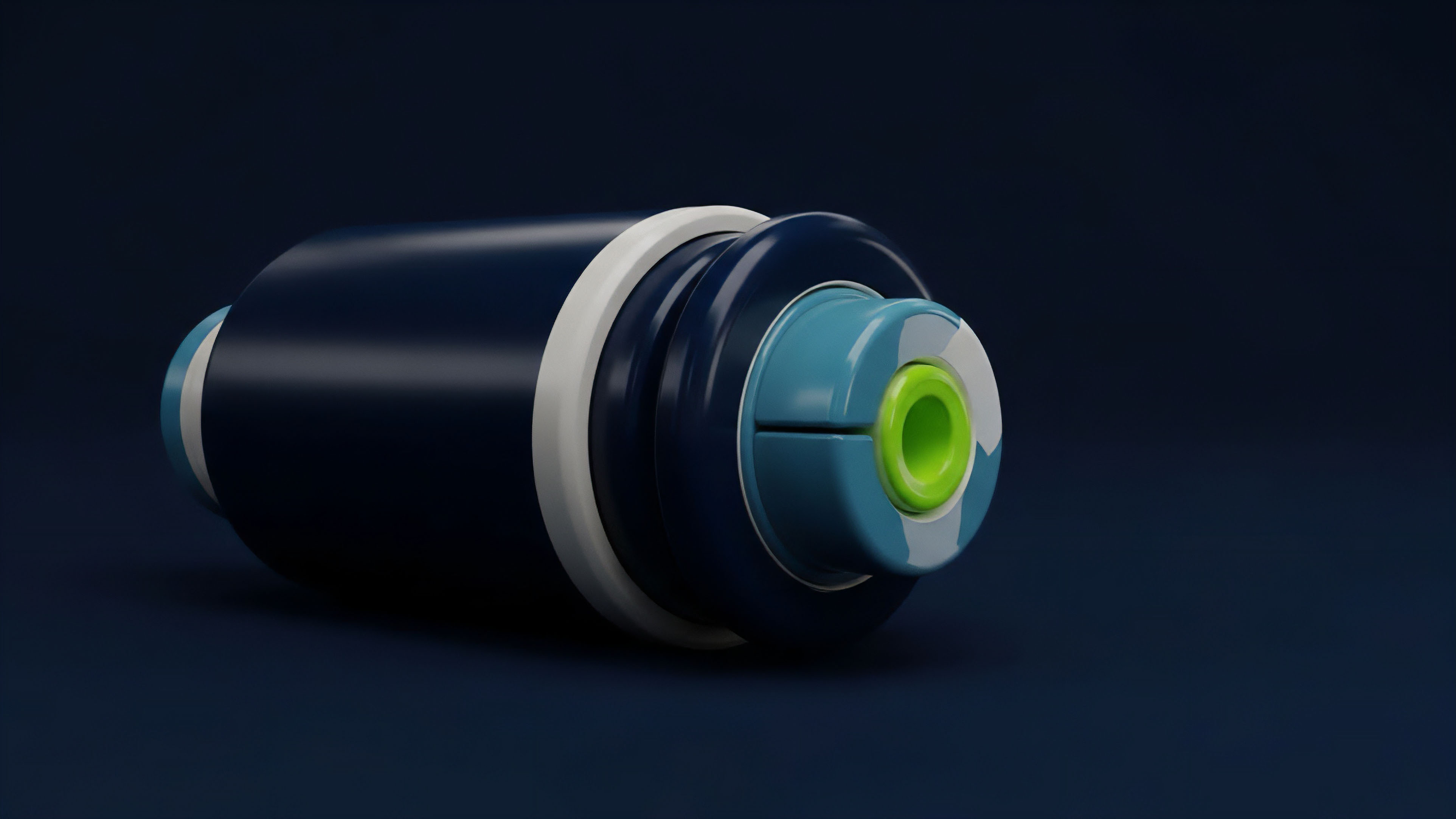
Another common approach involves implementing time-weighted average prices (TWAPs). A TWAP calculates the average price over a specific time interval, making it necessary for an attacker to sustain the manipulated price for the duration of that interval. This significantly increases the capital cost and risk for the attacker.
If an attacker must hold a large position for 10 minutes to manipulate the price, the risk of front-running by other market participants increases, reducing the attack’s profitability. This approach trades off price freshness for security, a critical design choice for options protocols where expiration price accuracy is paramount.
A third strategy involves designing protocol-level circuit breakers. These mechanisms automatically halt trading or liquidate positions in a controlled manner if price volatility exceeds a predefined threshold. While effective at preventing catastrophic losses from sudden manipulation attempts, circuit breakers introduce a different kind of risk ⎊ that of a “stuck” protocol during periods of genuine market stress.
The trade-off here is between market stability and market efficiency, a difficult balance to strike in a fast-moving environment.
- Decentralized Oracle Networks: These systems increase manipulation cost by requiring an attacker to compromise multiple data sources, ensuring price feeds reflect global market consensus rather than a single exchange’s price.
- Time-Weighted Average Prices: By averaging prices over a time window, TWAPs prevent flash loan attacks and force attackers to commit capital for a longer duration, increasing the cost and risk of the manipulation attempt.
- Liquidity Incentivization: Increasing the depth of liquidity pools directly increases the slippage cost for manipulation. Protocols often offer incentives to liquidity providers to make manipulation economically unviable.

Evolution
The evolution of price manipulation cost has been an ongoing arms race between protocol designers and adversarial actors. Initially, manipulation cost was underestimated, leading to a wave of flash loan attacks on early DeFi protocols. These attacks were straightforward: borrow capital, manipulate a low-liquidity spot price, and trigger a derivative liquidation or favorable option exercise.
The cost for the attacker was minimal, often just the transaction fees. This era taught the industry that on-chain price feeds must be resistant to single-transaction manipulation.
The first significant evolutionary response was the widespread adoption of TWAPs. This raised the manipulation cost by requiring a sustained attack over time. However, attackers adapted by developing more sophisticated strategies, such as “bribe attacks” on oracle networks.
The evolution continued with the introduction of decentralized oracle networks (DONs) that source data from multiple independent nodes and exchanges. This forces attackers to compromise a significant portion of the network to influence the price, increasing the cost substantially.
We see a parallel evolution in options protocol design. Early protocols focused on capital efficiency, but often sacrificed security by relying on simplistic price feeds. Newer protocols are prioritizing security first, often incorporating features like dynamic collateral requirements and liquidation mechanisms that use a combination of TWAPs and external market data.
This progression highlights a shift in design philosophy where security and manipulation resistance are now considered foundational, rather than secondary optimizations.
The arms race between attackers and defenders has shifted the focus from simple price feeds to sophisticated, multi-layered oracle systems that increase manipulation cost by orders of magnitude.
This dynamic resembles a co-evolutionary system where each new defense mechanism leads to a more complex attack vector. The manipulation cost calculation constantly changes as new tools and protocol architectures are developed. The current generation of protocols recognizes that a manipulation-resistant design must be built from first principles, where the cost to attack is mathematically guaranteed to be higher than the potential profit from any exploit.

Horizon
Looking ahead, the horizon for price manipulation cost involves a move toward Layer 2 solutions and a deeper integration of economic security mechanisms. The current challenge with Layer 1 oracles is the cost of on-chain data verification and aggregation, which can limit the frequency of price updates. Layer 2 solutions, particularly those utilizing optimistic rollups or zero-knowledge proofs, offer a path to higher-frequency, lower-cost price updates, making manipulation more difficult by increasing the required speed and precision of an attack.
The future of options protocol design will likely involve a shift toward “trust-minimized” oracles that use game-theoretic incentives rather than relying solely on external data sources. This means designing a system where it is economically irrational for an oracle node to report a false price. The manipulation cost in this future state is not just the capital required to move the price; it is the economic penalty for misbehavior, which must exceed the potential profit from manipulation.
This approach aligns with the core principles of decentralized finance, where security is derived from economic incentives rather than trust in a centralized entity.
We must also consider the role of regulatory pressure on manipulation cost. As traditional finance institutions enter the crypto options space, they will demand higher standards of market integrity. This will accelerate the adoption of robust oracle solutions and standardized risk management practices.
The cost of manipulation will become less about technical exploits and more about the cost of violating established regulatory frameworks, mirroring the high costs seen in traditional markets for market abuse.
Future research must focus on the following design principles for minimizing manipulation cost:
- Dynamic Liquidation Thresholds: Adjusting collateral requirements based on market volatility and oracle latency, ensuring that positions cannot be easily liquidated during periods of high manipulation risk.
- Decentralized Price Aggregation: Moving beyond simple AMM price feeds to utilize decentralized oracle networks that aggregate data from multiple exchanges and sources.
- Off-Chain Computation for Price Discovery: Using Layer 2 solutions or off-chain computation to calculate option settlement prices, reducing the on-chain attack surface and increasing data frequency.
The ultimate goal is to create options protocols where the cost of manipulation is so high that it renders any attack economically unviable, ensuring the integrity and stability of the underlying financial system.
Glossary

Defi Cost of Capital

Data Manipulation Resistance

L1 Data Availability Cost

Volatility Skew
Oracle Networks

Manipulation Cost

Gas Cost Internalization
Collateral Asset Manipulation
Flash Loan