Essence
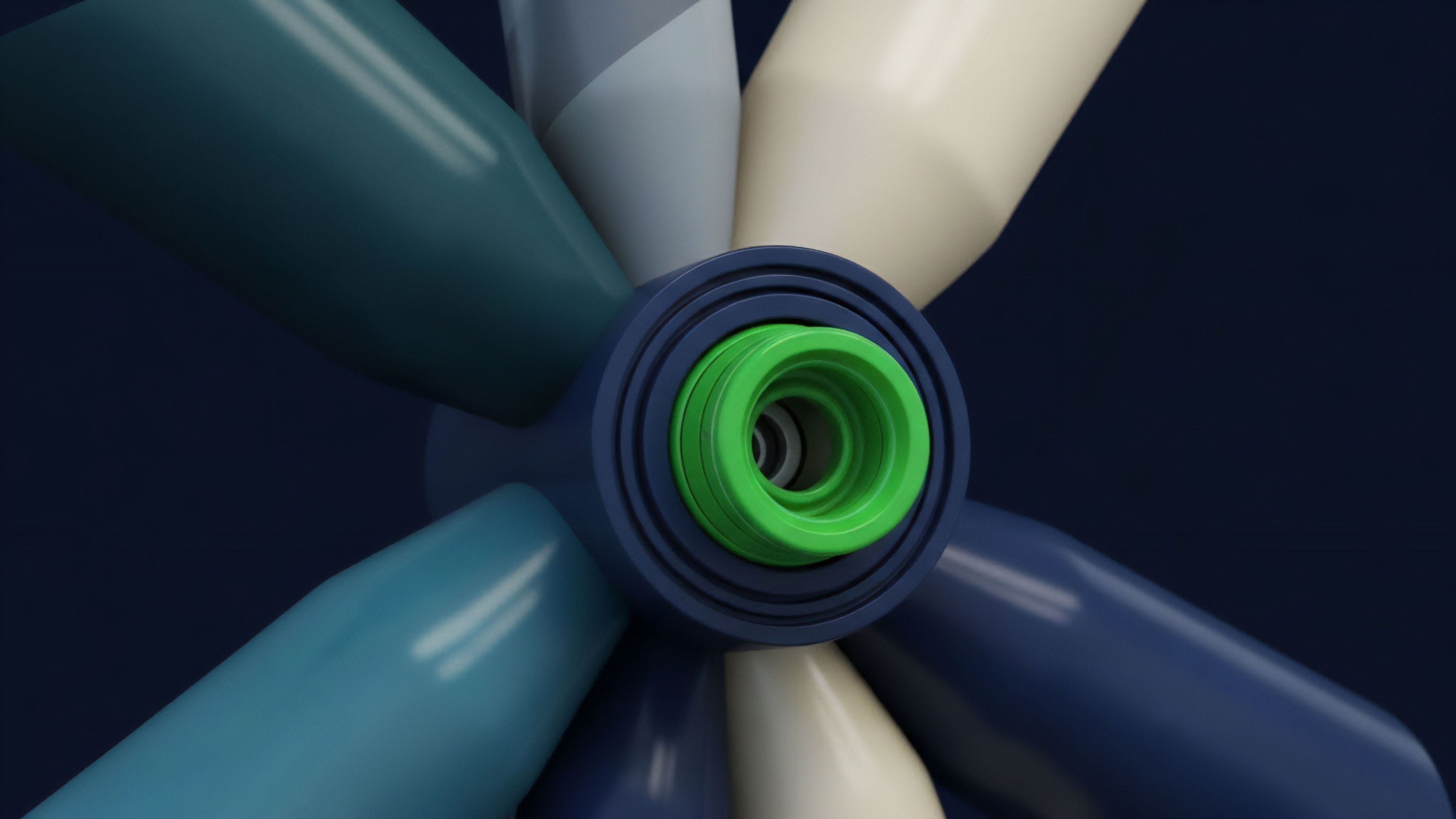
Order Flow Verification functions as the structural guarantee that trade instructions remain immutable and untampered from the moment of signature to the point of on-chain settlement. This mechanism removes the reliance on intermediary honesty by replacing reputational trust with mathematical certainty. In the adversarial environment of decentralized finance, the ability to confirm that an order was executed according to its original parameters without being front-run or sandwiched by a block builder determines the actual realized yield of any derivative position.
Cryptographic proofs of intent ensure that the execution price matches the signed parameters without intermediary interference.
The operational reality of Order Flow Verification centers on the protection of user intent. Market participants broadcast signed messages that define specific constraints ⎊ price limits, slippage tolerances, and expiration timestamps. Verification protocols ensure these constraints are respected by the sequencers and builders who control the ordering of transactions.
Without this layer, the value leaked to MEV (Maximal Extractable Value) agents represents a direct tax on liquidity providers and traders, eroding the capital efficiency of the entire market. Execution transparency provides the necessary data for sophisticated participants to audit the performance of their routing logic. By verifying the path an order takes through various liquidity pools, Order Flow Verification exposes hidden latencies and price manipulations that often occur in opaque execution environments.
This shift toward verifiable execution allows for the creation of more robust financial instruments where the risk of execution failure is quantified and mitigated through code rather than legal contracts.

Origin
The necessity for Order Flow Verification emerged from the predatory conditions found in the early Ethereum mempool, often described as a dark forest. As decentralized exchanges gained volume, automated bots began exploiting the transparency of pending transactions to execute front-running attacks. This systemic leakage forced a transition from public broadcast models to more sophisticated, private communication channels between traders and block producers.
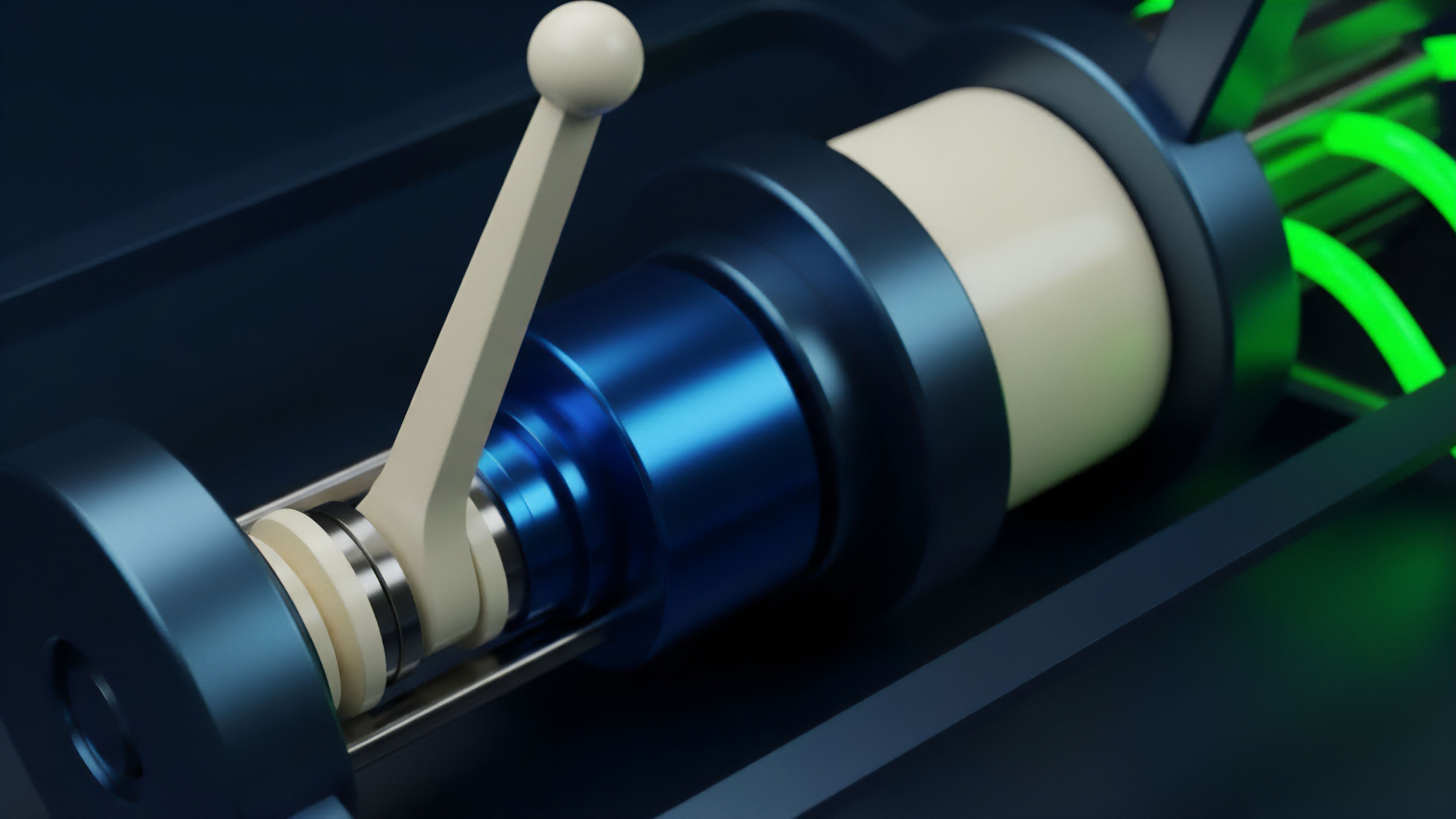
Flashbots introduced the first major attempt at stabilizing this environment through the creation of a sidecar auction mechanism. This allowed traders to send transactions directly to miners, bypassing the public mempool and reducing the risk of being targeted by arbitrageurs. This development marked the beginning of a move toward structured order flow, where the path of a transaction is carefully managed to preserve value.
Verification logic shifts the burden of honesty from the participant to the mathematical constraints of the protocol.
Traditional finance has long utilized similar concepts in the form of dark pools and direct market access, but these systems rely on regulatory oversight and legal recourse. In the digital asset space, the lack of a central authority necessitated a technical solution. The evolution of Proposer-Builder Separation (PBS) further refined this by decoupling the entities that select transactions from those that construct the actual blocks, creating a competitive market for order flow that requires rigorous verification to maintain integrity.
Theory
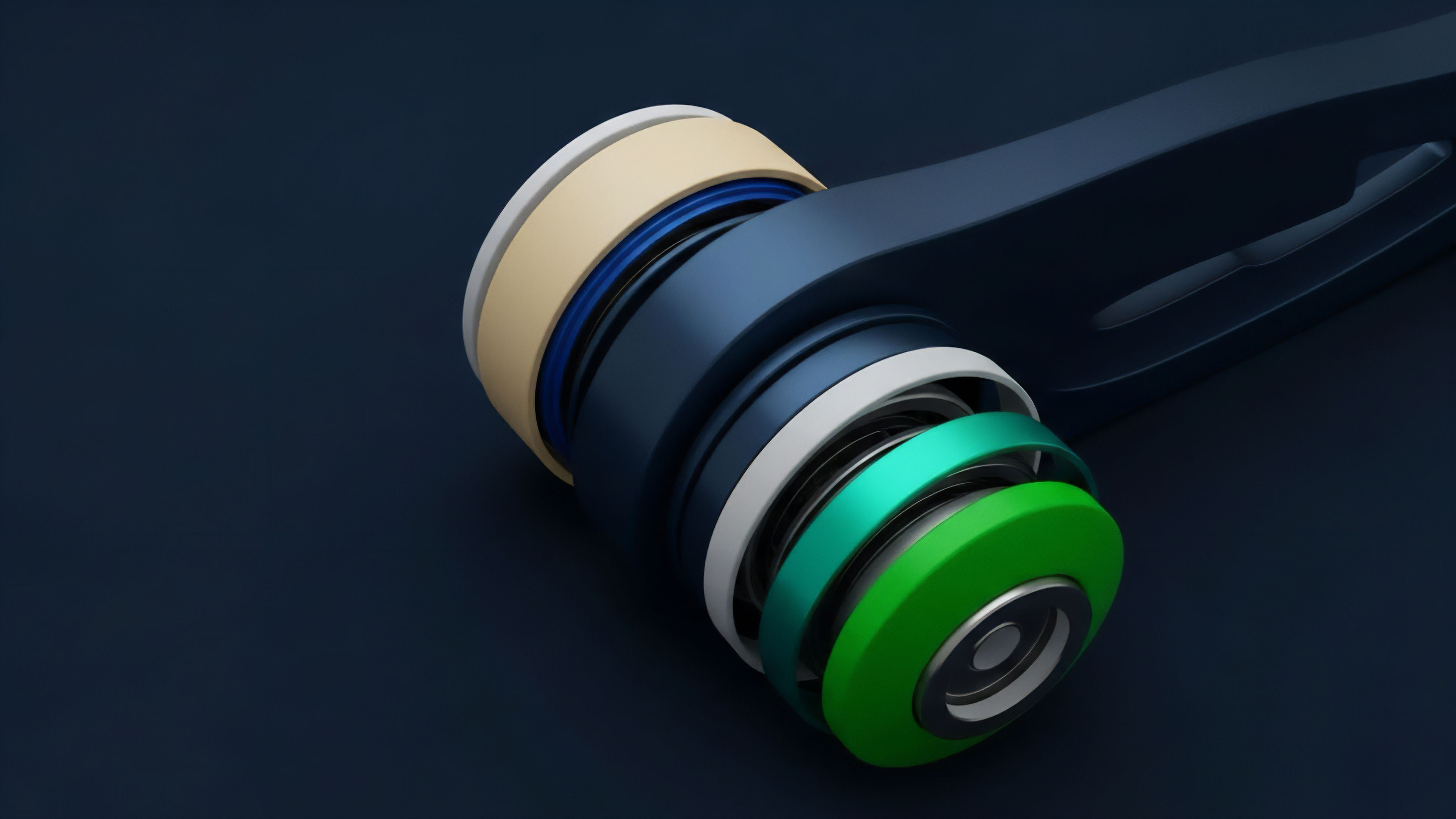
The mathematical foundation of Order Flow Verification rests on commitment schemes and zero-knowledge proofs.
A trader commits to an action without revealing the full details to the entire network until the moment of execution. This prevents adversarial actors from using the information to position themselves ahead of the trade. The verification process then confirms that the revealed action matches the original commitment, ensuring the integrity of the transaction lifecycle.

Verification Architectures
Different models of verification offer varying levels of security and speed. The choice of architecture influences the latency and the degree of decentralization within the execution path.
| Model Type | Verification Mechanism | Trust Assumption |
| Private RPC | Relay Filtering | Relay Neutrality |
| ZK-Rollup | Validity Proofs | Mathematical Correctness |
| Optimistic | Fraud Proofs | Economic Rationality |
| PBS Circuits | Commit-Reveal | Proposer Honesty |

Structural Requirements for Secure Routing
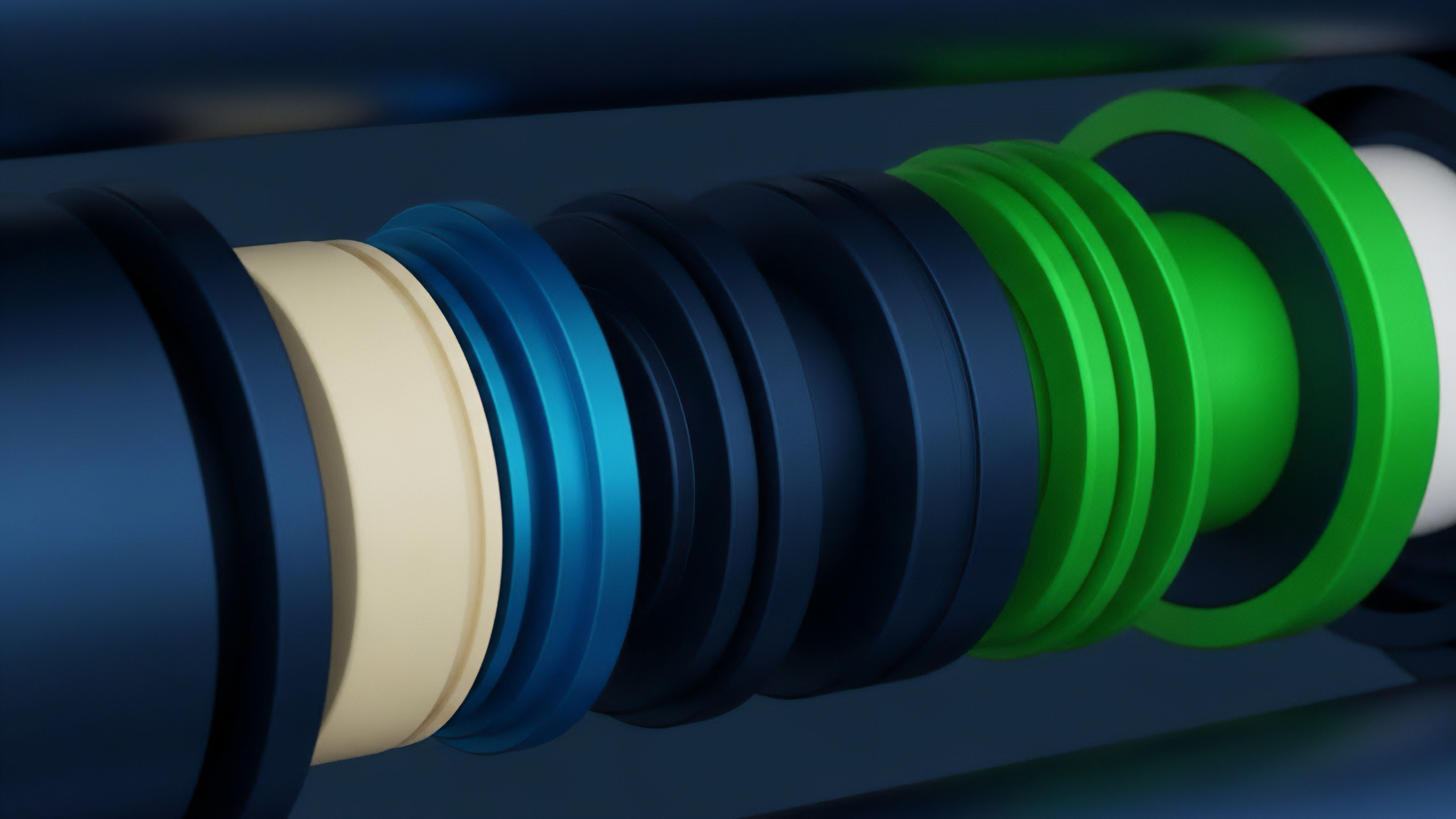
- Signature Integrity ensures that the original intent of the trader cannot be altered by any intermediary during the transmission phase.
- State Consistency guarantees that the execution environment at the time of settlement matches the conditions under which the order was validated.
- Temporal Ordering prevents the reordering of transactions within a block to extract value through sandwich attacks or other forms of manipulation.
- Execution Atomicity requires that either the entire order is filled according to the verified parameters or the transaction fails completely, leaving no partial or unfavorable fills.
Transparent order routing eliminates the hidden costs associated with toxic flow and adversarial block building.
The interaction between Order Flow Verification and liquidity provision is a feedback loop. When order flow is verified as non-toxic ⎊ meaning it does not originate from informed arbitrageurs looking to exploit stale prices ⎊ market makers can offer tighter spreads. This reduces the cost of trading for all participants and increases the overall depth of the market.
Verification acts as a filter, separating legitimate hedging and speculative activity from predatory latency games.
Approach
Current implementation of Order Flow Verification involves the use of specialized relays and private execution endpoints. Traders route their transactions through services like Flashbots Protect or similar private RPCs, which promise not to broadcast the transaction to the public mempool. These services verify the order against a set of rules before passing it to a network of builders who compete to include the transaction in a block.

Risk Parameters in Execution
Evaluating the effectiveness of a verification system requires an analysis of specific risk vectors and the corresponding mitigation strategies employed by the protocol.
| Attack Vector | Description | Verification Solution |
| Front-running | Inserting a transaction before a target order | Mempool Obfuscation |
| Sandwiching | Surrounding a trade with buy and sell orders | Slippage Bound Verification |
| Censorship | Excluding specific orders from block inclusion | Inclusion Proofs |
| Inventory Risk | Market makers being forced into unfavorable positions | Toxic Flow Identification |
The use of Order Flow Verification in decentralized options markets is particularly vital due to the complexity of multi-leg positions. Verifying that all legs of a spread are executed simultaneously at the desired prices is a significant technical challenge. Protocols now utilize atomic bundles, where multiple transactions are linked together and verified as a single unit.
If any part of the bundle fails the verification check, the entire set is discarded, protecting the trader from directional exposure.

Evolution
The transition from simple gas-price auctions to complex, multi-dimensional execution environments has redefined the role of Order Flow Verification. Initially, verification was a binary state ⎊ either a transaction was in the mempool or it was not. Today, it involves a sophisticated analysis of the entire block construction process.
The rise of MEV-Boost and similar architectures has created a marketplace where verification happens at every step of the supply chain, from the user to the searcher, the builder, and finally the proposer. This evolution has been driven by the increasing sophistication of adversarial actors. As bots became better at identifying profitable opportunities, the defense mechanisms had to become more robust.
The introduction of encrypted mempools represents a significant shift in this battle, where the contents of a transaction are hidden even from the block builders until the block is finalized. This ensures that Order Flow Verification is the only way to interact with the network securely. The shift toward app-specific chains and rollups has also influenced how verification is handled.
Each environment has its own rules for order ordering and execution, requiring a modular approach to verification. Instead of a one-size-fits-all solution, we now see specialized verification circuits tailored to the specific needs of different financial instruments, such as perpetual futures or complex option strategies.

Horizon
The future of Order Flow Verification lies in the expansion of cross-chain execution and the integration of artificial intelligence in block building. As liquidity becomes increasingly fragmented across multiple layers and chains, the ability to verify order flow across these boundaries will be the defining feature of successful derivative protocols.
Cross-chain intents will require sophisticated verification proofs that can be validated on the destination chain without introducing significant latency.

Future Requirements for Institutional Adoption
- Privacy Preserving Proofs will allow institutions to verify their execution quality without revealing their underlying strategies or positions to the broader market.
- Regulatory Compliance Modules must be integrated into the verification layer to ensure that all participants meet specific jurisdictional requirements without compromising decentralization.
- Standardized Execution Metrics will provide a common language for evaluating the performance of different verification providers, fostering competition and transparency.
- Automated Risk Mitigation will use real-time verification data to adjust trading parameters or pause execution during periods of extreme volatility or suspected market manipulation.
The ultimate goal is a state of total transparency where every participant can verify the fairness of the market in real-time. This does not mean that all data is public, but rather that the proofs of correct execution are available to those who need them. In this future, Order Flow Verification becomes the invisible infrastructure that supports a global, permissionless financial system, ensuring that value is preserved for those who create it rather than those who simply intercept it.

Glossary

Maximal Extractable Value

Risk Management Circuits

Price Discovery
Protocol Physics

Zero Knowledge Proofs

On-Chain Privacy

Smart Contract Security

Network Consensus

Latency Optimization






