Essence
Oracle manipulation risk represents the fundamental vulnerability of decentralized financial derivatives to external data corruption. A derivative contract’s value and settlement logic are contingent on an external price feed ⎊ the oracle ⎊ that bridges off-chain market reality with on-chain smart contract execution. The risk materializes when an attacker successfully feeds false or manipulated data to this oracle, causing the smart contract to execute a financial action (such as liquidation, settlement, or collateral valuation) based on incorrect information.
The core challenge lies in the fact that a blockchain’s deterministic nature makes it inherently incapable of verifying real-world information without a trusted external input.
In the context of crypto options, this risk is particularly acute because options contracts are highly sensitive to price changes and volatility. A flash loan attack can temporarily spike or crash the price feed, triggering premature liquidations or allowing an attacker to purchase options at an artificially low price before the true market price is restored. The integrity of the options protocol hinges entirely on the integrity of its data source.
When the data source is compromised, the protocol’s financial logic collapses, leading to a loss of collateral for honest users and a gain for the manipulator.
Oracle manipulation risk is the single point of failure where a decentralized financial contract’s integrity meets the fallibility of external data feeds.
Origin
The concept of oracle risk is not new to finance, but its manifestation in decentralized systems presents a unique challenge. In traditional finance, price feeds are provided by trusted, regulated intermediaries like Bloomberg or Reuters. These feeds are considered authoritative due to legal frameworks and the high cost of data manipulation.
The decentralized finance space, however, cannot rely on these centralized entities without reintroducing counterparty risk. The “oracle problem” was therefore born from the necessity of finding a trustless, cryptographic solution to verify off-chain data on-chain.
Early solutions relied on simple, on-chain price discovery mechanisms (like automated market makers or AMMs), but these proved highly susceptible to front-running and manipulation. The introduction of external oracle networks, such as Chainlink, sought to solve this by decentralizing the data source itself, using a network of independent nodes to aggregate data from multiple exchanges. While this approach significantly raised the cost of manipulation, it did not eliminate the risk entirely.
The origin of the current risk landscape stems from the transition from single-source price feeds to multi-source aggregation, creating new attack vectors where an attacker must now compromise a quorum of data providers rather than a single source.

Theory
The theoretical underpinnings of oracle manipulation risk are rooted in game theory and market microstructure. An attacker’s strategy often involves exploiting a mismatch between the oracle’s price update frequency and the market’s real-time price action, particularly in low-liquidity markets. The primary attack vectors are flash loan manipulation and time-weighted average price (TWAP) exploits.

Flash Loan Manipulation and Liquidity Gaps
Flash loans allow an attacker to borrow large amounts of assets without collateral, execute a sequence of transactions, and repay the loan all within a single transaction block. This creates a powerful mechanism for manipulation when combined with low-liquidity decentralized exchanges (DEXs) used by an oracle. The attack sequence typically follows this pattern:
- Borrowing: The attacker obtains a large flash loan of the asset to be manipulated.
- Price Manipulation: The attacker uses the borrowed assets to execute large buy or sell orders on a low-liquidity DEX that serves as a data source for the target options protocol’s oracle. This artificially inflates or deflates the asset’s price.
- Oracle Update: The oracle queries the manipulated DEX price and updates the options protocol’s smart contract with the false data.
- Exploitation: The attacker executes a trade against the options protocol at the manipulated price, either by triggering a favorable liquidation or by opening a position at an incorrect valuation.
- Repayment: The attacker repays the flash loan, having profited from the price discrepancy, and the market price on the DEX returns to normal.
This attack vector demonstrates that the vulnerability is not a flaw in the oracle code itself, but a flaw in the economic model that links the oracle to a specific liquidity source. The attack’s success depends on the cost of manipulation being lower than the profit derived from exploiting the target protocol. This cost is determined by the depth of liquidity in the source market.

TWAP Vs. Instant Price Feeds
To mitigate flash loan manipulation, many protocols moved away from instant price feeds (IPFs) toward time-weighted average price (TWAP) feeds. A TWAP calculates the average price of an asset over a specified time window, making it significantly more expensive for an attacker to manipulate the price for a sustained period. However, this introduces a new risk: latency.
A TWAP feed, by design, lags behind real-time market movements. This creates a different set of opportunities for manipulation, particularly for sophisticated actors who can front-run the oracle’s update schedule. An attacker can anticipate the TWAP update and execute trades against the protocol based on the known, delayed price.
This is a trade-off between security against flash loans and accuracy during high-volatility events.
| Feature | Instant Price Feed (IPF) | Time-Weighted Average Price (TWAP) |
|---|---|---|
| Latency | Low (near real-time) | High (delayed by time window) |
| Manipulation Cost | Low (susceptible to flash loans) | High (requires sustained capital) |
| Use Case | Real-time trading, low-value assets | High-value collateral, derivatives settlement |
| Risk Profile | Sudden price spikes, flash loan attacks | Front-running, volatility-induced lag |
The selection between an instant price feed and a time-weighted average price feed is a design trade-off between mitigating flash loan attacks and accepting front-running risk during periods of high market volatility.

Approach
The current approach to mitigating oracle manipulation risk involves a combination of technical and economic strategies. The core principle is to make the cost of manipulation prohibitively high by diversifying data sources and implementing robust economic incentives.

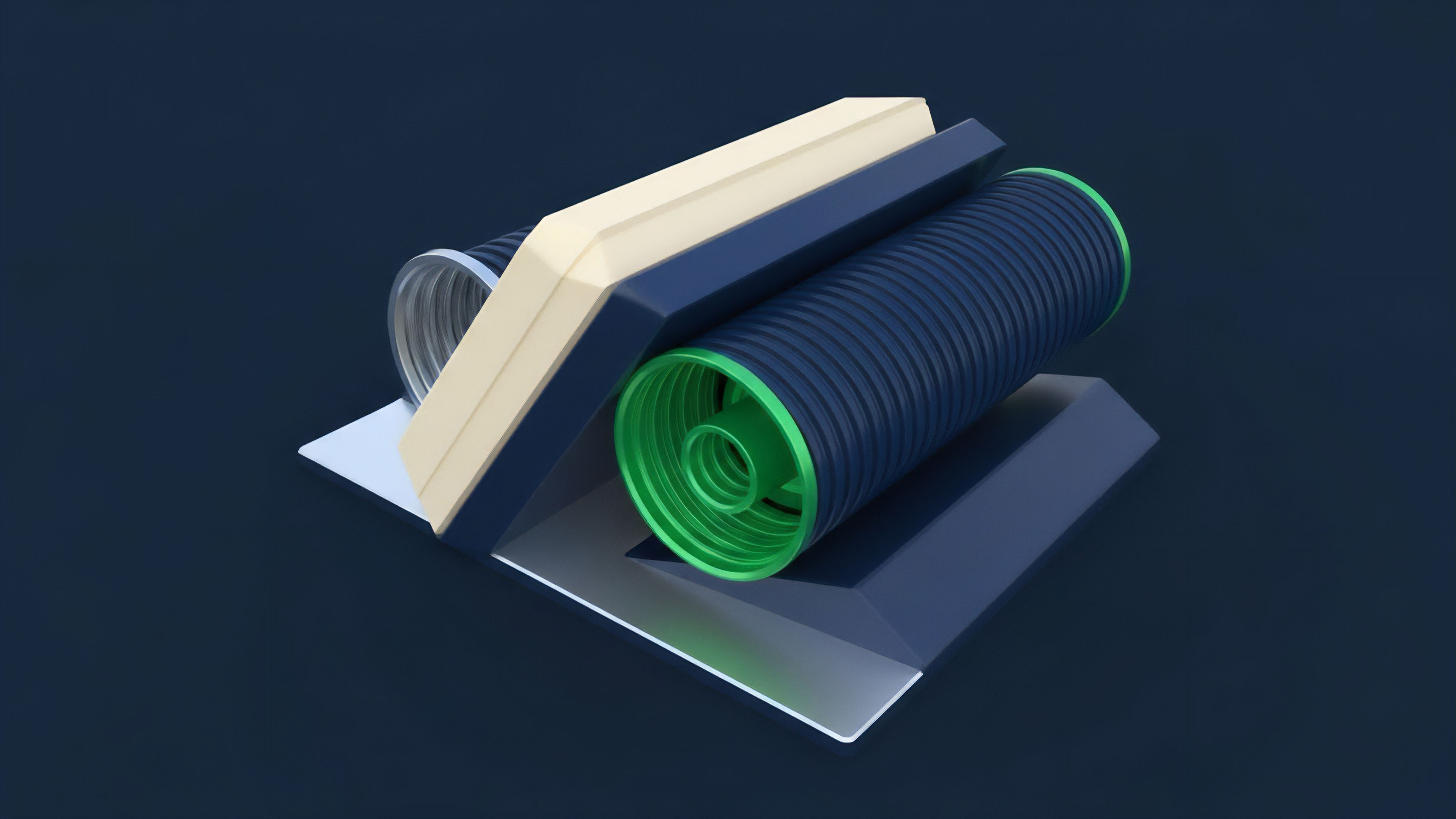
Data Aggregation and Decentralization
The most widely adopted approach involves data aggregation from multiple independent sources. Protocols like Chainlink operate by having a decentralized network of nodes gather data from various exchanges. The final price feed is calculated by taking a median or average of these inputs.
This design increases the capital required for manipulation; an attacker must now successfully manipulate a significant portion of the data sources simultaneously, rather than just one. This approach shifts the security model from a single point of failure to a game-theoretic challenge where the cost of attacking the system outweighs the potential profit.
Decentralized Data Markets and Economic Incentives
Another approach involves creating decentralized data markets where data providers are financially incentivized to provide accurate information and penalized for providing inaccurate information. Protocols like Pyth Network use a pull-based model where data providers stake collateral and receive rewards for timely updates. If a data provider submits data that deviates significantly from the median price, their stake can be slashed.
This creates an economic incentive structure where data providers act as market participants, ensuring data accuracy through a system of financial rewards and penalties. The challenge here is determining the correct threshold for slashing and ensuring the penalty is greater than the potential gain from collusion.

Volatility and Skew Management
In the context of options, a new set of challenges arises when dealing with volatility data. Options pricing models rely on volatility as a key input (the Black-Scholes model, for instance). An attacker could manipulate the price feed not just to trigger a liquidation, but to distort the calculation of implied volatility, allowing them to buy or sell options at mispriced values.
The solution here requires a more sophisticated approach than a simple spot price feed. It necessitates the creation of specialized volatility oracles that aggregate data on historical volatility, implied volatility skew, and other market parameters to provide a more robust input for options pricing models. This moves the focus from price accuracy to volatility accuracy.

Evolution
The evolution of oracle manipulation has mirrored the increasing complexity of decentralized finance. Early attacks focused on simple price manipulation on low-liquidity AMMs. As protocols adapted with TWAP feeds and aggregated data sources, attackers shifted their focus to more sophisticated vectors, including multi-protocol exploits and manipulating the underlying asset’s price in a way that affects multiple protocols simultaneously.
The risk is no longer isolated to a single contract; it is now systemic across interconnected protocols.

The Rise of Volatility Manipulation
A significant shift in the risk landscape is the transition from manipulating spot prices to manipulating volatility. Options pricing models are highly sensitive to implied volatility. An attacker can use a series of trades to artificially flatten or steepen the volatility skew ⎊ the relationship between implied volatility and strike price ⎊ to misprice options.
This attack vector is particularly difficult to detect because it does not require a large, sudden price spike; it relies on subtle changes in market dynamics that affect the calculation of option premiums. This new type of manipulation targets the core financial models of derivatives protocols rather than the simple price feed.
Novel Conjecture
The primary risk to decentralized options protocols in the coming years will not be the manipulation of spot prices, but the manipulation of the volatility surface itself. As protocols adopt more sophisticated pricing models, attackers will shift from targeting the single price point to targeting the inputs that determine the entire options chain. This suggests a future where a successful attack involves distorting the calculation of implied volatility skew, leading to mispriced options that allow an attacker to profit from a statistically significant edge across the entire term structure, rather than from a single liquidation event.
As DeFi matures, attackers will increasingly target the manipulation of implied volatility surfaces, rather than simple spot prices, to exploit mispriced options contracts across entire term structures.

Horizon
The future of oracle security will be defined by the integration of zero-knowledge proofs (ZKPs) and the development of specialized oracles that provide richer data sets. ZKPs allow a data provider to prove that they have submitted a specific piece of data without revealing the data itself, ensuring privacy and integrity. The development of specialized oracles for specific financial instruments is also essential.
A single price feed cannot adequately secure a complex derivatives protocol. The future requires oracles that provide specific data points, such as volatility surfaces, interest rate curves, and real-time risk parameters.

The Volatility Oracle
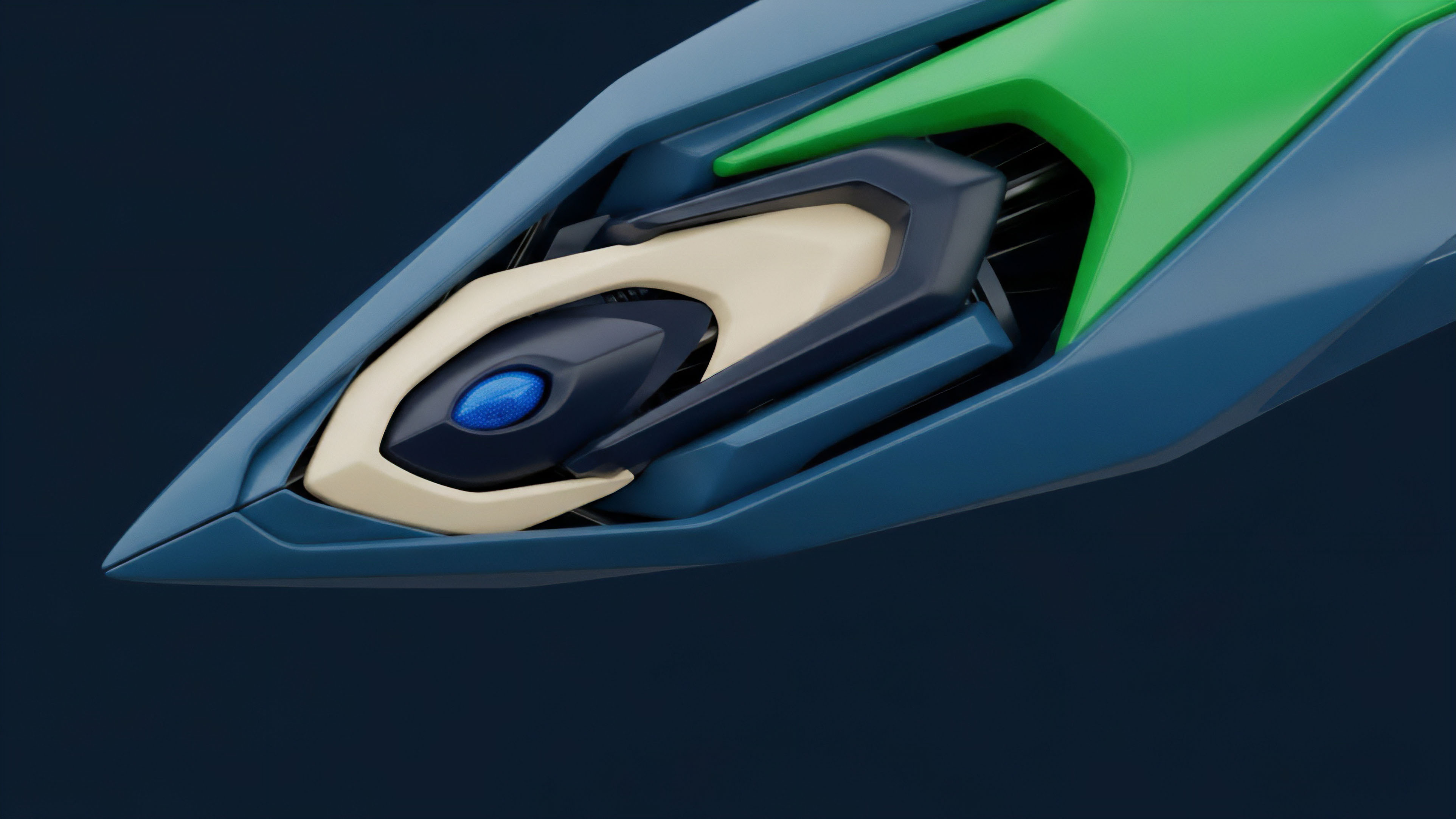
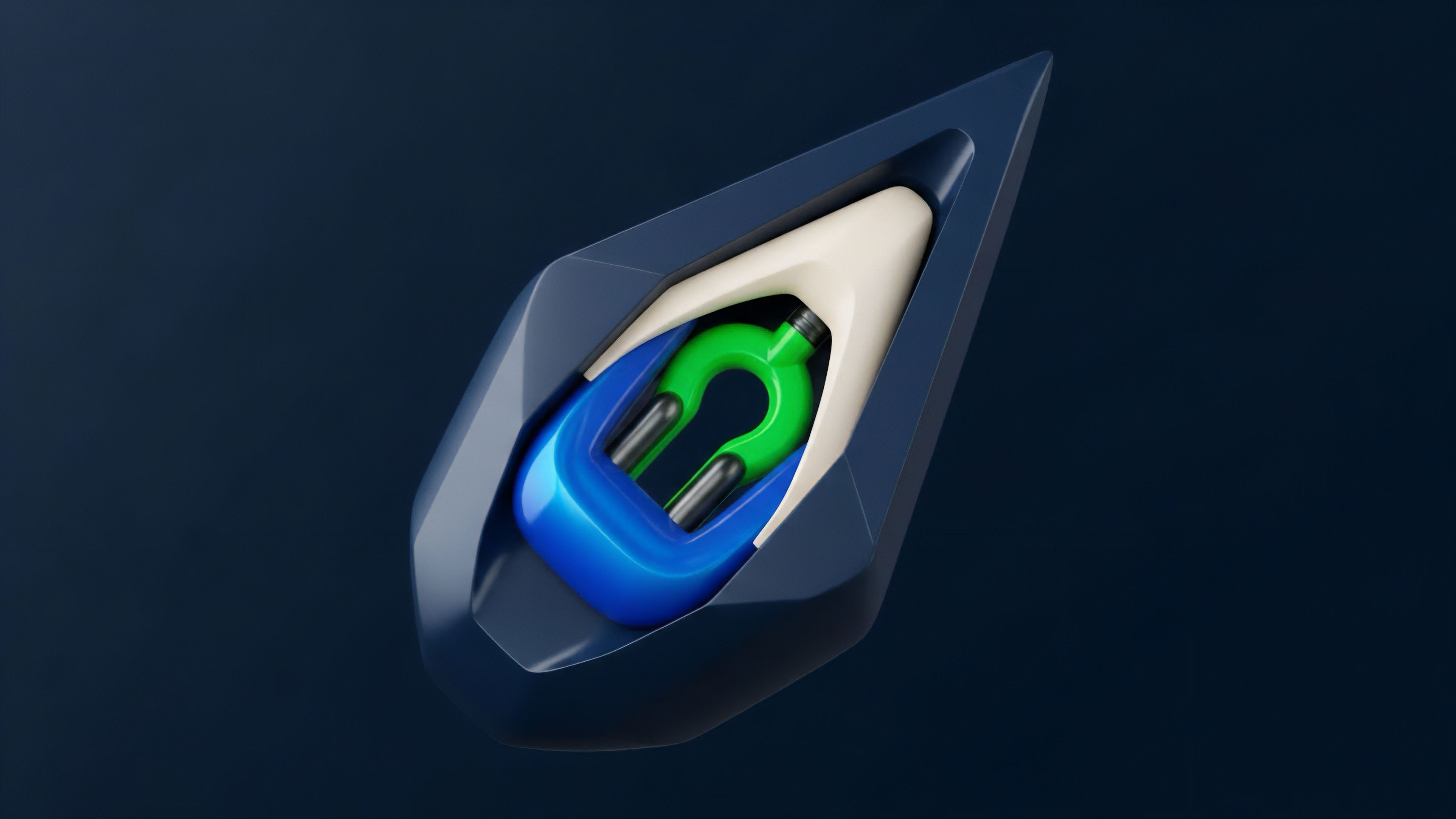
To address the evolving threat landscape, we must design specialized “Volatility Oracles” that move beyond simple spot price aggregation. These oracles would be responsible for calculating and verifying implied volatility skew across different strike prices and maturities. This requires a new design that aggregates data from options market makers, calculates the skew, and verifies the accuracy of the calculation on-chain.
This instrument of agency would protect options protocols from the next generation of attacks by ensuring the integrity of the most critical input to options pricing models.
- Data Source Aggregation: The oracle aggregates real-time options data (bids, asks, volumes) from multiple decentralized options exchanges.
- Volatility Surface Calculation: It calculates a standardized volatility surface, including implied volatility skew and term structure, using established quantitative models.
- On-Chain Verification: The calculation is verified on-chain using a consensus mechanism where nodes attest to the accuracy of the inputs and the calculation itself.
- Data Delivery: The oracle delivers a verified volatility surface, rather than a single price, to the options protocol, allowing for accurate pricing of options contracts.
This approach shifts the focus from price accuracy to risk parameter accuracy, creating a more robust foundation for decentralized options markets. The implementation of such a system requires significant collaboration between quantitative finance experts and blockchain engineers to ensure both mathematical rigor and cryptographic security.
Glossary
Specialized Oracle Feeds

Economic Health Oracle

Options Greeks in Manipulation

Short-Term Price Manipulation

Asset Manipulation

Options Manipulation
On Chain Carry Oracle

Off-Chain Manipulation

Protocol Manipulation Thresholds