
Essence
An Option Contract represents a formalized, programmable agreement granting the holder the right, though not the obligation, to execute a transaction involving a specified digital asset at a predetermined price within a defined temporal window. This instrument functions as a foundational building block for risk management, allowing participants to isolate and transfer specific volatility exposures.
An option contract functions as a programmable financial instrument that isolates price risk by decoupling the right to trade from the obligation to perform.
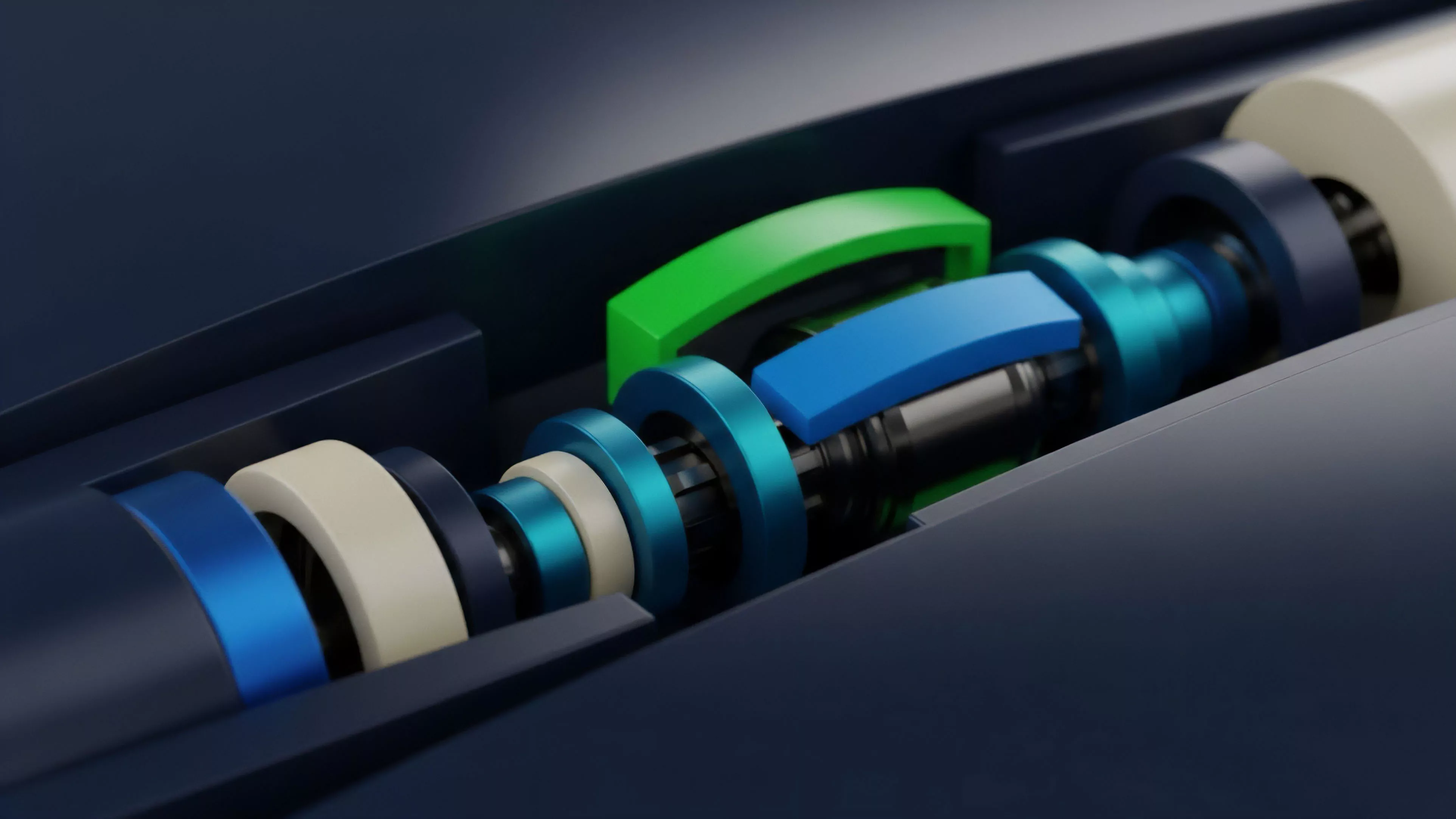
The mechanical integrity of these contracts relies upon the precise definition of parameters including the strike price, the expiration date, and the underlying asset reference. Within decentralized environments, these parameters reside in immutable code, ensuring that the contractual obligations execute automatically upon meeting the specified conditions, thereby removing reliance on centralized intermediaries to guarantee settlement.

Origin
The lineage of modern crypto option mechanics traces back to traditional financial derivatives, yet it undergoes a fundamental transformation through the adoption of smart contract architecture. Initial iterations attempted to replicate centralized exchange models on-chain, but the unique requirements of blockchain settlement ⎊ specifically the necessity for collateralization ⎊ forced a shift toward collateralized option vaults and automated market makers.
- Permissionless settlement removes the requirement for trusted clearinghouses by utilizing cryptographic proof for contract enforcement.
- On-chain margin engines dictate the capital requirements for writers, ensuring that the protocol remains solvent even during periods of extreme market stress.
- Programmable composability allows these instruments to integrate directly into broader decentralized financial protocols, creating automated hedging strategies.
This evolution represents a departure from traditional, ledger-based accounting toward a system where the contract logic serves as the ultimate arbiter of value transfer.

Theory
The pricing of these instruments utilizes mathematical models such as the Black-Scholes-Merton framework, adapted for the high-volatility, non-continuous nature of digital asset markets. The Greeks ⎊ specifically Delta, Gamma, Theta, and Vega ⎊ provide the quantitative lens through which market participants measure their exposure to price movement, acceleration, time decay, and volatility shifts.
The Greeks provide a quantitative framework for measuring sensitivity to market variables, allowing participants to hedge specific components of price risk.

Risk Sensitivity Analysis
The technical architecture of these protocols must account for the non-linear relationship between the underlying asset price and the option value. Gamma risk becomes particularly acute near the strike price, as rapid changes in Delta require constant rebalancing of hedging positions, which can exacerbate volatility in the underlying spot market.
| Greek | Primary Sensitivity | Systemic Implication |
| Delta | Underlying Asset Price | Directional exposure and hedging requirements |
| Gamma | Rate of Delta Change | Non-linear risk and hedging acceleration |
| Theta | Time Decay | Yield generation for option writers |
| Vega | Volatility Shifts | Exposure to market sentiment and uncertainty |
The mathematical rigor applied to these models is constantly tested by the adversarial nature of decentralized liquidity pools. Traders and automated agents continuously exploit discrepancies between theoretical pricing and realized market volatility.

Approach
Current implementations prioritize capital efficiency and liquidity aggregation through decentralized pools. Protocols manage risk by requiring writers to lock assets as collateral, effectively neutralizing counterparty risk at the expense of capital lock-up.
This design forces a trade-off between user accessibility and the depth of available liquidity.
Decentralized option protocols utilize collateralized vaults to replace traditional credit-based clearing, fundamentally altering the risk profile for liquidity providers.

Collateral Management Mechanisms
- Isolated Collateral ensures that the failure of one contract does not propagate through the entire protocol, protecting the solvency of other participants.
- Dynamic Margin Requirements adjust based on the volatility of the underlying asset, preventing under-collateralization during rapid price movements.
- Automated Liquidation triggers when the value of the collateral falls below a predefined threshold, maintaining the integrity of the contract settlement.
The shift toward decentralized limit order books for options indicates a maturation of the space, moving away from simple automated market makers toward more sophisticated price discovery mechanisms that mimic high-frequency trading environments.

Evolution
The transition from simple, monolithic protocols to modular derivative architectures defines the current stage of market development. Early designs struggled with fragmented liquidity and high transaction costs, whereas newer protocols leverage Layer 2 scaling solutions to reduce latency and gas expenses, enabling more frequent hedging activity. The interaction between on-chain governance and protocol parameters has become the primary site of innovation. Communities now vote on the acceptable risk parameters for collateral, effectively crowdsourcing the underwriting process that was once the exclusive domain of institutional risk managers.
Horizon
Future developments will likely focus on cross-chain settlement and the integration of oracle-agnostic pricing to reduce dependency on centralized data feeds. As protocols achieve greater maturity, the emergence of institutional-grade derivatives will rely on the ability of decentralized systems to handle complex multi-leg strategies without incurring prohibitive costs or security risks. The path forward involves bridging the gap between decentralized transparency and the performance requirements of global finance. This necessitates the creation of protocols capable of maintaining high-throughput execution while ensuring that the underlying cryptographic proofs remain robust against evolving computational threats.
