
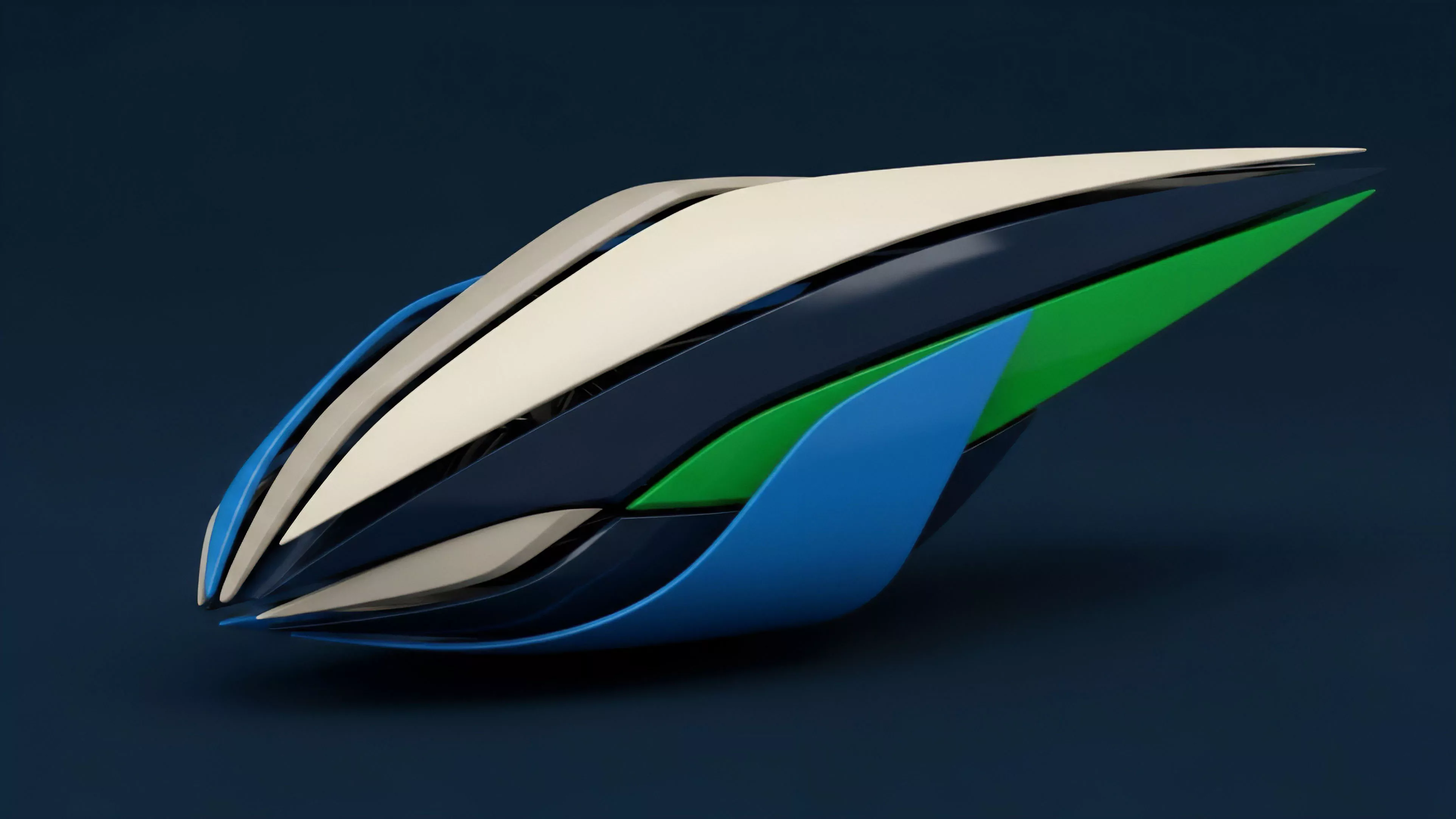
Essence
Network Security Engineering serves as the structural bedrock for decentralized derivative protocols. It encompasses the design, implementation, and maintenance of cryptographic defenses that protect order flow, asset custody, and protocol state against adversarial actors. Without these mechanisms, the execution of complex financial instruments remains exposed to systemic failure.
Network Security Engineering establishes the defensive architecture necessary to preserve the integrity and solvency of decentralized derivative markets.
The discipline focuses on hardening the attack surface of automated market makers, clearing engines, and settlement layers. By leveraging robust consensus mechanisms and secure smart contract design, this engineering field transforms volatile, permissionless environments into functional, predictable financial venues. It prioritizes the mitigation of front-running, sandwich attacks, and oracle manipulation through technical rigor.

Origin
The emergence of Network Security Engineering tracks directly to the vulnerabilities exposed in early decentralized finance experiments.
Initial protocols often relied on naive implementation patterns, assuming that code transparency equated to inherent security. Adversarial actors exploited these assumptions, draining liquidity pools and manipulating pricing feeds, which necessitated a shift toward rigorous defensive design.
- Early Vulnerability Analysis: Identified systemic flaws in liquidity provisioning mechanisms that allowed for price slippage exploitation.
- Cryptographic Primitive Development: Established foundational standards for multi-party computation and zero-knowledge proofs to enhance private execution.
- Protocol Hardening: Shifted from rapid, experimental iteration toward formalized verification processes for smart contract architecture.
This field drew heavily from traditional computer science, cryptography, and game theory, adapting these established domains to the high-stakes, adversarial environment of programmable money. It recognizes that in a system where code dictates financial outcomes, the security of that code determines the economic viability of the entire protocol.
Theory
The theoretical framework of Network Security Engineering relies on the concept of protocol physics, where the rules of the system define the boundaries of participant behavior. Quantitative finance models are mapped onto these physical constraints, ensuring that derivative pricing remains accurate even under high volatility or network congestion.
| Concept | Mechanism | Risk Mitigation |
| State Consistency | Formal Verification | Logic Exploits |
| Oracle Integrity | Decentralized Aggregation | Price Manipulation |
| Latency Arbitrage | Batch Auctions | Front-running |
The mathematical modeling of risk sensitivities ⎊ commonly referred to as Greeks ⎊ requires high-frequency, secure data feeds. Any discrepancy between the oracle price and the true market price creates an arbitrage opportunity for adversarial agents, leading to rapid capital depletion. Thus, engineering the security of these feeds is as vital as the underlying derivative math.
Rigorous mathematical modeling of protocol state transitions prevents the exploitation of inherent system latency and oracle synchronization errors.
Adversarial agents constantly probe these systems for weak points in the state transition logic. A small deviation in how a margin engine calculates collateral requirements can lead to systemic contagion during market stress. Security engineers must therefore model the entire lifecycle of a trade as a continuous, adversarial game, where every state update is a potential point of failure.

Approach
Modern practitioners of Network Security Engineering employ a multi-layered defense strategy, prioritizing proactive auditing and automated monitoring over reactive patching.
The approach involves integrating security directly into the development lifecycle, treating the protocol as an evolving entity under constant siege.
- Formal Methods Application: Utilizing mathematical proofs to verify that smart contract code adheres to intended economic specifications.
- Adversarial Simulation: Running continuous stress tests against the protocol to identify potential liquidation threshold failures.
- Real-time Surveillance: Deploying automated agents to monitor on-chain transaction flow for anomalies indicative of exploit attempts.
This methodology requires a deep synthesis of quantitative finance and distributed systems architecture. Engineers analyze the trade-offs between protocol throughput and security guarantees, recognizing that increased decentralization often introduces new, complex attack vectors. The goal is to maximize capital efficiency while maintaining a hardened defensive perimeter that resists both individual exploits and broader systemic contagion.

Evolution
The field has moved from simple bug hunting toward the development of modular, resilient infrastructure.
Early systems were monolithic, meaning a single flaw in the smart contract code could compromise the entire derivative platform. Current architectural trends favor a separation of concerns, where custody, execution, and clearing are handled by distinct, audited components.
The evolution of defensive architecture shifts from monolithic codebases to modular, verifiable components that isolate systemic risk.
This structural shift mirrors the evolution of traditional finance, albeit with significantly faster feedback loops and higher levels of transparency. The industry now prioritizes interoperability with standardized security libraries, reducing the reliance on custom, untested implementations. As market participants demand higher levels of leverage and complexity, the burden on Network Security Engineering to maintain stability increases, driving the adoption of more sophisticated, hardware-backed security modules.

Horizon
Future developments in Network Security Engineering will center on the integration of hardware-level security and advanced cryptographic proofs.
As decentralized derivative markets mature, the focus will shift from preventing basic code exploits to securing the integrity of complex, multi-chain settlement processes.
| Future Trend | Strategic Implication |
| Hardware Security Modules | Enhanced Key Custody |
| Zero Knowledge Scaling | Privacy Preserving Settlement |
| Autonomous Risk Engines | Dynamic Collateral Adjustment |
The ability to prove the correctness of a financial state without revealing sensitive participant data will redefine market microstructure. This transition will require a new class of security engineer who understands the delicate balance between privacy, speed, and auditability. The resilience of the global financial system will eventually depend on these decentralized security foundations, marking the transition from experimental finance to institutional-grade digital infrastructure. Is the inherent complexity of decentralized financial systems reaching a threshold where the cost of total security verification outweighs the potential gains of protocol innovation?
