
Essence
Mobile Verification functions as the cryptographic bridge between decentralized financial protocols and the verified identity of a physical user. It operates by binding a specific, non-transferable identifier ⎊ often linked to a mobile device’s hardware security module ⎊ to a blockchain-based wallet address. This mechanism provides the necessary assurance for protocols to execute under strict regulatory mandates, such as Know Your Customer and Anti-Money Laundering compliance, without compromising the underlying pseudonymity of the network.
Mobile Verification establishes a verifiable link between a digital wallet and a physical identity using secure hardware-bound cryptographic signatures.
The architectural significance of Mobile Verification lies in its ability to mitigate the risks associated with Sybil attacks and automated bot activity within high-frequency trading environments. By requiring proof of personhood via a mobile device, decentralized exchanges can enforce unique user limits, manage tiered access to liquidity pools, and implement sophisticated risk management frameworks that depend on verified participant behavior rather than anonymous, address-based interactions.

Origin
The necessity for Mobile Verification emerged from the systemic friction between decentralized, permissionless protocols and the rigid, centralized requirements of global financial regulators. Early iterations of decentralized finance favored complete anonymity, which led to significant liquidity fragmentation and susceptibility to manipulative, automated trading strategies.
As institutional capital sought to enter the digital asset space, the industry encountered a wall: the inability to satisfy jurisdictional requirements for identity confirmation without re-introducing centralized gatekeepers.
- Device Binding: Early attempts utilized simple SMS verification, which proved vulnerable to SIM-swapping and lacked the cryptographic integrity required for financial settlement.
- Hardware Attestation: The evolution toward using Trusted Execution Environments within modern mobile devices provided a robust, tamper-resistant method for verifying the presence of a unique user.
- Cryptographic Proofs: Zero-knowledge proofs were adopted to allow users to verify their identity or status without revealing sensitive personal data to the protocol itself.
This trajectory shifted the focus from purely anonymous interaction toward a model where identity is verified through decentralized, privacy-preserving cryptographic primitives. The shift acknowledges that long-term survival for decentralized derivatives requires a hybrid approach: maintaining the efficiency of blockchain-based settlement while respecting the legal and risk-management boundaries of the broader financial system.
Theory
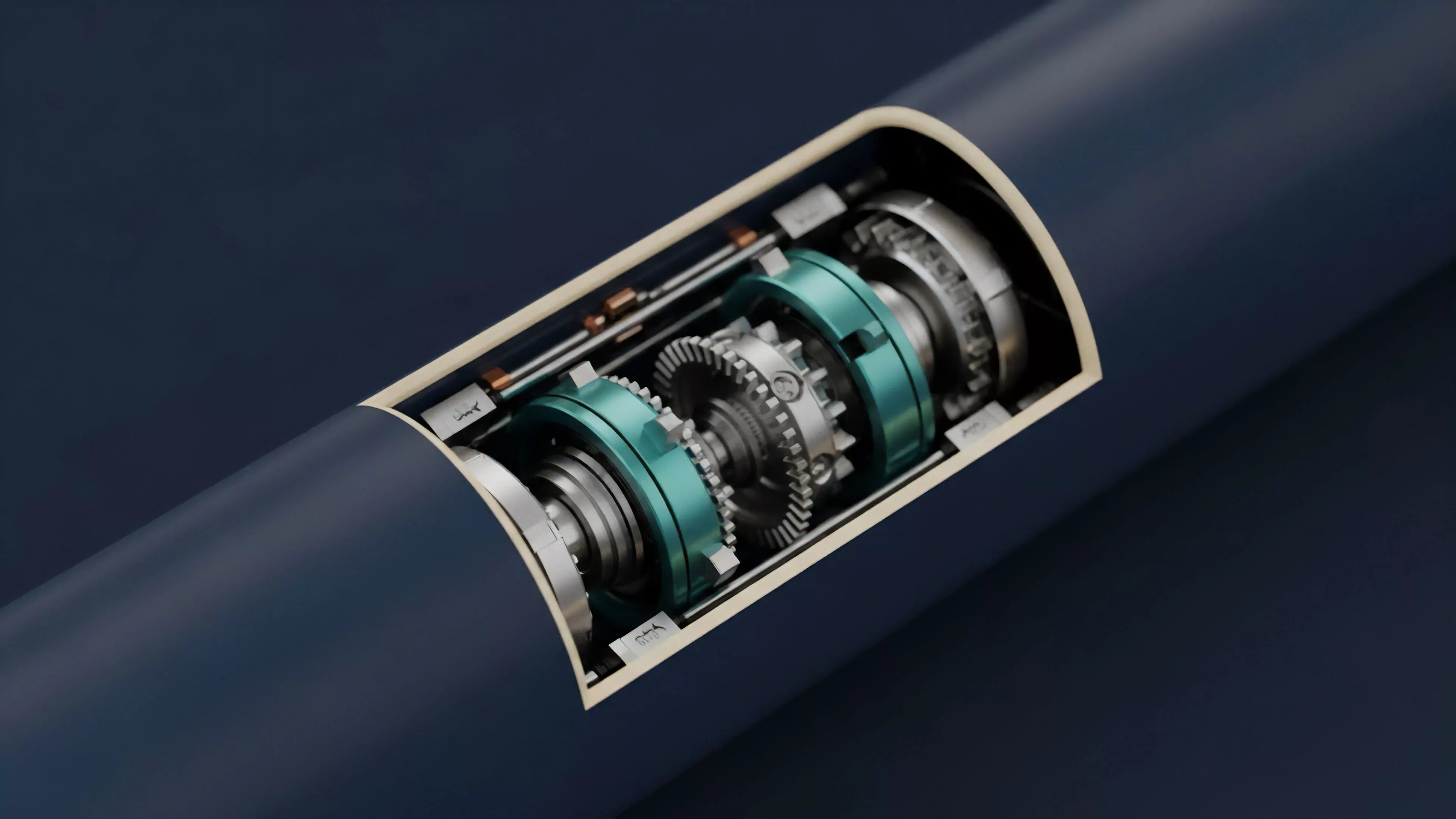
The technical framework of Mobile Verification relies on the interaction between a mobile device’s Secure Element and the protocol’s smart contract layer. When a user initiates a transaction, the mobile application generates a cryptographic signature within the secure hardware, confirming that the request originated from a device associated with a verified identity.
This signature is then transmitted to the blockchain, where it acts as a condition for the smart contract to execute.
The integration of hardware-based attestation allows protocols to treat a mobile device as a secure, verified signing agent for decentralized transactions.
Quantitative modeling of this process requires an analysis of the latency introduced by the verification step. In high-frequency trading environments, every millisecond of delay affects the competitiveness of a participant’s order. Architects must balance the security benefits of rigorous verification against the performance costs of these cryptographic checks.
| Metric | Standard Wallet | Mobile Verified Wallet |
| Sybil Resistance | Low | High |
| Regulatory Compliance | Minimal | Advanced |
| Execution Latency | Baseline | Increased |
The adversarial reality of this system means that the security of Mobile Verification is only as strong as the underlying hardware attestation. If a device’s security module is compromised, the integrity of the entire verification chain is at risk. Therefore, protocols must maintain dynamic, multi-factor verification strategies to ensure that the cost of exploiting the identity layer remains prohibitively high.

Approach
Current implementations prioritize a modular architecture, separating the identity verification process from the core trading engine.
This allows protocols to integrate with various identity providers ⎊ ranging from decentralized identity protocols to traditional banking APIs ⎊ without altering the fundamental structure of the order book or the settlement mechanism.
- Decentralized Identifiers: Users maintain control over their identity credentials, sharing only the necessary proofs with the trading protocol.
- Threshold Signatures: Multi-party computation is employed to distribute the verification risk, ensuring that no single entity can compromise the user’s identity data.
- Reputation Scoring: Verified identities allow for the creation of on-chain reputation systems, where historical behavior informs risk parameters and collateral requirements.
This approach shifts the burden of identity management away from the protocol itself, reducing the attack surface for potential exploits. By utilizing established standards for verifiable credentials, protocols can ensure interoperability across different chains and trading venues, creating a unified identity layer for the decentralized derivatives market.

Evolution
The path from simple address-based trading to identity-verified decentralized markets has been driven by the need for capital efficiency and regulatory compliance. Initially, protocols treated all wallet addresses as equal, which made it impossible to implement risk-based margin requirements or differentiated fee structures.
The evolution toward Mobile Verification reflects a maturing understanding of the trade-offs between privacy, security, and access.
Evolution in this sector is marked by the transition from passive wallet monitoring to active, hardware-backed user verification protocols.
One might consider the parallel to the evolution of the early internet; just as the transition from anonymous bulletin boards to authenticated user accounts enabled the rise of e-commerce, so too does Mobile Verification enable the growth of institutional-grade decentralized finance. The shift is not a rejection of decentralization, but a necessary maturation of the infrastructure required to handle larger volumes of capital. This development acknowledges that systemic stability is a function of knowing who, or at least what kind of agent, is interacting with the protocol at any given moment.

Horizon
The future of Mobile Verification points toward the integration of biometric-backed cryptographic proofs, where the user’s physical presence is the ultimate key to the protocol.
This will likely involve the standardization of hardware-based identity across different blockchain networks, allowing for seamless, verified movement of capital and positions between decentralized exchanges.
| Future Trend | Impact |
| Biometric Attestation | Eliminates device-based theft risks |
| Cross-Chain Identity | Unified reputation across protocols |
| Institutional Integration | Direct on-ramp for regulated capital |
As the technology matures, we will see the emergence of autonomous identity agents that manage a user’s verification status across multiple platforms, optimizing for both privacy and regulatory compliance. The challenge will remain the constant tension between the desire for total decentralization and the practical reality of operating within a regulated, adversarial financial world. The protocols that succeed will be those that can automate this verification process without introducing bottlenecks that stifle market liquidity.
