Essence
The core of MEV exploitation within crypto options protocols is the extraction of value from predictable state changes, specifically targeting the inherent pricing inefficiencies and liquidation mechanisms of decentralized automated market makers (AMMs). This activity represents a fundamental challenge to the capital efficiency and risk profile of options liquidity pools. Unlike traditional market making where price discovery is continuous and largely opaque to external observers, options protocols on a blockchain create a deterministic environment where future state changes ⎊ such as an oracle price update or a liquidation event ⎊ can be predicted and acted upon by specialized searcher bots.
The searcher’s objective is to observe a pending transaction or a specific market condition that creates a temporary arbitrage opportunity and then execute a trade at a more favorable price before the protocol’s AMM can adjust. This is a high-stakes, low-latency race condition where the searcher attempts to profit from the lag between the market price change and the protocol’s response.
This dynamic transforms the options market from a simple exchange of risk between users and liquidity providers (LPs) into an adversarial environment where a third party (the searcher) captures value from both sides. For LPs, this means their expected returns are diminished by the consistent siphoning of premium by searchers. For retail traders, it results in higher costs of execution and a form of hidden taxation on their trades.
The very design of options AMMs, which must balance liquidity provision with risk management, creates the specific vulnerabilities that MEV searchers exploit. These vulnerabilities often stem from the AMM’s reliance on a pricing model (such as Black-Scholes or variations) that requires frequent updates based on underlying asset prices, volatility, and time decay.
MEV exploitation in options markets is a race condition where automated searchers extract value by front-running predictable pricing adjustments or liquidation events within decentralized protocols.
The searcher’s profit is derived from the delta between the price at which the AMM should have re-priced and the price at which the searcher executes their trade. The value extracted is a direct cost to the liquidity pool. This systemic issue highlights the tension between the transparency of decentralized ledgers and the competitive nature of financial markets, where information asymmetry is highly prized.
The searcher essentially acts as a highly efficient, adversarial “risk engine” that liquidates positions and captures premium discrepancies before the AMM can adjust.

Origin
The concept of MEV has roots in traditional finance, specifically in high-frequency trading (HFT) and order flow manipulation. The core idea of profiting from information asymmetry and transaction ordering has existed since the earliest days of electronic trading. In traditional markets, HFT firms pay for order flow to gain insight into pending large trades, allowing them to front-run those trades or capture arbitrage opportunities before they disappear.
This practice, often referred to as “latency arbitrage,” is the non-blockchain analog to MEV.
When DeFi emerged, the transparent and deterministic nature of blockchain state transitions created a new, more accessible version of this behavior. The term “MEV” was coined to describe the value extracted from reordering transactions on the Ethereum blockchain. Initially, MEV primarily focused on simple decentralized exchange (DEX) arbitrage, where searchers would identify price differences between two liquidity pools and execute a profitable swap by front-running other transactions.
This quickly evolved to include “sandwich attacks,” where a searcher places a buy order immediately before a large user trade and a sell order immediately after, profiting from the user’s slippage.
The transition to options protocols introduced a more complex set of MEV vectors. Early options protocols often relied on simple AMMs or vault structures where pricing was based on a combination of oracle feeds and pool rebalancing logic. The deterministic nature of these rebalancing events created predictable windows for exploitation.
For instance, if an options protocol used an external oracle to determine the strike price for a new options series, searchers could observe the oracle update transaction in the mempool and execute trades based on the new price before the protocol itself fully processed the update. The options market, with its inherent complexity related to volatility and time decay, presented a more sophisticated playground for MEV searchers compared to simple spot swaps.

Theory
The theoretical foundation of options MEV exploitation lies at the intersection of quantitative finance, behavioral game theory, and protocol physics. From a quantitative perspective, the primary source of MEV in options protocols is the mispricing of volatility and delta, which occurs when an AMM’s pricing curve fails to adjust immediately to changes in market conditions. This creates a predictable arbitrage opportunity.
From a game theory standpoint, MEV represents a non-cooperative game between liquidity providers (LPs) and searchers, where the searcher’s optimal strategy is to maximize extraction by identifying and acting on information asymmetries.
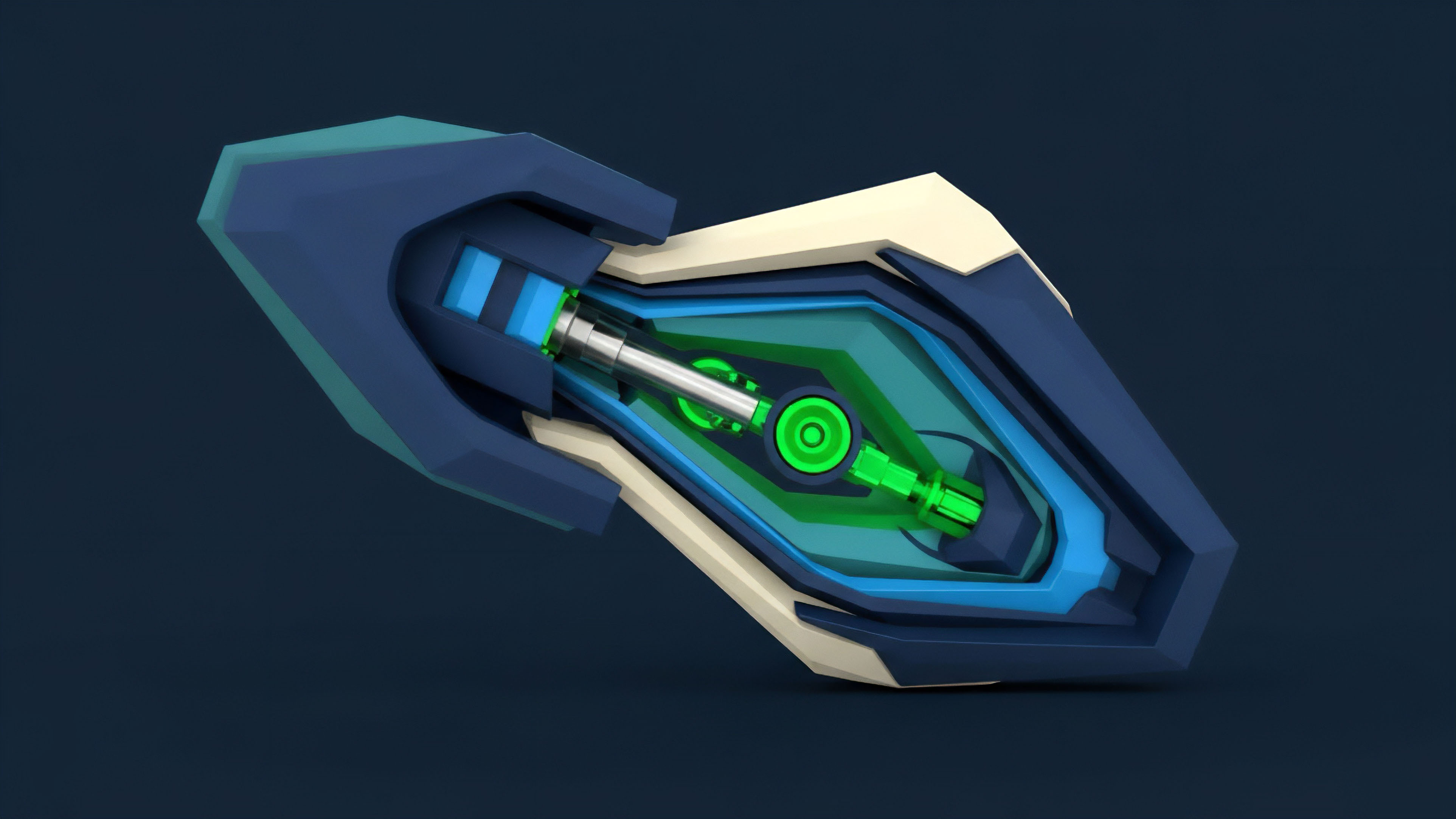
A core vulnerability arises from the fact that options AMMs must maintain a balance of options and underlying assets. When a large trade or market movement changes the delta of the pool, the AMM needs to rebalance to maintain a neutral risk profile. This rebalancing process creates a temporary price discrepancy between the AMM’s internal price and the external market price.
The searcher’s role is to identify this discrepancy and execute a trade that captures the difference before the AMM’s rebalancing logic corrects the price. This extraction fundamentally shifts the risk-reward calculation for LPs, who are often unaware that a significant portion of their potential premium is being siphoned off by searchers.
A specific area of exploitation is related to volatility skew. In traditional markets, volatility skew refers to the phenomenon where options with different strike prices have different implied volatilities. Options AMMs often struggle to accurately model and reprice this skew in real-time, especially when underlying asset prices move rapidly.
Searchers can exploit this by identifying when the AMM’s implied volatility for a specific strike is significantly lower than the market’s implied volatility, allowing them to buy cheap options from the AMM and sell them on a different venue.

Liquidation Exploitation and Protocol Design
Liquidation mechanisms represent another major vector for options MEV. In protocols that allow users to short options or provide collateralized positions, a drop in collateral value or a change in underlying price can trigger a liquidation event. The liquidation process itself creates a deterministic opportunity for searchers.
When a position becomes eligible for liquidation, searchers compete in a priority gas auction (PGA) to execute the liquidation transaction first. The winning searcher profits by acquiring the collateral at a discount or by collecting a liquidation fee. This creates a negative feedback loop for users and LPs, where the risk of liquidation is amplified by the presence of searchers competing to liquidate positions as quickly as possible.
- Deterministic Pricing Models: AMMs for options often rely on models that are slow to react to real-time volatility shifts, creating predictable arbitrage opportunities.
- Liquidation Triggers: The conditions for liquidation are often public and easily monitored, allowing searchers to front-run the liquidation process and capture the collateral discount.
- Oracle Latency: Price updates from external oracles introduce a delay between the real-world price change and the protocol’s state change, creating a window for MEV extraction.
Approach
The practical execution of options MEV exploitation involves a sophisticated technical stack that goes beyond simple mempool monitoring. The modern searcher operates within a highly competitive ecosystem where speed and network topology are critical. The core strategy revolves around identifying opportunities in the public transaction pool (mempool) and then constructing a transaction bundle designed to maximize profit and minimize risk of failure.
The most common approach for options MEV searchers is to identify a pending large options trade or a market-moving event. The searcher then constructs a “sandwich attack” or a simple arbitrage trade. In a sandwich attack on an options trade, the searcher executes a small trade before the user’s large trade to move the AMM price in their favor, then executes a trade after the user’s trade to capture the slippage created by the user.
This is a complex form of exploitation in options because it requires precise calculations of the AMM’s pricing curve.

Priority Gas Auctions and Bundle Construction
To ensure their transaction executes before others, searchers engage in priority gas auctions (PGAs). This involves submitting a transaction with a high gas fee to incentivize block proposers to include their transaction. The competition for block space has led to the development of sophisticated MEV relay networks and private transaction pools (e.g.
Flashbots) where searchers can submit their bundles directly to block builders without broadcasting them publicly. This “dark forest” environment allows searchers to execute complex strategies without revealing their intentions to other competitors.
| MEV Strategy | Description | Target Vulnerability |
|---|---|---|
| Liquidation Front-Running | Monitoring positions for liquidation eligibility and submitting a liquidation transaction with high gas to execute first. | Deterministic liquidation thresholds and collateral requirements. |
| Options Arbitrage | Identifying price discrepancies between the AMM’s calculated price and the external market price (e.g. CEX options or spot price). | Lag in AMM re-pricing and oracle updates. |
| Sandwich Attacks | Placing buy and sell orders around a large user trade to capture slippage and profit from price impact. | User slippage tolerance and AMM pricing curve. |
The searcher’s approach must account for the high cost of gas and the risk of other searchers competing for the same opportunity. This creates a highly technical and capital-intensive environment where only sophisticated players can consistently profit. The searcher must calculate the maximum profitable gas price to pay, ensuring their profit exceeds the cost of inclusion.

Evolution
The evolution of options MEV exploitation is characterized by an ongoing arms race between searchers and protocol developers. Initially, protocols were built with simple AMM models that were highly susceptible to basic arbitrage. The first generation of countermeasures focused on transaction batching and implementing “decay mechanisms” to mitigate the impact of front-running.
These early solutions, however, often introduced new complexities or reduced capital efficiency for LPs.
A significant development in the MEV arms race was the introduction of Proposer-Builder Separation (PBS) on Ethereum. PBS aims to separate the role of block building from block proposal. This change allows searchers to submit transaction bundles directly to builders, rather than competing publicly in the mempool.
While PBS was designed to decentralize MEV extraction and make it more efficient, it has also created a highly specialized ecosystem where searchers pay directly for priority inclusion. This has centralized MEV extraction into a few large searcher-builder pools, potentially increasing the efficiency of options MEV exploitation by reducing the risk of a searcher’s bundle failing due to a competing transaction.
Countermeasures and Mitigation Techniques
Protocol developers have implemented various techniques to mitigate MEV. These strategies focus on making it harder for searchers to identify and exploit opportunities, or by internalizing the MEV value for LPs.
- Dynamic Pricing Adjustments: Implementing real-time pricing models that adjust immediately to underlying market movements, reducing the window for arbitrage.
- Transaction Batching: Grouping multiple user transactions together and processing them as a single batch, making it difficult for searchers to front-run individual trades.
- Internalized Liquidity: Using a Request-for-Quote (RFQ) model where market makers directly provide liquidity, rather than a public AMM, to hide order flow from searchers.
- MEV-Resistant AMMs: Designing options AMMs with built-in mechanisms that internalize MEV by adjusting pricing to reflect potential searcher activity, thereby benefiting LPs.
The current state of options MEV is one where searchers are constantly innovating to find new vulnerabilities, while protocols are constantly adapting to patch those vulnerabilities. The core tension remains unresolved: how to maintain the transparency and permissionless nature of a decentralized ledger while preventing sophisticated actors from exploiting that transparency for profit at the expense of other users.

Horizon
Looking forward, the future of options MEV exploitation will be defined by the shift from public-pool arbitrage to private-order-flow internalization. The current model, where searchers compete publicly for opportunities, is inefficient for both searchers and protocols. The next generation of options protocols will likely adopt architectural changes that fundamentally alter the MEV landscape.
We will see a move toward “dark pools” for options trading where transactions are routed directly to market makers or specialized builders, bypassing the public mempool entirely. This model, while potentially more efficient for execution, raises concerns about transparency and decentralization.
The core issue remains: MEV is not going away. It is an intrinsic part of any financial system with transaction ordering. The challenge is to shift MEV from being a cost to users to a source of value for liquidity providers.
This requires a new approach to protocol design that internalizes MEV, effectively turning the searcher’s profit into a yield for LPs. The question is whether we can design systems where the efficiency gains from MEV extraction benefit the protocol’s participants rather than external, parasitic searchers.

The Synthesis of Divergence
The critical divergence point for options MEV lies in the choice between two futures: a fully internalized MEV model where protocols become “MEV searchers” themselves, or a model where MEV extraction is decentralized through new block construction mechanisms. If protocols successfully internalize MEV, LPs will receive higher yields, but this may centralize power in the hands of protocol developers. If MEV extraction remains decentralized but optimized, the competitive pressure on searchers will increase, leading to a highly efficient, but potentially predatory, market.
The long-term challenge for options protocols is not eliminating MEV, but rather internalizing it to benefit liquidity providers instead of external searchers.

Novel Conjecture
A new hypothesis emerges: The future of options MEV will be defined by a shift in incentive structures where searchers are incentivized to provide liquidity rather than extract value. This would involve a mechanism where searchers are rewarded for rebalancing the AMM efficiently, rather than for simply front-running user trades. The current model creates a conflict of interest; a better design would align searcher incentives with protocol health.

Instrument of Agency
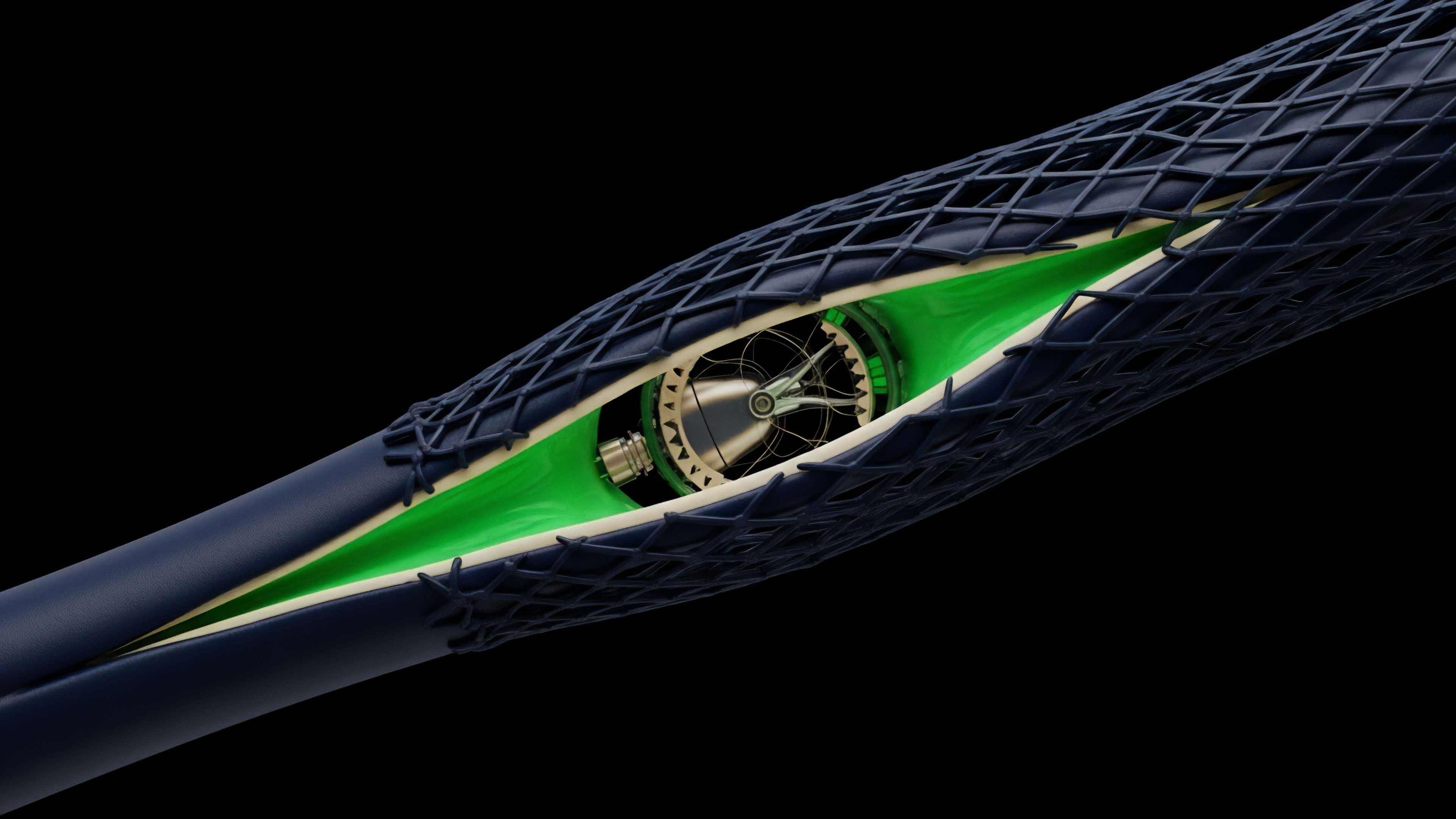
A potential solution to this conflict is a Dynamic Premium Adjustment Mechanism (DPAM). This mechanism would be integrated directly into the options AMM and would function as follows: When an oracle update or large trade creates a potential MEV opportunity, the DPAM automatically adjusts the options premium in real-time. This adjustment captures the value that would otherwise be extracted by searchers and distributes it directly to LPs in the form of increased yield.
The mechanism would dynamically increase the transaction fee for trades that attempt to capture MEV, effectively internalizing the profit. This system would be designed to make MEV extraction unprofitable for external searchers, forcing them to participate as LPs instead.
The future of options MEV requires a shift in incentive structures to align searcher profit with protocol health, transforming parasitic extraction into productive rebalancing.

Glossary

Logic Flaw Exploitation

Mev Profitability Analysis Frameworks for Options

Mev Resistant Sequencing

Exploitation Cycles
Oracle Manipulation Mev
Mev Frontrunning

Mev Resistance Strategies

Competitive Landscape
Protocol Exploitation