Essence
The Oracle Manipulation Cost (OMC) is a critical financial metric representing the minimum aggregate capital required to maliciously shift a price feed ⎊ used by a crypto options or derivatives protocol ⎊ sufficiently to force a profitable liquidation or settlement event for the attacker. It functions as the ultimate stress test for any decentralized finance (DeFi) architecture. This is not a static value; it is a dynamic, time-sensitive function of the underlying market’s liquidity depth, the oracle’s aggregation methodology, and the total value locked (TVL) secured by that price feed.
Our primary concern as architects is the integrity of the settlement layer. If the cost to corrupt the data is less than the potential profit from that corruption, the system is fundamentally unsound. The OMC quantifies this vulnerability, providing a hard, financialized security budget for the protocol.
It must always be calculated against the highest-leverage positions and the thinnest liquidity pools that feed the oracle, often requiring an analysis of order book microstructure across multiple decentralized exchanges (DEXs).
Oracle Manipulation Cost (OMC) is the quantifiable, adversarial capital requirement to force a protocol’s liquidation engine into an incorrect and profitable state for the attacker.
A robust derivative system views the OMC as a load-bearing structural component. A protocol’s solvency is directly tied to the difficulty an attacker faces in moving the reference price. A low OMC signals a high-leverage target, irrespective of the smart contract code’s quality.

Origin
The concept of quantifying manipulation cost arose from the earliest exploits against decentralized lending and synthetic asset protocols, where reliance on a single, unaudited spot price feed proved catastrophic. These initial attacks demonstrated that the economic security of a protocol was decoupled from its cryptographic security. A flash loan could be used to temporarily drain a small liquidity pool, spiking the price on a DEX and subsequently forcing an incorrect liquidation on the dependent lending protocol.
The response was an architectural shift toward time-weighted average price (TWAP) oracles. The introduction of the TWAP mechanism forced the attacker to sustain the price deviation over a period ⎊ the TWAP window ⎊ thereby dramatically increasing the capital and time required for a successful attack. The OMC calculation, therefore, evolved from a simple “cost to empty a pool” to a complex function incorporating the cost of capital, the cost of sustained market friction, and the probability of arbitrageurs correcting the price during the attack window.
Financial history shows us that systemic risk often hides in the settlement mechanism. In the crypto space, the oracle is the settlement mechanism. The early failures of simple spot price feeds were a harsh lesson, establishing the first principle of DeFi security: economic defense must be proportional to economic exposure.

Theory
The theoretical foundation of OMC rests on the adversarial relationship between a protocol’s total open interest and the market’s aggregate liquidity profile. The attacker’s objective is to achieve a net positive expected value (E ) from the attack, where the profit from forced liquidations or advantageous settlements must exceed the capital cost and transaction fees associated with the manipulation. This calculation is complex because it involves modeling market impact across non-linear Automated Market Maker (AMM) curves and predicting the reaction function of external arbitrageurs.
The fundamental equation is a function of four primary variables, often represented as a dynamic optimization problem: OMC = f(Liquidity Depth, TWAP Window, Target Slippage, Attack Vector Caπtal). The cost is not just the capital deployed to move the price, but the cost of that capital being locked up for the duration of the TWAP window, creating a carry cost. This cost must be modeled as a sustained pressure on the order book, not a single trade.
The elegance of the model lies in its integration of traditional market microstructure ⎊ the friction of order flow and slippage ⎊ directly into the protocol’s security budget, transforming a technical vulnerability into a quantifiable financial risk that can be hedged or insured against. Our inability to respect the skew in liquidity depth is the critical flaw in our current models; we must account for the non-uniform distribution of capital across the depth-of-market.

Core Variables in OMC Modeling
- Liquidity Depth Profile: The capital required to achieve a target price movement on the primary liquidity sources feeding the oracle. This is non-linear due to AMM curve shapes.
- Time-Weighted Average Price (TWAP) Window: The duration over which the manipulation must be sustained, directly impacting the capital’s opportunity cost and exposure to arbitrage.
- Target Slippage Threshold: The necessary price deviation needed to trigger the most profitable or systemically important liquidation cluster within the options protocol.
- Arbitrage Correction Speed: The estimated velocity at which external market participants will correct the manipulated price, effectively acting as the protocol’s first line of economic defense.

Illustrative OMC Capital Requirement
We can simplify the capital requirement based on the liquidity profile of the target exchange, assuming a 10-minute TWAP window and a 10% target price deviation.
| Target DEX Liquidity ($M) | Estimated Capital to Sustain 10% Deviation ($M) | Implied OMC (Approx.) |
|---|---|---|
| $10M | $1.5M – $2.5M | Low (High Vulnerability) |
| $100M | $15M – $25M | Medium (Acceptable Risk) |
| $500M+ | $75M – $125M+ | High (Robust Security) |
This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored. A low OMC means the protocol’s security budget is easily exceeded by the profit potential of the attack.

Approach
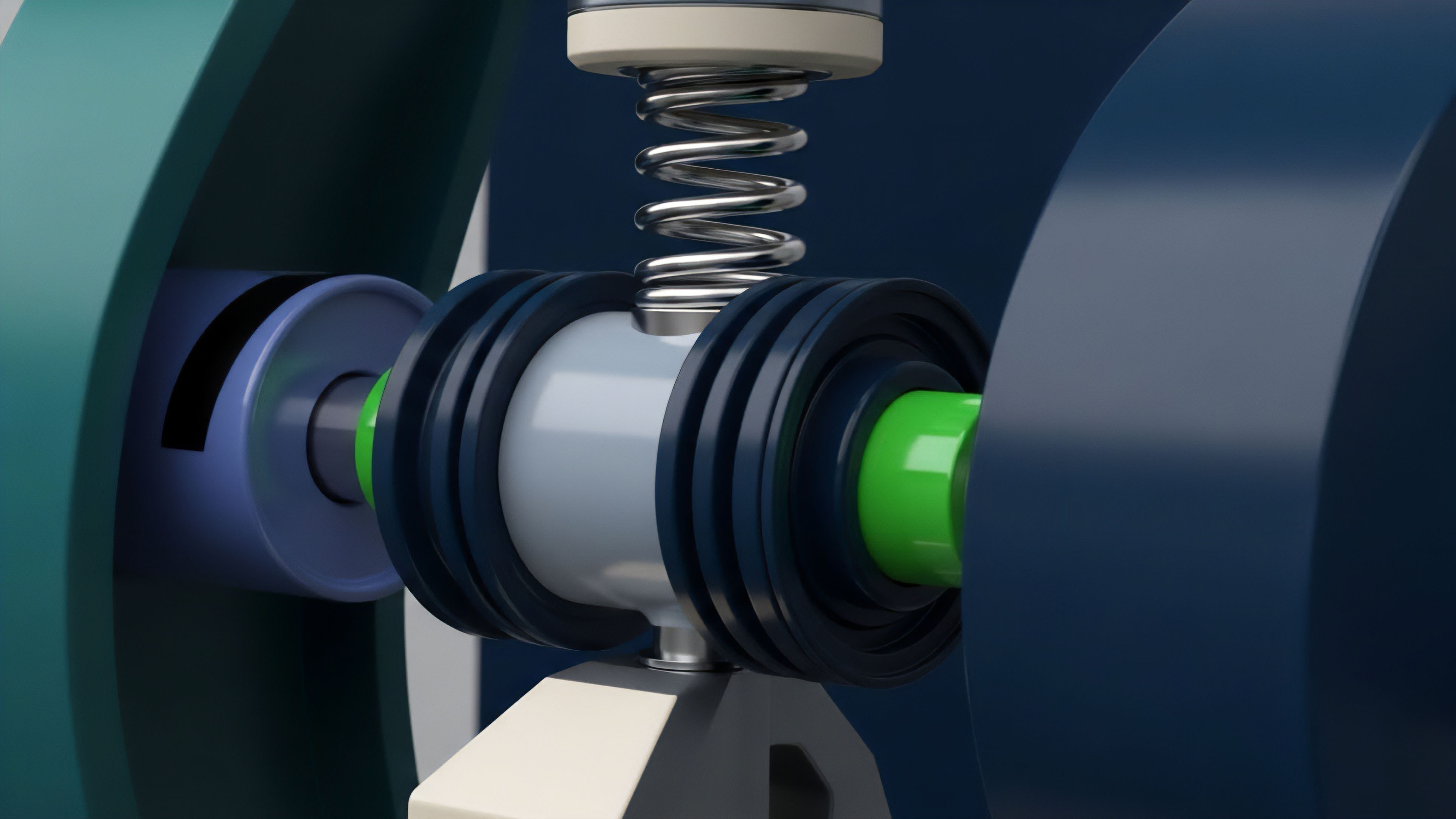
The practical calculation of OMC begins with a full mapping of the protocol’s aggregate exposure. This involves calculating the total delta and vega of all outstanding options and perpetual futures positions to identify the precise price points where liquidation cascades or margin calls are clustered. This cluster point defines the attacker’s profit target.
Next, the protocol must conduct a rigorous Liquidity Profile Mapping across all reference exchanges. This involves querying historical and real-time order book data to construct a non-linear slippage function for the relevant trading pairs. This function reveals the cost to move the price by the target amount, δ P, over the duration of the oracle’s aggregation window, δ T.
The practical application of OMC requires continuous stress-testing against the protocol’s liquidation thresholds, treating the market itself as the adversarial actor.
We translate the protocol’s aggregate exposure into a quantifiable attack surface. A protocol with a massive short Vega position, for example, is highly vulnerable to a sudden, manipulated volatility spike, which an attacker can profit from by moving the reference index.
Protocol Assessment Steps for OMC
- Determine the maximum profitable payout to an attacker by aggregating all open interest and identifying the most vulnerable liquidation cluster.
- Identify all underlying liquidity sources that feed the price oracle, focusing on those with the highest volatility and lowest depth.
- Model the capital required to sustain the necessary price deviation on the weakest link over the oracle’s time window, incorporating estimated transaction and slippage costs.
- Set the protocol’s minimum collateralization ratio and liquidation buffer to a level that ensures the cost of attack always significantly exceeds the maximum potential profit.
The system must be engineered with a high degree of capital redundancy. This means the collateral securing the derivatives must be sufficient to absorb a price shock that is demonstrably less costly than the calculated OMC. If the system’s economic defense mechanism fails before the attacker’s capital is exhausted, the model is flawed.

Evolution
The evolution of Oracle Manipulation Cost calculation is a story of an arms race. Early protocols calculated a single, static OMC based on the deepest liquidity pool. Today, the calculation must account for cross-protocol contamination.
An attacker might manipulate a less liquid token that is a component of a basket index used by the options protocol, effectively exploiting a lower OMC on a tangential asset to compromise a high-value derivative.
This forces the adoption of Multi-Source Hybrid Oracles that sample prices from a diverse array of sources, including centralized exchanges (CEXs), multiple DEXs, and specialized data providers. The calculation of OMC must now be a weighted average of the manipulation costs of all these sources, with the weight determined by the oracle’s aggregation algorithm. The attacker is forced to target the entire composite structure, exponentially increasing the capital required.
Adversarial game theory dictates that a successful manipulation attack is one where the attacker’s expected profit is greater than the total Oracle Manipulation Cost plus the risk of failure.
The systemic implications are profound. The stability of a major options protocol is no longer just a function of its own design; it is a function of the aggregate liquidity depth of the entire DeFi landscape. This is why we see a movement toward protocol-level cooperation in liquidity provisioning.
To understand the true cost of attack, one must study the adversary. Sun Tzu’s principles apply here: know your enemy ⎊ the arbitrageur ⎊ and know your battleground ⎊ the order book. A successful defense anticipates the attacker’s optimal path of least resistance, then strategically reinforces that weakest point.
Oracle Design Trade-Offs and OMC
| Oracle Design Type | OMC Impact | Latency Trade-Off |
|---|---|---|
| Single Spot Price | Extremely Low (High Risk) | Minimal (Fastest) |
| Decentralized TWAP | Medium-High (Capital-Intensive Attack) | High (Slowest, most secure) |
| Hybrid (TWAP + CEX Feed) | Highest (Multi-Vector Attack Required) | Medium (Balancing speed and security) |
Horizon
The future of OMC calculation moves toward real-time, dynamic fee adjustments. Imagine a system where the collateralization requirements and trading fees are directly linked to the calculated OMC of the underlying asset. If liquidity on the reference exchange thins out, the OMC drops, and the protocol automatically raises margin requirements or charges a higher insurance premium on new positions to offset the increased systemic risk.
This transforms the static security budget into a dynamic, market-driven defense mechanism.
We are also moving toward Protocol Insurance Pools that are specifically capitalized to absorb an OMC-level attack. These pools would be funded by a small fee levied on all derivative trades, with the fee size calibrated by the protocol’s real-time OMC score. This financializes the risk of manipulation, making it a tradable, hedgeable externality.
The ultimate horizon involves cryptographically enforced price feeds, such as zero-knowledge (ZK) proofs validating off-chain price data before it is accepted on-chain. This shifts the defense from a purely economic problem ⎊ how much capital is needed to attack ⎊ to a cryptographic problem ⎊ how much computational power is needed to break the ZK proof. This is the final frontier in creating antifragile derivatives, where the cost of manipulation becomes astronomically high, pushing the attacker’s required capital far beyond the realm of feasibility.

Glossary

Realized Volatility Calculation
L2 Transaction Cost Amortization

Basis Trade Yield Calculation
Economic Security Proportionality

Worst Case Loss Calculation

Greek Calculation Inputs

Cost-Effective Data

Anti-Manipulation Measures
Low-Cost Execution Derivatives