
Essence
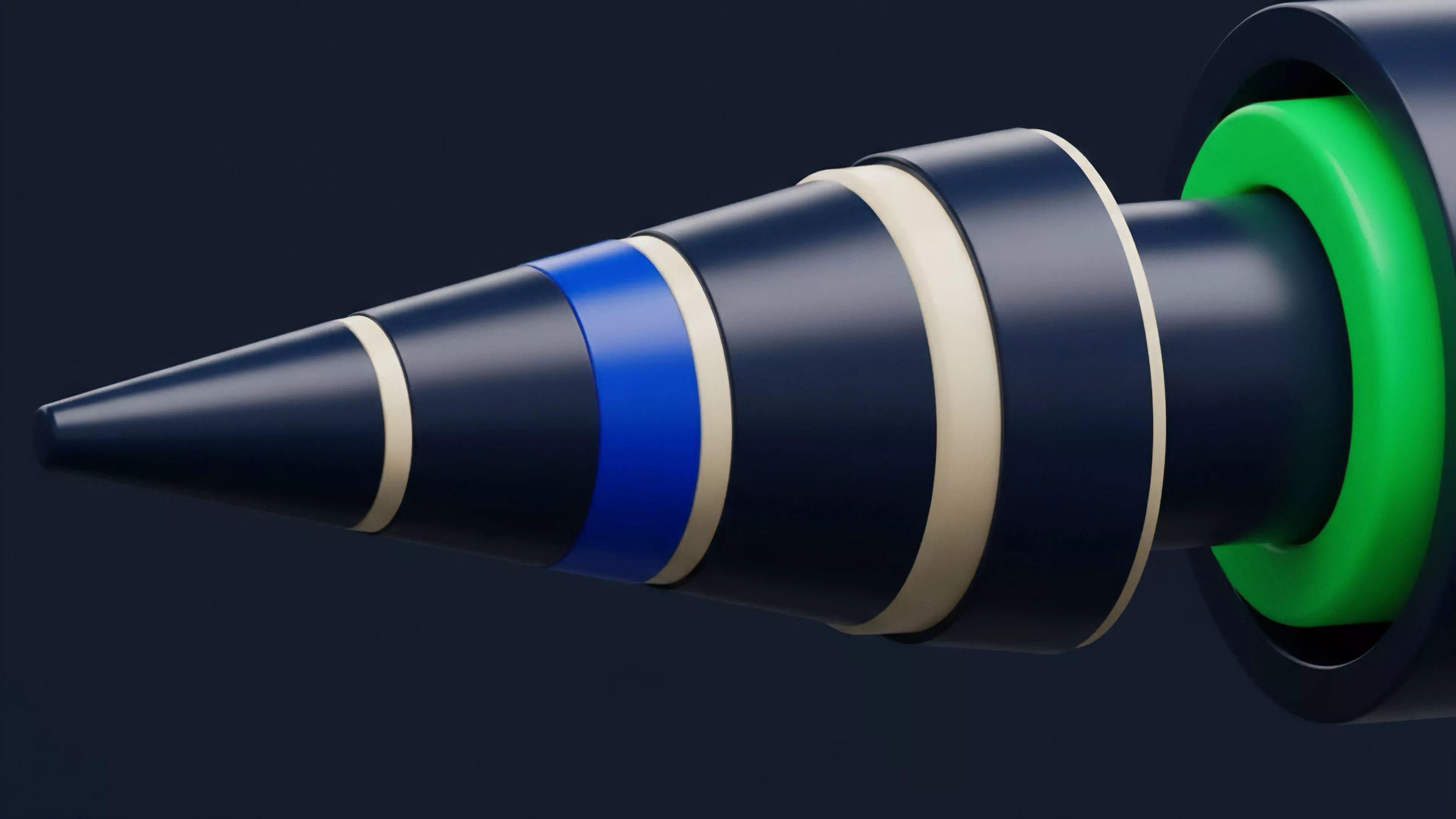
Liquidity Pool Security represents the structural integrity and defensive mechanisms protecting automated market maker protocols from insolvency, manipulation, and exogenous shocks. It functions as the foundational layer ensuring that decentralized trading venues maintain solvency when faced with extreme volatility or adversarial capital flows.
Liquidity pool security acts as the structural defense against insolvency and manipulation in automated market maker protocols.
This domain encompasses the technical, economic, and cryptographic safeguards designed to prevent the drain of underlying assets. It requires constant calibration of parameters such as slippage tolerance, oracle reliability, and pool composition to withstand systemic pressures.

Origin
The inception of Liquidity Pool Security traces back to the realization that constant product market makers operate without traditional order books. Early implementations revealed that price manipulation via flash loans posed a lethal risk to decentralized exchanges.
- Constant Product Formula established the initial pricing mechanism but lacked built-in defenses against price manipulation.
- Oracle Vulnerabilities surfaced when protocols relied on single-source price feeds, leading to significant arbitrage exploits.
- Capital Inefficiency prompted early designers to implement tiered liquidity tiers to manage risk more granularly.
Market participants quickly recognized that decentralized protocols required sophisticated risk engines to prevent total pool depletion. The transition from simplistic automated exchanges to robust, multi-layered financial infrastructure necessitated the formalization of Liquidity Pool Security as a primary design constraint.

Theory
The theoretical framework relies on the intersection of game theory and quantitative finance to maintain equilibrium. Liquidity Pool Security operates on the principle that the pool must remain mathematically solvent even during periods of extreme price divergence between the pool and external markets.
Quantitative Risk Parameters
The stability of a pool is contingent upon several mathematical sensitivities:
| Parameter | Systemic Function |
| Impermanent Loss | Measures divergence risk for liquidity providers |
| Slippage Tolerance | Limits price impact during large trades |
| Oracle Latency | Determines accuracy of price synchronization |
The integrity of a liquidity pool depends on the mathematical calibration of risk parameters to ensure solvency under stress.
Adversarial agents exploit gaps in these parameters. If the cost of manipulating the price within the pool is lower than the potential profit from arbitrage, the protocol suffers capital flight. Therefore, the design must force the cost of attack to exceed the expected gain.
Sometimes I wonder if our reliance on algorithmic pricing creates a false sense of security that blinds us to the raw, chaotic nature of human intent. The code holds firm until it encounters a market force it was never programmed to anticipate.

Game Theoretic Equilibrium
Security is achieved when the incentives for honest participation outweigh the incentives for malicious action. Protocols use fee structures, governance tokens, and lock-up periods to align the interests of liquidity providers with the long-term health of the pool.

Approach
Current methodologies emphasize defense-in-depth, combining on-chain monitoring with rigorous smart contract auditing. Architects now prioritize modularity to isolate risks within specific liquidity pools.
- Decentralized Oracle Aggregation ensures that price data remains resistant to single-point failures.
- Dynamic Fee Adjustments allow protocols to compensate liquidity providers for higher volatility and risk exposure.
- Automated Circuit Breakers pause trading activities when extreme price movements threaten the pool solvency.
Modern liquidity pool security employs modular architectures and decentralized oracles to mitigate systemic risk.
Developers are increasingly deploying off-chain monitoring agents that detect anomalous trading patterns before they manifest as on-chain exploits. This proactive stance marks a shift from reactive patching to preventative system engineering.

Evolution
The discipline has shifted from simple, monolithic liquidity models to highly complex, capital-efficient systems. Initial protocols prioritized ease of access, but recent iterations focus heavily on granular risk management.

Structural Advancements
- Concentrated Liquidity enabled providers to supply capital within specific price ranges, increasing efficiency while requiring advanced risk monitoring.
- Cross-Chain Liquidity Bridges introduced new vectors for contagion, necessitating security protocols that span multiple blockchain environments.
- Permissioned Liquidity Pools emerged to address regulatory requirements, adding a layer of identity-based access to traditional pool structures.
The market now demands transparency regarding the underlying security assumptions of any liquidity pool. Investors no longer accept black-box protocols; they require verifiable data on audit history, oracle sources, and historical performance under stress.

Horizon
Future developments will center on the integration of predictive modeling and real-time risk hedging. We expect the rise of automated liquidity management agents that dynamically adjust parameters based on market conditions.
| Innovation | Impact |
| AI Risk Agents | Real-time adjustment of slippage and fee parameters |
| Zero Knowledge Proofs | Verifiable privacy for large liquidity providers |
| Cross-Protocol Insurance | Automated coverage for liquidity pool failures |
The next phase involves the development of decentralized insurance layers that provide immediate restitution for pool-level exploits. This will lower the barrier for institutional participation, provided that Liquidity Pool Security matures into a standardized, audited framework that regulators can interpret. What happens when the automated agents controlling liquidity begin to optimize for risk in ways that contradict human intent?
