
Essence
A Hardware Security Module functions as a tamper-resistant physical device designed to manage the lifecycle of cryptographic keys. Within the sphere of digital asset derivatives, these units provide the foundational trust layer for signing transactions, executing smart contracts, and safeguarding the private keys that control collateral. The device operates in a hardened environment, ensuring that sensitive key material remains isolated from general-purpose operating systems and potential network-based threats.
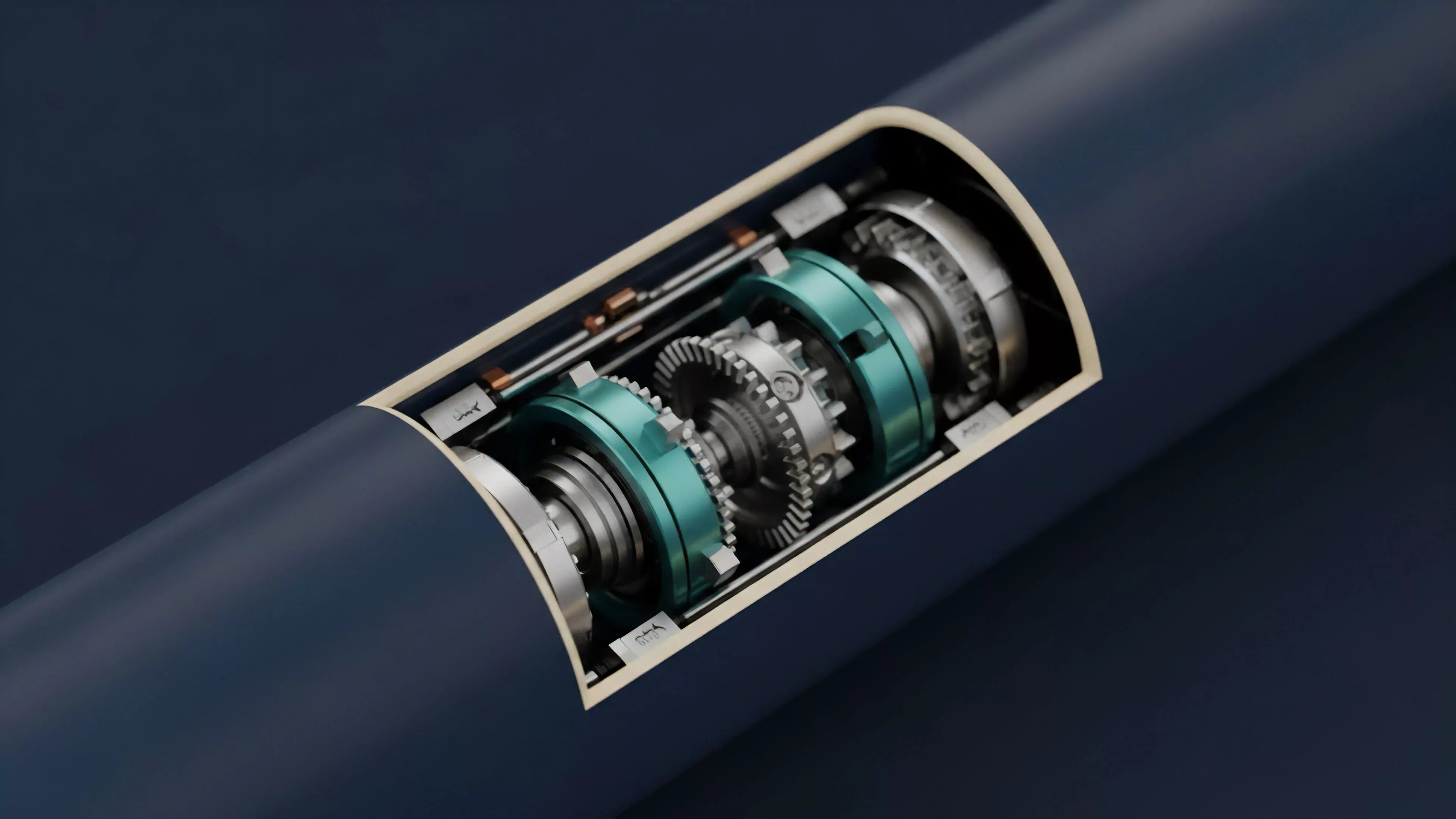
A Hardware Security Module acts as a secure vault for cryptographic keys, ensuring their integrity and isolation from external digital attack vectors.
These modules provide high-assurance cryptographic operations, including key generation, encryption, decryption, and digital signing. In decentralized finance, the ability to perform these actions without exposing private keys to memory-resident exploits defines the reliability of a custody solution or a high-frequency trading engine. The physical architecture typically includes specialized circuitry to detect and respond to environmental tampering, such as voltage manipulation, temperature shifts, or physical intrusion attempts.
Origin
The necessity for Hardware Security Module technology emerged from the fundamental requirement to protect root secrets in traditional banking and governmental infrastructure.
As cryptographic protocols became the standard for securing communication, the vulnerability of storing keys in software became evident. Standard servers, with their expansive attack surfaces, proved insufficient for protecting high-value cryptographic assets against sophisticated adversaries.
- FIPS 140-2 standards established the benchmark for physical security, dictating the requirements for cryptographic modules used in regulated environments.
- Financial institutions historically deployed these modules to secure ATM networks and interbank transaction clearing systems.
- Digital asset custody providers adopted these legacy principles, adapting them to the unique requirements of blockchain address management and decentralized protocol interaction.
The transition of these modules into the crypto-financial sector marked a shift from centralized, siloed security models to decentralized, programmable trust architectures. Early adopters recognized that managing digital asset risk required a shift toward hardware-level isolation, moving away from vulnerable software-based hot wallets.

Theory
The architectural theory of a Hardware Security Module rests on the principle of minimal trust exposure. By decoupling the cryptographic execution environment from the application layer, the module ensures that even a total compromise of the host system does not lead to the extraction of the underlying private keys.
The system utilizes a secure internal processor that performs computations within a protected memory space, returning only the requested output ⎊ such as a signed transaction or an encrypted message ⎊ to the host.
The theoretical strength of a Hardware Security Module lies in its ability to perform cryptographic operations without ever revealing the private key to the host environment.
Quantitative analysis of security risks often utilizes threat modeling to evaluate the probability of key compromise. In a standard software-based environment, the risk of a heap spray or buffer overflow attack is significant. By shifting the key management to a Hardware Security Module, the threat vector shifts from remote code execution to physical hardware access, which is statistically more difficult to scale across global networks.
| Security Layer | Implementation Mechanism | Risk Profile |
| Software Wallet | Memory-resident keys | High remote exploitability |
| Hardware Security Module | Isolated secure enclave | High physical access requirement |
The mathematical rigor of these modules ensures that key generation utilizes high-entropy sources, which is vital for preventing predictability in derivative contract signatures. The device enforces strict access control policies, requiring multi-party authorization for sensitive operations, thereby aligning technical security with institutional governance.

Approach
Current implementations of Hardware Security Module technology involve sophisticated integration with institutional-grade trading platforms and decentralized clearinghouses. These systems employ a tiered architecture where the module handles the final authorization of order flow, margin liquidation calls, and withdrawal requests.
This approach allows firms to maintain high capital efficiency while mitigating the systemic risks associated with single-point-of-failure vulnerabilities.
- Multi-signature integration requires multiple independent modules to authorize a single transaction, preventing unilateral control.
- Automated policy enforcement embeds trading constraints directly into the module, ensuring that transactions only execute if they satisfy pre-defined risk parameters.
- Attestation services provide cryptographic proof that a specific operation occurred within a verified module, enhancing auditability for regulators and liquidity providers.
Professional market participants often leverage these modules to manage collateral held in smart contracts. By anchoring the ownership of the contract’s admin keys in a Hardware Security Module, they ensure that the governance of the derivative protocol remains secure against malicious internal actors or compromised administrative credentials.

Evolution
The trajectory of Hardware Security Module technology has moved from static, monolithic appliances to cloud-native, scalable infrastructure. Early versions were physically cumbersome and difficult to integrate into agile software development lifecycles.
Modern iterations utilize virtualization and containerized interfaces, allowing developers to interact with hardened security boundaries through standardized APIs without sacrificing the integrity of the underlying hardware.
Modern Hardware Security Module designs have evolved from isolated physical appliances into agile, cloud-integrated services that support high-frequency institutional trading.
This evolution reflects a broader trend toward the institutionalization of decentralized markets. As derivative volumes increase, the reliance on specialized security hardware has become a prerequisite for large-scale participation. The shift toward Hardware Security Module-as-a-Service models allows smaller participants to access institutional-grade security, thereby reducing the systemic barriers to entry and increasing the overall resilience of the derivative ecosystem.
| Era | Deployment Model | Primary Use Case |
| Legacy | On-premise appliances | Internal banking systems |
| Emerging | Cloud-native HSMs | Digital asset custody |
| Future | Decentralized secure enclaves | Trustless derivative settlement |
I often consider how the physical constraints of these devices have historically dictated the speed of financial innovation, acting as a bottleneck until the software interfaces caught up to the hardware capabilities. It remains a fascinating paradox that the most advanced digital financial instruments rely on the physical limitations of specialized silicon to maintain their integrity.

Horizon
The future of Hardware Security Module technology resides in the integration with zero-knowledge proofs and secure multi-party computation. These advancements promise to enable trustless, hardware-backed execution where the module does not need to know the full state of the transaction to verify its validity. This shift will likely lead to the creation of autonomous, hardware-secured derivative protocols that operate with higher transparency and lower reliance on centralized custody providers. The next generation of these devices will focus on tighter coupling with blockchain consensus mechanisms, potentially allowing for the direct validation of state transitions within the module itself. This will enable near-instantaneous settlement of complex derivative contracts while maintaining the highest possible standard of cryptographic security. The systemic implication is a more robust financial infrastructure capable of handling massive volumes with minimal counterparty risk.
