Essence
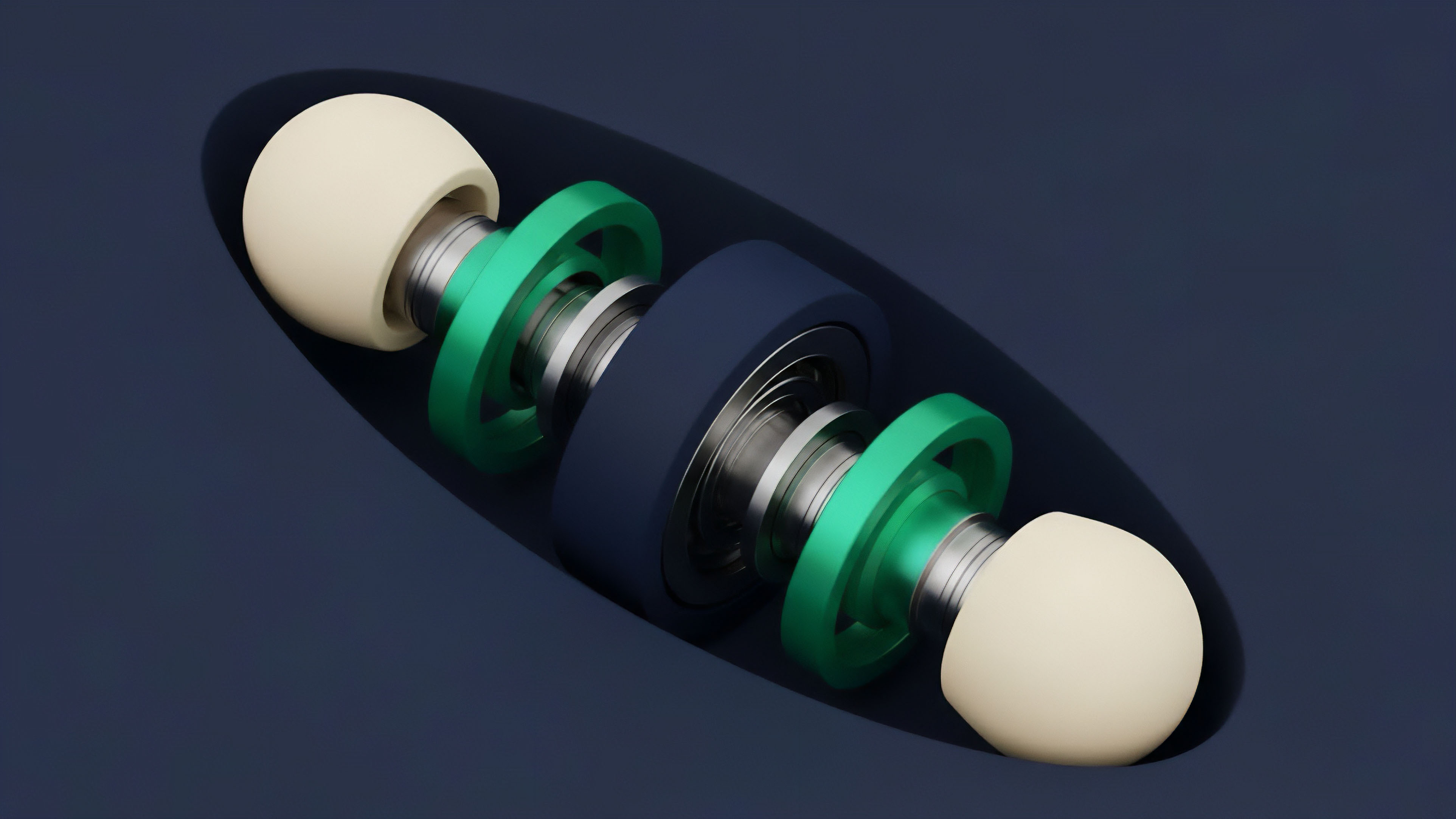
Flash loan manipulation represents a high-velocity, single-block attack vector that exploits the economic logic of decentralized finance protocols. It leverages the unique primitive of a flash loan ⎊ an uncollateralized loan that must be repaid within the same atomic transaction ⎊ to acquire vast amounts of capital temporarily. This capital is then used to execute a sequence of actions designed to exploit a vulnerability in a target protocol, most frequently by manipulating the price feed used by that protocol to determine asset values.
The core vulnerability stems from the reliance on easily influenced on-chain price oracles, typically from decentralized exchanges (DEXs) with insufficient liquidity relative to the attacker’s borrowed capital. The attack is a high-stakes, adversarial game where the attacker’s profit is derived from the difference between the manipulated price and the true market price.
Flash loan manipulation exploits the atomic nature of a single transaction to temporarily acquire uncollateralized capital, execute a price-altering sequence, and extract value from a vulnerable protocol.
The key distinction from traditional financial attacks lies in the elimination of credit risk for the lender. The flash loan itself is risk-free for the lending protocol because the transaction reverts if repayment fails. The risk is transferred entirely to the protocols and liquidity providers that are vulnerable to the subsequent price manipulation.
This changes the economic calculus for the attacker, enabling large-scale exploits without requiring any initial capital investment beyond transaction fees. The attack is a direct challenge to the fundamental assumption that on-chain prices accurately reflect off-chain market conditions in real-time.

The Adversarial Nature of Atomic Transactions
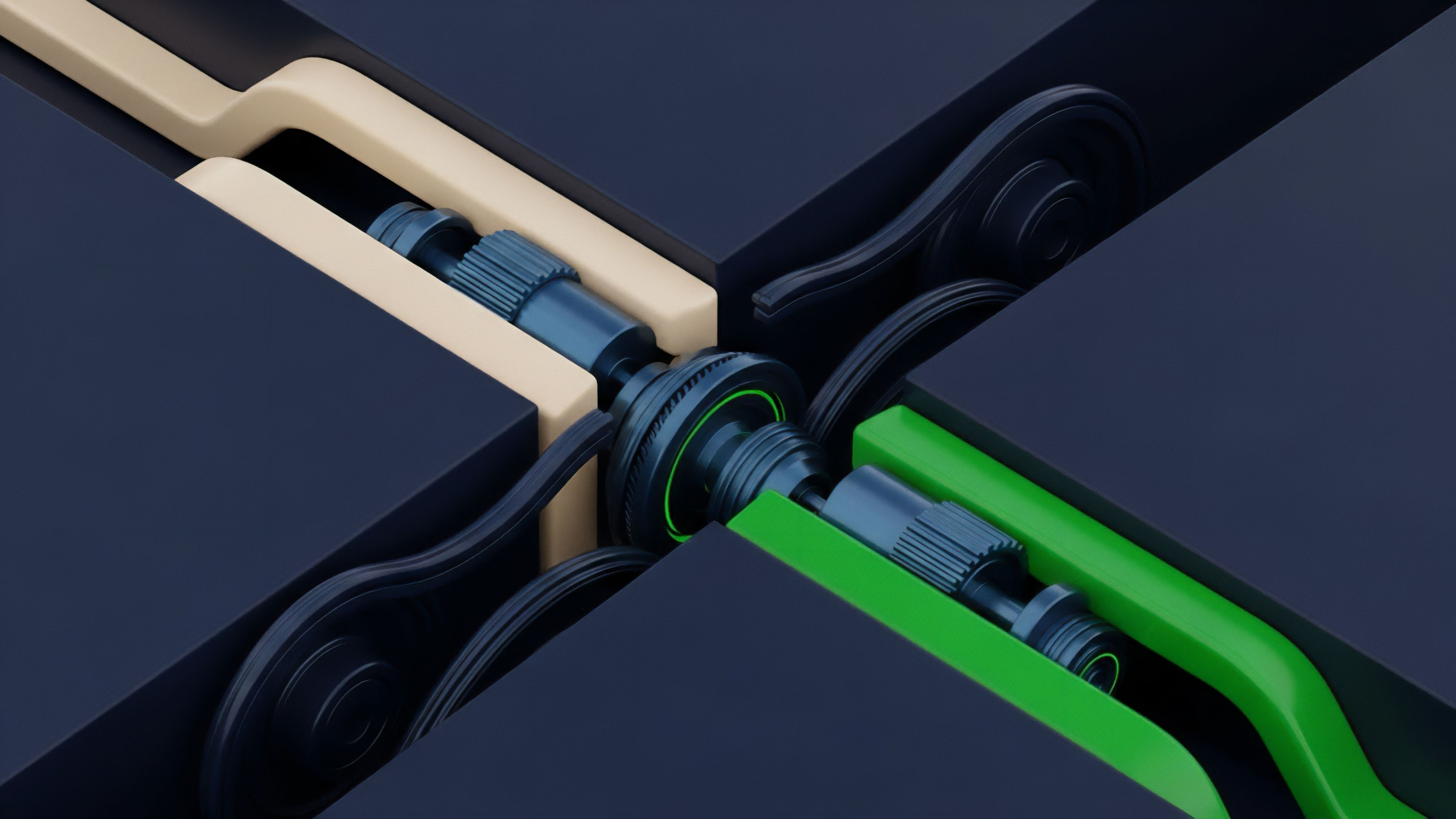
The concept of atomicity in blockchain transactions means that a series of operations either all succeed or all fail as a single unit. This design choice, while powerful for composability, creates a new class of systemic risk. A flash loan manipulation attack is essentially a complex arbitrage strategy where the “arbitrage opportunity” is created by the attacker themselves.
The attacker identifies a protocol that uses a vulnerable price feed, borrows capital, manipulates the price on the source exchange, exploits the target protocol at the manipulated price, and then repays the loan, all within a few hundred milliseconds. This high-speed execution prevents external actors from intervening or arbitraging away the manipulated price before the attack completes.

Origin
The genesis of flash loan manipulation traces directly to the introduction of flash loans by the Aave protocol in early 2020.
The original design concept was to create a new form of capital efficiency for arbitrageurs, allowing them to profit from price differences between exchanges without needing to lock up collateral. This was celebrated as a novel financial primitive that showcased the power of DeFi composability. However, the first major exploits quickly followed, revealing a critical design flaw in the interconnected protocols that relied on simple on-chain price feeds.

The Bzx Attacks and Systemic Discovery
The bZx protocol experienced some of the earliest and most significant flash loan manipulations in February 2020. These events served as a proof-of-concept for the adversarial potential of flash loans. The attacks demonstrated that a large flash loan could be used to execute a large-scale swap on a DEX like Uniswap, causing significant slippage.
A separate protocol that relied on Uniswap’s spot price as an oracle would then misinterpret this manipulated price as the true market value. The attacker would then use this misrepresentation to perform actions like borrowing assets against inflated collateral, or triggering liquidations at an incorrect price. The immediate aftermath of these initial attacks led to a re-evaluation of oracle design and protocol physics.
It became clear that time-weighted average prices (TWAPs) were necessary to smooth out single-block price volatility. The financial community recognized that flash loans were not merely tools for efficient arbitrage; they were also instruments for exploiting systemic vulnerabilities that existed at the intersection of capital access and price discovery. This period marked a critical shift in how DeFi protocols approached risk management, moving from a focus on individual protocol security to a broader consideration of systemic interconnectedness and adversarial game theory.

Theory
The theoretical underpinnings of flash loan manipulation rest on a confluence of quantitative finance principles, behavioral game theory, and smart contract security. The attack model can be framed as an exploitation of protocol physics , specifically the discrepancy between the time-bound nature of on-chain price updates and the instantaneous nature of a flash loan transaction.

Price Oracle Vulnerabilities and Model Risk
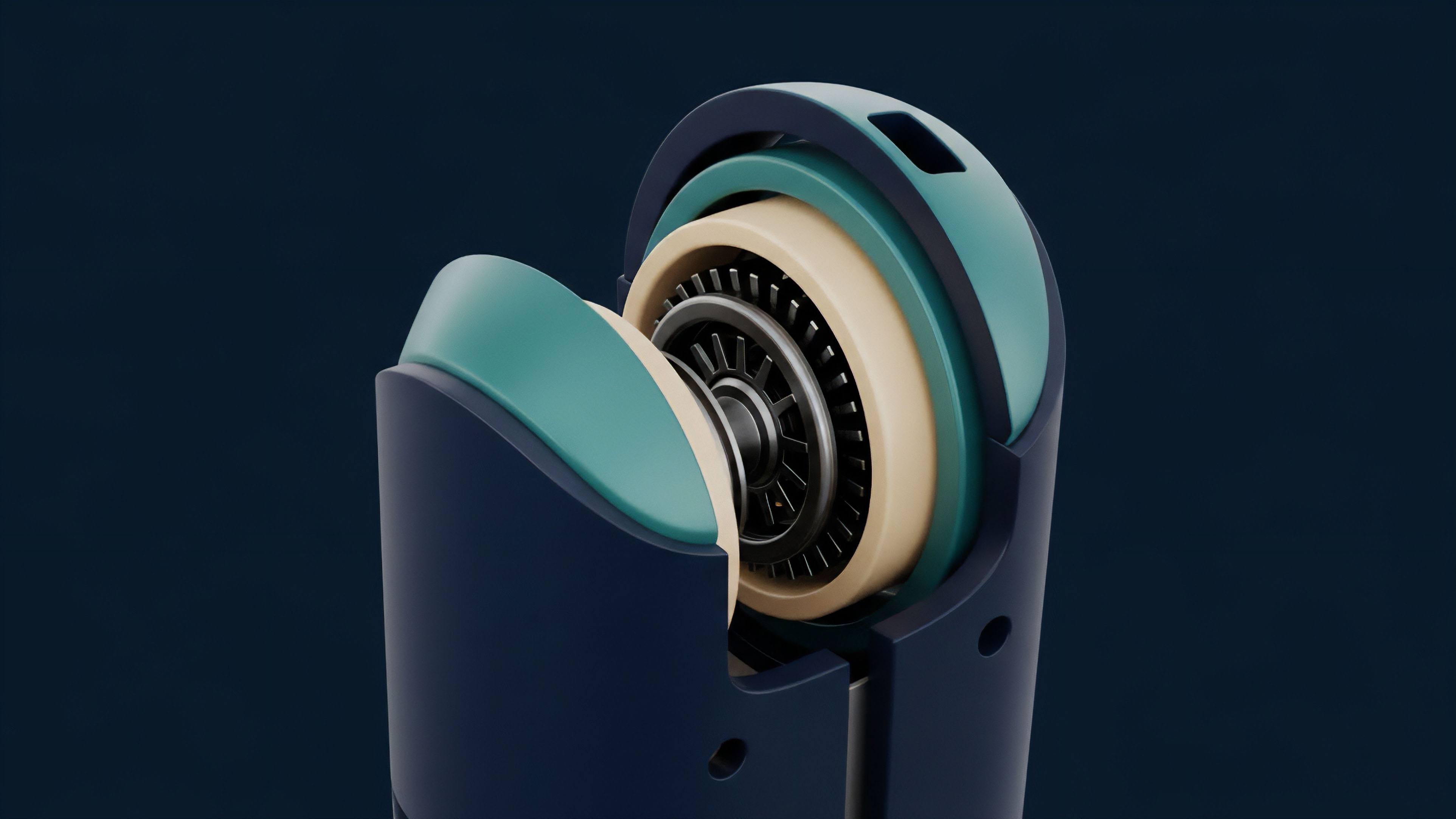
The central point of failure in most flash loan manipulations is the price oracle. Protocols need a reliable external data source to determine the value of assets held as collateral or to calculate liquidation thresholds. Vulnerable protocols often rely on a spot price oracle , which queries the price from a DEX at a single point in time within the transaction.
A flash loan attacker exploits this model risk by creating a temporary price spike or crash on the source DEX, knowing that the target protocol will read this manipulated value. The transition to TWAPs (Time-Weighted Average Prices) was an initial defense mechanism. TWAPs calculate the average price over a period of time, making it difficult to manipulate the price in a single block.
However, even TWAPs can be manipulated if the attacker controls enough liquidity or if the TWAP window is too short. The most robust solutions, like Chainlink’s decentralized oracle network, aggregate data from multiple off-chain sources, making manipulation significantly more expensive and complex than a single-block flash loan attack.

Adversarial Game Theory and Systemic Contagion
Flash loan manipulation exemplifies a high-stakes behavioral game theory scenario. The attacker identifies a Nash equilibrium where exploiting the system yields a higher payoff than acting honestly. The cost of mounting the attack (transaction fees) is minimal compared to the potential profit.
The risk to the attacker is zero, as the transaction reverts if the exploit fails. This creates a powerful incentive structure for adversarial behavior. The systemic implication is that a vulnerability in one protocol (a weak oracle on a DEX) can create contagion risk for another protocol (a lending platform) that relies on it.
| Oracle Type | Vulnerability to Flash Loan Manipulation | Key Trade-Offs |
|---|---|---|
| Spot Price Oracle | High. Easily manipulated by single, large-volume trade within one block. | Simple implementation; high capital efficiency but extremely high risk. |
| TWAP Oracle (Short Window) | Medium. Manipulation requires sustained price impact across a short time window. | Better security than spot price, but still vulnerable to large-scale, coordinated attacks. |
| Decentralized Oracle Network (e.g. Chainlink) | Low. Aggregates data from multiple off-chain sources; manipulation requires compromising numerous nodes and data feeds. | High security; higher implementation cost and data latency. |
Approach
A typical flash loan manipulation attack follows a precise sequence of events within a single transaction block. The complexity of these attacks has grown significantly, moving beyond simple price manipulation to include more subtle forms of protocol logic exploitation. The steps outlined below represent a common pattern observed in successful exploits.

Attack Sequence
- Flash Loan Acquisition: The attacker initiates the transaction by requesting a flash loan for a large amount of capital (e.g. millions of dollars worth of a specific token) from a lending protocol. The loan is conditional on repayment within the same transaction.
- Price Manipulation: The borrowed capital is used to execute a large-scale trade on a decentralized exchange (DEX) where the target protocol sources its price feed. The attacker either sells a large amount of the token to depress its price or buys a large amount to inflate it. This action creates a significant price discrepancy between the manipulated DEX and other exchanges.
- Value Extraction: The attacker interacts with the target protocol, which uses the manipulated price from the DEX. For example, if the price was inflated, the attacker deposits a small amount of collateral at the artificially high price to borrow a much larger amount of another asset. If the price was deflated, the attacker might trigger liquidations of other users’ positions at an incorrect value.
- Arbitrage and Repayment: The attacker sells the newly acquired assets on a different exchange where the price has not been manipulated, locking in a profit. The original flash loan amount, plus interest, is then repaid to the lending protocol, completing the atomic transaction.
The attacker’s goal is to exploit a design flaw in the target protocol’s economic logic by temporarily distorting its view of reality through price manipulation.
Sophisticated Exploits and Derivative Manipulation
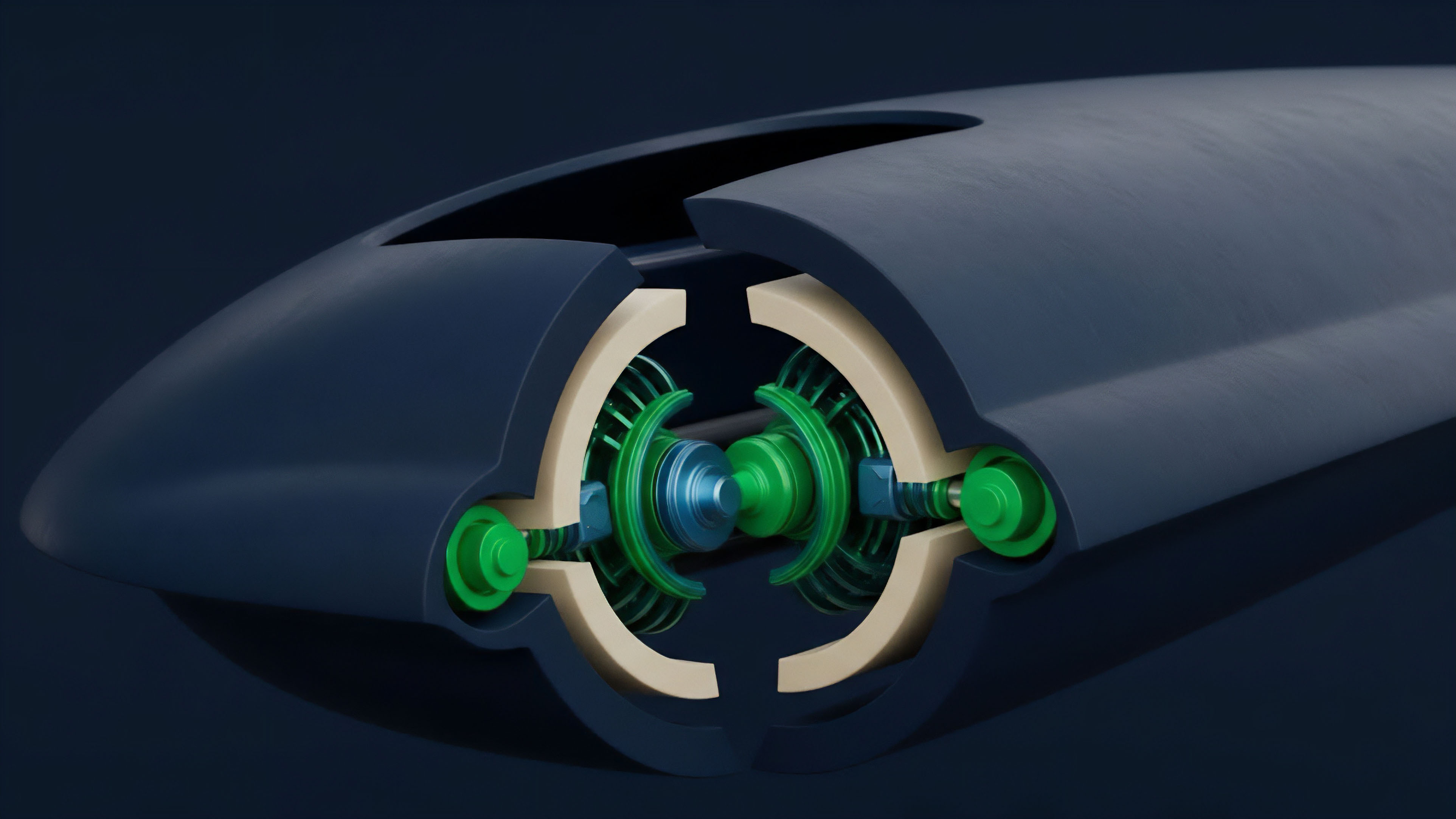
The attack surface has broadened beyond simple lending protocols. More advanced flash loan manipulations target derivative protocols and options vaults. In these scenarios, the attacker manipulates a key variable used in the options pricing model.
For example, by temporarily changing the asset price, the attacker can affect the calculation of implied volatility or the value of options collateral, allowing them to mint options at an artificially low price or redeem them at an inflated value. These attacks often require a deeper understanding of quantitative finance models and how they are implemented on-chain, moving beyond simple price feeds to exploit more complex financial logic.
Evolution
Flash loan manipulation has evolved from a novel exploit to a sophisticated, multi-stage attack methodology.
The arms race between attackers and defenders has forced protocols to rethink their fundamental security assumptions, leading to a shift in market microstructure.

The Shift from Spot Price to TWAP to Decentralized Oracles
Early defenses focused on replacing spot price oracles with TWAPs. This required attackers to manipulate prices over a longer period, increasing the capital cost and making the attack more difficult to execute within a single transaction. However, attackers quickly adapted, finding ways to manipulate TWAPs by exploiting low liquidity pools or through more complex, multi-protocol attacks.
The current standard defense involves decentralized oracle networks (DONs) like Chainlink. DONs aggregate price data from multiple independent nodes and off-chain sources, making it prohibitively expensive to manipulate the price feed in real-time.

Exploiting Second-Order Effects
The next generation of flash loan manipulations moved beyond direct price manipulation to exploit second-order effects within protocol logic. This includes manipulating interest rate models in lending protocols, altering the calculation of funding rates in perpetual futures, or even influencing governance votes. For example, an attacker could use a flash loan to acquire enough governance tokens to pass a malicious proposal that changes protocol parameters in their favor, before repaying the loan and reverting the vote.
- Liquidity Provision Manipulation: Attackers target protocols where liquidity providers (LPs) are incentivized based on specific metrics. By using a flash loan to manipulate trading volume or price movements, an attacker can artificially increase their LP rewards before returning the capital.
- Options Vault Exploitation: More complex attacks target options protocols by manipulating the underlying asset price used to calculate option value. This allows the attacker to mint options cheaply and exercise them at a manipulated profit, exploiting a vulnerability in the Black-Scholes or similar models implemented on-chain.
- Cross-Protocol Arbitrage: The most advanced attacks involve a sequence of interactions across multiple protocols. An attacker might manipulate a price on one DEX, use that manipulated price to borrow assets on a lending protocol, and then use those borrowed assets to exploit a derivative protocol, creating a chain reaction of value extraction.
Horizon
Looking ahead, the future of flash loan manipulation and its defenses suggests a continuous escalation in complexity. The arms race will likely shift from basic price oracle security to a deeper understanding of protocol incentive structures and systemic risk modeling.

The Convergence of Derivatives and Oracle Design
The next frontier for defense involves on-chain volatility products and more sophisticated pricing models. Instead of simply relying on a price feed, protocols may begin to calculate risk based on real-time volatility data derived from on-chain options markets. This would create a dynamic risk assessment that automatically adjusts collateral requirements or liquidation thresholds based on market conditions.
The future of DeFi security requires protocols to move beyond simple price feeds to implement on-chain volatility modeling and dynamic risk assessment.
The Rise of Systemic Risk Mitigation
The primary lesson from flash loan manipulation is that composability creates systemic risk. A vulnerability in one protocol can propagate throughout the entire ecosystem. Future defenses will focus on systemic risk mitigation frameworks that analyze the interconnectedness of protocols.
This involves creating mechanisms that automatically pause interactions between protocols when a large price deviation is detected, or implementing circuit breakers that limit transaction size based on liquidity depth. The long-term solution lies in building protocols that are inherently resilient to single-block price volatility, ensuring that a protocol’s economic logic remains sound even under extreme stress.
The Adversarial Challenge to Market Microstructure
Flash loan manipulation fundamentally challenges our understanding of market microstructure in a decentralized context. It highlights the difference between on-chain and off-chain market dynamics. The attacker’s ability to create and exploit price discrepancies in a single block forces a re-evaluation of how liquidity, volatility, and price discovery function in a permissionless environment. The future will require protocols to move toward a more robust, multi-layered approach to security that integrates economic game theory directly into smart contract design.

Glossary

Market Contagion

Order Sequencing Manipulation

Price Oracle Manipulation Attacks

Economic Manipulation

Data Manipulation Prevention
Market Manipulation Resistance

Flash Loan Rebalancing

Flash Crash Impact

Flash Loan Protocol Evolution