
Essence
Financial Derivative Exploits represent the intentional subversion of automated market mechanisms within decentralized finance protocols to extract value through systemic manipulation. These actions target the fragile intersection where smart contract logic meets volatile market reality, forcing outcomes that deviate from intended economic design. Participants executing these strategies leverage information asymmetry, execution latency, or flaws in oracle data feeds to capture surplus liquidity at the expense of protocol stability.
Financial Derivative Exploits constitute the systematic extraction of value by manipulating the underlying logic and oracle inputs of decentralized financial protocols.
The primary objective involves forcing liquidations, triggering flawed pricing models, or draining insurance funds through synthetic order flow. This behavior highlights the adversarial nature of programmable finance, where the code serves as both the infrastructure and the primary attack vector. Understanding these exploits requires recognizing that decentralized markets operate as complex systems under constant stress from automated agents seeking to capitalize on architectural oversights.

Origin
The genesis of these vulnerabilities resides in the rapid transplantation of traditional financial instruments into permissionless environments without accounting for the absence of centralized circuit breakers.
Early decentralized exchange models relied on simplistic constant product formulas that ignored the reality of exogenous price discovery. As sophisticated options and perpetual swap protocols launched, the reliance on off-chain price feeds created a distinct class of systemic risk.
- Oracle Manipulation occurs when participants influence the price feeds that determine margin health and liquidation thresholds.
- Liquidity Fragmentation facilitates exploits by allowing attackers to move price across low-liquidity venues before impacting the main protocol.
- Execution Latency provides a window for front-running or sandwiching transactions that adjust derivative positions.
This evolution mirrors the historical progression of traditional market manipulation, yet the speed of execution and the irreversibility of smart contract settlement create a unique threat profile. Developers initially prioritized rapid deployment over rigorous stress testing of margin engines, leaving systemic gaps that adversarial participants identified with remarkable speed. The transition from simple token swaps to complex derivative structures amplified these risks, turning every architectural decision into a potential point of failure.

Theory
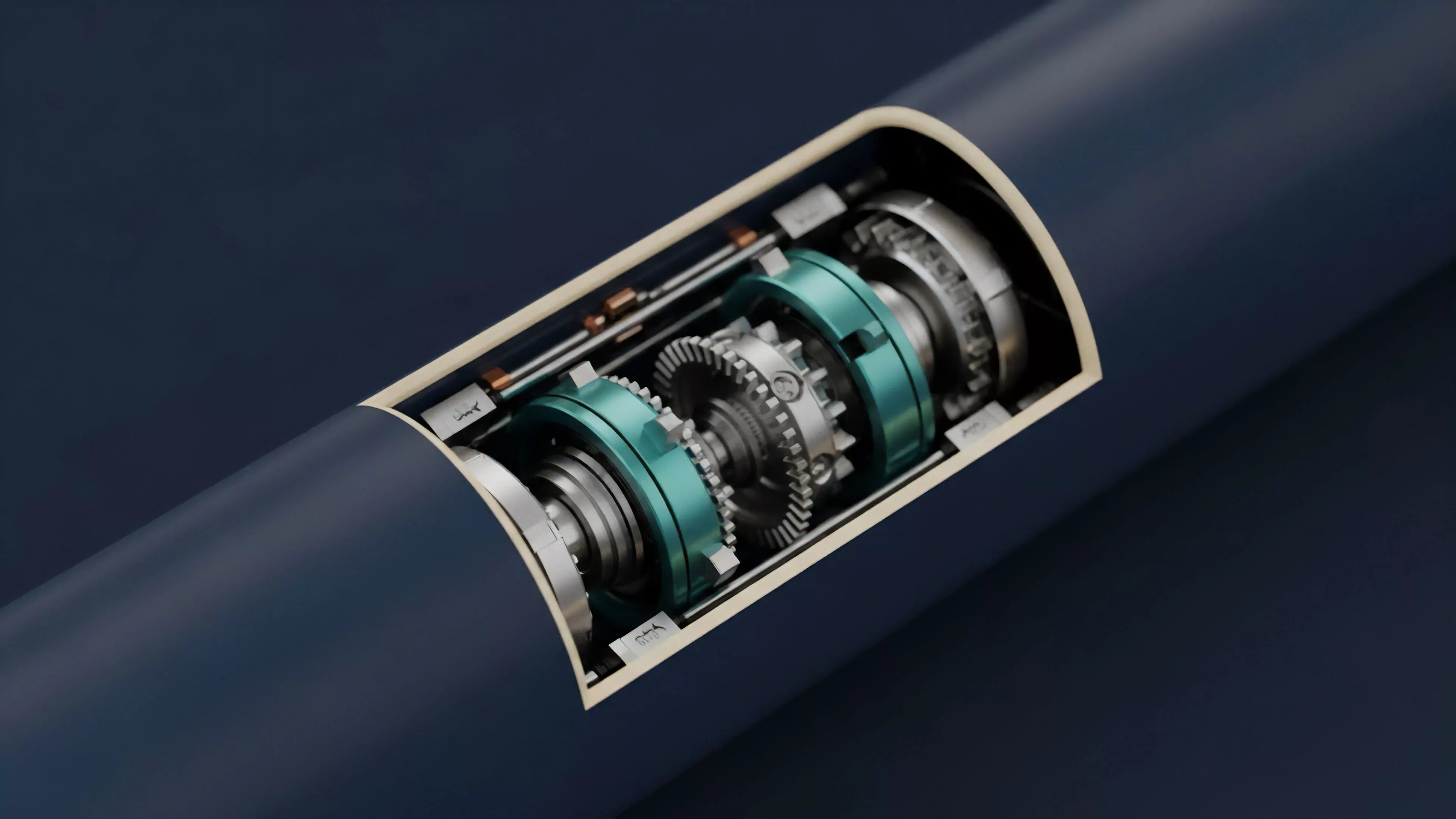
The mechanics of these exploits center on the failure of the Margin Engine to accurately reflect the true economic state of the protocol under high volatility.
When an asset experiences rapid price swings, the lag between decentralized oracles and on-chain settlement creates a divergence that attackers exploit to trigger mass liquidations. Quantitative models often assume continuous liquidity, a fallacy that ignores the discrete, block-based reality of blockchain transaction ordering.
Effective derivative design necessitates robust margin engines that account for discrete execution risks and oracle latency during periods of high volatility.
Behavioral game theory explains the strategic interaction between protocol participants. Attackers model the cost of manipulation against the potential profit from triggering liquidation cascades. If the cost to distort the oracle price is lower than the value captured from liquidated positions, the protocol becomes inherently unstable.
| Exploit Vector | Systemic Impact | Primary Mitigation |
|---|---|---|
| Oracle Lag | Incorrect liquidation pricing | Multi-source decentralized oracles |
| Slippage Manipulation | Synthetic margin calls | Volume-weighted average price |
| Flash Loan Attack | Immediate liquidity exhaustion | Circuit breakers and rate limits |
The mathematical modeling of these systems must incorporate the Greeks ⎊ specifically delta and gamma ⎊ under conditions of restricted liquidity. In traditional markets, market makers provide stability, but in decentralized derivatives, the market maker is often the protocol itself, creating a feedback loop where the system reacts to its own instability.

Approach
Current defensive strategies focus on hardening the Settlement Layer through multi-layered validation and real-time risk monitoring. Architects now implement sophisticated rate-limiting mechanisms and circuit breakers that pause activity when price deviation exceeds predefined thresholds.
This transition represents a shift from reactive patching to proactive, systemic risk management, acknowledging that code vulnerabilities are an inevitable feature of complex financial engineering.
- Risk Parameters define the boundaries for leverage, margin requirements, and asset volatility thresholds within the protocol.
- Liquidation Algorithms must incorporate dynamic penalties to prevent the exploitation of gas-dependent settlement processes.
- Insurance Funds serve as the ultimate backstop against cascading failures when collateralization ratios drop below critical levels.
Market participants now utilize specialized monitoring tools to detect anomalous order flow before it impacts the protocol. This environment demands a high degree of quantitative rigor, where protocol health is measured by the resilience of its liquidation mechanism rather than total value locked. The focus remains on maintaining protocol integrity despite the presence of adversarial agents who continuously test the limits of smart contract logic.
Evolution
The trajectory of these exploits has shifted from simple code bugs to sophisticated structural attacks that leverage the interplay between multiple protocols.
Initially, attackers focused on single-protocol vulnerabilities, such as flawed collateral calculation. The current landscape involves cross-protocol contagion, where an exploit in one derivative platform triggers liquidations across others, amplifying the systemic impact. Sometimes, one considers how these digital architectures mirror the chaotic self-organization observed in biological systems, where survival depends on the ability to adapt to sudden environmental shifts.
The market has moved toward decentralized risk management, where governance protocols adjust parameters in real-time to counter emerging threats. This evolution signifies a maturation of the space, moving away from experimental designs toward more resilient, battle-tested architectures.
Structural evolution in decentralized derivatives emphasizes cross-protocol resilience and real-time governance to mitigate systemic contagion risks.
| Development Phase | Focus | Risk Profile |
|---|---|---|
| Early | Protocol launch | Smart contract bugs |
| Intermediate | Margin scaling | Oracle manipulation |
| Current | Systemic resilience | Cross-protocol contagion |

Horizon
The future of decentralized derivatives lies in the development of Permissionless Clearinghouses that utilize zero-knowledge proofs to verify margin health without sacrificing privacy. This architectural shift will decouple the settlement layer from the execution layer, reducing the impact of oracle latency and transaction ordering manipulation. As protocols adopt more sophisticated, automated risk-mitigation frameworks, the ability to execute these exploits will diminish, favoring platforms with superior economic design. The next generation of derivatives will integrate predictive modeling directly into the protocol’s consensus mechanism, allowing for autonomous adjustment of margin requirements based on real-time market sentiment. This creates a self-healing financial infrastructure that treats volatility as an input rather than a threat. The ultimate goal remains the creation of an open financial system that provides the efficiency of traditional derivatives while maintaining the transparency and security of decentralized ledger technology.
