Essence
The Economic Security Margin (ESM) is a critical capital buffer within a decentralized derivatives protocol, designed to absorb systemic losses that extend beyond the capacity of standard maintenance margin and liquidation engines. This is the protocol’s self-insurance mechanism against what we call “Protocol Physics” failures ⎊ events that are technical and game-theoretic, not purely market-driven. The ESM exists to ensure the finality of settlement and the integrity of the collateral pool for all non-defaulting participants.
It is the capital layer that protects against the catastrophic, correlated failure of multiple mechanisms simultaneously: an oracle price feed lag coinciding with a liquidity crunch and a mass liquidation event. Without a robust ESM, a decentralized exchange faces the inevitability of a socialized loss, where the losses of one defaulting position are spread across all solvent users, destroying confidence and the protocol’s solvency. The calculation of this margin must account for the second-order effects of adversarial behavior, where a malicious actor seeks to profit not from a market prediction, but from the systemic failure of the protocol’s internal mechanisms.
The Economic Security Margin is the non-market capital buffer required to maintain protocol solvency against coordinated technical and game-theoretic attacks.

Systemic Risk Aggregation
The core challenge in sizing the ESM lies in aggregating risks that are typically modeled in isolation. A traditional derivatives counterparty risk model assumes a functioning market, but the ESM must account for the disruption of that market. This includes:
- Smart Contract Security: The potential loss from a vulnerability that allows a position to be under-collateralized or an oracle to be spoofed.
- Protocol Governance: The time delay required for a decentralized autonomous organization (DAO) to enact an emergency shutdown or parameter change, during which bad debt can accrue.
- Liquidity Black Holes: The risk that deep-in-the-money options cannot be hedged or liquidated due to sudden, correlated withdrawal of Automated Market Maker (AMM) liquidity.
Origin
The concept of a security margin that transcends simple financial risk has its roots in the failures of the centralized financial system, yet its modern application is a direct response to the unique vulnerabilities of on-chain finance. After the 2008 crisis, regulators acknowledged that individual counterparty risk models were insufficient; a systemic, interconnected risk existed. The ESM formalizes this lesson for the decentralized world.
Early decentralized finance (DeFi) protocols, operating with insufficient security buffers, experienced multiple instances of bad debt accumulation. These events often followed flash loan attacks that manipulated oracles, causing liquidations to execute at faulty prices. The resulting losses were then “socialized” across the remaining protocol users or required an emergency token issuance ⎊ a bailout ⎊ to recapitalize the system.
The Economic Security Margin was conceived as the pre-funded, algorithmic solution to this problem, removing the need for human or governance intervention during a crisis. It represents a paradigm shift from post-facto recovery to proactive solvency.
Historical Precedents
The need for a buffer against systemic failure is not new, but the mechanisms are.
- Long-Term Capital Management (LTCM) Lessons: The failure demonstrated how high leverage, combined with model-blind tail risk, can destroy capital far beyond theoretical Value-at-Risk (VaR) estimates.
- Decentralized Exchange Socialized Loss Events: These incidents proved that simple liquidation engines, designed for efficiency, cannot handle adversarial flash-loan-induced price manipulation, necessitating a deeper capital cushion.
- On-Chain Latency: The inherent delay between a trade executing and the on-chain price feed updating creates an exploitable gap that the margin system must account for as a fundamental, unavoidable risk.
Theory
The determination of the Economic Security Margin’s size is not a static percentage; it is a dynamically calculated value derived from a multi-factor risk model that extends well beyond the standard Black-Scholes and Greeks-based margin calculations. This framework requires a Stress Value-at-Risk (SVaR) methodology, where the loss distribution is intentionally skewed by incorporating protocol-specific technical risks and adversarial game theory. The true quantitative challenge lies in modeling the “Protocol Physics” of liquidation: the speed and efficiency of the liquidator bots, the gas costs that can halt liquidations during network congestion, and the potential for a “liquidation spiral” where collateral sales further depress the price, compounding the problem.
The ESM must cover all standard Greek exposures ⎊ δ, γ, ν, and ρ ⎊ under a simulated 5-sigma price shock combined with a liquidity exit, a scenario where the price-liquidity correlation is assumed to be perfectly negative. This is the moment where the pricing model becomes truly elegant ⎊ and dangerous if ignored ⎊ as it attempts to quantify the unquantifiable. The core calculation involves determining the maximum probable loss (MPL) over a specific settlement and intervention window, factoring in the time required for governance to act or a full protocol shutdown to be executed.
The ESM is the capital required to halt this spiral and absorb the resulting bad debt, essentially acting as a first-loss tranche funded by the protocol or a dedicated insurance fund, a necessary cost for achieving systemic resilience ⎊ the intellectual challenge here is to model the human element, the game-theoretic reality of adversarial behavior that seeks to exploit the precise moment the system is most stressed. The margin engine must not only account for market risk but also the cost of adversarial execution, which is an entirely different class of risk modeling, demanding a constant reassessment of the model’s assumptions against live network data.
A solvent decentralized options market requires the ESM to model the cost of a coordinated, adversarial exploit under conditions of maximum market stress.

Modeling Adversarial Execution
The Economic Security Margin must be calculated by running Monte Carlo simulations that factor in non-linear and non-stochastic variables.

Key Modeling Inputs
- Liquidation Slippage Cost: The estimated loss from forced collateral sales in a low-liquidity environment.
- Oracle Update Latency: The maximum time-weighted average price (TWAP) lag that can be exploited by a flash loan.
- Gas Price Spike Multiplier: A factor accounting for liquidator bot failure during periods of network congestion and high gas fees.
- Governance Time-to-Action: The minimum time required for a governance vote to pass and execute a protocol safety function.
Approach
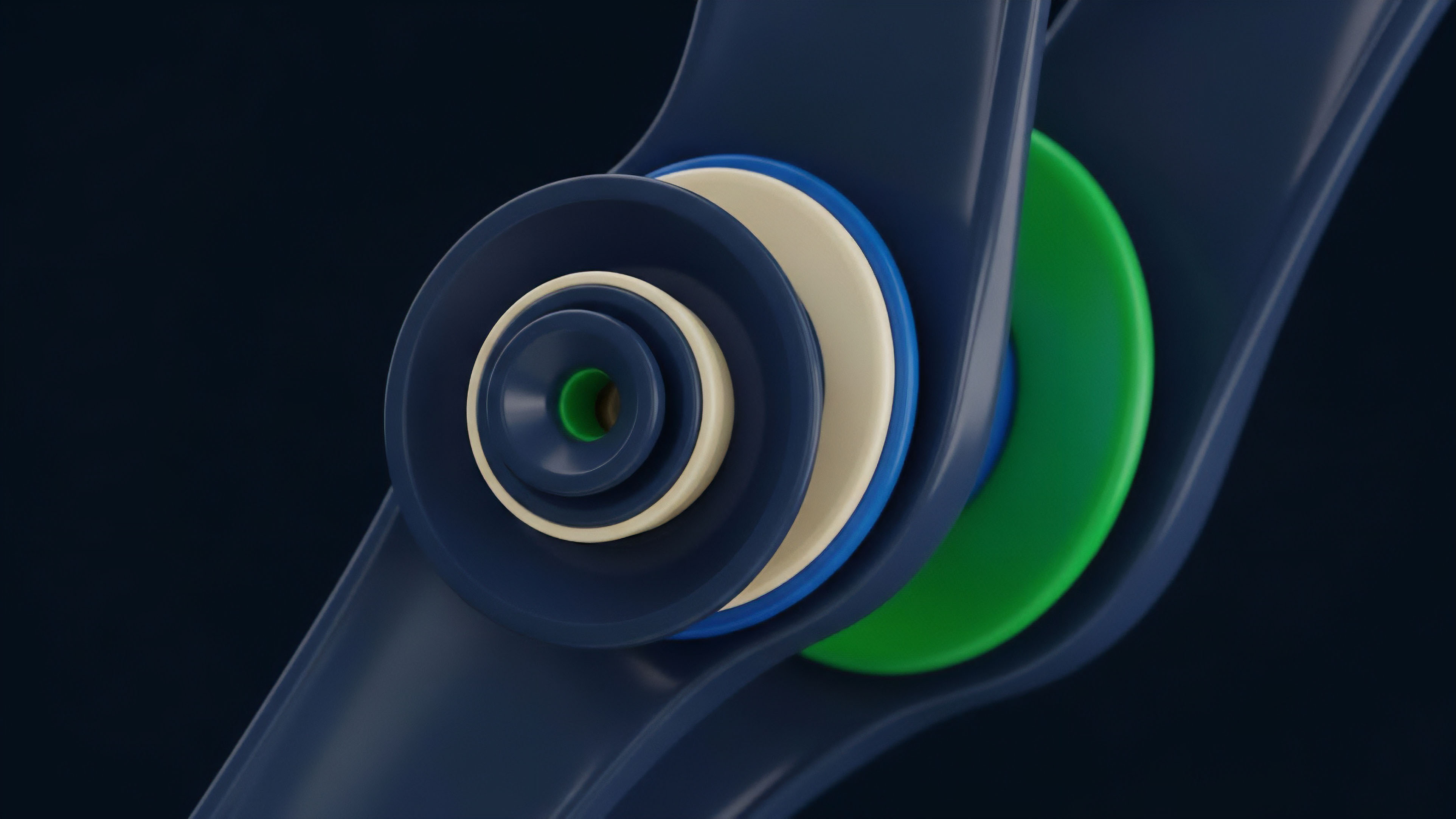
In practice, the Economic Security Margin is implemented through specific on-chain capital pools that are separate from user collateral. These pools are designed to be the last line of defense, recapitalized either through protocol fees, native token emissions, or a combination of both. The two dominant architectural approaches for implementing the ESM are the dedicated Insurance Fund and the Staked Safety Module.
| Mechanism | Capital Source | Recapitalization Method | Primary Drawback |
|---|---|---|---|
| Insurance Fund | Protocol Trading Fees, Liquidations Surplus | Ongoing fee accrual | Slow to scale; limited size in early stages |
| Staked Safety Module | Native Token Staking (with slashing risk) | Token emissions to stakers | Relies on native token value; potential for capital flight |
Capitalization Inputs
The dynamic sizing of the ESM pool requires real-time data from both the market microstructure and the protocol physics layers. The system must constantly calculate the maximum bad debt exposure under a defined stress scenario.
- Aggregate Protocol Open Interest: The total notional value of all outstanding options contracts.
- Portfolio Stress Test VaR: The maximum loss potential of the aggregated protocol book under a 99.9% confidence interval, including a 30% volatility spike.
- Oracle Deviation Threshold: The calculated capital needed to absorb the loss from a price deviation event lasting the duration of the governance delay period.
Evolution
The evolution of margin systems in crypto finance marks a shift from centralized, opaque risk models to transparent, algorithmic security mechanisms. Early crypto derivatives platforms mimicked the TradFi model ⎊ centralized exchanges with segregated margin accounts and proprietary risk engines. The move to decentralized finance introduced two major breakthroughs that necessitated the ESM concept: algorithmic transparency and pooled security.
This transformation converted the margin requirement from a private counterparty risk calculation into a public good problem. The current stage of this evolution is characterized by a push toward systemic, cross-protocol security. A protocol-specific insurance fund is insufficient in an interconnected environment.
A single protocol failure can create cascading effects through shared liquidity pools and common collateral types. The industry is moving toward a unified risk ledger, where the capital backing the ESM is fungible and can be deployed to any integrated protocol experiencing a solvency crisis. This requires standardized risk parameters and a shared governance framework, a complex undertaking that tests the limits of decentralized coordination.
The shift from private counterparty risk to a public, pooled security layer defines the systemic importance of the Economic Security Margin in decentralized finance.
| Parameter | Traditional Finance Margin | Decentralized ESM |
|---|---|---|
| Risk Calculation | Proprietary, Centralized | Algorithmic, Transparent |
| Loss Absorption | Clearing House/Counterparty Capital | Pooled Capital/Staked Token Slashing |
| Focus | Default Risk | Systemic & Protocol Risk |

Horizon
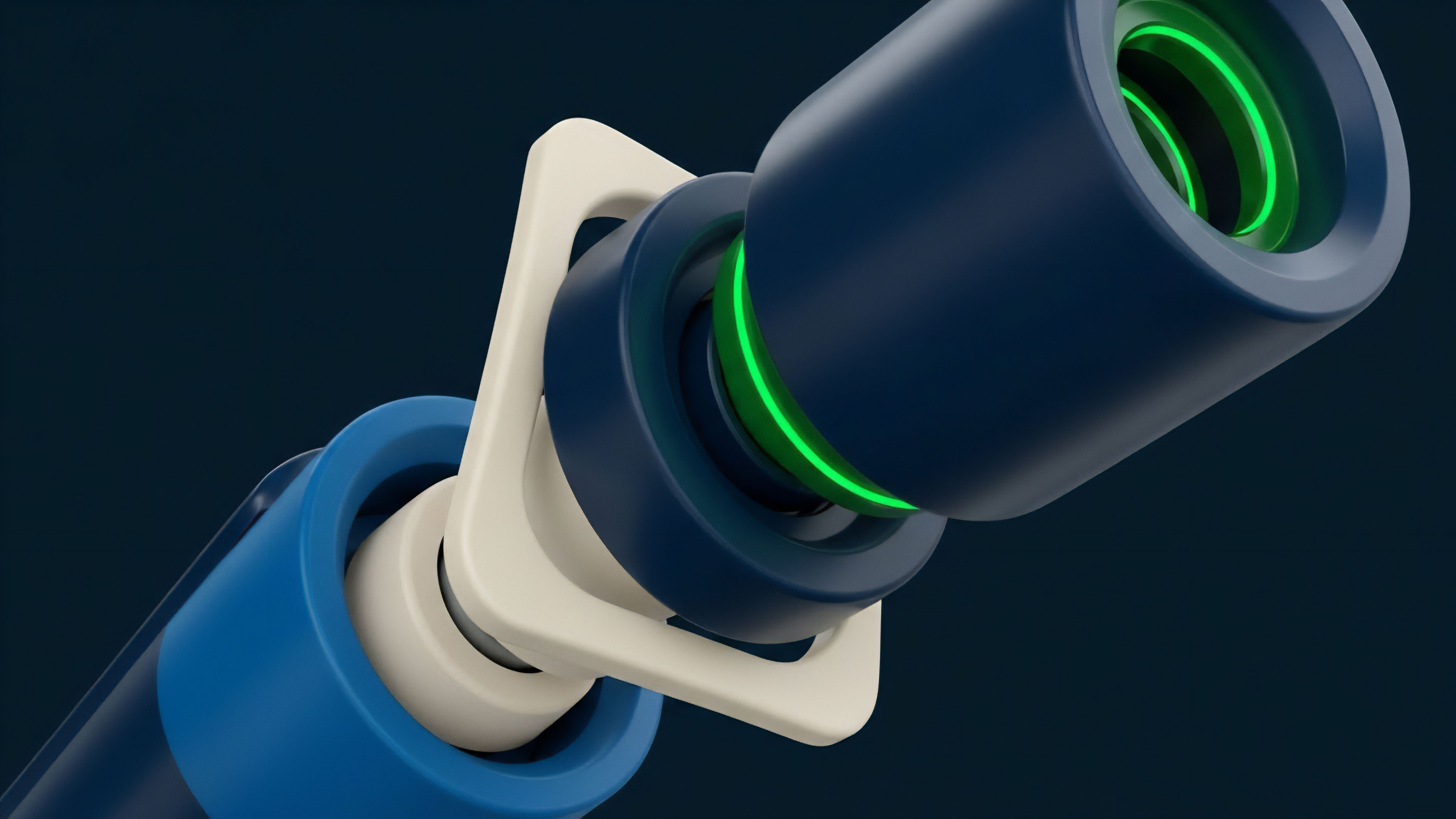
The future of the Economic Security Margin is inextricably linked to the interoperability of the wider crypto ecosystem. As options markets span multiple chains and layer-two solutions, the protocol-specific ESM becomes obsolete. We are moving toward a “Super-Sovereign” security layer, a decentralized reinsurer that can absorb losses across multiple independent virtual machines.
This pooled, systemic insurance market is the necessary endpoint for scaling decentralized derivatives. The greatest challenge on the horizon is the regulatory convergence. Global regulatory bodies, focused on systemic stability, will inevitably translate the technical concept of ESM into a legal mandate.
This will force protocols to standardize their risk modeling inputs and minimum capital requirements, effectively bridging the gap between on-chain risk parameters and off-chain financial compliance. Protocols that can demonstrate a robust, auditable ESM will hold a significant competitive advantage, as they offer the institutional-grade security necessary to onboard vast pools of capital. The next generation of ESM will feature automated, conditional governance triggers ⎊ a “circuit breaker” written into the smart contract that automatically increases the margin requirement or halts trading based on real-time stress test failures, removing human discretion entirely from the most critical security decisions.

Future ESM Components
The next phase of ESM development will focus on three core areas.
- Cross-Chain Solvency Module: A unified staking pool secured by a bridge mechanism, allowing collateral to be instantly deployed to cover bad debt on any connected chain.
- Adversarial Simulation Oracles: Decentralized networks that continuously run worst-case scenario simulations, updating the ESM requirement in real time based on observed gas prices, oracle latency, and open interest growth.
- Dynamic Fee Allocation: A mechanism that automatically redirects a higher percentage of trading fees into the ESM pool when the calculated risk coverage ratio falls below a predefined threshold.

Glossary

Market Security
Network Security Monitoring

Protocol Security Incident Response Procedures

Circuit Security
Smart Contract Security Challenges
Economic Exploit Prevention
Decentralized Exchange
Blinding Factor Security

Decentralized Protocol Security Architectures