Essence
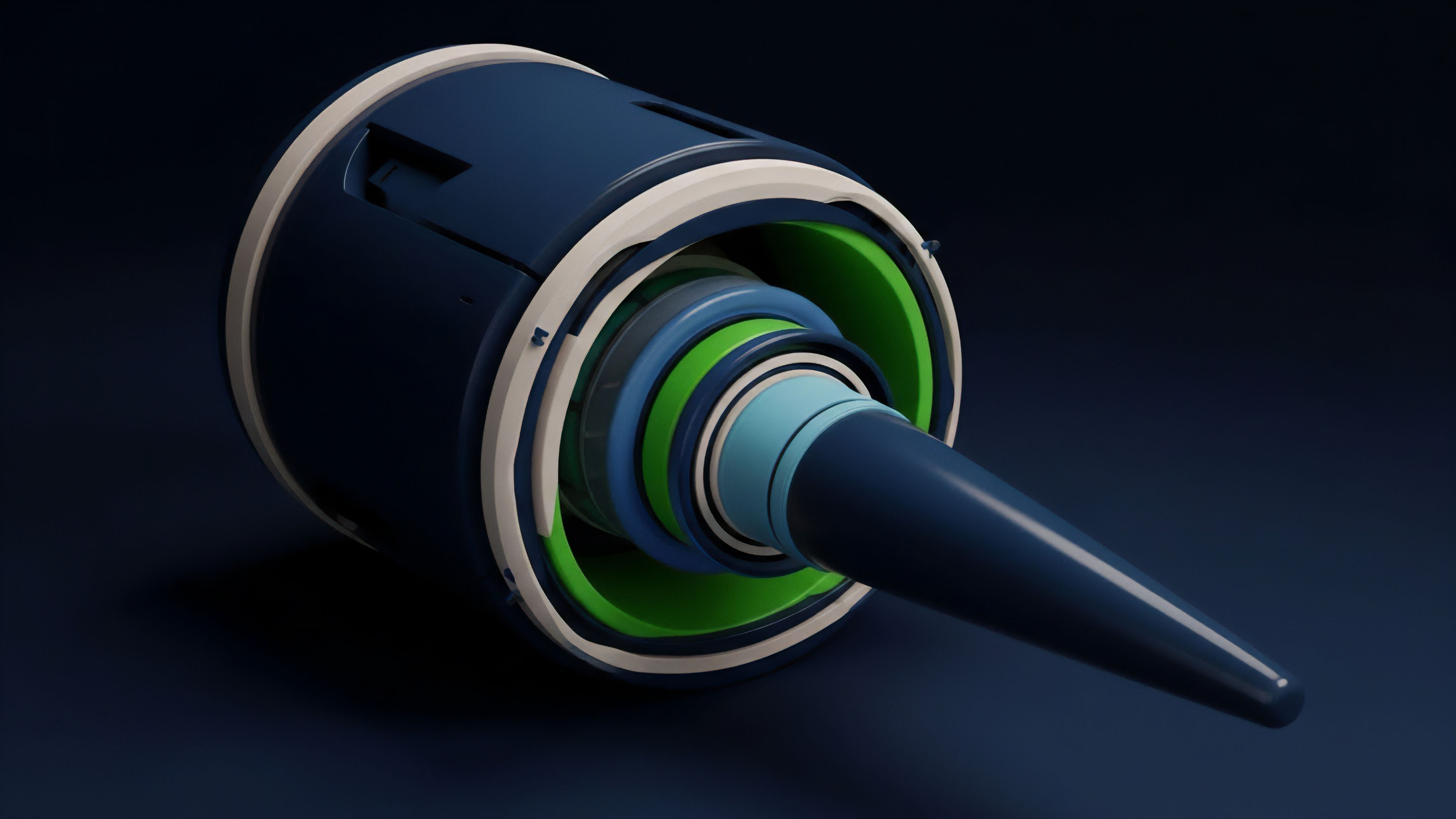
The central challenge in decentralized derivatives is the trilemma of transparency, capital efficiency, and user privacy. Traditional financial systems solve solvency through opaque, centralized clearing houses that audit all positions ⎊ a model antithetical to the ethos of decentralized finance. The Dynamic Solvency Proofs (DSP) system resolves this by leveraging advanced cryptography to prove a portfolio’s financial state without revealing the underlying assets, liabilities, or individual positions.
This mechanism functions as a non-interactive, on-chain cryptographic audit of a margin engine’s health.
Dynamic Solvency Proofs are cryptographic primitives that assert a derivatives platform’s net capital exceeds its total liabilities at a specific point in time without disclosing any user-specific data.
DSP shifts the regulatory and market burden from continuous, full-disclosure collateral checks to intermittent, cryptographically verifiable assertions of solvency. It is a fundamental architectural upgrade to the market microstructure of decentralized options. The proof itself is a compact, computationally sound statement that the protocol’s aggregate Net Asset Value (NAV) surpasses the sum of all counterparty risk exposure, typically measured by the maximum theoretical loss under defined stress scenarios.
This approach allows a protocol to hold less aggregate collateral than a fully transparent, over-collateralized system would require, injecting a vital element of capital efficiency into the market. The very act of generating the proof becomes the clearing mechanism.
| Feature | Traditional CEX/Clearing House | Transparent DeFi (e.g. Over-collateralized AMM) | Dynamic Solvency Proofs (DSP) |
|---|---|---|---|
| Privacy | High (Centralized Secrecy) | Low (All data on-chain) | High (Cryptographic Obfuscation) |
| Capital Efficiency | Medium (Portfolio Margining) | Low (Max Over-collateralization) | High (Risk-based Proof) |
| Trust Requirement | High (Trust in Central Entity) | Low (Trust in Code) | Zero (Trust in Cryptography) |
| Audit Frequency | Intermittent (Manual/Internal) | Continuous (Public Ledger) | Dynamic (Threshold or Time-based Proof Generation) |

Origin
The concept finds its genesis not in finance, but in the computer science domain of Zero-Knowledge Proofs (ZKP) , specifically the work on interactive and non-interactive proof systems that began with Goldwasser, Micali, and Rackoff in the 1980s. The financial application only became viable with the maturation of succinct non-interactive arguments of knowledge ⎊ ZK-SNARKs and ZK-STARKs ⎊ which allow a prover to construct a proof in a reasonable time and a verifier to check it almost instantly. The immediate predecessor to DSP was the application of ZKP technology to privacy-preserving layer-one and layer-two solutions ⎊ protocols that needed to prove the validity of state transitions without revealing the transaction contents.
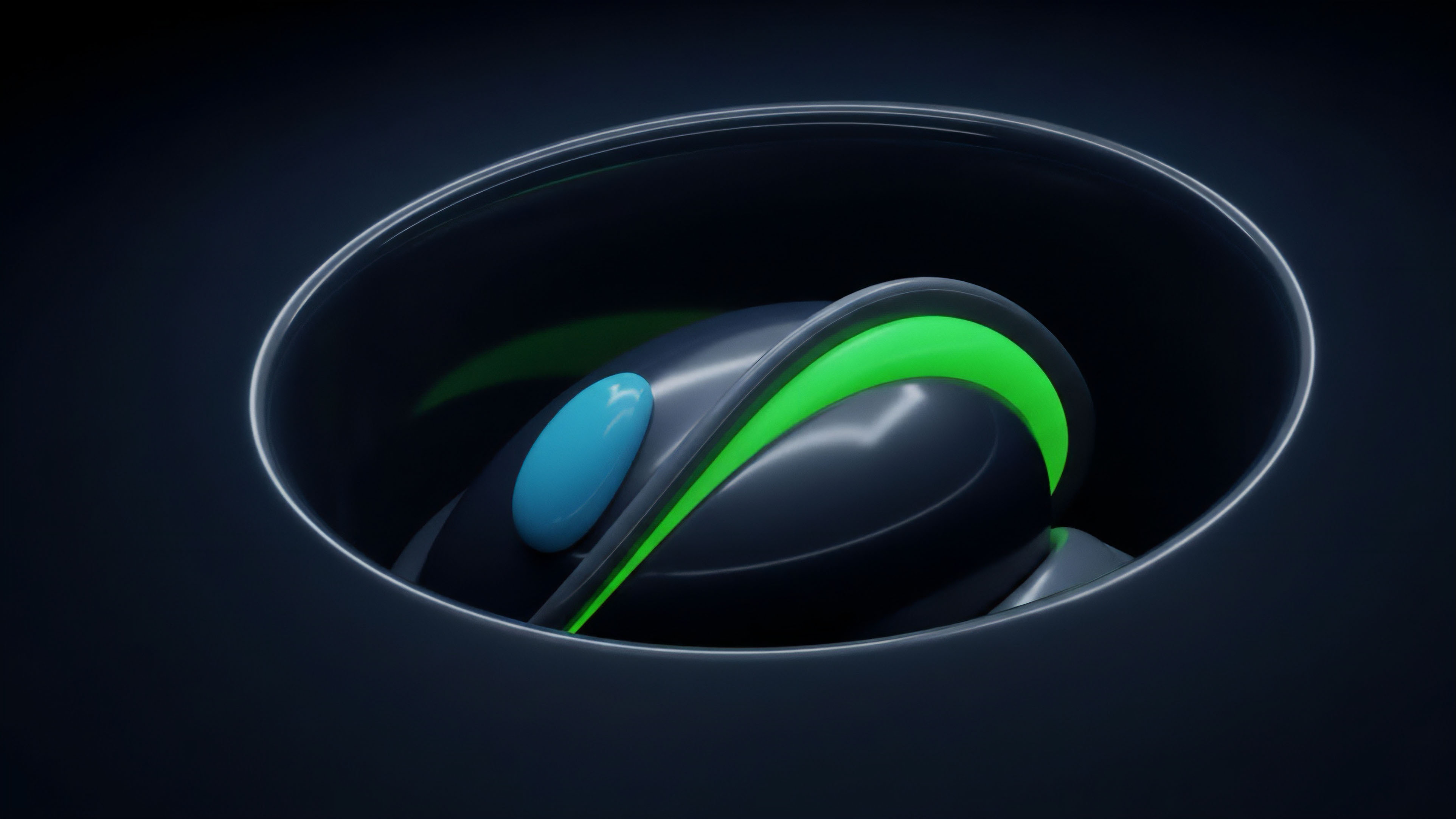
The logical extension was to treat a derivatives platform’s margin engine as a complex, private state machine. The system’s ‘state’ is the sum of all user positions and collateral, and the ‘transition’ is the calculation of whether that state is solvent. This is a subtle, yet profound, shift in perspective: treating the financial system itself as a cryptographic circuit.
The initial attempts at decentralized options clearing were hamstrung by the need for full transparency, which made sophisticated strategies like portfolio margining ⎊ where a short call is offset by a long call ⎊ impossible without revealing the entire strategy to the public ledger. The market demanded privacy for alpha generation, but the system required transparency for systemic risk management. DSP is the cryptographic bridge that spans this gulf, drawing directly from the architectural blueprints of privacy-focused computation.

Theory
The theoretical foundation of DSP rests on translating the complex, continuous-time solvency equation of a derivatives book into a discrete, finite field arithmetic circuit. The core mathematical statement the proof circuit must verify is the following inequality:
- Net Asset Value (NAV) Commitment: The sum of all user collateral commitments must be greater than or equal to the total liability commitment.
- Liability Aggregation: Total liability is not simply the current Mark-to-Market (MtM) value, but a worst-case scenario calculation. This requires a stress-test function, σi f(Positioni, Volatility, δ t), which typically incorporates the portfolio’s aggregated Greek exposures.
- Proof Generation: A prover generates a proof π such that Verify(Public Parameters, CommitmentNAV ge CommitmentLiability) = True.
The proving circuit is constructed to accept commitments to the user’s positions and collateral ⎊ the private inputs ⎊ and a set of public, protocol-defined risk parameters. This process demands a delicate balancing act, as the inclusion of options Greeks is computationally intensive. Our inability to respect the inherent complexity of the Black-Scholes or similar models within a finite field arithmetic is the critical bottleneck in current implementations ⎊ a deep philosophical problem of translating continuous reality into discrete computation.

Solvency Proof Variables
The dynamic nature of DSP is dictated by the variables that trigger a re-proof. These are typically market-driven and defined by the protocol’s risk engine.
- System-Wide Delta: The aggregate delta of the entire options book, which measures directional exposure. High absolute delta values necessitate more frequent re-proofs.
- Aggregate Vega Exposure: Measures sensitivity to volatility changes. As Vega increases, the risk of a sudden, unhedged volatility spike grows, demanding a fresh solvency check.
- Liquidity Thresholds: If the available collateral pool falls below a pre-set buffer, a re-proof is immediately triggered, irrespective of time.
- Time Elapsed: A base-layer constraint, ensuring a proof is generated at least once per epoch or block interval, guaranteeing a minimum audit frequency.
The computational complexity of a Dynamic Solvency Proof is fundamentally tied to the number of gates required to model the non-linear payoff structure of options and their sensitivity to market parameters.
| Parameter | Financial Rationale | DSP Role |
|---|---|---|
| σ δ | Systemic directional risk | Input to the stress-test function |
| σ Vega | Systemic volatility risk | Multiplier for collateral buffer calculation |
| Time-to-Expiry | Gamma/Theta risk profile | Factor in the liability commitment calculation |
| Historical Volatility | Reference for stress scenarios | Public parameter defining the liability floor |
Approach
The practical execution of DSP centers on the selection of the underlying zero-knowledge system. The trade-off is consistently between the succinctness of the proof and the computational cost of its generation.
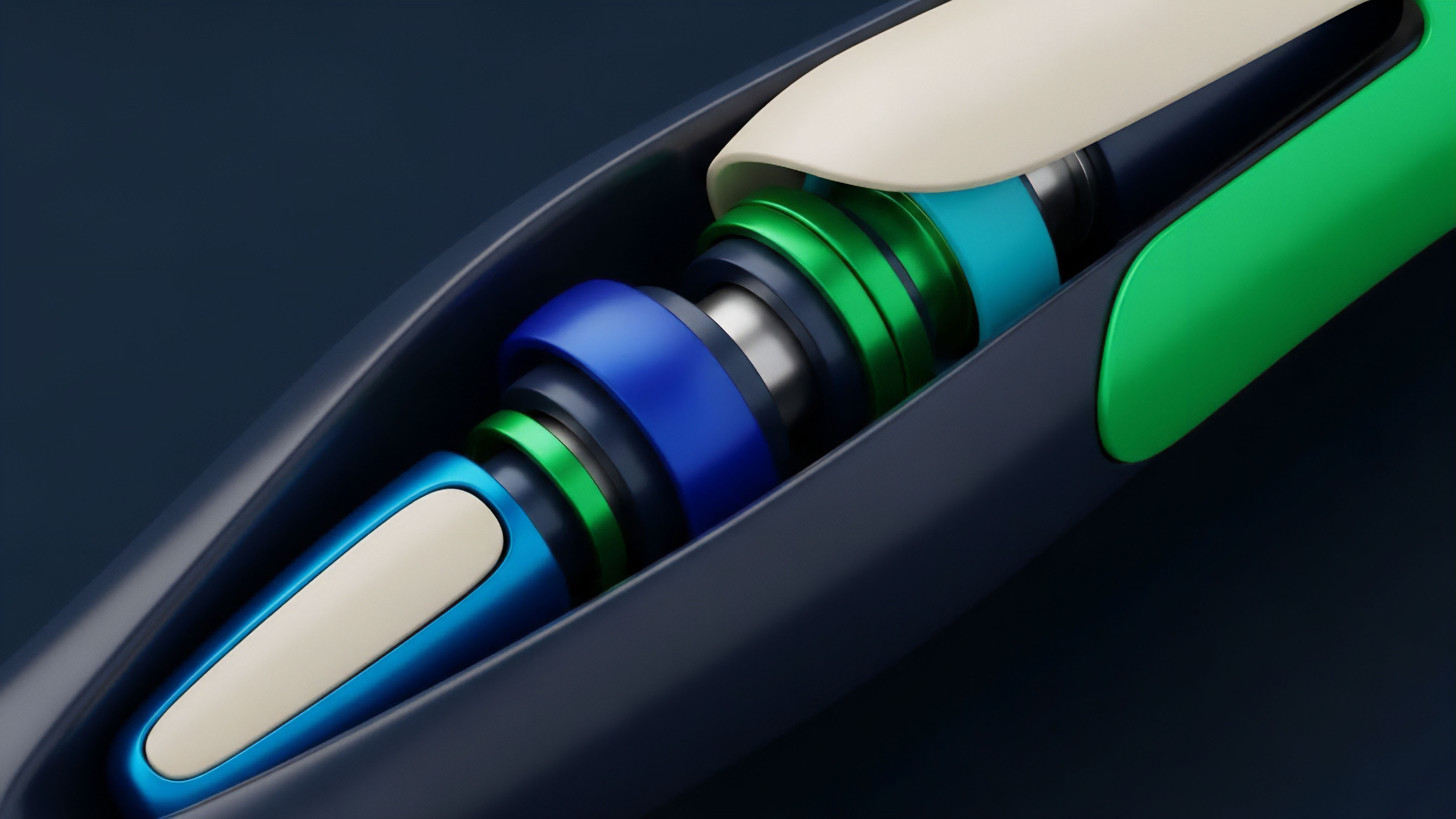
Proving System Selection
The choice between ZK-SNARKs and ZK-STARKs defines the performance profile of the derivatives clearing house. SNARKs yield extremely compact proofs and fast verification times, but require a trusted setup ⎊ a single point of failure that is philosophically problematic for decentralized systems. STARKs, conversely, are transparently setup, relying only on collision-resistant hash functions, but produce larger proofs and often take longer to verify on-chain.
| Feature | ZK-SNARK (e.g. Groth16) | ZK-STARK (e.g. Plonky2) |
|---|---|---|
| Proof Size | Small (Constant) | Large (Logarithmic) |
| Proving Time | Faster (For simple circuits) | Slower (Requires more computation) |
| Setup | Trusted Setup Required | Transparent Setup (No Trust) |
| Scalability | Lower (Less flexible circuit updates) | Higher (Easier to update the proving system) |
The prevailing strategy in advanced derivatives protocols leans toward ZK-STARKs or hybrid systems to eliminate the toxic dependency on a trusted setup, prioritizing systemic integrity over minor gas savings.
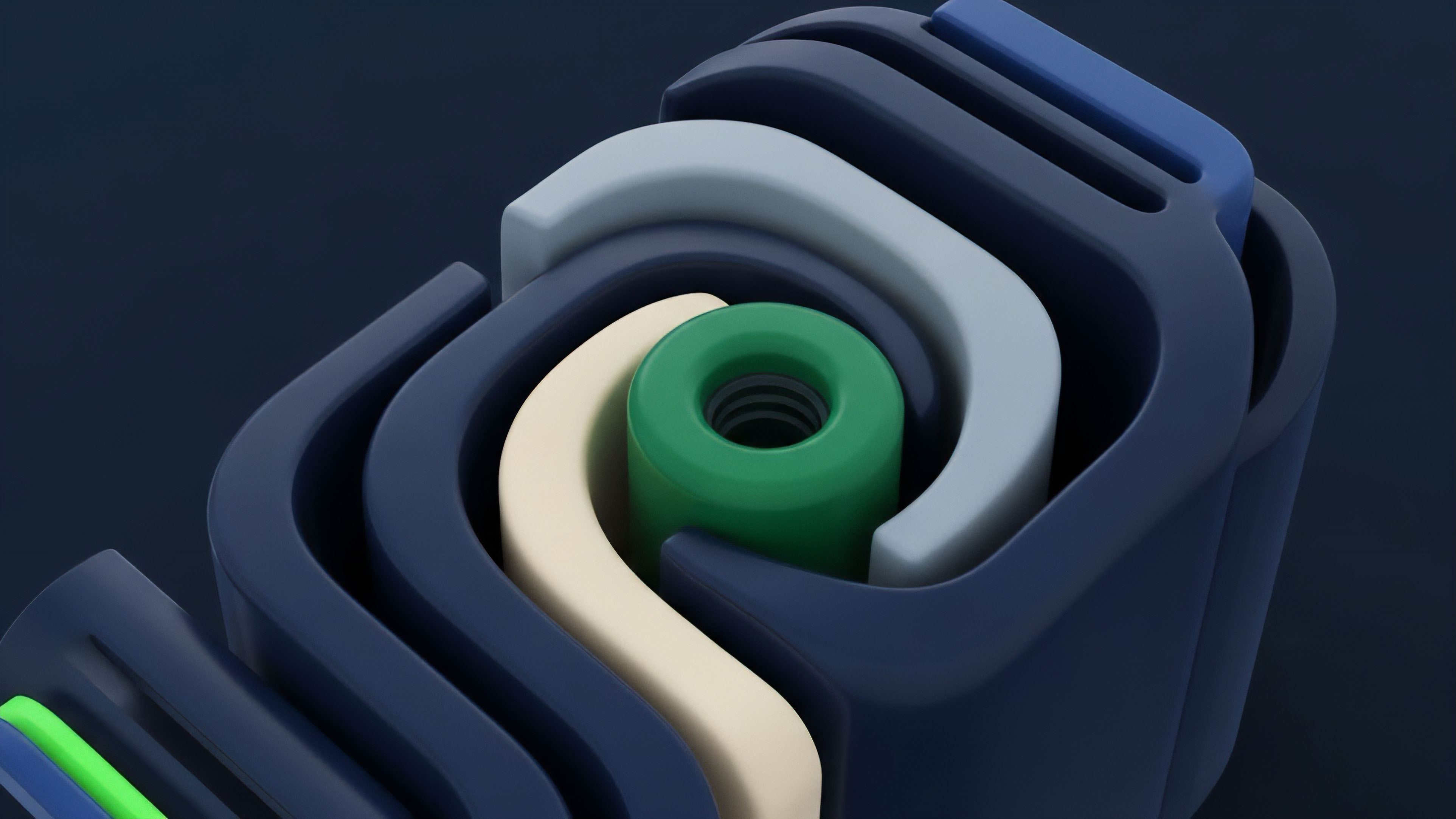
Dynamic Re-Proving Mechanisms
The ‘Dynamic’ element of DSP is instantiated through two primary mechanisms that dictate when the costly proof generation process is executed.
- Risk-Threshold Trigger: The protocol’s risk engine maintains a non-ZK, public estimation of the system’s risk buffer. When this buffer is breached ⎊ for instance, if the aggregate Vega exposure crosses a predefined limit ⎊ the smart contract mandates a full, cryptographic solvency proof.
- Adversarial Challenge Window: A game-theoretic layer where any market participant can post a bond to challenge the current solvency status. If the challenge is valid (i.e. the subsequent DSP reveals insolvency), the challenger is rewarded from the system’s insurance fund; if invalid, the challenger’s bond is slashed. This incentivizes continuous, external verification and creates a robust, economically-secured audit loop.
The dynamic nature of the proof system ensures that the high computational cost of zero-knowledge cryptography is only incurred when the system’s risk parameters indicate a genuine need for a full cryptographic audit.

Evolution
The path of DSP has moved from theoretical cryptographic papers to highly specialized, production-grade circuits. Early implementations were rudimentary, focusing only on proving the sum of collateral, which is a simple linear function. The true difficulty arose in attempting to encode the non-linear, path-dependent calculations of options pricing and risk management into a proof circuit.
The initial versions of DSP were essentially static solvency checks ⎊ a proof generated once a day. The current state is defined by the move to continuous, event-driven proving, which requires significant advances in hardware acceleration and specialized pre-compiles on the base layer. This is not a software problem; it is a fundamental hardware and cryptographic engineering challenge.

Implementation Challenges and Trade-Offs
The deployment of DSP presents several critical systemic trade-offs that systems architects must confront.
- Proof Latency: The time taken to generate a complex solvency proof can range from seconds to minutes. In a high-volatility event, this latency represents a systemic risk window where the public solvency statement is outdated.
- Gas Costs: Verifying a ZK proof on a public blockchain is computationally expensive, incurring high gas fees. This cost must be amortized across the platform’s trading volume or subsidized by a governance treasury.
- Circuit Complexity: Each time a new derivative product or a more sophisticated margining technique (like cross-margining) is introduced, the entire proving circuit must be redesigned, audited, and redeployed ⎊ a costly and risky undertaking.
The systemic implication of a flawed DSP implementation is not just a loss of funds; it is the instantaneous destruction of trust. If a proof is generated and verified as ‘True,’ yet the system subsequently collapses, the cryptographic assurances are rendered meaningless, and the damage to the entire decentralized finance project would be profound. This is why the engineering must prioritize safety and mathematical rigor over speed.
The market has a low tolerance for systemic failure masked by cryptographic opacity.
| Challenge Area | Systemic Risk Implication | Mitigation Strategy |
|---|---|---|
| Proof Generation Latency | Insolvency event occurs before re-proof completes | Hardware acceleration; use of state channels for interim proofs |
| Verification Cost | Unsustainable gas fees; centralization of prover nodes | Optimized ZK-STARKs; Layer 2 settlement; EIP integration |
| Circuit Audit Risk | Vulnerability in the financial logic of the circuit | Formal verification; public bug bounties on the circuit code |
Horizon
The future trajectory of Dynamic Solvency Proofs leads directly to the ultimate goal of decentralized finance: a fully trustless, non-custodial clearing house that rivals the capital efficiency of its centralized counterparts. This is the final frontier for derivatives architecture. The next generation of DSP will move beyond simply proving NAV ge Liability.
They will incorporate Contagion Proofs , which assert not only the solvency of the platform itself but also its interconnected risk with other protocols. This is critical for managing the systemic risk inherent in composable DeFi. A contagion proof would verify that the liquidation of a single large position, or the failure of a dependent lending protocol, would not cascade into the insolvency of the options platform.

Systemic Implications
The widespread adoption of DSP will fundamentally alter the structure of crypto options markets in three key ways.
- It will enable true Portfolio Margining in a non-custodial environment, allowing traders to net their risk across disparate positions without revealing their alpha-generating strategies to the public. This dramatically lowers the capital required to trade complex strategies.
- It will serve as a Regulatory Primitive , offering a compliance pathway for derivatives protocols. Regulators are primarily concerned with systemic risk and consumer protection; a DSP offers a verifiable, continuous, non-intrusive audit that addresses these concerns without requiring a back-door to user data.
- It accelerates the development of Cross-Chain Derivatives , where collateral on one chain can be cryptographically proven to cover liabilities on another, creating a unified, highly liquid global options pool.
The architectural mandate is clear: build systems that are not merely auditable, but that are mathematically self-auditing. DSP represents the shift from passive transparency to active, cryptographic assurance. The ultimate horizon is a financial system where the proof of solvency is not a document, but a constantly executing, computationally verified truth statement.

Glossary
Succinct Non-Interactive Arguments

Finite Field Arithmetic

Proof Generation

Economic Security Layer

On-Chain Verification Cost

Solvency Proofs
Proving System Selection

Capital Efficiency Primitive
Decentralized Finance