
Essence
Digital Asset Verification serves as the cryptographic anchor for decentralized financial integrity. It represents the procedural mechanism through which network participants confirm the validity, ownership, and state of a tokenized asset without reliance on centralized intermediaries. By leveraging proof-of-work, proof-of-stake, or alternative consensus architectures, this process ensures that every transaction adheres to the immutable rules defined by the underlying protocol.
Digital Asset Verification functions as the technical foundation for trustless settlement by cryptographically confirming asset state and ownership across decentralized ledgers.
The systemic relevance of this process lies in its ability to mitigate double-spending and unauthorized state transitions. In a landscape defined by adversarial actors, the verification layer acts as the primary defense against systemic insolvency. It transforms raw data into verifiable financial truth, enabling participants to interact with liquidity pools and derivative markets with a mathematically grounded expectation of security.

Origin
The genesis of Digital Asset Verification traces back to the fundamental challenge of maintaining a distributed ledger in a peer-to-peer environment.
Early attempts at digital cash failed due to the reliance on trusted third parties to prevent fraudulent duplication. The introduction of Bitcoin resolved this by embedding verification directly into the consensus mechanism.
- Cryptographic Hashing: The process of mapping data of arbitrary size to a fixed-size bit string, providing a unique fingerprint for every transaction.
- Merkle Trees: The data structure enabling efficient and secure verification of large sets of transactions within a block.
- Digital Signatures: The application of public-key cryptography to authenticate ownership and authorize asset movement.
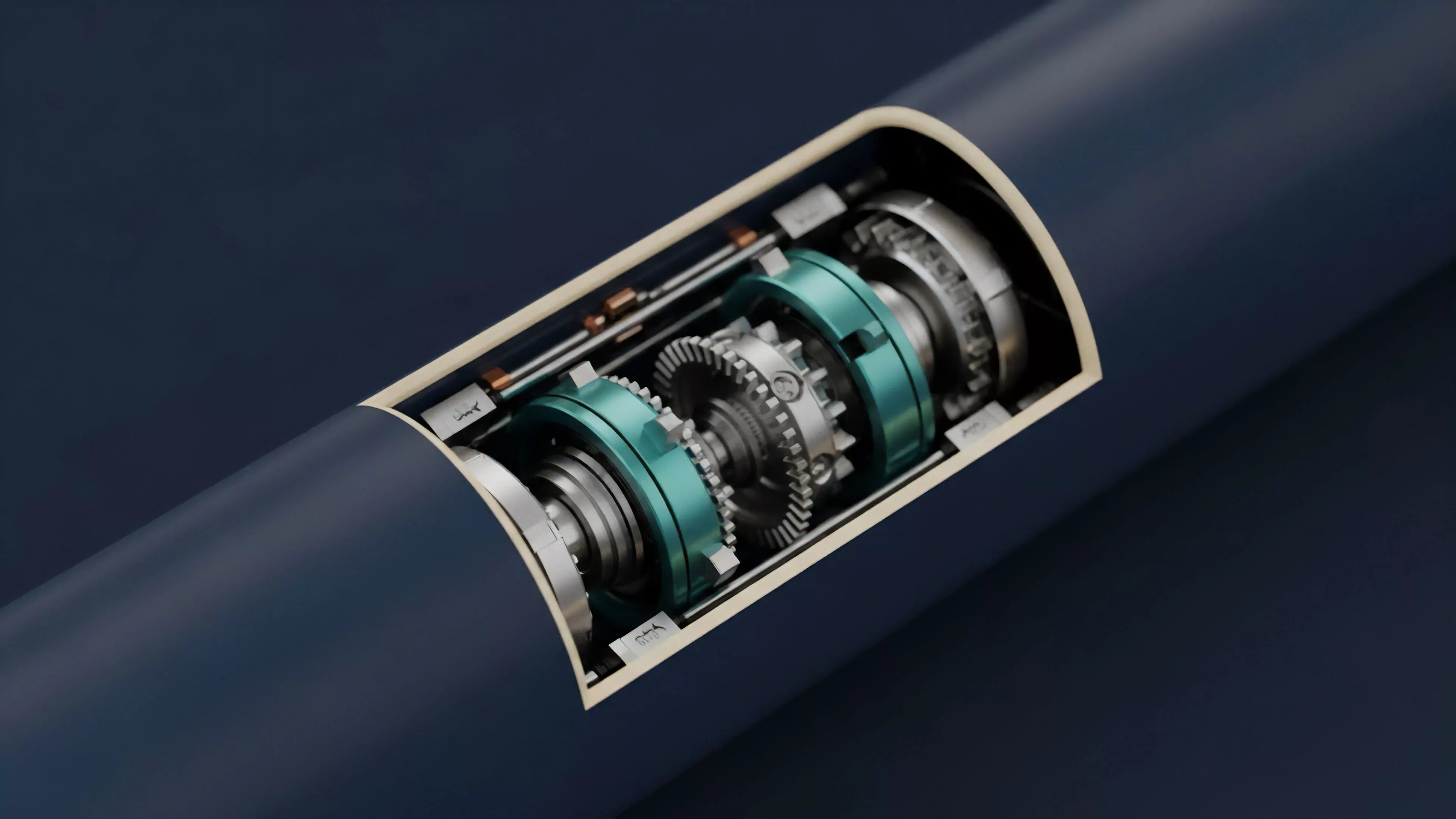
These components combined to create a self-correcting system where verification is not a peripheral task but the core product of network activity. The transition from simple value transfer to programmable smart contracts necessitated more complex verification layers, allowing protocols to confirm not just existence, but the fulfillment of arbitrary logical conditions.

Theory
Digital Asset Verification relies on the interaction between protocol physics and game theory. At the architectural level, the system must achieve a balance between security, scalability, and decentralization.
The verification overhead directly influences the throughput of the network, as every node must validate the history of state changes to ensure the current ledger remains accurate.
| Mechanism | Verification Metric | Systemic Risk |
|---|---|---|
| Proof of Work | Computational Hash Rate | 51 Percent Attack |
| Proof of Stake | Staked Capital Weight | Validator Cartelization |
| Zero Knowledge Proofs | Computational Validity | Proof Generation Latency |
The strategic interaction between validators and users creates a game-theoretic environment. Validators are incentivized to provide accurate verification to earn rewards, while malicious actors face economic penalties through slashing or lost block rewards. This alignment of incentives maintains the system under constant stress, as automated agents seek to identify and exploit minute discrepancies in state validation.
Verification theory dictates that the cost of challenging the ledger must exceed the potential gain from a successful fraudulent transaction to ensure system stability.
One might observe that the rigor of verification mirrors the evolution of physical infrastructure, where the strength of the foundation determines the height of the skyscraper. When the verification mechanism falters, the contagion risk spreads instantly across all derivative instruments anchored to the corrupted asset state.

Approach
Current implementations of Digital Asset Verification prioritize modularity and efficiency. Modern protocols utilize off-chain computation to reduce the load on the primary settlement layer.
This shift allows for higher throughput without compromising the security guarantees provided by the underlying consensus.
- Optimistic Rollups: These assume validity by default and only initiate verification upon a challenge, optimizing for speed in low-risk environments.
- Validity Rollups: These use advanced mathematics to produce succinct proofs that are verified instantly by the main chain.
- Cross-Chain Bridges: These require multi-party verification protocols to ensure assets remain locked on the origin chain while being utilized on a destination chain.
The current market environment forces a trade-off between the speed of settlement and the depth of verification. High-frequency derivative markets often require rapid, lightweight verification, whereas long-term collateral management demands absolute, high-assurance confirmation. This bifurcation drives the development of specialized verification layers tailored to specific financial instrument requirements.
Evolution
The trajectory of Digital Asset Verification has moved from monolithic, on-chain validation to sophisticated, multi-layered architectures.
Early protocols required every participant to verify the entire history, creating significant bottlenecks. The industry has since shifted toward partitioning the verification process, allowing for specialized roles such as light clients, full nodes, and sequencers.
The evolution of verification systems tracks the transition from rigid, monolithic consensus to flexible, modular architectures capable of handling massive throughput.
This shift has created new risks, particularly regarding the security of bridges and cross-chain messaging. As systems become more interconnected, the verification surface area expands, introducing points of failure that were not present in isolated networks. The future of this domain lies in formal verification of smart contracts and the automation of audit processes to detect vulnerabilities before they become exploitable systemic weaknesses.

Horizon
The next phase of Digital Asset Verification will be defined by the widespread adoption of hardware-accelerated zero-knowledge proofs.
By offloading complex cryptographic operations to dedicated silicon, networks will achieve near-instant verification times without sacrificing security. This advancement will enable institutional-grade derivatives platforms to operate with the same performance as traditional high-frequency exchanges.
| Future Trend | Impact |
|---|---|
| Hardware Acceleration | Reduced Proof Generation Time |
| Formal Verification | Reduction in Smart Contract Bugs |
| Autonomous Auditing | Real-time Security Monitoring |
The systemic goal is the creation of a global, verifiable financial substrate that is immune to localized failure. As verification becomes faster and more reliable, the distinction between decentralized and traditional finance will blur, leading to a unified market structure built on transparent, mathematically enforceable rules. The ultimate test remains the resilience of these verification layers during extreme market volatility and adversarial pressure.
