Essence
DeFi Security Landscape represents the totality of risk vectors, defensive protocols, and architectural safeguards governing decentralized financial instruments. This domain functions as the digital equivalent of an industrial safety standard, operating under the constraint that all financial logic resides within immutable, public-facing code. Every transaction, collateralization, and liquidation event exists within a transparent, adversarial environment where code logic dictates the distribution of value.
DeFi Security Landscape defines the operational safety parameters within autonomous financial systems where contract code dictates economic outcomes.
The core objective centers on maintaining protocol integrity against unauthorized state transitions. Participants engage with systems that lack traditional institutional intermediaries, shifting the burden of trust from legal entities to cryptographic verification and economic incentives. This transition creates a singular requirement for robust smart contract design, as system failures result in immediate, non-recoverable capital loss.

Origin
Early decentralized protocols operated with minimal regard for formal verification, prioritizing rapid deployment and feature expansion.
This period characterized by experimental, unoptimized code led to frequent, catastrophic exploits. Developers recognized the requirement for rigorous testing after witnessing the systemic collapse of initial liquidity pools due to reentrancy vulnerabilities and oracle manipulation. The transition toward formal security frameworks emerged from the realization that financial primitives require a higher standard than standard application code.
Historical failures provided the data needed to construct modern defense-in-depth strategies.
- Smart Contract Audits: Independent technical reviews identifying logic flaws before mainnet deployment.
- Formal Verification: Mathematical proofs confirming that contract code behaves according to specified parameters.
- Bug Bounty Programs: Incentivized disclosure mechanisms leveraging white-hat researchers to discover vulnerabilities.
This evolution demonstrates a shift from reactive patching to proactive, systemic engineering. Protocols now prioritize modularity and upgradability, allowing for security updates without compromising the underlying liquidity or governance state.

Theory
The architecture of DeFi Security Landscape relies on the interaction between game theory and formal logic. Protocols operate as autonomous agents, constantly responding to market-driven state changes.
The primary theoretical challenge involves balancing accessibility with extreme adversarial resilience.
Protocol Physics
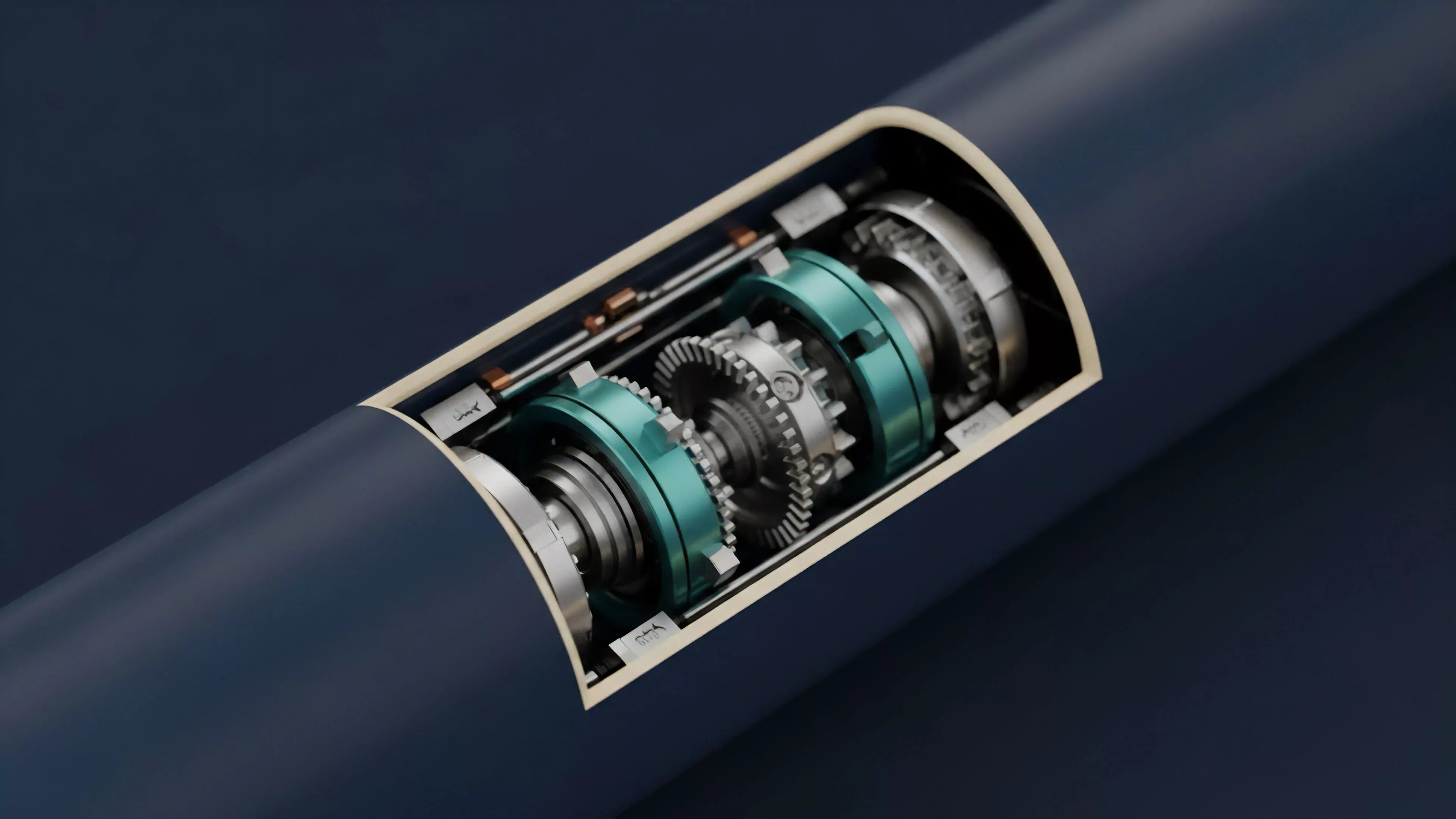
Consensus mechanisms define the finality of transactions, impacting how protocols handle liquidation events during periods of high network congestion. When a system relies on external price feeds, the security of those feeds dictates the validity of every collateralized position.
| Component | Primary Security Function |
| Oracle Networks | Ensuring accurate off-chain price ingestion |
| Governance Modules | Managing protocol parameters and emergency pauses |
| Liquidation Engines | Maintaining solvency during volatility |
Protocol security relies on the synchronization of external data feeds with internal contract logic to maintain accurate solvency ratios.
The mathematical modeling of risk involves calculating the probability of cascading liquidations under various volatility regimes. This requires precise Greeks-based analysis to understand how underlying asset price movements influence the stability of collateralized debt positions. A minor deviation in pricing data triggers systemic instability, as automated agents act to protect protocol health.
Occasionally, I observe that the rigidity of these systems mirrors the mechanical precision of early industrial clockwork ⎊ unforgiving, precise, and entirely dependent on the integrity of each gear. Returning to the mechanics, the interaction between governance token holders and protocol parameters introduces a layer of social risk that code cannot fully mitigate.

Approach
Current defensive strategies utilize a layered architecture to detect and respond to threats in real-time. Protocols implement automated monitoring tools that track abnormal transaction patterns, such as sudden, massive withdrawals or suspicious interaction sequences.
- Monitoring Agents: Systems tracking mempool activity for potential sandwich attacks or flash loan manipulation.
- Circuit Breakers: Automated mechanisms halting specific protocol functions when predefined risk thresholds are exceeded.
- Multi-Sig Governance: Distributed control structures requiring multiple independent signatures for critical parameter changes.
Risk management within these systems focuses on minimizing the blast radius of any single exploit. By compartmentalizing liquidity and implementing strict exposure limits, developers reduce the potential impact of a compromised module. This requires constant evaluation of the trade-off between capital efficiency and system safety.
| Strategy | Objective |
| Staged Rollouts | Limit initial capital exposure to new code |
| Immutable Timelocks | Provide transparency for governance changes |
| Liquidity Capping | Restrict total value at risk in unproven modules |

Evolution
Security practices have moved toward decentralization of the auditing process itself. The industry now emphasizes continuous monitoring rather than point-in-time assessments. Protocols incorporate real-time, on-chain analytics to detect anomalies, moving away from reliance on external centralized security providers.
Continuous on-chain monitoring represents the current standard for maintaining protocol integrity in volatile market environments.
Governance models have also matured, incorporating more sophisticated checks on proposal execution. The introduction of optimistic governance and specialized security councils allows for rapid response times without sacrificing the principles of decentralized control. These advancements reflect a broader recognition that security is an ongoing operational process rather than a static state.

Horizon
The future of DeFi Security Landscape lies in the integration of autonomous, AI-driven defensive agents capable of patching vulnerabilities in real-time. These systems will likely operate alongside human oversight, providing a secondary layer of protection against complex, multi-step exploits. The path forward requires the development of standardized, interoperable security protocols that allow different DeFi applications to share risk data. This will enable a more unified defense, where an exploit attempt on one protocol provides actionable intelligence to others. Ultimately, the industry must transition toward a state where security is inherently designed into the programming languages and virtual machines that power decentralized finance, reducing the reliance on external audits.
