Essence
Data Provider Incentives are the economic and cryptographic mechanisms designed to secure the integrity of external data feeds, specifically for decentralized applications (dApps) like crypto options protocols. In traditional finance, options markets rely on trusted, centralized data vendors and exchanges to determine asset prices for pricing and settlement. In decentralized finance, where trust is minimized and code dictates outcomes, this function is transferred to oracles.
The oracle problem is the fundamental challenge of securely importing off-chain information onto a blockchain. For options, this data integrity is non-negotiable. An options contract’s value is non-linear and highly sensitive to the underlying asset price, particularly near expiration.
A manipulated price feed allows a malicious actor to settle contracts in their favor, resulting in catastrophic losses for liquidity providers and counter-parties. The core function of these incentives is to create a game-theoretic environment where the cost of attacking the oracle system exceeds the potential profit from manipulating the options protocol. This requires careful design of staking requirements, reward mechanisms, and slashing conditions.
The incentives align the financial interests of the data providers with the overall security and stability of the options market.
Data Provider Incentives establish a game-theoretic equilibrium where the cost of data manipulation outweighs the potential profit from exploiting options contracts.
Without robust incentives, the options protocol operates on a foundation of sand. The protocol’s entire risk management framework ⎊ from margin calculations to liquidation thresholds ⎊ is built upon the assumption that the provided data accurately reflects reality. When data providers are incentivized correctly, they become active participants in the protocol’s security model, rather than passive, potentially vulnerable, third-party inputs.

Origin
The need for explicit data provider incentives arose directly from the vulnerabilities exposed during the early stages of decentralized finance. Before the development of sophisticated oracle networks, protocols relied on simplistic mechanisms, such as fetching data from a single, trusted source or using Time Weighted Average Price (TWAP) feeds. While a TWAP feed averages prices over a period to mitigate short-term price manipulation, it remains susceptible to flash loan attacks and prolonged manipulation, especially when the underlying liquidity source is shallow.
The critical turning point occurred with a series of exploits in early DeFi protocols. Attackers leveraged flash loans to manipulate the spot price on a decentralized exchange (DEX), then immediately executed a transaction against a lending protocol or options protocol that relied on that manipulated price feed for collateral valuation or settlement. The resulting losses demonstrated that a robust oracle system was not an optional feature but a core requirement for any financial primitive operating on-chain.
This led to the creation of dedicated oracle networks that moved beyond simple data provision to focus on security through economic guarantees. The shift in design philosophy from simple data feeds to incentive-driven networks represents a fundamental change in how decentralized applications approach risk. The original design assumption that data would be provided honestly by default proved flawed.
The current model acknowledges the adversarial nature of decentralized systems and implements a financial guarantee for data integrity.
Theory
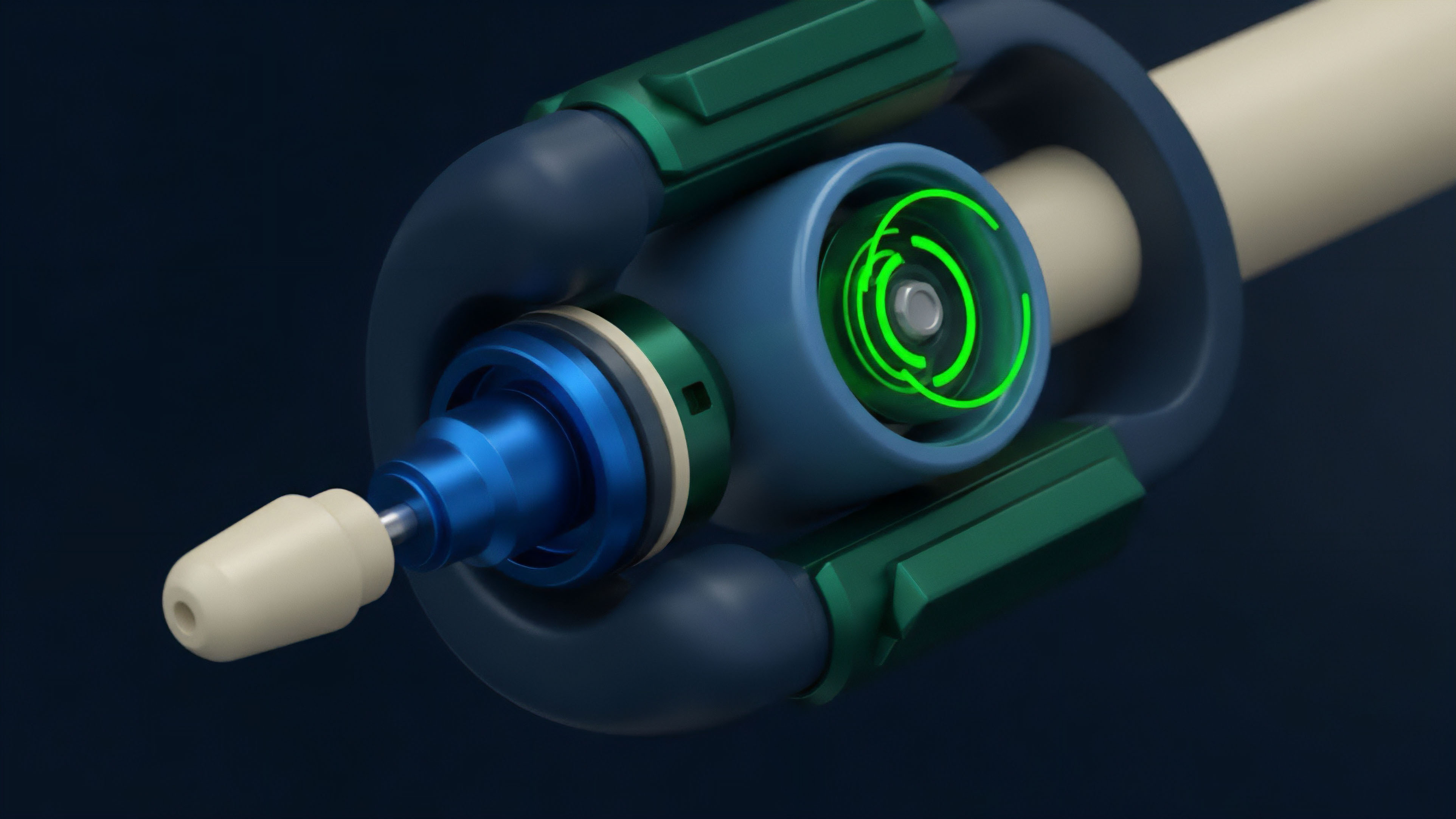
The theoretical foundation of Data Provider Incentives for options protocols rests heavily on mechanism design and game theory, specifically focusing on the cost-of-attack analysis. The core mechanism involves a staking and slashing model.
Data providers are required to lock up a significant amount of capital as collateral. This stake serves as a bond against malicious behavior.

Game Theory of Slashing
The incentive model operates on the principle that the potential financial loss from slashing must exceed the potential financial gain from manipulating the data feed to exploit an options contract. The value at risk (VAR) within the options protocol dictates the required size of the data provider’s stake. If an options protocol secures $100 million in value, the cost to corrupt the oracle must be significantly higher than $100 million.
This creates a disincentive for malicious actors, as the economic cost of the attack would result in a net loss. The system assumes that data providers are rational economic actors seeking to maximize profit, and the incentive structure aligns profit with honest behavior.

Data Aggregation and Consensus
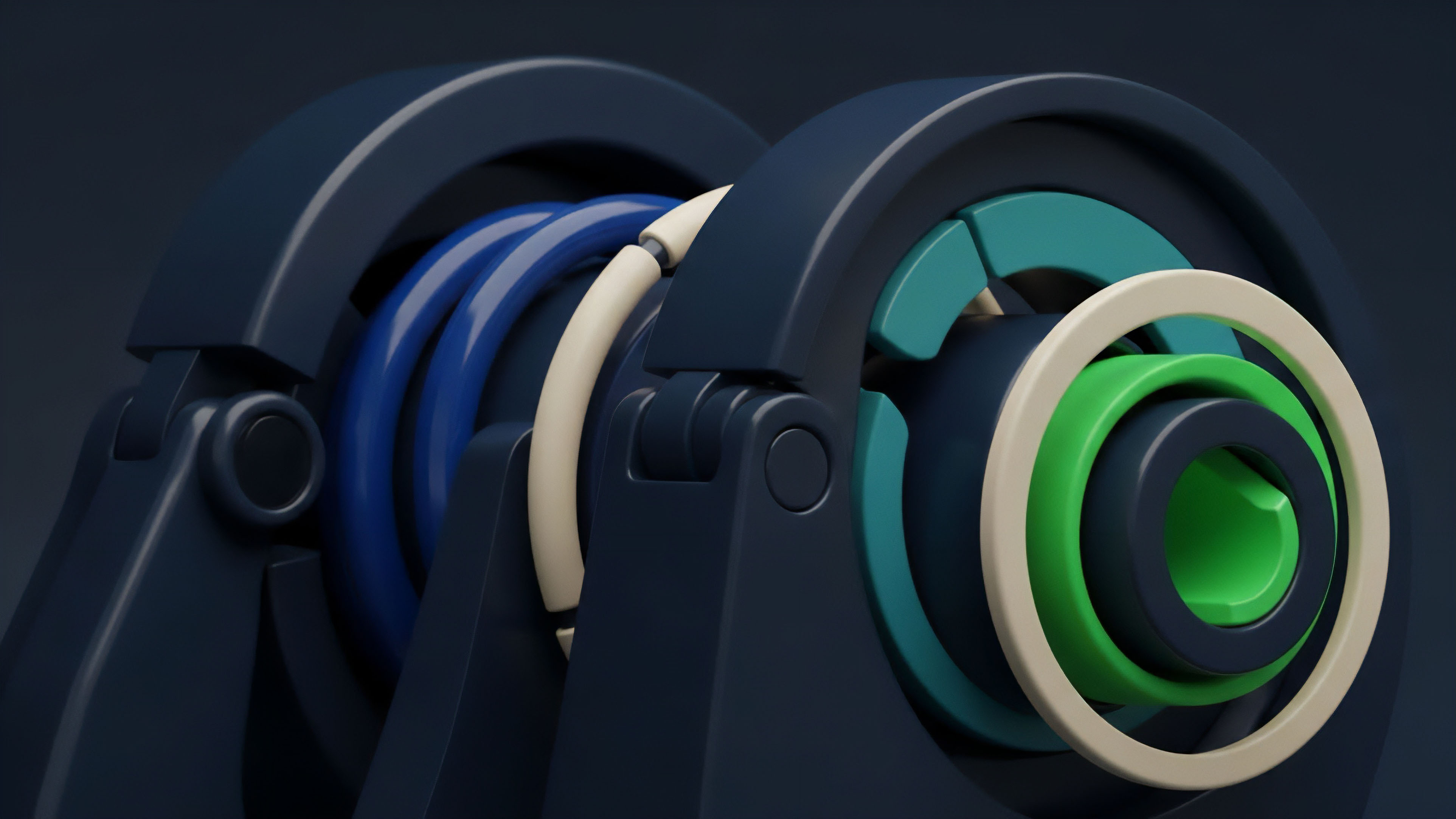
To mitigate the risk of a single point of failure, options protocols rarely rely on a single data provider. Instead, they utilize data aggregation. A protocol requests price data from multiple independent data providers.
The system then calculates a median or weighted average of these inputs. This consensus mechanism makes manipulation significantly more difficult, requiring an attacker to compromise a majority of the data providers simultaneously. The incentives ensure that each provider within the aggregation set reports truthfully to avoid being slashed for deviating from the consensus median.

Reputation and Selection Models
Advanced incentive models incorporate reputation systems. Data providers with a history of accurate reporting gain a higher reputation score, which may grant them access to more valuable data provision contracts and higher rewards. Conversely, providers who deviate from consensus are penalized, either by slashing or by having their reputation score reduced.
This creates a long-term incentive for honesty, as building a strong reputation allows providers to capture a greater share of the data market over time.
| Model Type | Security Mechanism | Latency Characteristics | Suitability for Options |
|---|---|---|---|
| Single Provider | Reputational trust, off-chain monitoring | Low latency, high speed updates | High risk, vulnerable to single-point-of-failure attacks |
| TWAP (Time Weighted Average Price) | Averaging over time window | Medium latency (time window dependent) | Vulnerable to prolonged manipulation and flash loans |
| Decentralized Aggregation (Staking/Slashing) | Economic incentives, consensus checking | Higher latency (consensus delay) | High security, suitable for high-value options markets |

Approach
The implementation of Data Provider Incentives for options protocols requires a specific architectural approach to balance security with the high-frequency demands of derivatives trading. The primary challenge for options is the need for both high-security guarantees and near real-time data delivery.

Real-Time Data and Latency
Options pricing models, especially those for short-term options, are highly sensitive to price fluctuations. The Black-Scholes model and its variations require accurate inputs for the underlying asset price and implied volatility. If the data feed is stale, the options premium calculated by the protocol will be inaccurate, creating arbitrage opportunities that drain value from liquidity providers.
The incentive structure must account for this by rewarding providers for timely updates and penalizing significant delays.

Cost of Attack Analysis
A critical step in designing the incentive structure is performing a detailed cost-of-attack analysis. This involves calculating the potential profit an attacker could make by manipulating the options market (e.g. through exercising options at a manipulated price) and setting the slashing penalty for data providers higher than that profit. This requires continuous monitoring of the protocol’s total value locked (TVL) and risk exposure.
The incentives are dynamically adjusted to reflect changes in market conditions and protocol usage.
The efficacy of data provider incentives in options markets is determined by a continuous cost-of-attack analysis that ensures the penalty for data corruption always exceeds the potential gain from market exploitation.

Options Specific Data Requirements
The data requirements for options go beyond a simple spot price. Options protocols need specific data points for accurate pricing and risk management:
- Underlying Asset Price: The current market price of the asset (e.g. ETH/USD) used for calculating option premiums and determining settlement value.
- Implied Volatility (IV): A measure of market expectations for future price movements. This is a crucial input for options pricing models.
- Time to Expiration: The time remaining until the option expires, which impacts time decay (theta).
Data provider incentives must be tailored to ensure the integrity of all these inputs, with specific mechanisms to prevent manipulation of volatility data.

Evolution
Data provider incentives have evolved significantly from simple price feeds to specialized data services. The initial focus was on securing basic spot prices, but the rise of complex derivatives, especially exotic options and volatility products, demanded a more sophisticated approach.

Volatility Oracles and V-Oracles
The most significant evolution for options protocols is the development of dedicated Volatility Oracles (V-Oracles). While standard price oracles provide the underlying asset price, V-oracles calculate and provide a real-time feed of implied volatility. Implied volatility is a complex input derived from market data, requiring specific calculation methodologies.
Incentives for V-oracles must be designed to ensure the integrity of this calculation, as manipulating IV can drastically alter option premiums.

MEV and Data Front-Running
The rise of Maximal Extractable Value (MEV) introduced new attack vectors. Data providers, or the block producers who include their data, can front-run liquidations or options settlements by manipulating the timing of data delivery. The incentive structure has evolved to mitigate this risk.
Mechanisms like delayed data feeds, or using aggregated feeds from a large number of providers, make it more difficult for a single actor to profit from data timing manipulation.
As decentralized finance matured, data provider incentives adapted to mitigate new attack vectors like MEV and flash loan manipulations, ensuring data integrity for complex financial products.

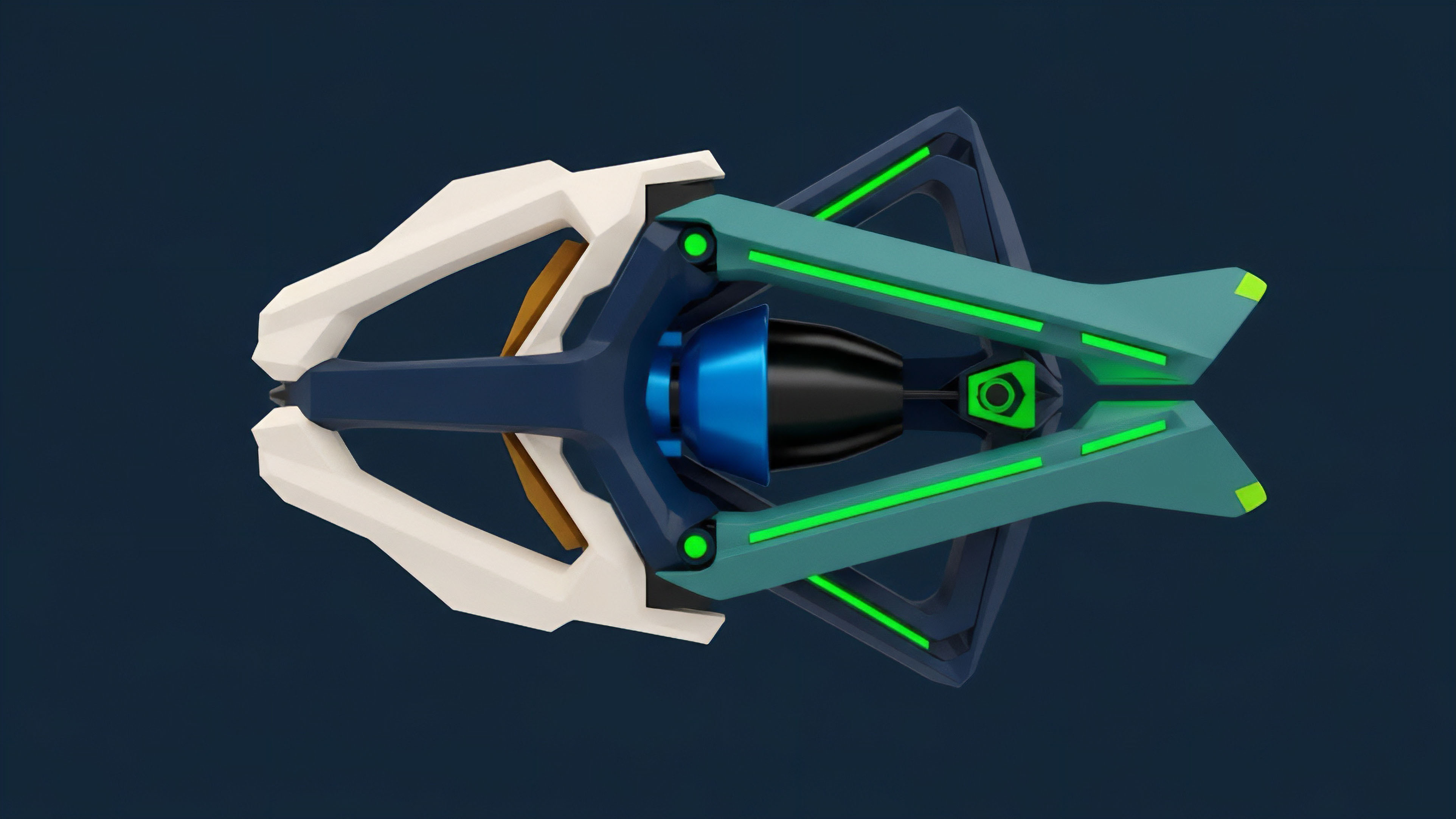
Decentralized Computation
The next step in incentive evolution involves moving beyond simple data feeds to decentralized computation. Instead of just providing raw data, some protocols are exploring models where data providers perform complex calculations (e.g. Black-Scholes pricing) on-chain before providing the result.
This approach reduces the computational burden on the options protocol itself and shifts the complexity of the calculation to the data providers, requiring incentives to ensure the calculation itself is performed correctly.
| Oracle Type | Data Provided | Incentive Focus | Key Risk |
|---|---|---|---|
| Price Oracle | Spot price of underlying asset | Preventing price manipulation at settlement | Flash loan attacks, single source failure |
| Volatility Oracle (V-Oracle) | Implied volatility (IV) calculation | Ensuring calculation methodology integrity | Calculation errors, data input manipulation |

Horizon
Looking forward, the evolution of data provider incentives for crypto options points toward greater specialization and interoperability. The next generation of options protocols will demand more granular and specific data feeds than simple price information.

Cross-Chain Data Integrity
The proliferation of layer 2 solutions and different blockchain ecosystems creates a new challenge for data providers. Options protocols operating on different chains will need access to a consistent, secure data source. The incentives must extend across multiple chains, ensuring that data provided on one chain is secured by collateral on another.
This requires complex cross-chain communication protocols and a unified incentive layer that can penalize malicious actors regardless of which chain they operate on.

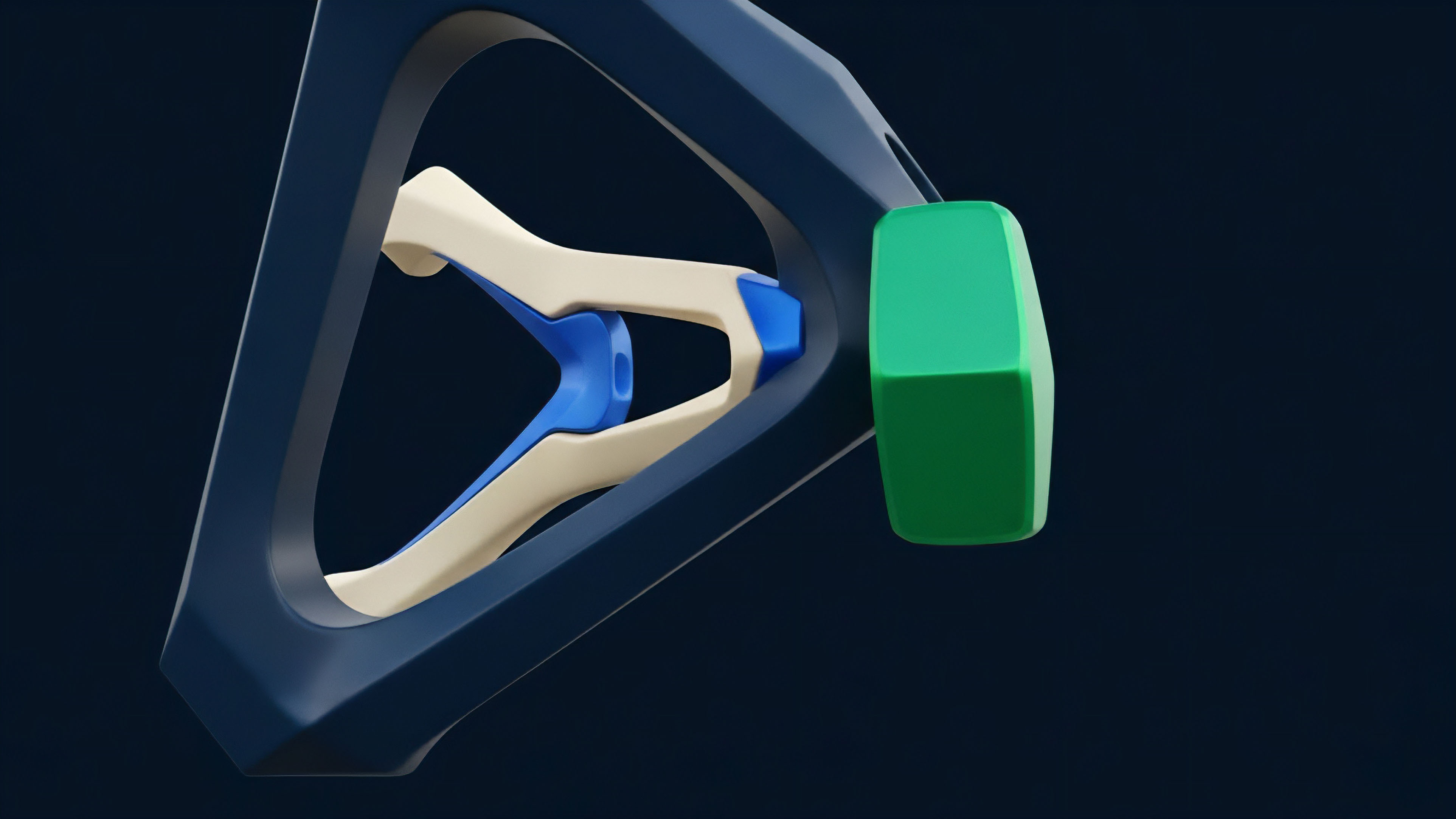
Computation Oracles and Risk Parameters
The future of options will see incentives designed not just around data inputs, but around risk parameters. Instead of simply providing price and volatility, a data provider may be incentivized to calculate and provide the Greeks (Delta, Gamma, Vega, Theta) for a specific option contract. This shifts the computational burden and risk analysis to the data provider network, requiring a new set of incentives to guarantee the accuracy of these complex calculations.
The incentive structure will need to account for the potential for subtle manipulation of risk parameters that could benefit an attacker without triggering a simple price deviation alert.

Dynamic Incentive Modeling
The most advanced future models will move toward dynamic incentives that automatically adjust based on market conditions. If volatility spikes, the value at risk in options protocols increases significantly. The incentive system should automatically increase the required stake or slashing penalties to match the heightened risk environment. This creates a self-adjusting security layer that responds dynamically to changes in market and systemic risk.
Glossary

Automated Market Maker Incentives

Liquidity Provider Vaults

Tokenomics and Incentives

Volatility Oracles

Decentralized Exchanges
Backstop Liquidity Provider

Economic Incentives Design

Liquidity Provider Capital Efficiency

Market Maker Liquidity Incentives and Risks