Essence
The core conflict in decentralized finance options markets arises from the tension between transparency and privacy. Public blockchains, by design, broadcast all transaction data to the network. This open ledger creates a significant vulnerability for market participants, particularly in high-frequency trading and derivatives.
Every order placed, every liquidation threshold set, and every pricing strategy deployed is exposed to automated front-running bots and sophisticated market actors seeking Maximal Extractable Value (MEV). For professional options market makers, this level of transparency is untenable; it eliminates alpha and allows for immediate exploitation of their risk management strategies. The fundamental challenge, therefore, is to architect a system where market participants can prove their compliance with protocol rules ⎊ such as possessing sufficient collateral or meeting margin requirements ⎊ without revealing the specific details of their positions or orders to adversaries.
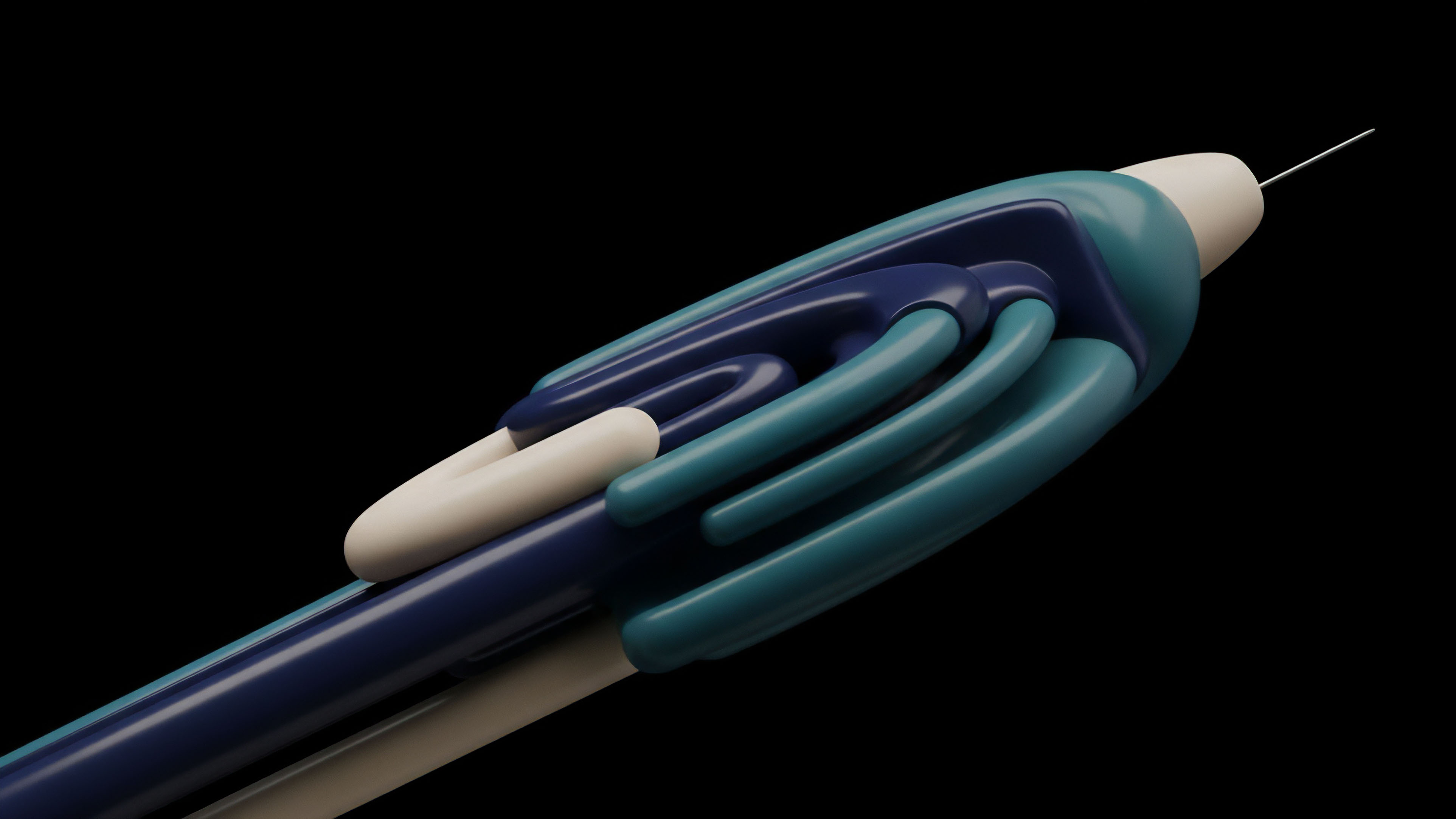
The solution lies in Zero-Knowledge Proofs (ZKPs) , a cryptographic primitive that allows a party to prove a statement is true without disclosing any information beyond the validity of the statement itself.
Zero-Knowledge Proofs allow market participants to verify their compliance with protocol rules without exposing their private financial data to public scrutiny.
This approach moves beyond simple data encryption by separating information from verification. In a traditional transparent market, verification requires full disclosure of data. In a ZK-enabled market, verification relies on a mathematical proof.
This distinction is vital for creating a robust, institutional-grade options market. It allows for the construction of a financial primitive that maintains the integrity of a decentralized settlement layer while offering the data privacy required for professional trading strategies. Without this capability, decentralized options markets remain confined to retail participants and simple strategies, unable to compete with the efficiency and depth of traditional financial systems.
Origin
The concept of zero-knowledge proofs originated not from finance, but from theoretical computer science in the 1980s. Shafi Goldwasser, Silvio Micali, and Charles Rackoff first introduced the concept in their seminal 1985 paper, defining a system where a prover convinces a verifier of a statement’s truth without revealing the underlying information. This initial work focused on the theoretical limits of cryptographic interactions.
The practical application of ZKPs in crypto began with privacy-focused digital currencies. Zcash, for example, pioneered the use of zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) to validate transactions without revealing the transaction amounts or addresses. This early implementation demonstrated the feasibility of using ZKPs to protect user privacy in a public ledger.
The transition from general transaction privacy to specific financial derivatives required significant innovation. Early decentralized finance protocols operated with full transparency, which led to a series of vulnerabilities, particularly related to liquidations and front-running. The need for a more sophisticated solution became clear as derivatives protocols attempted to scale.
The challenge was to apply ZKPs to complex financial logic, not just simple value transfers. This involved creating cryptographic circuits capable of proving statements about complex calculations, such as margin requirements based on volatility inputs or portfolio risk exposure. The development of ZK-rollups for scalability also accelerated the research into ZKPs for privacy, as it provided a framework for off-chain computation and on-chain verification.

Theory
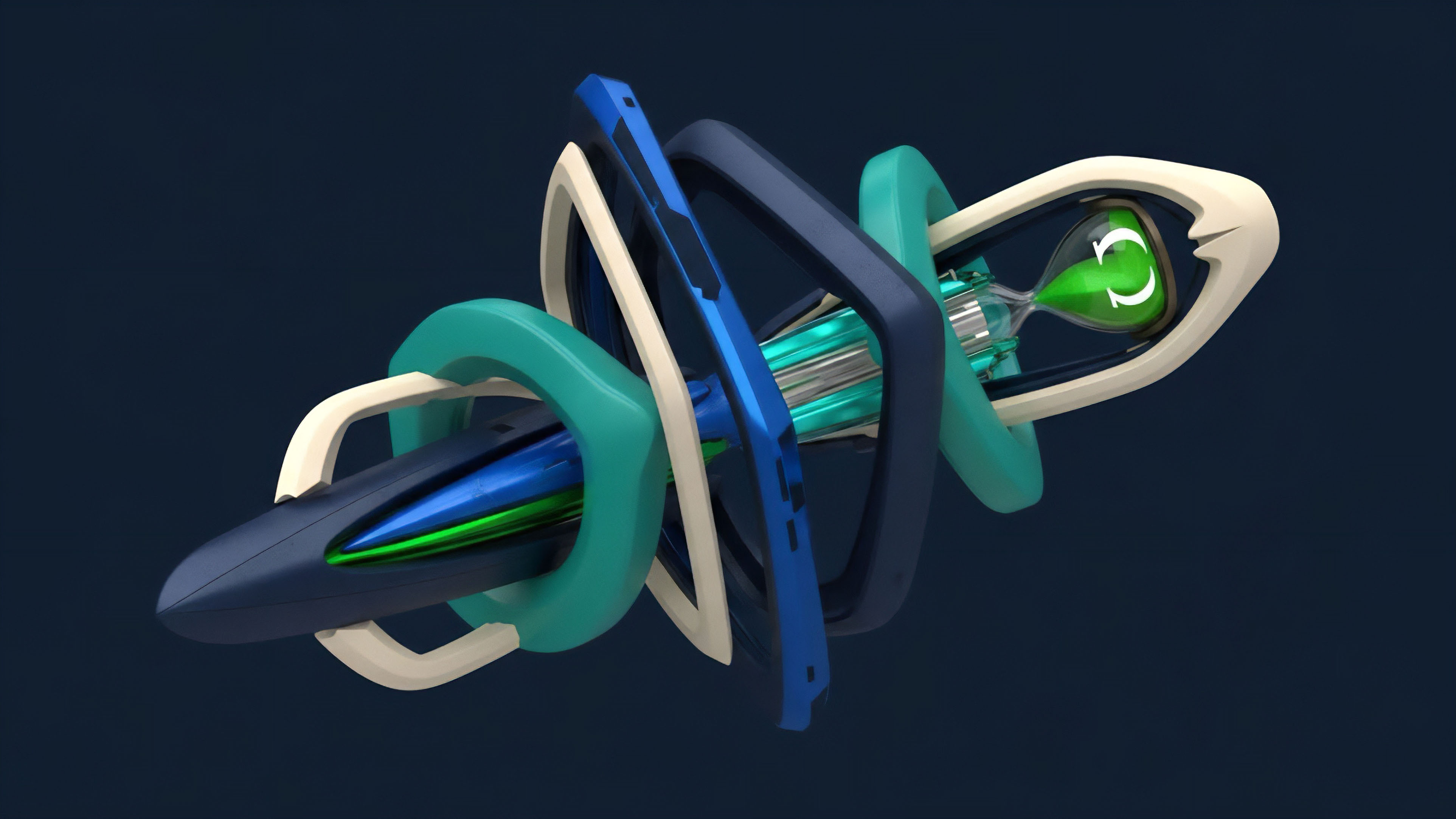
The application of ZKPs in options markets requires a deep understanding of cryptographic primitives and their interaction with market microstructure. The core idea is to move sensitive calculations off-chain, where a proof is generated, and then verify that proof on-chain. The specific variant of ZKP often used is the zk-SNARK , valued for its compact proof size and rapid verification time.
This efficiency is necessary for a high-throughput financial system. The process involves several key steps in a decentralized options trade:
- Private Order Generation: A user generates an options order with specific parameters (strike price, expiry, collateral amount) on their local machine.
- Proof Generation: The user’s client creates a ZKP that demonstrates the order parameters adhere to the protocol’s rules. This proof confirms that the user has sufficient collateral in their account to cover the position and that the order meets all necessary risk checks. The proof does not reveal the exact collateral amount or the specific order details.
- On-Chain Verification: The user submits the ZKP to the protocol’s smart contract. The smart contract, acting as the verifier, checks the proof’s validity. If the proof passes, the order is accepted and matched, even though the contract has no knowledge of the specific details within the proof.
This approach directly addresses the issue of front-running. In traditional transparent systems, a market maker’s pending order is visible in the mempool, allowing a bot to submit a nearly identical order with a higher gas fee to execute first. By contrast, a ZK-enabled order is opaque; the only information visible in the mempool is the proof itself, which reveals nothing about the order’s contents.
This obfuscation eliminates the information asymmetry that MEV relies upon. The system relies on a mathematical guarantee that the order meets the necessary conditions for execution, removing the need for a third party to inspect the private data.

Cryptographic Components and Risk
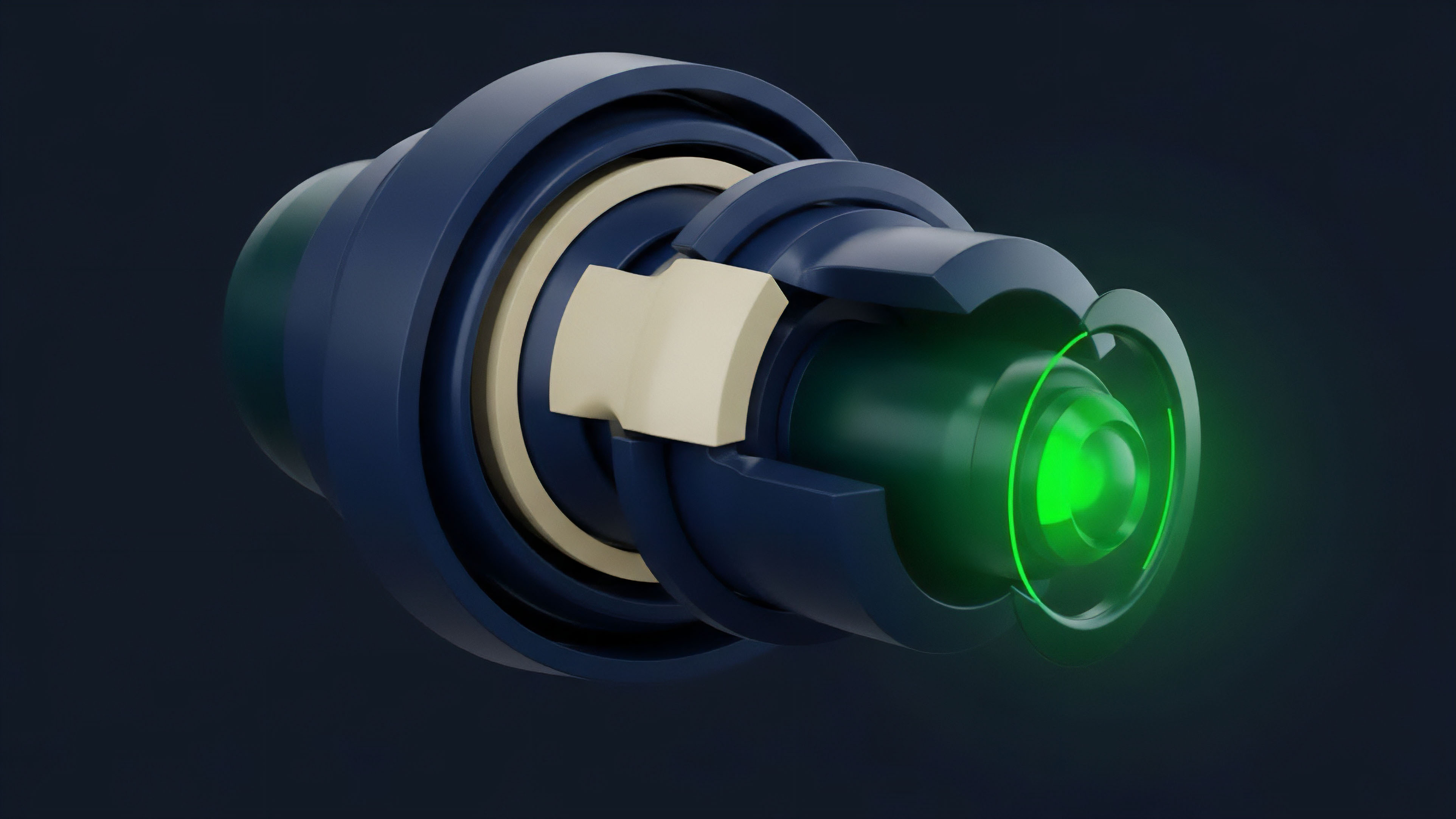
The security of a ZK-enabled options protocol hinges on the cryptographic circuit design. The circuit must correctly implement the protocol’s financial logic, such as margin calculations and risk assessments. Any flaw in the circuit design could allow a malicious actor to generate a valid proof for an invalid order.
Furthermore, the selection of the ZKP type involves trade-offs. While zk-SNARKs are efficient for verification, their initial setup often requires a trusted setup ceremony , which introduces a single point of failure if not executed properly. Newer ZK variants, like zk-STARKs , avoid the trusted setup but generate larger proofs, increasing on-chain costs.
The choice between these variants depends on the protocol’s specific needs for speed, security, and trust assumptions.
Approach
The practical application of ZKPs in options markets currently focuses on two main areas: order book privacy and portfolio risk management. For order book protocols, ZKPs prevent front-running by obfuscating the details of resting orders. Market makers can submit bids and asks without fear of immediate exploitation by searchers.
This changes the market microstructure significantly, shifting competition from information extraction to pricing efficiency. For portfolio risk management, ZKPs allow users to prove compliance with margin requirements without revealing their entire position to the protocol. This enables sophisticated risk strategies and unlocks institutional capital that would otherwise be restricted by internal privacy policies.
Implementing ZKPs for complex financial products requires a specific set of architectural choices. The computational cost of generating proofs for complex financial models ⎊ such as Black-Scholes calculations or portfolio value at risk (VaR) ⎊ is high. Protocols must carefully manage the trade-off between the level of privacy offered and the computational overhead.
A full-privacy system where every aspect of a trade is hidden requires more resources than a partial-privacy system that only obfuscates specific parameters.
The successful deployment of ZKPs in derivatives markets depends on striking a balance between cryptographic overhead and the required level of data protection for different market participants.
A key benefit of ZK-enabled derivatives markets is the potential to create a level playing field for market makers. In traditional markets, high-frequency trading firms gain an advantage through proximity to exchanges and access to private data feeds. In decentralized markets, this advantage translates into MEV.
ZKPs neutralize this information asymmetry by making order flow opaque. This forces market makers to compete on pricing and capital efficiency rather than on technological superiority in data extraction.
The table below illustrates the key differences in market dynamics between transparent and ZK-enabled options protocols:
| Feature | Transparent Options Protocol | ZK-Enabled Options Protocol |
|---|---|---|
| Order Flow Visibility | Public mempool; all order details visible. | Private mempool; only cryptographic proof visible. |
| Front-Running Risk | High; significant MEV extraction possible. | Low; information asymmetry eliminated. |
| Collateral Verification | Direct inspection of on-chain balances. | Verification of ZKP; balance remains private. |
| Institutional Adoption | Low; privacy concerns limit participation. | High potential; privacy safeguards meet compliance needs. |

Evolution
The evolution of data privacy in decentralized options markets has followed a clear trajectory from complete transparency to selective, cryptographic obfuscation. Early DeFi protocols were designed with the assumption that full transparency was sufficient. However, the emergence of MEV demonstrated that this design choice created significant systemic risks.
The initial response involved simple solutions, such as transaction batching and using private relayers to prevent mempool front-running. These solutions were effective but did not address the fundamental issue of data exposure. The shift toward ZKPs represents a maturation of the architectural approach.
This evolution is driven by the demand for institutional-grade financial infrastructure. Institutional participants require privacy not just for competitive reasons, but also for regulatory compliance. The public disclosure of client positions, for example, is often prohibited by financial regulations.
ZKPs offer a pathway to meet these requirements within a decentralized system. The development of ZK-rollups has provided the necessary infrastructure, allowing for the creation of high-speed, low-cost execution environments where ZKPs can be generated and verified efficiently. This progression indicates a clear movement toward a future where privacy is a core feature, not an afterthought.

The Impact of ZK-Rollups
The development of ZK-rollups for scaling Ethereum and other blockchains has directly influenced the design of privacy-preserving derivatives protocols. ZK-rollups perform transaction processing off-chain and submit a single ZKP to the main chain. This architecture allows for a high degree of privacy by default, as the individual transaction details are not published on the main network.
Derivative protocols built on these rollups benefit from this inherent privacy layer. The combination of ZKPs for scaling and ZKPs for specific financial logic creates a powerful stack for building resilient, private, and efficient options markets.

Horizon
Looking forward, the integration of ZKPs with decentralized options protocols presents significant opportunities and challenges. The primary challenge lies in reconciling data privacy with regulatory requirements for anti-money laundering (AML) and know-your-customer (KYC) compliance. Regulators require access to information to prevent illicit activities, which appears to conflict with the core principle of ZKPs.
The solution will likely involve selective disclosure mechanisms. These mechanisms allow a user to prove they are compliant with regulations (e.g. that they are not on a sanctions list) without revealing their identity or transaction history to the protocol itself. The system could be designed to allow a designated regulatory authority to verify specific information by providing an additional key, creating a “privacy with auditability” framework.
This architecture enables a new form of financial system where privacy is a default setting, and transparency is granted only when required by law or explicit user consent. The long-term impact of ZKPs on options markets extends beyond mere efficiency gains; it redefines the relationship between market participants and the financial infrastructure itself. It creates a system where institutional capital can participate without compromising their strategies, leading to deeper liquidity and more robust pricing.
The future of decentralized derivatives depends on the successful implementation of this privacy layer, transforming a transparent, retail-focused product into a secure, globally accessible financial primitive.
The future direction of privacy in decentralized finance involves selective disclosure frameworks that reconcile user anonymity with regulatory compliance requirements.
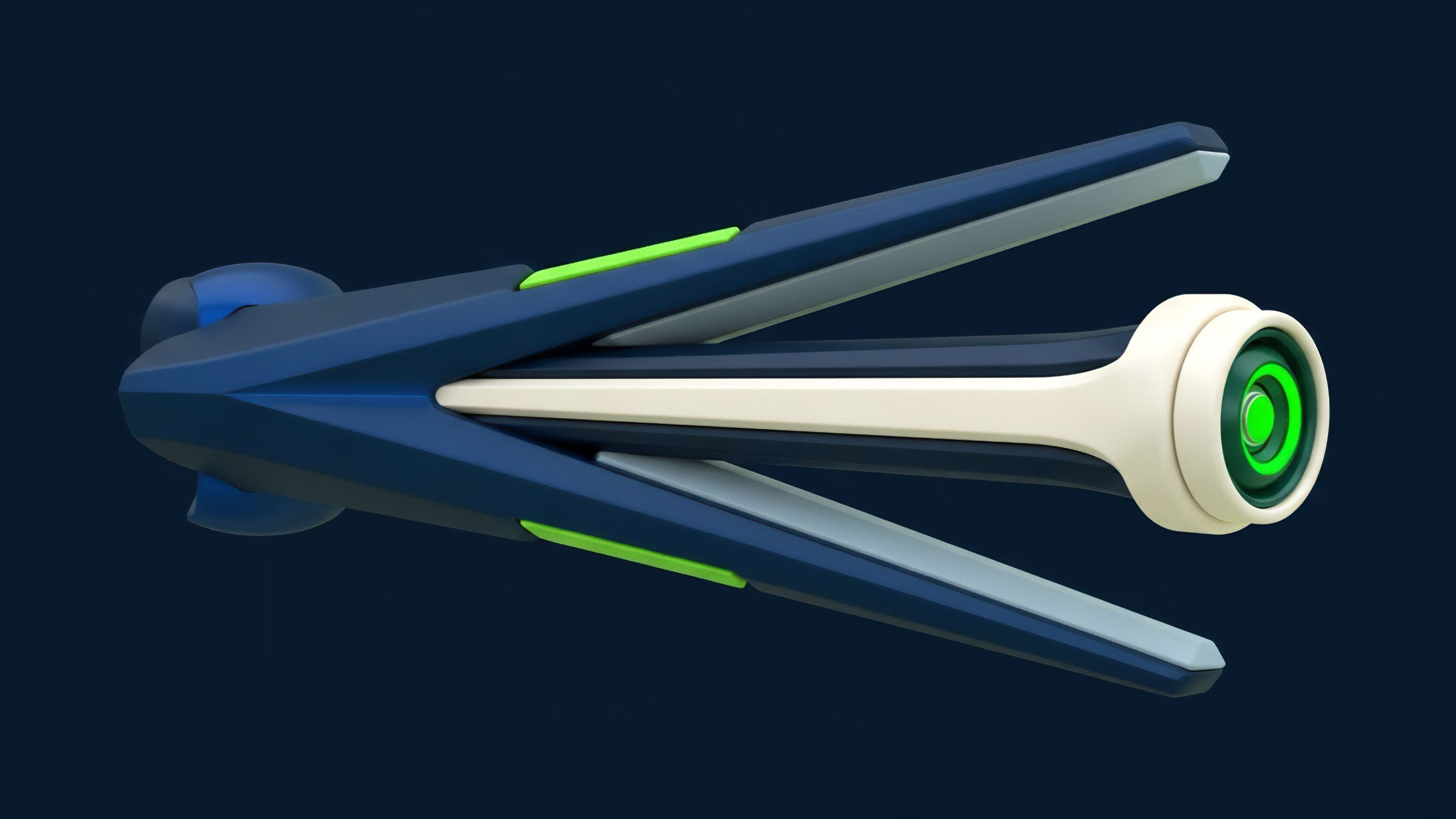
The next iteration of ZK-enabled options protocols will also focus on integrating private calculations of complex financial models. This includes:
- Private Greeks Calculation: Enabling market makers to calculate their risk sensitivities (delta, gamma, vega) in a private environment, allowing them to adjust positions without revealing their overall strategy.
- Private Liquidation Mechanisms: Allowing liquidations to occur based on a private proof of undercollateralization, rather than a public check of a user’s balance. This prevents a “liquidation race” where bots compete to liquidate positions, potentially causing market instability.
- Private Volatility Surfaces: Allowing protocols to use private data feeds for volatility inputs, ensuring that pricing models are robust against manipulation.
This shift in data governance will ultimately allow decentralized derivatives markets to scale to institutional volumes. The successful implementation of these systems requires a high degree of engineering precision and a careful balancing of privacy, efficiency, and regulatory needs.

Glossary

Market Maker Alpha
Financial Privacy Preservation

Transaction Security and Privacy Considerations

Strategic Holdings Privacy

Market Efficiency

Financial Primitive

Absolute Privacy

Market Maker Privacy
Privacy-Preserving Matching Engines