Essence
Zero-Knowledge Proofs (ZKPs) are a cryptographic primitive allowing one party (the prover) to demonstrate to another party (the verifier) that a specific statement is true, without revealing any information beyond the validity of the statement itself. In the context of decentralized options markets, this capability directly addresses the fundamental conflict between financial transparency and strategic privacy. Traditional finance relies on centralized intermediaries to manage counterparty risk, where all participants must disclose their positions and collateral to a central clearinghouse.
Decentralized finance (DeFi) initially sought to replace this with full on-chain transparency, making all positions public. This transparency, however, creates significant strategic disadvantages for sophisticated market makers and high-frequency traders, as their proprietary strategies and risk management parameters become immediately visible to competitors. The application of Cryptographic Security via ZKPs resolves this tension by enabling verifiable computation and private settlement.
ZKPs allow a protocol to enforce critical financial logic ⎊ such as confirming that a counterparty has sufficient collateral to cover their short option position or verifying the correct pricing of a complex derivative ⎊ without exposing the precise values of the collateral, the underlying asset price inputs, or the exact pricing model parameters. This shift allows for the construction of markets where risk can be accurately assessed by the system, while individual participant data remains private.
Zero-Knowledge Proofs enable verifiable computation without revealing the underlying data, balancing market transparency with strategic privacy for derivatives traders.

Origin
The theoretical foundation of ZKPs was established in the seminal 1985 paper “The Knowledge Complexity of Interactive Proof Systems” by Shafi Goldwasser, Silvio Micali, and Charles Rackoff. This work introduced the concept of an interactive proof system where a prover convinces a verifier of a statement’s truth through a series of interactions. The initial concepts focused on a specific class of problems, proving knowledge of a solution to a mathematical problem without revealing the solution itself.
The practical application in financial systems began with the development of specific ZKP schemes that moved beyond theoretical constructs. The evolution from these initial concepts to practical, non-interactive ZKPs (zk-SNARKs and zk-STARKs) has been driven by the need for scalability and efficiency in blockchain environments. The development of zk-SNARKs, specifically, enabled the creation of succinct proofs that could be verified quickly on-chain, making them suitable for high-throughput applications where verification cost is a primary constraint.
The shift in focus from privacy in general to verifiable computation for financial derivatives represents a significant architectural progression. Early blockchain privacy solutions focused on obfuscating transaction history. The current generation of ZKP applications in options and derivatives protocols focuses on proving the integrity of complex financial calculations.
This allows for the implementation of sophisticated risk management engines and pricing models off-chain, where computational cost is lower, while retaining the on-chain verifiability required for trustless settlement. This progression highlights the transition from simply obscuring data to proving the correct execution of code logic.

Theory
The theoretical application of ZKPs to options requires a re-imagining of market microstructure, specifically concerning the calculation of margin requirements and option pricing.
In traditional systems, the clearinghouse calculates margin requirements based on proprietary models and private position data. In a decentralized ZKP-based system, the prover (the options protocol or a market maker) generates a proof that verifies the margin calculation, and the verifier (the blockchain or another protocol component) checks this proof without seeing the input variables. This process relies on a core cryptographic concept: verifiable computation.
For options, verifiable computation is complex because pricing models are often non-linear and computationally intensive. The Black-Scholes model, for instance, requires calculations involving logarithms and cumulative distribution functions. ZKPs must be constructed to prove the correct execution of these calculations.
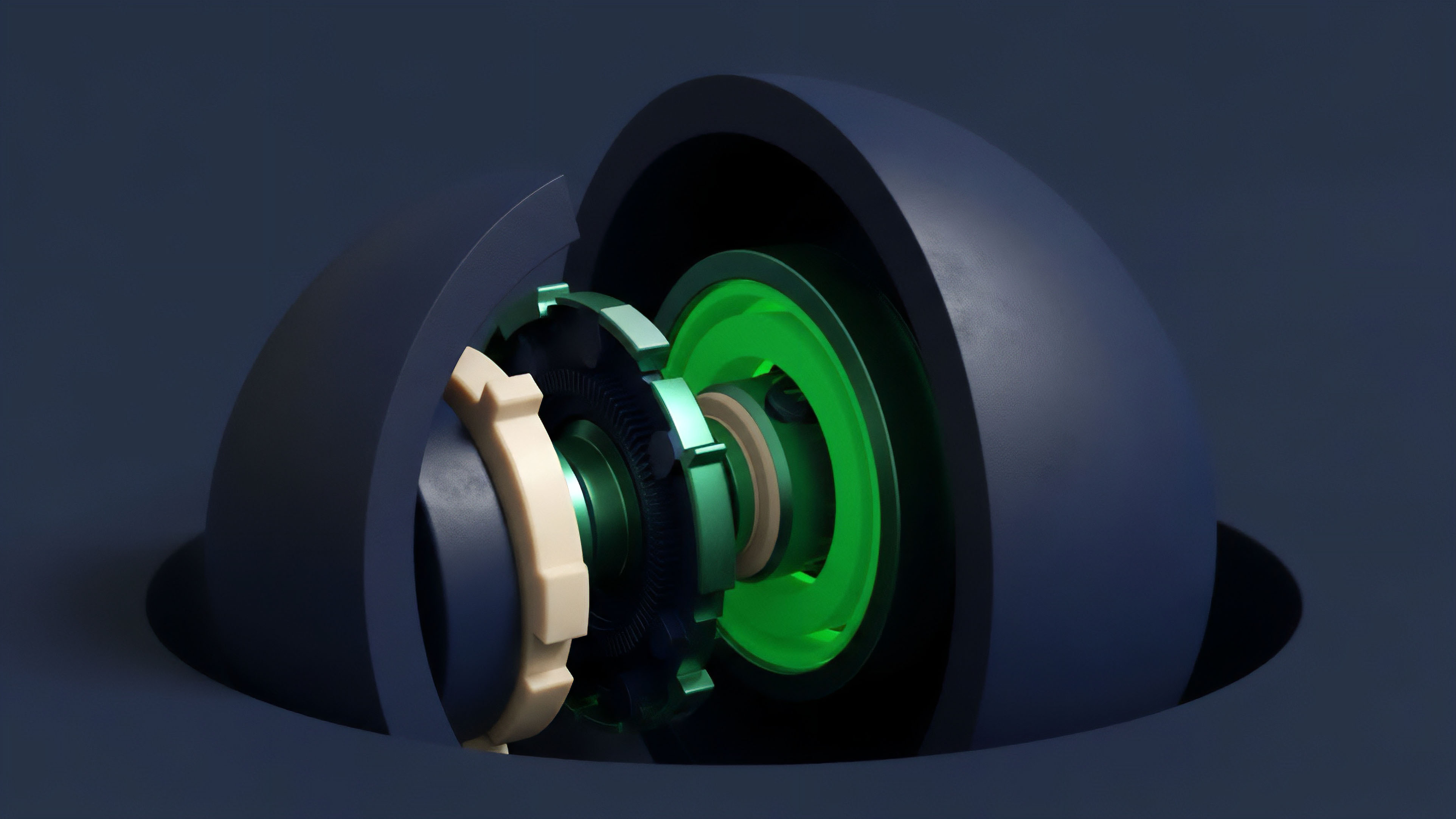
The complexity of the underlying financial model directly impacts the computational cost of generating the proof. The design choice between different ZKP types ⎊ specifically zk-SNARKs and zk-STARKs ⎊ is critical here, balancing proof size, generation time, and trust assumptions. The specific implementation of ZKPs in options protocols centers on two primary use cases: private margin engines and verifiable pricing oracles.
- Private Margin Engines: A user’s collateral and position data are kept private. When a user wishes to open a new position, a ZKP is generated to prove that their collateral exceeds the required margin for the new position. The verifier only sees a boolean output (true/false) from the proof, confirming solvency without revealing the exact collateral amount or the specific position details.
- Verifiable Pricing Oracles: For complex options, a pricing model must be executed off-chain to avoid high gas costs. A ZKP can prove that the off-chain calculation, using verified market data inputs, was executed correctly according to the protocol’s defined pricing function. This ensures that all parties agree on the fair value of the option without requiring a computationally expensive on-chain calculation.
| ZKP Type | Trust Assumption | Proof Size | Proof Generation Cost | Best Use Case for Options |
|---|---|---|---|---|
| zk-SNARK | Trusted setup required; vulnerable if setup compromised. | Small and constant; fast verification. | High; requires significant computation. | On-chain verification where speed and cost are paramount, once trusted setup is complete. |
| zk-STARK | No trusted setup; relies on post-quantum security assumptions. | Larger than SNARKs; slower verification. | Lower generation cost than SNARKs for complex computations. | Off-chain computations where trust minimization is prioritized over verification speed. |

Approach
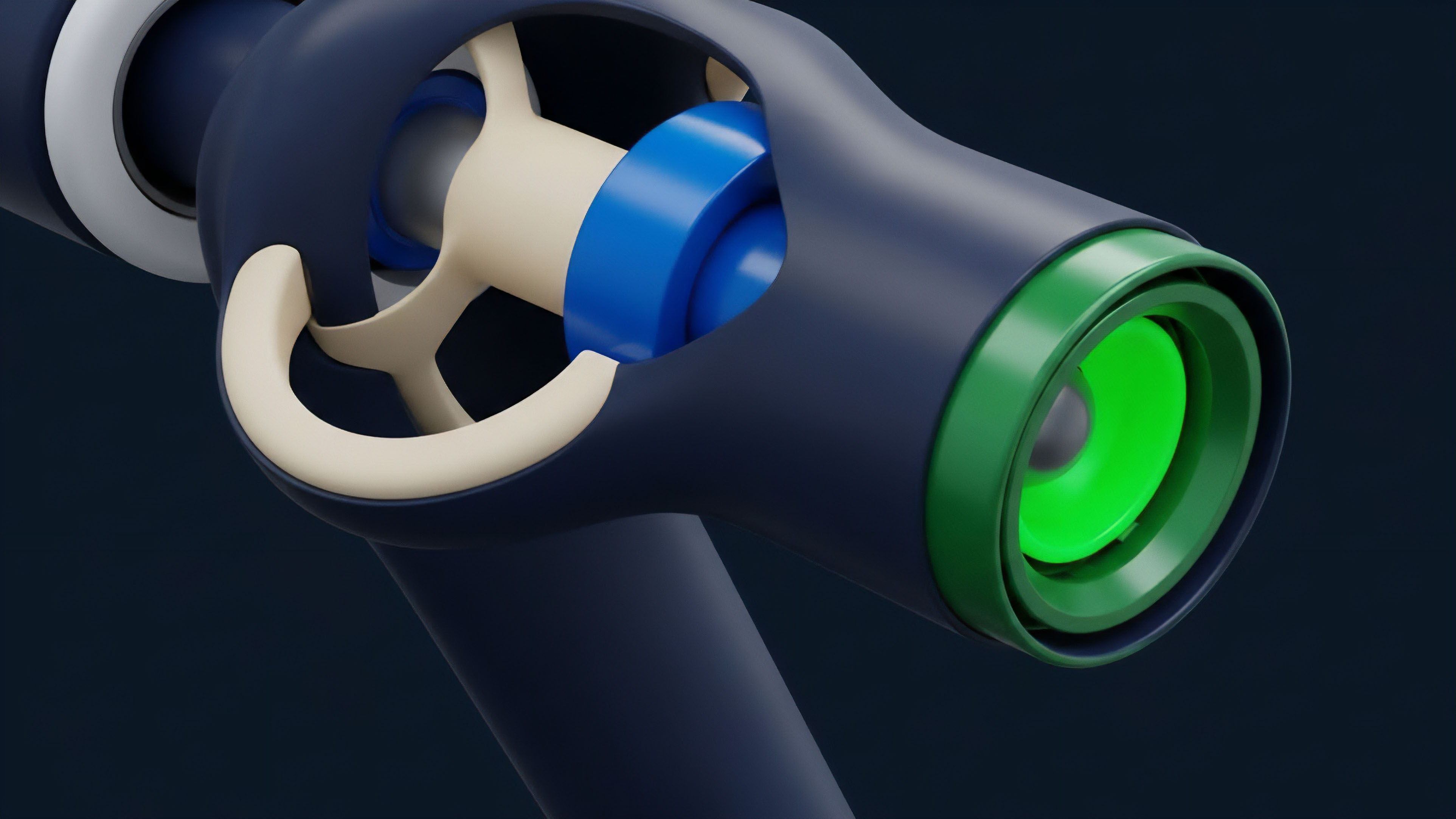
The practical application of ZKPs in decentralized options protocols follows a structured approach focused on mitigating counterparty risk and information asymmetry. The design of these systems centers on creating a “private clearinghouse” where all financial logic is enforced cryptographically rather than by a centralized entity. This approach requires a fundamental shift in how we think about risk management in decentralized markets.
The core design principle is to separate the data (user positions, collateral balances) from the logic (margin calculation, liquidation triggers). The logic is encoded into the ZKP circuit, and the data is used as private input to generate a proof. The on-chain verifier then checks the proof’s validity.
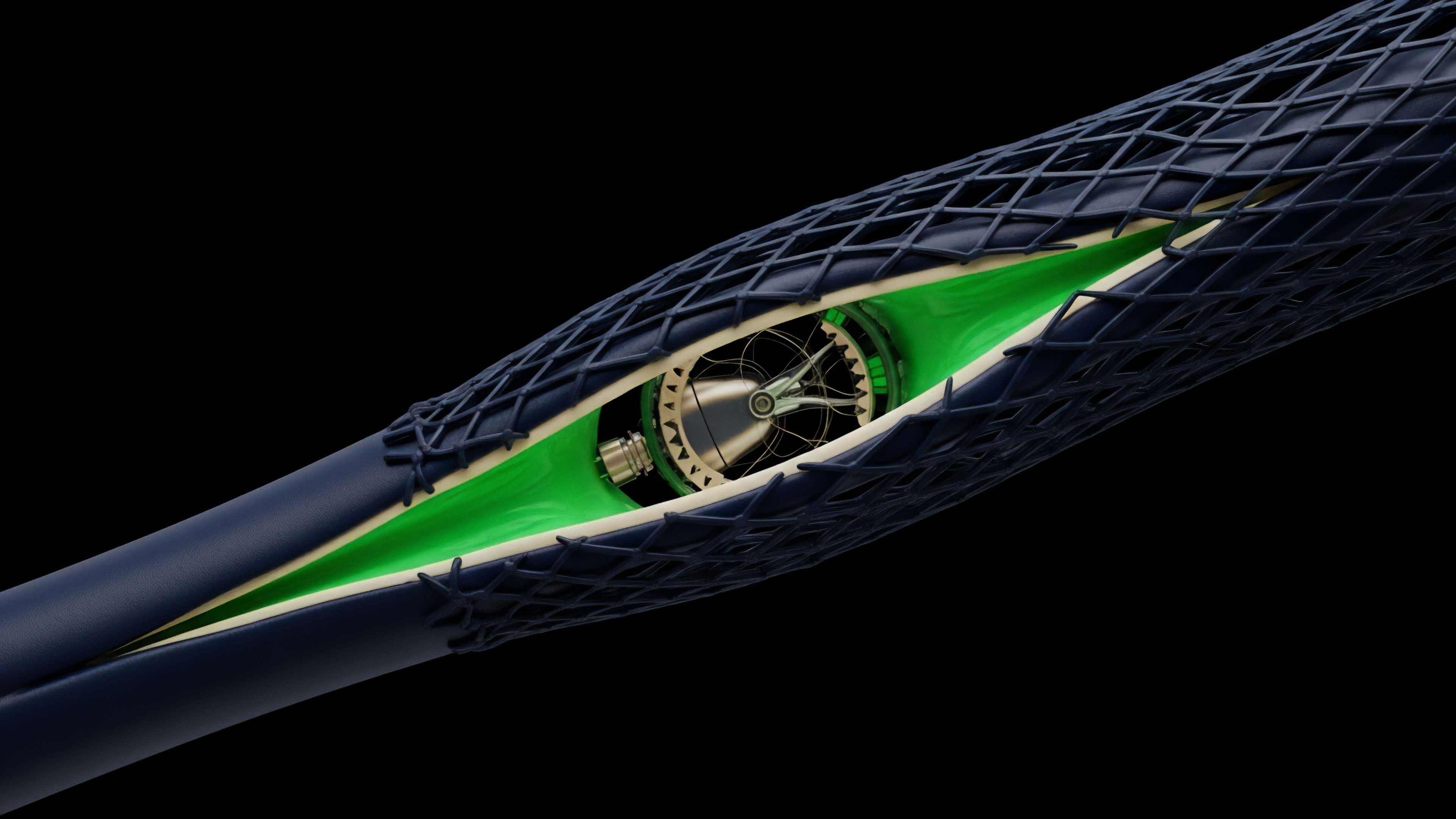
This allows for complex financial logic to be executed efficiently and privately. One significant challenge in this approach is the design of the liquidation mechanism. In a fully transparent system, liquidators monitor public positions and execute liquidations when a margin call is triggered.
In a ZKP-based system, liquidators cannot see the positions. The protocol must instead implement a “liquidation proof” where a third party (or the protocol itself) generates a proof that a specific position is under-collateralized, triggering an automatic liquidation without revealing the full state of the position to the public. This design protects the privacy of the defaulting user while ensuring systemic stability.
The trade-offs inherent in this design are significant. The computational cost of generating ZKPs for complex options calculations remains high. This creates a cost barrier for smaller market participants and introduces latency between the market event (price change) and the generation of the proof required to update positions.
Furthermore, the complexity of ZKP circuits for derivatives means that a single error in the circuit design can have catastrophic financial consequences, potentially allowing for under-collateralized positions to be validated as solvent.
Implementing ZKPs for options requires careful balancing of computational cost against the privacy gains, particularly in designing liquidation mechanisms that function without public position data.

Evolution
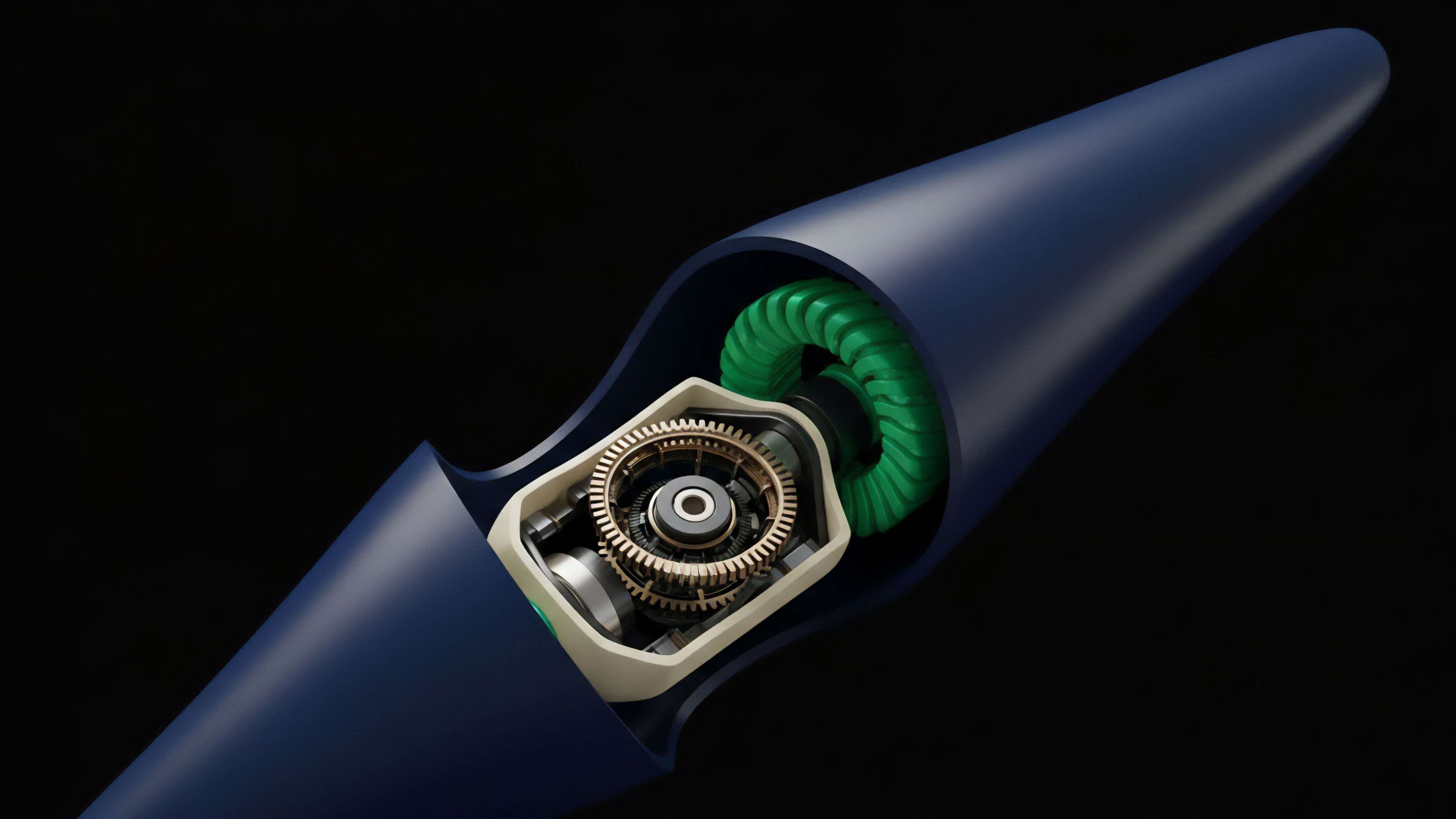
The evolution of ZKPs for options is closely tied to the broader development of ZK-rollups and ZK-EVMs. Early implementations of ZKPs for financial applications were limited to specific, highly constrained calculations, such as proving ownership of funds or verifying simple transaction balances. The current phase involves building more general-purpose computing environments where complex financial logic can be executed within a ZKP-enabled virtual machine.
The progression from simple ZK-rollups to full ZK-EVMs represents a significant leap in capability for derivatives protocols. A ZK-EVM allows developers to write complex smart contracts for options (including complex multi-leg strategies, exotic options, and dynamic margin requirements) in familiar languages like Solidity, and have the entire execution of that contract verified via a ZKP. This removes the need for custom-designed ZKP circuits for every specific financial product.
The integration of ZKPs with decentralized options protocols is also driving a re-evaluation of how liquidity provision functions. In current transparent protocols, market makers often face “griefing attacks” where competitors can front-run their orders or replicate their strategies by observing their public positions. ZKP-based private order books offer a solution, allowing market makers to place orders and manage inventory without revealing their strategy to the public.
This increases capital efficiency by allowing market makers to operate with tighter spreads and reduced risk of being exploited. The next generation of options protocols will likely leverage these advancements to create more competitive and robust markets.

Horizon
The future trajectory of ZKPs in options markets points toward a complete re-architecture of market microstructure.
The convergence of ZKPs with decentralized autonomous organizations (DAOs) and on-chain governance models creates a pathway for fully automated, self-regulating markets where risk is managed cryptographically. This future state would feature options protocols where all participants operate in private, yet the system as a whole maintains complete verifiable integrity. The ultimate goal is to create a market where information asymmetry between participants is minimized, while simultaneously maximizing privacy.
This requires moving beyond the current model of either full transparency or full opacity. ZKPs provide the mechanism to achieve this by allowing all participants to verify the rules of the game and the solvency of the system without revealing the specific positions of individual players. A key challenge on the horizon is the development of ZKP-friendly option pricing models.
Current models, designed for centralized environments, are not optimized for the constraints of ZKP circuits. The future will require financial engineers to collaborate closely with cryptographers to design new pricing models that are both financially accurate and computationally efficient for ZKP generation. The regulatory implications of this shift are profound.
A fully private options market presents challenges for traditional oversight bodies that rely on public position data for systemic risk assessment. However, ZKPs also offer a potential solution by allowing protocols to generate specific, auditable proofs for regulators without compromising user privacy. The system could generate a proof that “all positions are fully collateralized,” satisfying regulatory requirements without revealing individual identities or balances.
The future of options markets hinges on ZKP technology, enabling private trading environments where systemic risk can be proven and verified without public disclosure of individual positions.

Glossary

Cryptographic Witness

Cryptographic Capital Efficiency

Protocol Security Engineering
Cryptographic Assumption Costs
Cryptographic Proof of Solvency

Cryptographic Data Structures for Scalability
Network Security Implications

Economic Security Derivatives

Security Parameter Thresholds