Essence
Cryptographic Proof Optimization is the systemic reduction of computational complexity required to verify a financial state transition on a decentralized ledger, transforming high-friction settlement into a single, succinct cryptographic assertion.
The core problem in decentralized derivatives is the computational cost of truth. Every option exercise, every margin call, and every collateral update involves complex arithmetic ⎊ pricing models, payoff functions, and risk checks ⎊ that are prohibitively expensive to execute and verify directly on a base layer like the Ethereum Virtual Machine (EVM). Cryptographic Proof Optimization addresses this bottleneck by moving the complex calculation off-chain, computing it within a specialized environment, and generating a highly compact, non-interactive proof of its correctness.
This proof, typically a Zero-Knowledge Succinct Non-Interactive Argument of Knowledge (ZK-SNARK) or a STARK, is then submitted on-chain, where its validity can be verified with a fixed, minimal amount of gas, independent of the complexity of the original calculation.

Origin of Succinct Verification
The conceptual origin of this optimization lies at the intersection of applied cryptography and the constraints of decentralized computing. The early DeFi derivatives protocols struggled with solvency checks and liquidations, often requiring complex, multi-step transactions that failed under network congestion ⎊ a failure mode tied directly to high computational friction. The formal mathematical groundwork comes from the 1990s work on Probabilistically Checkable Proofs (PCPs) and later, the development of ZK-SNARKs by researchers like Eli Ben-Sasson and Alessandro Chiesa.
The realization that this technology could abstract away the computational weight of a financial contract ⎊ effectively creating a cryptographic receipt for a complex event ⎊ provided the foundational architectural shift for modern, capital-efficient derivatives protocols. The system’s integrity hinges on the computational hardness of forgery, a principle far more robust than relying on external, centralized computation or high-cost, synchronous on-chain verification.

Theory
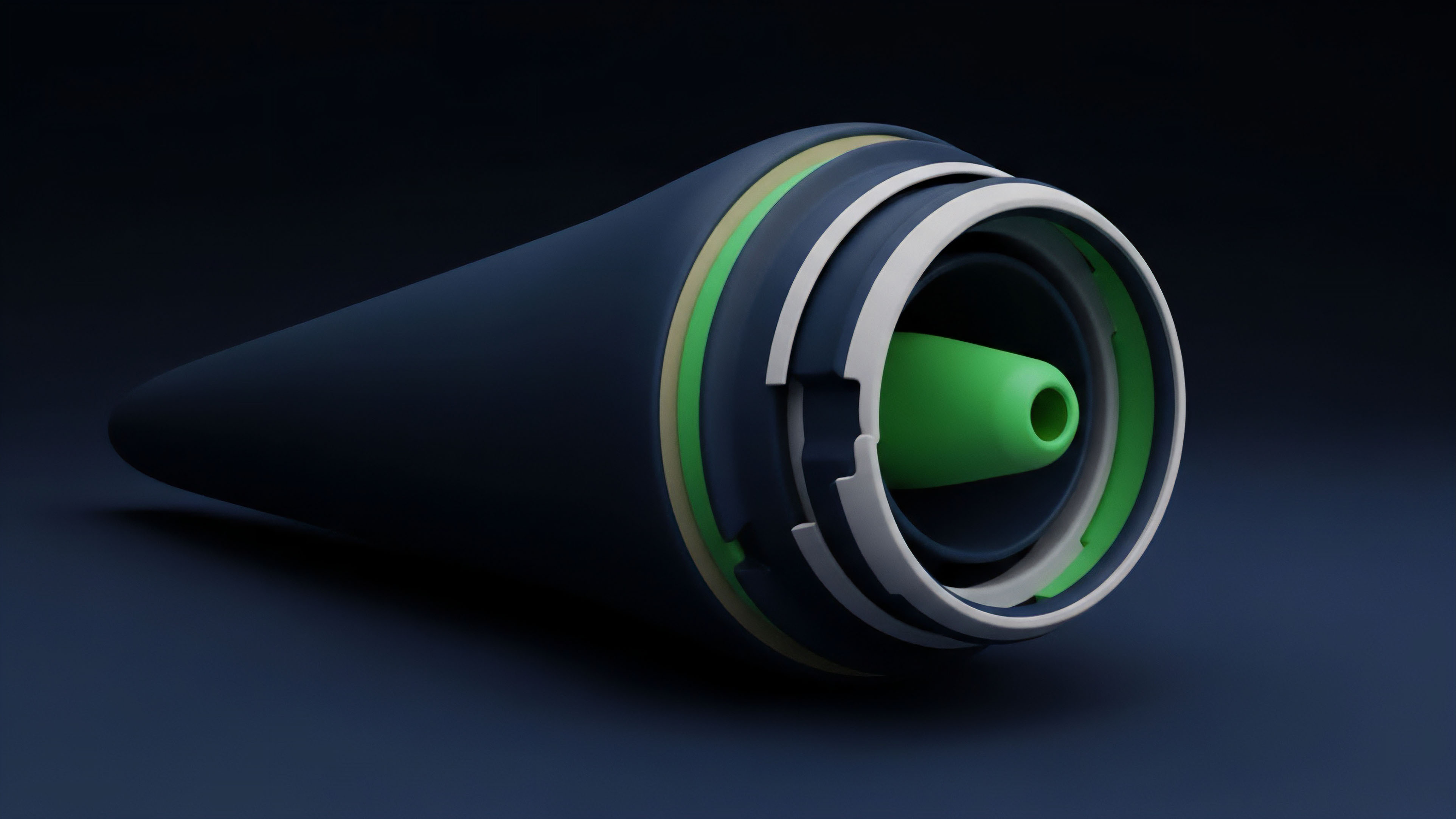
The theoretical underpinning of Cryptographic Proof Optimization is the transformation of financial logic into a verifiable arithmetic circuit.
This process requires mapping the continuous mathematics of quantitative finance ⎊ the payoff function of a European option, the calculation of Delta and Gamma ⎊ into a discrete, finite set of polynomial equations that can be efficiently proven and checked.
Constraint System Mapping
The standard approach involves translating the financial contract’s logic into a Rank-1 Constraint System (R1CS), a series of equations used in many ZK-SNARK constructions. A payoff function, for instance, P = max(S-K, 0) for a call option, must be expressed as a set of linear and quadratic constraints. The optimization objective is not merely to prove correctness, but to minimize the number of constraints ⎊ the ‘circuit size’ ⎊ because the proof generation time scales linearly with this size.
Our inability to respect the circuit size limit is the critical flaw in our current attempts to onboard truly exotic, path-dependent derivatives.
- Arithmetic Circuit Design The financial model (e.g. a volatility surface lookup) is compiled into a sequence of additions and multiplications, which form the constraints.
- Witness Generation The off-chain server, the prover, computes the result of the financial transaction and generates a ‘witness’ ⎊ the set of intermediate values that satisfy the circuit’s constraints.
- Proof Generation The prover uses the witness and the circuit structure to generate the succinct cryptographic proof, which is exponentially smaller than the witness itself.

Verifier Complexity and Trade-Offs
The true optimization is measured by the verifier’s cost. The goal is a mathcalO(1) or mathcalO(log N) verification cost, where N is the number of constraints, a property achieved by ZK-SNARKs and STARKs, respectively. The systems architect must weigh the computational overhead of proof generation (Prover Time) against the final on-chain cost (Verifier Gas).
| Metric | ZK-SNARK (e.g. Groth16) | ZK-STARK (e.g. Cairo) |
|---|---|---|
| Proof Size | Constant (Smallest) | Logarithmic (Larger) |
| Verifier Cost | Constant (Lowest Gas) | Logarithmic (Low Gas) |
| Trust Assumption | Trusted Setup Required | Trustless (Transparent Setup) |
| Use Case Preference | Simple, High-Value Options | Complex, Auditable Logic |
Approach
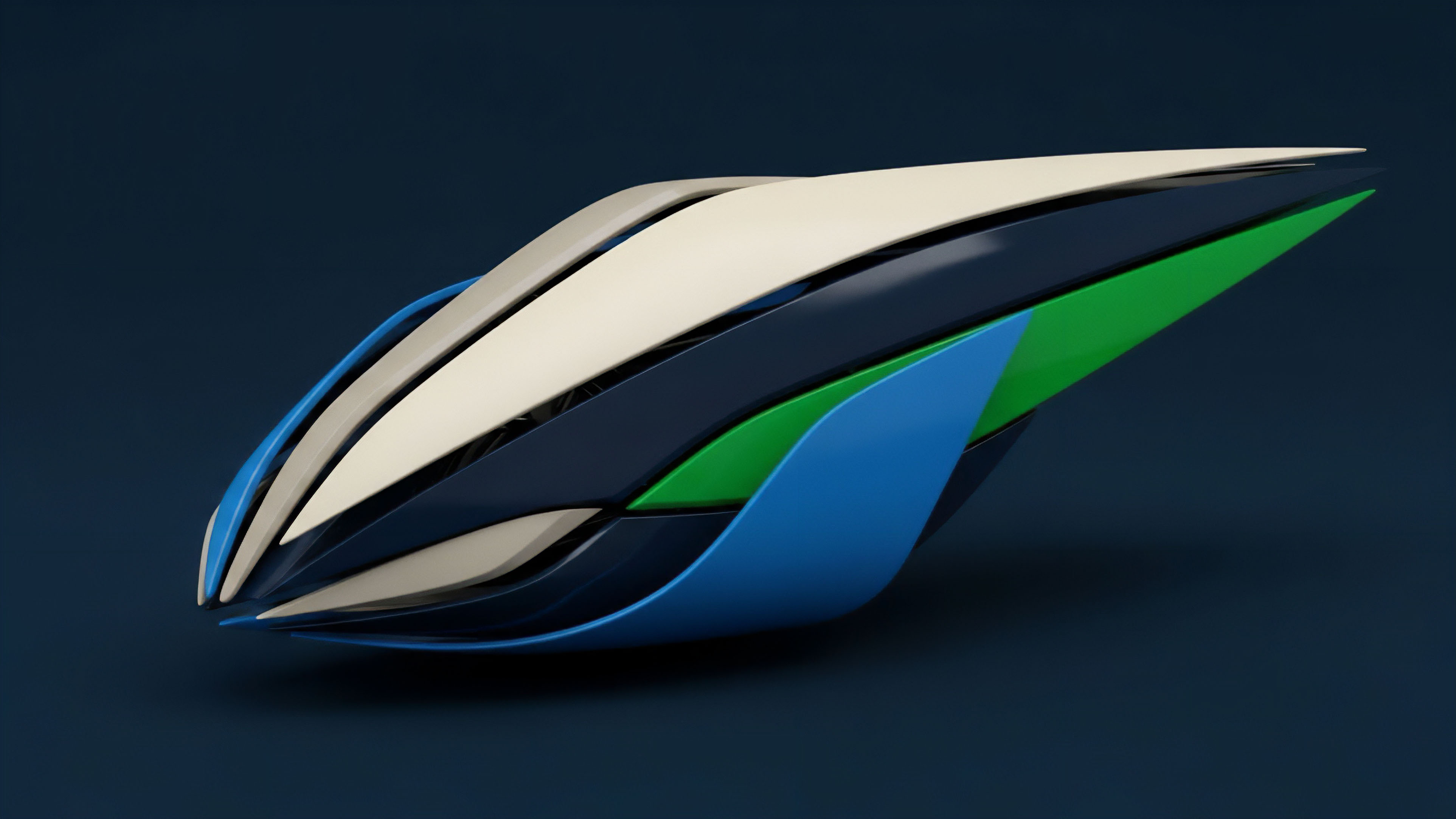
The current approach to implementing Cryptographic Proof Optimization centers on two primary technical vectors: Proof Aggregation and Recursive Composition. These techniques are essential for turning a theoretical concept into a system capable of handling the transaction volume of a high-frequency trading environment.
Proof Aggregation for Market Microstructure
In a decentralized options market, order flow is discontinuous. Rather than submitting a proof for every single option exercise, which remains too costly even with optimized verifiers, the system batches thousands of user interactions into a single, unified proof. This aggregation dramatically lowers the effective cost per transaction.
The system operator ⎊ the sequencer in a ZK-Rollup, for instance ⎊ collects a block of transactions, computes the resultant state transition, and generates one proof that validates the entire block. This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored ⎊ because a single, faulty constraint in the aggregation circuit invalidates the entire batch, a systemic risk that requires robust circuit design and rigorous audit.
- Batch Collection Market events (trades, exercises, liquidations) are collected off-chain by a sequencer.
- Single Circuit Evaluation All events are processed through a single, massive arithmetic circuit representing the net state change of the options protocol.
- Proof Submission One succinct proof is submitted to the base layer, updating the canonical state for all thousands of transactions simultaneously.
The most potent application of proof optimization is its ability to compress the systemic risk footprint of thousands of leveraged positions into a single, verifiable hash.

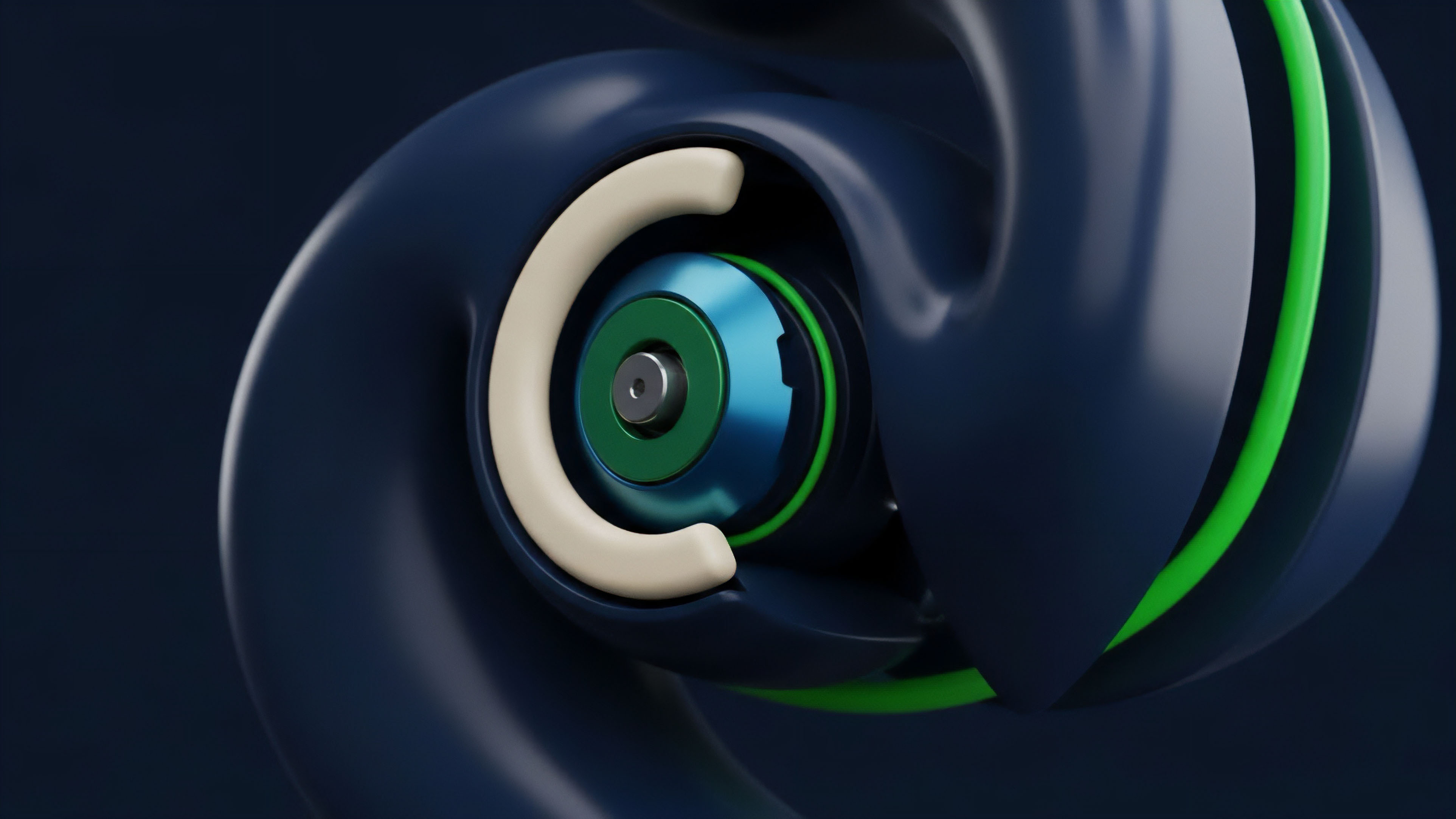
Recursive Proof Composition
Recursive proof composition represents the cutting edge of this optimization. It involves a proof verifying the correctness of a previous proof. This creates a chain of verifiable computation that can extend indefinitely.
For financial systems, this allows for the creation of perpetual, verifiable history without the need to re-verify the entire history with every new block. The system can prove: “I have a proof that the state was correct at time t0, and I have a proof that the transition from t0 to t1 was correct, therefore the state at t1 is correct.” This capability is non-negotiable for scaling a decentralized margin engine or a collateral pool, providing finality and auditability without the linear increase in verification cost that plagued earlier architectures.
Evolution
The trajectory of Cryptographic Proof Optimization is a clear march toward fixed-cost finality, moving from a conceptual tool to a foundational layer of decentralized market microstructure.
The earliest derivative protocols attempted to use optimistic rollups, relying on a dispute window and economic incentives to enforce correctness. This introduced a significant time delay for final settlement ⎊ a critical vulnerability for options, which are highly time-sensitive instruments. The shift to ZK-based optimization eliminates this delay, moving the security guarantee from a game-theoretic assumption of honesty to a mathematical certainty of cryptographic proof.
This evolution changes the game for high-frequency market makers, providing them with the necessary speed and certainty for capital deployment. This is the difference between operating a market on a volatile, crowded street and running it within a clean, mathematically-secured vault. The practical implication for order flow is immense: liquidity providers can now quote tighter spreads because the uncertainty premium associated with settlement delay and high gas volatility is significantly reduced.
This reduction in the ‘friction tax’ directly translates to deeper order books and better pricing for retail and institutional participants alike. The efficiency gains extend to the liquidation engine ⎊ a traditionally centralized and opaque process ⎊ which can now be codified as a verifiable proof. The liquidation trigger and execution are calculated off-chain and proven on-chain, ensuring fair, deterministic execution that cannot be front-run or manipulated by the sequencer, thereby significantly reducing systemic contagion risk.

Efficiency Metrics in Decentralized Finance
The functional relevance of this evolution can be quantified by comparing the metrics of first-generation protocols to those using optimized ZK-Rollups.
| Metric | L1 Direct Settlement (Legacy) | L2 ZK-Proof Optimization (Current) |
|---|---|---|
| Cost per Trade Verification | $5 – $50 (Variable) | $0.01 – $0.10 (Fixed/Amortized) |
| Finality Time | Minutes (Probabilistic) | Seconds (Cryptographic) |
| Maximum Throughput (Trades/Sec) | 10 – 25 | 1,000 – 10,000+ |
The ability to achieve fixed-cost, cryptographic finality is the reason decentralized options markets can finally compete on a structural level with their centralized counterparts ⎊ the throughput is higher, the settlement is faster, and the auditability is absolute.
Horizon
The next stage for Cryptographic Proof Optimization moves beyond simple settlement and into the domain of privacy and regulatory compliance. The ultimate goal is the creation of a verifiable, yet private, decentralized financial system.
ZK-Verified Solvency and Privacy
The immediate horizon involves using zero-knowledge proofs to verify a market maker’s solvency without revealing their underlying portfolio positions ⎊ a ‘Proof of Reserves’ that maintains a competitive edge. This is a powerful tool for systems risk management. We can construct a circuit that verifies:
- Collateral Sufficiency The value of the market maker’s collateral is greater than their aggregate risk exposure, VCollateral > sum VRisk, without revealing the specific assets or positions.
- Regulatory Proofs Compliance with jurisdictional rules ⎊ such as preventing trading from sanctioned addresses or restricting access to specific instruments ⎊ can be enforced at the proof layer. The proof attests that a transaction adheres to a complex rule set without revealing the identity of the transacting party.
The Architecture of Cryptographic Derivatives
The profound depth of this technology will enable the creation of truly novel financial instruments that are currently impossible due to regulatory and technical friction. Think of a Cryptographic Credit Default Swap where the proof itself verifies the non-occurrence of a default event based on an external, verifiable data feed (an oracle). The proof is the instrument. The systemic implication is a world where counterparty risk is not assumed away by legal contracts or centralized clearing houses, but is mathematically eliminated by the structure of the transaction itself ⎊ a system where trust is replaced by computation, a far more durable and scalable foundation for global finance. The final, open question remains: how do we design the economic incentives around the prover to ensure decentralized, censorship-resistant proof generation remains viable under all market conditions?

Glossary

Risk Sensitivity Analysis

Zk-Starks
Censorship Resistance Protocol

Capital Efficiency Gains

R1cs Constraints
Option Payoff Function

Zk-Snarks

Verifier Complexity

Smart Contract Vulnerabilities