Systemic Substance
Cryptographic Price Oracles function as the primary epistemological link between isolated blockchain environments and external market data. These systems verify, aggregate, and transmit off-chain information to smart contracts, enabling deterministic code to interact with fluctuating asset values. Within the digital asset architecture, the blockchain exists as a walled garden, a mathematical construct of absolute certainty that cannot natively perceive the chaotic state of global finance.
Cryptographic Price Oracles translate probabilistic market data into deterministic state transitions within a distributed ledger.
The data provided by these mechanisms determines the solvency of lending protocols, the execution of liquidations, and the settlement of derivative contracts. Without a reliable mechanism for importing external truth, decentralized finance remains a closed loop of internal state changes. The reliability of this data transmission depends on the economic incentives of the participants and the cryptographic proofs used to validate the source.
Information Symmetry
Smart contracts require high-fidelity data to maintain market efficiency. If the price feed lags or becomes susceptible to manipulation, the entire financial stack faces systemic risk. Cryptographic Price Oracles mitigate this by sourcing data from multiple high-liquidity venues, ensuring that the reported price reflects a broad market consensus rather than a localized anomaly.
This process transforms raw exchange data into a verified signal that the blockchain can act upon with confidence.

Historical Genesis
The need for these systems arose from the inherent limitation of the Ethereum Virtual Machine to fetch external data without compromising consensus. Early decentralized applications relied on centralized APIs, which created single points of failure. These early feeds were often controlled by a single entity, making them vulnerable to downtime or malicious data injection.
The “Oracle Problem” became a primary hurdle for the growth of trustless financial instruments.
Financial stability in decentralized markets relies on the mathematical integrity of data aggregation and the game-theoretic cost of corruption.
Early exploits demonstrated that a centralized price feed could be manipulated to trigger unfair liquidations. This led to the development of decentralized oracle networks that distribute the responsibility of data reporting across a broad set of independent nodes. By requiring a quorum of nodes to agree on a price, the system reduces the risk of a single actor corrupting the feed.

Consensus Evolution
The transition from centralized feeds to decentralized networks was driven by the demand for censorship resistance. Market participants recognized that if a price feed could be shut down or altered by a regulatory body or a malicious actor, the underlying smart contracts were not truly decentralized. Cryptographic Price Oracles evolved to include economic penalties for dishonest reporting, aligning the interests of the data providers with the health of the network.

Architectural Logic
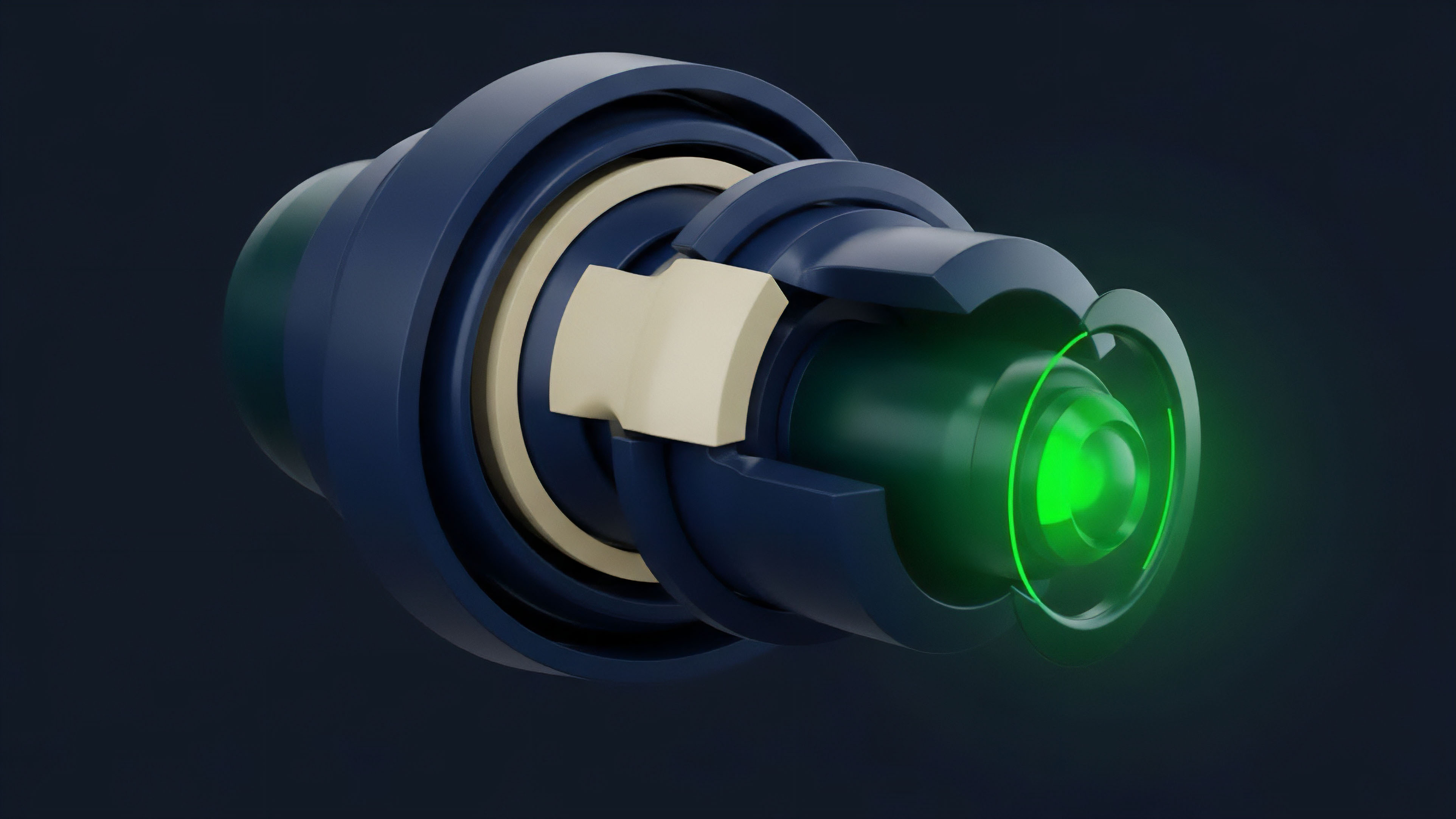
The mathematical foundation of Cryptographic Price Oracles rests on game theory and decentralized consensus.
Most modern systems utilize a Schelling Point mechanism, where independent actors are incentivized to report the truth because they expect others to do the same. If a node reports a price that deviates significantly from the aggregate mean, it faces a loss of staked collateral through a process known as slashing.
| Model Type | Update Mechanism | Gas Cost | Latency |
|---|---|---|---|
| Push Model | Periodic on-chain updates | High | Medium |
| Pull Model | On-demand data fetching | Low | Low |
| Hybrid Model | Threshold-based updates | Medium | Low |
Price discovery in these systems is a function of volume-weighted averages across fragmented liquidity pools. By aggregating data from both centralized and decentralized exchanges, the oracle minimizes the impact of localized volatility. This mirrors the “wisdom of crowds” observed in biological systems, where collective intelligence often exceeds the accuracy of any single participant.

Aggregation Methods
- Medianization involves taking the middle value from a set of reports to eliminate outliers.
- Volume Weighted Average Price (VWAP) assigns more weight to exchanges with higher trading activity.
- Time Weighted Average Price (TWAP) averages the price over a specific duration to prevent flash loan attacks.

Operational Execution
Current implementations of Cryptographic Price Oracles focus on minimizing the window of opportunity for arbitrageurs and attackers. High-frequency updates are required for protocols managing leveraged positions, as even a small delay in price reporting can lead to under-collateralization. The execution of these updates is often triggered by a Deviation Threshold, where a new price is pushed on-chain only if the market has moved by a certain percentage.
Low-latency data transmission and cryptographic verification are the primary defenses against toxic order flow and oracle-based arbitrage.
Protocols like Synthetix and Aave utilize these feeds to manage billions in capital. The security of these systems is maintained through a combination of node reputation and economic bonding. Nodes with a history of accurate reporting are given more weight in the consensus process, while new or unreliable nodes must prove their integrity over time.

Security Parameters
- Data Source Diversity ensures that no single exchange failure can compromise the feed.
- Node Quorum Requirements mandate that a minimum number of independent participants must sign off on a data point.
- Signed Data Proofs provide a cryptographic trail that verifies the origin and integrity of the information.

Iterative Progression
The development of these systems has moved toward reducing the trust required in the data providers themselves. The rise of First-Party Oracles, where the data source itself signs the data, eliminates the middleman and reduces the risk of data tampering during transmission. This shift improves both the speed and the reliability of the price feeds, as the information travels directly from the exchange to the blockchain.
| Generation | Security Focus | Primary Mechanism |
|---|---|---|
| First Generation | Centralized Trust | Single API Feeds |
| Second Generation | Decentralized Quorum | Multi-node Aggregation |
| Third Generation | Cryptographic Proofs | ZK-Oracles and TEEs |
Besides this, the industry is seeing a move toward Pull Oracles, which allow users to fetch the most recent price data only when they need to execute a transaction. This significantly reduces the gas costs associated with constant on-chain updates. The market is also adapting to the risks of Maximal Extractable Value (MEV), where searchers exploit the delay between an oracle update and its execution on-chain.
Mitigation Strategies
To combat toxic order flow, developers are implementing commit-reveal schemes and zero-knowledge proofs. These technologies allow for the validation of data without exposing the specific price until the transaction is processed. This prevents front-running and ensures that the oracle remains a neutral provider of truth rather than a tool for sophisticated market manipulation.

Future Prospects
The next phase of Cryptographic Price Oracles will likely involve the integration of Zero-Knowledge Proofs (ZKP) to provide absolute certainty regarding the authenticity of data.
ZK-Oracles will allow for the verification of complex off-chain computations and data sets without revealing the underlying sensitive information. This will expand the utility of oracles beyond simple price feeds into areas like credit scoring and identity verification. The survival of decentralized derivatives depends on the ability of these systems to provide sub-second latency.
As Layer 2 scaling solutions become more prevalent, oracles will move their aggregation logic off-chain, using the mainnet only for final settlement and verification. This will enable a new class of high-frequency trading applications that were previously impossible due to network constraints.

Systemic Resilience
The ultimate goal is a system where the cost of attacking the oracle exceeds the potential gain from manipulating the market. This requires a sophisticated understanding of the Liveness-Security Trade-off. Future architectures will likely incorporate AI-driven anomaly detection to identify and ignore suspicious data points in real-time, further hardening the infrastructure against sophisticated adversarial attacks. The transition toward institutional adoption will demand these levels of rigor and mathematical certainty.

Glossary
Censorship Resistance
Gas Efficiency
Multi-Signature

Pull Model

Tee

Volatility Surface

Consensus Mechanism

Probabilistic Finality

Gamma Risk