
Essence
Continuous Integration Security represents the automated verification of cryptographic integrity within financial protocol development lifecycles. This practice ensures that every modification to a decentralized derivative contract undergoes rigorous, programmatic validation against pre-defined safety constraints before deployment. The objective involves maintaining a state of perpetual readiness where the security posture of an asset-issuing protocol remains immutable and resistant to adversarial manipulation.
Continuous Integration Security functions as an automated sentinel that prevents the propagation of compromised code into live financial derivatives markets.
This operational model shifts security from a reactive, post-mortem activity into a proactive, embedded component of the build process. By treating security checks as essential protocol physics, developers eliminate human error and ensure that financial primitives retain their intended economic behavior under all market conditions.

Origin
The necessity for Continuous Integration Security arose from the systemic failures witnessed during the early expansion of decentralized finance. Historical precedents involving catastrophic smart contract exploits highlighted a fundamental disconnect between rapid feature deployment and the immutable nature of on-chain execution.
Developers recognized that manual auditing cycles failed to keep pace with the velocity of market evolution.
- Protocol Fragility: Early decentralized systems lacked automated gates for detecting logic errors in complex financial instruments.
- Adversarial Evolution: Market participants developed sophisticated methods for exploiting vulnerabilities, necessitating a faster, machine-driven defense.
- Systemic Risk: The interconnection of liquidity pools meant that a single flaw in one protocol could trigger contagion across the entire decentralized landscape.
This realization forced a transition toward modular architectures where security validation is inseparable from the deployment pipeline. The shift reflects a maturation in how developers approach the construction of programmable money, prioritizing structural resilience over sheer speed of feature release.

Theory
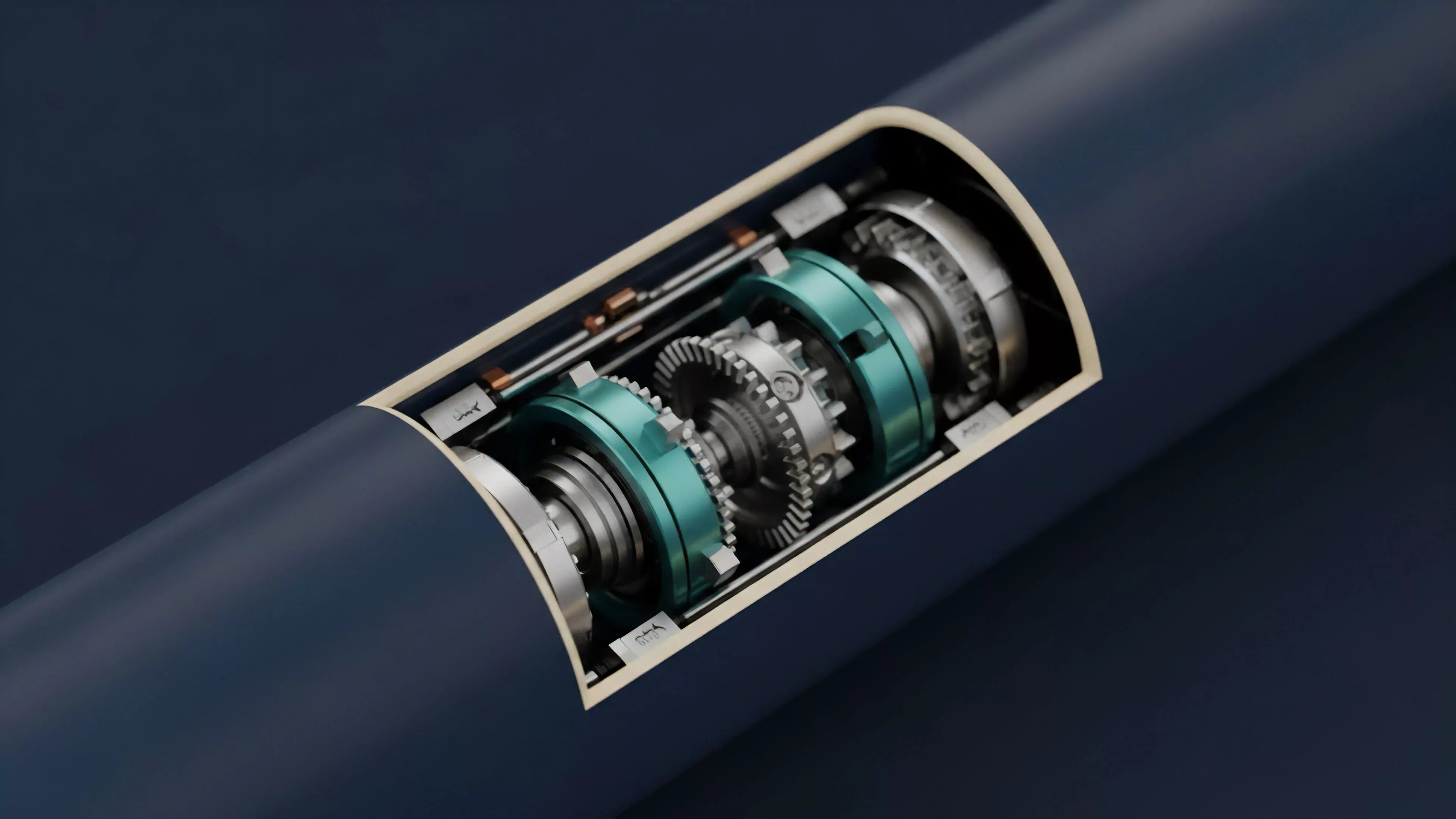
The architecture of Continuous Integration Security relies on a multi-layered verification framework. This structure incorporates static analysis, symbolic execution, and formal verification to model potential outcomes of contract interactions before they reach the mainnet.
By simulating adversarial behavior within a controlled environment, the system identifies edge cases that could lead to insolvency or unauthorized asset extraction.
| Component | Function |
| Static Analysis | Automated code scanning for known vulnerability patterns |
| Symbolic Execution | Mathematical exploration of all possible execution paths |
| Formal Verification | Proof-based validation of contract logic against specifications |
The strength of Continuous Integration Security lies in its ability to mathematically prove the absence of specific classes of exploits before code reaches the ledger.
These mechanisms create a feedback loop that enforces discipline within the development process. When a code commit fails these automated tests, the deployment pipeline halts, preventing the introduction of systemic risk into the market. This approach acknowledges the adversarial nature of blockchain environments, where the cost of a mistake is total loss.
Approach
Modern implementation of Continuous Integration Security focuses on the seamless integration of security tooling into developer workflows.
Teams utilize containerized environments to run parallel tests, ensuring that every branch of code receives comprehensive scrutiny. This approach emphasizes the automation of regression testing to guarantee that new updates do not break existing safety properties.
- Automated Gating: Pipelines require successful completion of security audits before triggering deployment scripts.
- Threat Modeling: Developers continuously update simulation parameters to reflect evolving attack vectors observed in the broader market.
- Incentivized Auditing: Protocols integrate bug bounty programs directly into the development cycle, rewarding external validation.
Strategic implementation requires a deep understanding of protocol physics. Engineers must balance the computational cost of intensive security checks against the requirement for timely updates. This balancing act defines the efficiency of a protocol’s development lifecycle and its ability to maintain trust among market participants.

Evolution
The trajectory of Continuous Integration Security has moved from manual, periodic audits toward real-time, autonomous monitoring.
Initially, security was a discrete event ⎊ a point-in-time check performed by third-party firms. The current state represents a transformation into a continuous, data-driven discipline where protocols monitor their own state and react to anomalies in real-time.
Continuous Integration Security evolves by transitioning from static pre-deployment checks to dynamic, runtime defense mechanisms that respond to live threats.
As decentralized markets increase in complexity, the integration of artificial intelligence and machine learning models has become common. These systems now analyze historical trade data and transaction flows to predict potential attack patterns. The transition from reactive code analysis to predictive systemic defense marks the current frontier of financial engineering.

Horizon
The future of Continuous Integration Security involves the widespread adoption of verifiable, hardware-accelerated security proofs.
As protocols become more complex, the computational burden of formal verification will necessitate specialized infrastructure. We anticipate the rise of decentralized security networks that pool resources to perform high-fidelity validation for multiple protocols simultaneously.
| Trend | Impact |
| Hardware Acceleration | Reduced latency for complex formal verification processes |
| Decentralized Auditing | Community-governed security validation and consensus-based trust |
| Self-Healing Protocols | Automated remediation of identified vulnerabilities at runtime |
The ultimate goal remains the creation of autonomous financial systems that possess inherent, immutable resistance to failure. By bridging the gap between advanced cryptographic research and practical deployment pipelines, we move toward a financial environment where security is a default property rather than a secondary concern.
