
Essence
Compliance-Centric Design represents the architectural integration of regulatory mandates directly into the protocol layer of decentralized financial systems. Rather than treating compliance as an external, post-hoc requirement, this paradigm embeds identity verification, transaction monitoring, and jurisdictional constraints within the smart contract logic itself.
Compliance-Centric Design embeds regulatory frameworks into the protocol layer to automate trust and jurisdictional adherence.
The core objective remains the reconciliation of permissionless innovation with the institutional demand for risk mitigation. By utilizing cryptographic proofs, such as zero-knowledge identifiers, systems maintain user privacy while ensuring that only authorized participants interact with specific liquidity pools. This approach transforms regulatory overhead into a programmatic feature, enabling scalable access to institutional capital within decentralized environments.
Origin
The genesis of Compliance-Centric Design stems from the systemic friction between the rapid expansion of decentralized exchanges and the rigid requirements of global financial oversight.
Early decentralized protocols prioritized censorship resistance and total anonymity, which inadvertently created significant barriers for institutional participants bound by Anti-Money Laundering and Know-Your-Customer directives.
- Institutional Requirements mandated that financial service providers verify counterparty identity before facilitating asset transfers.
- Regulatory Fragmentation forced protocols to choose between operating in legal grey zones or excluding entire jurisdictions.
- Protocol Security needs demanded robust mechanisms to prevent illicit capital flows that could trigger systemic de-platforming.
This structural incompatibility necessitated a transition from purely anonymous architectures toward systems capable of handling verified claims. Developers began utilizing decentralized identity standards to allow users to prove compliance status without exposing raw sensitive data. The resulting shift aimed to provide the necessary assurances for regulated entities to engage with decentralized derivatives without compromising the fundamental ethos of blockchain technology.

Theory
The mechanical foundation of Compliance-Centric Design relies on the separation of identity from transaction execution.
Protocols implement a permissioned gatekeeper mechanism where the smart contract validates a cryptographic proof of compliance before updating the state of the order book or margin engine.
| Mechanism | Function | Systemic Impact |
| Identity Oracle | Verifies off-chain credentials | Enables conditional access |
| ZK-Proof Validation | Confirms eligibility anonymously | Preserves user privacy |
| Jurisdictional Filtering | Restricts cross-border flows | Ensures regulatory alignment |
The mathematical modeling of these systems requires rigorous handling of state transitions. When a participant initiates an order, the protocol evaluates the interaction against a set of compliance rules. If the user fails to provide the required cryptographic attestation, the transaction reverts at the consensus level.
This creates a deterministic environment where compliance is enforced by code, eliminating the reliance on centralized intermediaries for enforcement.
Programmatic enforcement of regulatory rules at the smart contract level ensures deterministic compliance in decentralized markets.
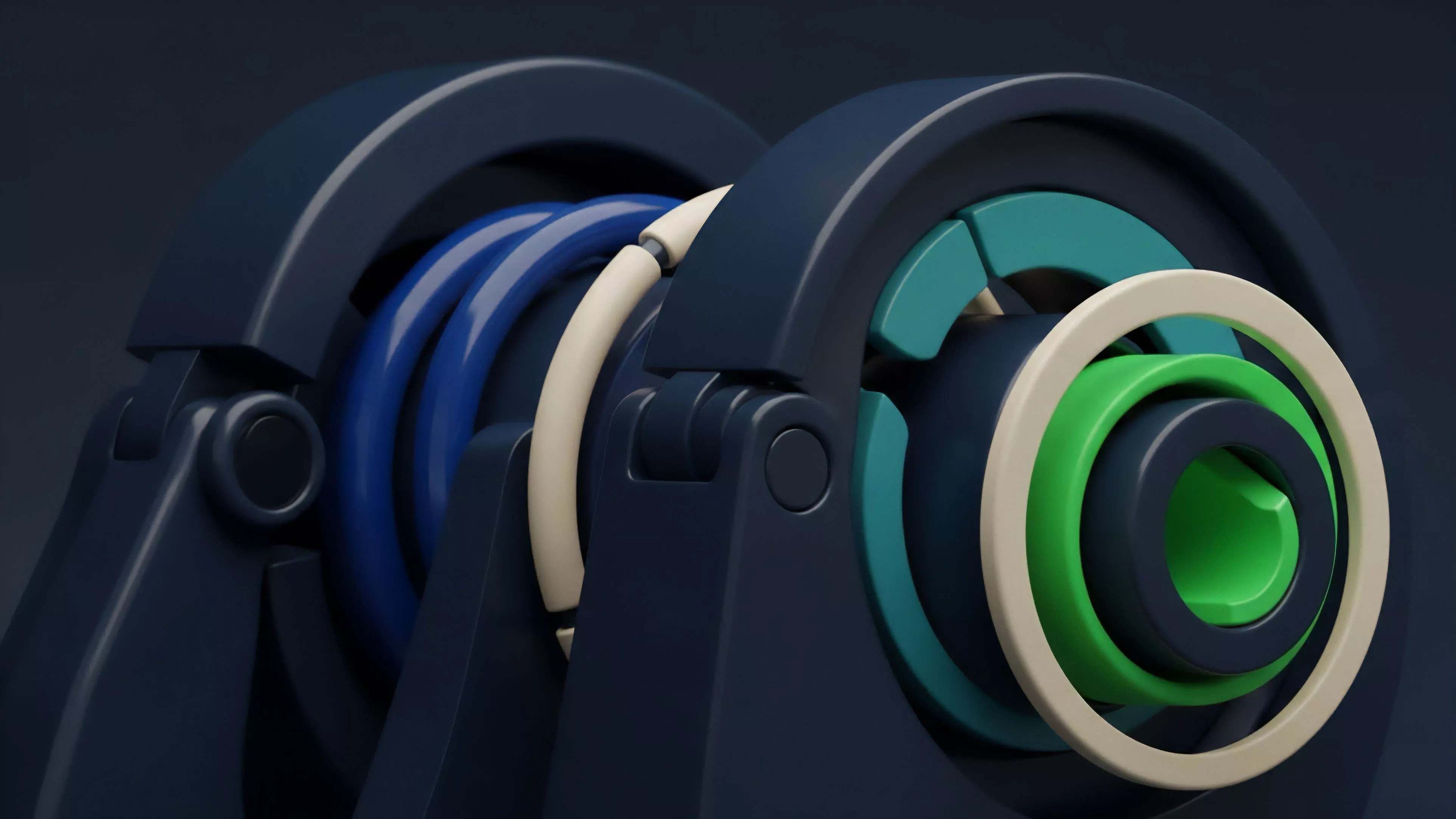
One might consider the protocol as a living organism; it adapts its internal permeability based on the environmental signals of the regulatory landscape, much like a cellular membrane regulating ion channels to maintain homeostasis. This structural flexibility allows the system to remain robust under varying degrees of external pressure, ensuring continuous operation while respecting the constraints of different legal regimes.

Approach
Current implementation strategies focus on the development of modular compliance middleware. Instead of building monolithic protocols, architects deploy specialized layers that handle identity verification and allow the core trading engine to remain focused on market microstructure and liquidity provision.
- Modular Architecture separates the compliance logic from the core matching engine to improve maintainability and auditability.
- Decentralized Identifiers provide a portable way for users to prove their compliance status across multiple platforms.
- Conditional Liquidity Pools isolate compliant capital from permissionless pools, mitigating contagion risks.
This approach necessitates a high degree of collaboration between protocol developers and legal experts. By defining standardized interfaces for compliance attestations, protocols can achieve interoperability, allowing a user to verify their status once and access a variety of compliant derivative venues. This standardization is critical for reducing the fragmentation of liquidity that currently hampers the efficiency of decentralized markets.

Evolution
The transition from early, unfiltered decentralized finance to the current state of Compliance-Centric Design reflects a maturation of the industry.
Initially, developers viewed any form of restriction as a failure of the decentralized vision. However, the accumulation of systemic risk and the subsequent regulatory response forced a re-evaluation of protocol architecture.
The evolution of protocol design reflects a shift from total anonymity to selective transparency and programmatic regulatory compliance.
The focus has moved from simple blacklisting to complex, multi-layered identity frameworks. Early iterations merely blocked specific wallet addresses, a blunt tool easily circumvented by professional actors. Modern designs utilize sophisticated zero-knowledge primitives to verify complex attributes, such as residency or investor status, without revealing the underlying identity of the participant.
This progress demonstrates a sophisticated understanding of how to balance the necessity of institutional participation with the requirements of privacy-preserving technology.

Horizon
The trajectory of Compliance-Centric Design points toward the automation of cross-jurisdictional regulatory alignment. Future protocols will likely feature dynamic, autonomous compliance engines that adjust their operational parameters in real-time based on shifts in global financial legislation.
| Development Phase | Technical Focus | Strategic Outcome |
| Integration | Identity and ZK-Proofs | Institutional onboarding |
| Interoperability | Cross-chain compliance standards | Unified liquidity access |
| Automation | Real-time regulatory updates | Dynamic risk management |
As these systems become more integrated, the distinction between traditional and decentralized finance will blur, leading to a hybrid infrastructure where assets move seamlessly across regulated and permissionless environments. The ultimate goal is the creation of a global, transparent, and resilient derivative market that operates with higher efficiency than existing legacy systems, while simultaneously providing the stability required by global capital allocators. What remains to be determined is whether these automated systems can maintain neutrality when confronted with the inherent subjectivity of political and legal enforcement.
